- DL manuals
- Abocom
- Gateway
- MH350
- User Manual
Abocom MH350 User Manual
Summary of MH350
Page 1
Mh350 multi-homing gateway user's manual ©2006 abocom systems, inc. All rights reserved.
Page 2
2 chapter 1 administrator................................................................................. 5 a dmin ........................................................................................................................... 7 l ogout .....................................................
Page 3
3 e xample ..................................................................................................................... 88 chapter 9 content blocking ...................................................................... 92 url...................................................................
Page 4
4 chapter 17 statistics ................................................................................... 227 wan s tatistics ....................................................................................................... 229 p olicy s tatistics ...............................................
Page 5: Chapter 1 Administrator
5 chapter 1 administrator administration “system” is the managing of settings such as the privileges of packets that pass through the mh350 and monitoring controls. The system administrators can manage, monitor, and configure mh350 settings. But all configurations are “read-only” for all users other...
Page 6
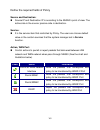
Define the required fields of administrator administrator name: the username of administrators and sub administrator for the mh350. The admin user name cannot be removed; and the sub-admin user can be removed or configure. The default account: admin; password: admin privilege: the privileges of ...
Page 7: Admin
Admin adding a new sub administrator step 1﹒in the admin webui, click the new sub admin button to create a new sub administrator. Step 2﹒in the add new sub administrator webui (figure 1-1) and enter the following setting: sub admin name: sub_admin password: 12345 7 add the user or click cancel t...
Page 8
Modify the administrator’s password step 1﹒in the admin webui, locate the administrator name you want to edit, and click on modify in the configure field. Step 2﹒the modify administrator password webui will appear. Enter the following information: password: admin new password: 52364 confirm pa...
Page 9: Add Permitted Ips
Add permitted ips step 1﹒add the following setting in permitted ips of administration: (figure1-3) name: enter master ip address: enter 163.173.56.11 netmask: enter 255.255.255.255 service: select ping and http click ok complete add new permitted ips (figure1-4) figure1-3 setting permitt...
Page 10: Logout
Logout step 1﹒click logout in system to protect the system while administrator are away. (figure1-5) figure1-5 confirm logout webui step 2﹒click ok and the logout message will appear in webui. (figure1-6) figure1-6 logout webui message 10
Page 11: Software Update
Software update step 1﹒select software update in system, and follow the steps below: to obtain the version number from version number and obtain the latest version from internet. And save the latest version in the hardware of the pc, which manage the mh350 click browse and choose the latest software...
Page 12: Chapter 2 Configure
12 chapter 2 configure configure the configure is according to the basic setting of the mh350. In this chapter the definition is setting, date/time, multiple subnet, route table, dhcp, dynamic dns, hosts table, and language settings..
Page 13
Define the required fields of settings mh350 configuration: the administrator can import or export the system settings. Click ok to import the file into the mh350 or click cancel to cancel importing. You also can revive to default value here. Email settings: select enable e-mail alert notificati...
Page 14
14 administration packet logging: after enable this function; the mh350 will record packet which source ip or destination address is mh350. And record in traffic log for system manager to inquire about. Define the required fields of time settings synchronize time/date: synchronizing the mh350 wi...
Page 15
15 nat mode: it allows internal network to set multiple subnet address and connect with the internet through different wan ip addresses. For example:the lease line of a company applies several real ip addresses 168.85.88.0/24, and the company is divided into r&d department, service, sales departme...
Page 16
16 define the required fields of dhcp subnet: the domain name of lan netmask: the lan netmask gateway: the default gateway ip address of lan broadcast ip: the broadcast ip of lan define the required fields of ddns domain name: the domain name that provided by ddns wan ip address: the wan...
Page 17: Setting
Setting system settings- exporting step 1﹒in system setting webui, click on button next to export system settings to client. Step 2﹒when the file download pop-up window appears, choose the destination place where to save the exported file and click on save. The setting value of mh350 will copy to th...
Page 18
System settings- importing step 1﹒in system setting webui, click on the browse button next to import system settings from client. When the choose file pop-up window appears, select the file to which contains the saved mh350 settings, then click ok. (figure2-2) step 2﹒click ok to import the file into...
Page 19
Restoring factory default settings step 1﹒select reset factory settings in mh350 configuration webui step 2﹒click ok at the bottom-right of the page to restore the factory settings. (figure2-4) figure2-4 reset factory settings 19.
Page 20
Enabling e-mail alert notification step 1﹒select enable e-mail alert notification under e-mail settings. Step 2﹒device name: enter the device name or use the default value. Step 3﹒sender address: enter the sender address. (required by some isps.) step 4﹒smtp server ip: enter smtp server’s ip address...
Page 21
Reboot mh350 step 1﹒reboot mh350:click reboot button next to reboot mh350 appliance. Step 2﹒a confirmation pop-up page will appear. Step 3﹒follow the confirmation pop-up page; click ok to restart mh350. (figure2-6) figure2-6 reboot mh350 21.
Page 22: Date / Time
Date / time date/time settings step 1﹒select enable synchronize with an internet time server (figure2-7) step 2﹒click the down arrow to select the offset time from gmt. Step 3﹒enter the server ip / name with which you want to synchronize. Step 4﹒set the interval time to synchronize with outside serv...
Page 23: Multiple Subnet
23 multiple subnet connect to the internet through multiple subnet nat or routing mode by the ip address that set by the lan user’s network card preparation mh350 wan1 (10.10.10.1) connect to the isp router (10.10.10.2) and the subnet that provided by isp is 162.172.50.0/24 to connect to internet, w...
Page 24: Adding Multiple Subnet
Adding multiple subnet add the following settings in multiple subnet of system function: click on new entry alias ip of lan interface: enter 162.172.50.1 netmask:enter 255.255.255.0 wan1: enter interface ip 10.10.10.1, and choose routing in forwarding mode wan2:enter interface ip 211.22.22...
Page 25
Wan1 and wan2 interface can use assist to enter the data. After setting, there will be two subnet in lan: 192.168.1.0/24 (default lan subnet) and 162.172.50.0/24. So if lan ip is: ˙192.168.1.Xx, it must use nat mode to access to the internet. (in policy it only can setup to access to internet by wan...
Page 26: Route Table
26 route table to connect two different subnet router with the mh350 and makes them to connect to internet through mh350 preparation company a: wan1 (61.11.11.11) connects with atur to internet wan2 (211.22.22.22) connects with atur to internet lan subnet: 192.168.1.1/24 the router1 which connect wi...
Page 27: Route Table
Route table step 1﹒enter the following settings in route table in system function: 【destination ip】: enter 192.168.10.1 【netmask】: enter 255.255.255.0。 【gateway】: enter 192.168.1.252 【interface】: select lan click ok (figure 2-10) figure2-10 add new static route1 step 2﹒enter the following ...
Page 28
Step 3﹒enter the following setting in route table in system function: 【destination ip】: enter 10.10.10.0 【netmask】: enter 255.255.255.0 【gateway】: enter 192.168.1.252 【interface】: select lan click ok (figure 2-12) figure2-12 add new static route3 28.
Page 29
Step 4﹒adding successful. At this time the computer of 192.168.10.1/24, 192.168.20.1/24 and 192.168.1.1/24 can connect with each other and connect to internet by nat (figure 2-13) figure 2-13 route table setting 29.
Page 30: Dhcp
30 dhcp step 1﹒select dhcp in system and enter the following settings: domain name:enter the domain name dns server 1: enter the distributed ip address of dns server1. dns server 2: enter the distributed ip address of dns server2. wins server 1: enter the distributed ip address of wins serve...
Page 31
Figure 2-14 dhcp webui when selecting automatically get dns, the dns server will lock it as lan interface ip. (using occasion: when the system administrator starts authentication, the users’ first dns server must be the same as lan interface ip in order to enter authentication webui) 31.
Page 32: Ddns
Ddns dynamic dns settings step 1﹒select dynamic dns in system function (figure2-15). Click new entry button service providers:select service providers. automatically fill in the wan 1/2 ip:check to automatically fill in the wan 1/2 ip.。 user name:enter the registered user name. password:ente...
Page 33
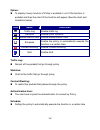
Chart meaning update successfully incorrect username or password connecting to server unknown error if system administrator had not registered a ddns account, click on sign up then can enter the website of the provider. If you do not select automatically fill in the wan ip and then you can enter a s...
Page 34: Host Table
Host table step 1 ﹒select host table in settings function and click on new entry domain name: the domain name of the server virtual ip address: the virtual ip address respective to host table click ok to add host table. (figure2-17) figure2-17 add new host table to use host table, the user pc’...
Page 35: Language
Language select the language version (english version/ traditional chinese version or simplified chinese version) and click ok. (figure2-18) figure2-18 language setting webui 35.
Page 36: Chapter 3 Interface
36 chapter 3 interface interface in this section, the administrator can set up the ip addresses for the office network. The administrator may configure the ip addresses of the lan network, the wan 1/2 network, and the dmz network. The netmask and gateway ip addresses are also configured in this sect...
Page 37
37 define the required fields of interface lan: using the lan interface, the administrator can set up the lan network of mh350. Ping: select this function to allow the lan users to ping the interface ip address. Http: select to enable the user to enter the webui of mh350 from interface ip. Wan...
Page 38
38 connect mode: display the current connection mode: pppoe (adsl user) dynamic ip address (cable modem user) static ip address saturated connections: set the number for saturation whenever session numbers reach it, the mh350 switches to the next agent on the list. Priority: set priority...
Page 39
39 dmz: the administrator uses the dmz interface to set up the dmz network. the dmz includes: nat mode:in this mode, the dmz is an independent virtual subnet. This virtual subnet can be set by the administrator but cannot be the same as lan interface. transparent mode: in this mode, the dmz ...
Page 40
40 we set up four interface address examples in this chapter: no. Suitable situation example page ex1 lan modify lan interface settings 41 ex2 wan setting wan interface address 42 ex3 dmz setting dmz interface address (nat mode) 50 ex4 dmz setting dmz interface address (transparent mode) 51.
Page 41: Lan
Lan modify lan interface settings step 1﹒select lan in interface and enter the following setting: enter the new ip address and netmask select ping and http click ok (figure3-1) figure3-1 setting lan interface webui the default lan ip address is 192.168.1.1. After the administrator setting the ...
Page 42: Wan
Wan setting wan interface address step 1﹒select wan in interface and click modify in wan1 interface. The setting of wan2 interface is almost the same as wan1. The difference is that wan2 has a selection of disable. The system administrator can close wan2 interface by this selection. (figure3-2) figu...
Page 43
Step 2﹒setting the connection service (icmp or dns way): icmp:enter an alive indicator site ip (can select from assist) (figure3-3) dns:enter dns server ip address and domain name (can select from assist) (figure3-4) setting time of seconds between sending alive packet. Figure3-3 icmp connecti...
Page 44
44 step 3﹒select the connecting way: pppoe (adsl user) (figure3-5): 1. Select pppoe 2. Enter user name as an account 3. Enter password as the password 4. Select dynamic or fixed in ip address provided by isp. If you select fixed, please enter ip address, netmask, and default gateway. 5. Enter max....
Page 45
Figure3-5 pppoe connection figure3-6 complete pppoe connection setting if the connection is pppoe, you can choose service-on-demand for wan interface to connect automatically when disconnect; or to set up auto disconnect if idle (not recommend) 45.
Page 46
46 dynamic ip address (cable modem user) (figure3-7): 1. Select dynamic ip address (cable modem user) 2. Click renew in the right side of ip address and then can obtain ip automatically. 3. If the mac address is required for isp then click on clone mac address to obtain mac ip automatically. 4. Ho...
Page 47
Figure3-7 dynamic ip address connection figure3-8 complete dynamic ip connection setting 47.
Page 48
static ip address (figure3-9) 1. Select static ip address 2. Enter ip address, netmask, and default gateway that provided by isp 3. Enter dns server1 and dns server2 in wan2, the connecting of static ip address does not need to set dns server 4. Enter max. Downstream bandwidth and max. Upstream ba...
Page 49
Figure3-10 complete static ip address connection setting when selecting ping and webui on wan network interface, users will be able to ping the mh350 and enter the webui wan network. It may influence network security. The suggestion is to cancel ping and webui after all the settings have finished. A...
Page 50: Dmz
Dmz setting dmz interface address (nat mode) step 1﹒click dmz interface step 2﹒select nat mode in dmz interface select nat in dmz interface enter ip address and netmask step 3﹒select ping and http step 4﹒click ok (figure3-11) figure3-11 setting dmz interface address (nat mode) webui 50
Page 51
Setting dmz interface address (transparent mode) step 1﹒select dmz interface step 2﹒select transparent mode indmz interface select dmz_transparent in dmz interface step 1﹒select ping and http step 2﹒click ok (figure3-12) figure 3-12 setting dmz interface address (transparent mode) webui in wan, th...
Page 52: Chapter 4 Address
Chapter 4 address address the mh350 allows the administrator to set interface addresses of the lan network, lan network group, wan network, wan network group, dmz and dmz group. An ip address in the address table can be an address of a computer or a sub network. The administrator can assign an easil...
Page 53
53 define the required fields of address name: the system administrator set up a name as ip address that is easily recognized. Ip address: it can be a pc’s ip address or several ip address of subnet. Different network area can be: internal ip address, external ip address, and dmz ip address. Net...
Page 54
54 we set up two address examples in this chapter: no suitable situation example page ex1 lan under dhcp circumstances, assign the specific ip to static users and restrict them to access ftp net service only through policy. 55 ex2 lan group wan set up a policy that only allows partial users to conne...
Page 55: Example
Example under dhcp situation, assign the specific ip to static users and restrict them to access ftp net service only through policy step 1﹒select lan in address and enter the following settings: click new entry button (figure4-1) name: enter rayearth ip address: enter 192.168.3.2 netmask: e...
Page 56
Step 2﹒adding the following setting in outgoing policy: (figure4-3) figure 4-3 add a policy of restricting the specific ip to access to internet step 3﹒complete assigning the specific ip to static users in outgoing policy and restrict them to access ftp net service only through policy: (figure4-4) f...
Page 57
When the system administrator setting the address book, he/she can choose the way of clicking on to make the mh350 to fill out the user’s mac address automatically. In lan of address function, the mh350 will default an inside any address represents the whole lan network automatically. Others like wa...
Page 58
Setup a policy that only allows partial users to connect with specific ip (external specific ip) step 1﹒setting several lan network address. (figure4-5) figure4-5 setting several lan network address 58.
Page 59
Step 2 ﹒enter the following settings in lan group of address: click new entry (figure 4-6) enter the name of the group select the users in the available address column and click add click ok (figure 4-7) figure4-6 add new lan address group figure4-7 complete adding lan address group the sett...
Page 60
Step 3﹒enter the following settings in wan of address function: click new entry (figure4-8) enter the following data (name, ip address, netmask) click ok (figure4-9) figure4-8 add new wan address figure4-9 complete the setting of wan address 60
Page 61
Step 4﹒to exercise step1~3 in policy (figre4-10, 4-11) figure4-10 to exercise address setting in policy figure4-11 complete the policy setting the address function really take effect only if use with policy. 61.
Page 62: Chapter 5 Service
Chapter 5 service service tcp and udp protocols support varieties of services, and each service consists of a tcp port or udp port number, such as telnet (23), smtp (21), smtp (25), pop3 (110), etc. The mh350 includes two services: pre-defined service and custom service. The common-use services like...
Page 63
63 it takes only one control policy to achieve the same effect as the 50 control policies..
Page 64
Define the required fields of service pre-defined webui’s chart and illustration: chart illustration any service tcp service, for example:ftp, finger, http, https , imap, smtp, pop3, any, aol, bgp, gopher, inter locator, irc, l2tp, ldap, netmeeting, nntp, pptp, real media, rlogin, ssh, tcp any, teln...
Page 65
65 we set up two service examples in this chapter: no suitable situation example page ex1 custom allow external user to communicate with internal user by voip through policy. (voip port: tcp 1720, tcp 15325-15333, udp 15325-15333) 65 ex2 group setting service group and restrict the specific users on...
Page 66: Custom
Custom allow external user to communicate with internal user by voip through policy. (voip port: tcp 1720, tcp 15328-15333, udp 15328-15333) step 1﹒set lan and lan group in address function as follows: (figure5-1, 5-2) figure5-1 setting lan address book webui figure5-2 setting lan group address book...
Page 67
Step 2﹒enter the following setting in custom of service function: click new entry (figure5-3) service name: enter the preset name voip protocol#1 select tcp, need not to change the client port, and set the server port as: 1720:1720 protocol#2 select tcp, need not to change the client port, a...
Page 68
Under general circumstances, the range of port number of client is 1024-65535. Change the client range in custom of is not suggested. If the port numbers that enter in the two spaces are different port number, then enable the port number under the range between the two different port numbers (for ex...
Page 69
Step 3﹒compare service to virtual server. (figure5-5) figure5-5 compare service to virtual server step 4﹒compare virtual server to incoming policy. (figure5-6) figure5-6 complete the policy for external voip to connect with internal voip step 5﹒in outgoing policy, complete the setting of internal us...
Page 70: Group
Group setting service group and restrict the specific users only can access to service resource that provided by this group through policy (group: http, pop3, smtp, dns) step 1﹒enter the following setting in group of service: click new entry (figure 5-8) name: enter main_service select http, p...
Page 71
Figure5-9 complete the setting of adding service group if you want to remove the service you choose from selected service, choose the service you want to delete and click remove. 71.
Page 72
Step 2﹒in lan group of address function, setting an address group that can include the service of access to internet. (figure5-10) figure5-10 setting address book group step 3﹒compare service group to outgoing policy. (figure5-11) figure5-11 setting policy 72.
Page 73: Chapter 6 Schedule
Chapter 6 schedule schedule in this chapter, the mh350 provides the administrator to configure a schedule for policy to take effect and allow the policies to be used at those designated times. And then the administrator can set the start time and stop time or vpn connection in policy or vpn. By usin...
Page 74: Example
Example to configure the valid time periods for lan users to access to internet in a day step 1﹒enter the following in schedule: click new entry (figure6-1) enter schedule name set up the working time of schedule for each day click ok (figure6-2) figure6-1 setting schedule webui figure6-2 co...
Page 75
Step 2﹒compare schedule with outgoing policy (figure6-3) figure6-3 complete the setting of comparing schedule with policy the schedule must compare with policy . 75.
Page 76: Chapter 7 Qos
Chapter 7 qos qos by configuring the qos, you can control the outbound and inbound upstream/downstream bandwidth. The administrator can configure the bandwidth according to the wan bandwidth. Downstream bandwidth : to configure the guaranteed bandwidth and maximum bandwidth. Upstream bandwidth:to co...
Page 77
Figure7-2 the flow after using qos (max. Bandwidth: 400kbps, guaranteed bandwidth: 200kbps) 77.
Page 78
78 define the required fields of qos wan: display wan1 and wan2 downstream bandwidth: to configure the guaranteed bandwidth and maximum bandwidth according to the bandwidth range you apply from isp upstream bandwidth: to configure the guaranteed bandwidth and maximum bandwidth according to the b...
Page 79
79 we set up two qos examples in this chapter: no suitable situation example page ex1 qos setting a policy that can restrict the user’s downstream and upstream bandwidth. 79.
Page 80: Example
Example setting a policy that can restrict the user’s downstream and upstream bandwidth step 1﹒enter the following settings in qos: click new entry (figure7-3) name: the name of the qos you want to configure. enter the bandwidth in wan1, wan2 select qos priority click ok (figure7-4) figure...
Page 81
Step 2﹒use the qos that set by step1 in outgoing policy. (figure7-5, 7-6) figure7 policy -5 setting the qos in figure7-6 complete policy setting when the administrator are setting qos, the bandwidth range that can be set is the value that system administrator set in the wan of interface. So when the...
Page 82: Chapter 8 Authentication
82 chapter 8 authentication authentication by configuring the authentication, you can control the user’s connection authority. The user has to pass the authentication to access to internet. The mh350 configures the authentication of lan’s user by setting account and password to identify the privileg...
Page 83
Define the required fields of authentication authentication management provide the administrator the port number and valid time to setup mh350 authentication. (have to setup the authentication first) authentication port: the internal user have to pass the authentication to access to the internet...
Page 84
Z when the user connect to external network by authentication, the following page will be displayed: (figure8-2) figure8-2 authentication login webui 84.
Page 85
Z it will connect to the appointed website after passing authentication: (figure8-3) figure8-3 connecting to the appointed website after authentication if the user ask for authentication positively, can enter the lan ip by the authentication port number. And then the authentication webui will be dis...
Page 86
86 auth-user name: the user account for authentication you want to set. Password: the password when setting up authentication. Confirm password: enter the password that correspond to password.
Page 87
87 we set up four authentication examples in this chapter: no suitable situation example page ex1 auth user auth group setting specific users to connect with external network only before passing the authentication of policy. (adopt the built-in auth user and auth group function) 87.
Page 88: Example
Example setting specific users to connect with external network only before passing the authentication of policy. (adopt the built-in auth user and auth group function) step 1﹒setup several auth user in authentication. (figire8-4) figure8-4 setting several auth users webui to use authentication, the...
Page 89
Step 2﹒add auth user group setting in authentication function and enter the following settings: click new entry name: enter laboratory select the auth user you want and add to selected auth user click ok complete the setting of auth user group (figure8-5) figure8-5 setting auth group webui...
Page 90
Step 3﹒add a policy in outgoing policy and input the address and authentication of step 2 (figure8-6, 8-7) 90 figure8-6 auth-user policy setting figure8-7 complete the policy setting of auth-user.
Page 91
Step 4﹒when user is going to access to internet through browser, the authentication ui will appear in browser. After entering the correct user name and password, click ok to access to internet. (figure8-8) step 5 ﹒if the user does not need to access to internet anymore and is going to logout, he/she...
Page 92: Chapter 9 Content Blocking
92 chapter 9 content blocking content filtering content filtering includes「url」,「script」,「p2p」,「im」,「download」. 【url blocking】 :the administrator can set up to “allow” or “restrict” entering the specific website by complete domain name, key words, and met character (~and*). 【script blocking】: the ac...
Page 93
93 define the required fields of content blocking url string: the domain name that restricts to enter or only allow entering. Popup blocking: prevent the pop-up webui appearing activex blocking: prevent activex packets java blocking: prevent java packets cookies blocking: prevent cookies p...
Page 94
94 sub-name file blocking: prevent users to deliver specific sub-name file by http all type: prevent users to send the audio, video types, and sub-name file…etc. By http protocol..
Page 95
95 we set up five content blocking examples in this chapter: no suitable situation example page ex1 url blocking restrict the internal users only can access to some specific website 95 ex2 script blocking restrict the internal users to access to script file of website. 98 ex3 p2p blocking restrict t...
Page 96: Url
Url restrict the internal users only can access to some specific website ※url blocking: symbol: ~ means open up; * means metacharacter restrict not to enter specific website: enter the 「complete domain name」 or 「key word」of the website you want to restrict in url string. For example: www.Kcg.Gov.Tw ...
Page 97
Step 1﹒enter the following in url of content filtering function: click new entry url string: enter ~yahoo, and click ok click new entry url string: enter ~google, and click ok click new entry url string: enter *, and click ok complete setting a url blocking policy (figure9-1) figure9-1...
Page 98
Step 2﹒add a outgoing policy and use in content blocking function: (figure9-2) figure9-2 url blocking policy setting step 3﹒complete the policy of permitting the internal users only can access to some specific website in outgoing policy function: (figure9-3) figure9-3 complete policy settings afterw...
Page 99: Script
Script restrict the internal users to access to script file of website step 1﹒select the following data in script of content blocking function: select popup blocking select activex blocking select java blocking select cookies blocking click ok complete the setting of script blocking (fig...
Page 100
Step 2﹒add a new outgoing policy and use in content blocking function: (figure9-5) figure9-5 new policy of script blocking setting step 3﹒complete the policy of restricting the internal users to access to script file of website in outgoing policy: (figure9-6) figure9-6 complete script blocking polic...
Page 101: P2P
P2p restrict the internal users to access to the file on internet by p2p step 1﹒select the following data in p2p of content blocking function: select edonkey blocking select bittorrent blocking select winmx blocking click ok complete the setting of p2p blocking (figure9-7) figure9-7 p2p bl...
Page 102
Step 2﹒add a new outgoing policy and use in content blocking function: (figure9-8) figure9-8 add new policy of p2p blocking step 3﹒complete the policy of restricting the internal users to access to the file on internet by p2p in outgoing policy: (figure9-9) figure9-9 complete p2p blocking policy set...
Page 103
Im restrict the internal users to send message, files, video and audio by instant messaging step 1﹒enter as following in im blocking of content blocking function: select msn messenger, yahoo messenger, icq messenger, qq messenger and skype. Click ok complete the setting of im blocking. (figure9-10...
Page 104
Step 2﹒add a new outgoing policy and use in content blocking function: (figire9-11) figure9-11 add new im blocking policy step 3﹒complete the policy of restricting the internal users to send message, files, audio, and video by instant messaging in outgoing policy: (figure9-12) figure9-12 complete im...
Page 105: Download
Download restrict the internal users to access to video, audio, and some specific sub-name file from http or ftp protocol directly step 1﹒enter the following settings in download of content blocking function: select all types blocking click ok complete the setting of download blocking. (figure...
Page 106
Step 2﹒add a new outgoing policy and use in content blocking function: (figure9-14) figure9-14 add new download blocking policy setting step 3﹒complete the outgoing policy of restricting the internal users to access to video, audio, and some specific sub-name file by http protocol directly: (figure9...
Page 107: Chapter 10 Virtual Server
107 chapter 10 virtual server virtual server the real ip address provided from isp is always not enough for all the users when the system manager applies the network connection from isp. Generally speaking, in order to allocate enough ip addresses for all computers, an enterprise assigns each comput...
Page 108
108 in this chapter, we will have detailed introduction and instruction of mapped ip and server 1/2/3/4: mapped ip: because the intranet is transferring the private ip by nat mode (network address translation). And if the server is in lan, its ip address is belonging to private ip address. Then the ...
Page 109
109 define the required fields of virtual server wan ip: wan ip address (real ip address) map to virtual ip: map the wan real ip address into the lan private ip address virtual server real ip: the wan ip address which mapped by the virtual server. Service name (port number): the service name...
Page 110
110 we set up four virtual server examples in this chapter: no. Suitable situation example page ex1 mapped ip make a single server that provides several services such as ftp, web, and mail, to provide service by policy. 110 ex2 virtual server make several servers that provide a single service, to pr...
Page 111: Example
Example make a single server that provides several services such as ftp, web, and mail, to provide service by policy step 1﹒setting a server that provide several services in lan, and set up the network card’s ip as 192.168.1.100. Dns is external dns server. Step 2﹒enter the following setting in lan ...
Page 112
Step 4﹒group the services (dns, ftp, http, pop3, smtp…) that provided and used by server in service function. And add a new service group for server to send mails at the same time. (figure10-3) figure10-3 service setting step 5﹒add a policy that includes settings of step3, 4 in incoming policy. (fig...
Page 113
Step 7﹒complete the setting of providing several services by mapped ip. (figure10-6) figure10-6 a single server that provides several services by mapped ip strong suggests not tochoose any when setting mapped ip and choosing service. Otherwise the mapped ip will be exposed to internet easily and may...
Page 114
114 make several servers that provide a single service, to provide service through policy by virtual server (take web service for example) step 1﹒setting several servers that provide web service in lan network, which ip address is 192.168.1.101, 192.168.1.102, 192.168.1.103, and 192.168.1.104.
Page 115
Step 2﹒enter the following data in server 1 of virtual server function: click the button next to virtual server real ip (“click here to configure”) in server 1 virtual server real ip: enter 211.22.22.23 (click assist for assistance) click ok (figure10-7) figure10-7 virtual server real ip setting c...
Page 116
Step 3﹒add a new policy in incoming policy, which includes the virtual server, set by step2. (figure10-9) figure10-9 complete virtual server policy setting in this example, the external users must change its port number to 8080 before entering the website that set by the web server. Step 4﹒complete ...
Page 117
The external user use voip to connect with voip of lan (voip port: tcp 1720, tcp 15328-15333, udp 15328-15333) step 1﹒set up voip in lan network, and its ip is 192.168.1.100 step 2﹒enter the following setting in lan of address function: (figure10-11) figure10-11 setting lan address webui step 3﹒add ...
Page 118
Step 4﹒enter the following setting in server1 of virtual server function: click the button next to virtual server real ip (“click here to configure”) in server1 virtual server real ip: enter 61.11.11.12 (click assist for assistance) (use wan) click ok (figure10-13) figure10-13 virtual server real ...
Page 119
Step 5﹒add a new incoming policy, which includes the virtual server that set by step4: (figure10-15) figure10-15 complete the policy includes virtual server setting step 6﹒enter the following setting of the internal users using voip to connect with external network voip in outgoing policy: (figure10...
Page 120
120 step 7﹒complete the setting of the external/internal user using specific service to communicate with each other by virtual server. (figure10-17) figure10-17 complete the setting of the external/internal user using specific service to communicate with each other by virtual server.
Page 121
Make several servers that provide several same services, to provide service through policy by virtual server. (take http, pop3, smtp, and dns group for example) step 1﹒setting several servers that provide several services in lan network. Its network card’s ip is 192.168.1.101, 192.168.1.102, 192.168...
Page 122
Step 3﹒group the service of server in custom of service. Add a service group for server to send e-mail at the same time. (figure10-20) figure10-20 add new service group 122.
Page 123
Step 4﹒enter the following data in server1 of virtual server: click the button next to virtual server real ip (“click here to configure”) in server1 virtual server real ip: enter 211.22.22.23 (click assist for assistance) click ok (figure10-21) figure10-21 virtual server real ip setting clic...
Page 124
Step 5﹒add a new incoming policy, which includes the virtual server that set by step 3: (figure10-23) figure10-23 complete incoming policy setting step 6﹒add a new policy that includes the settings of step2, 3 in outgoing policy. It makes server can send e-mail to external mail server by mail servic...
Page 125
Step 7﹒complete the setting of providing several services by virtual server. (figure10-25) figure10-25 complete the setting of providing several services by several virtual server 125.
Page 126: Chapter 11 Vpn
Chapter 11 vpn vpn the mh350 adopts vpn to set up safe and private network service. And combine the remote authentication system in order to integrate the remote network and pc of the enterprise. Also provide the enterprise and remote users a safe encryption way to have best efficiency and encryptio...
Page 127
127 define the required fields of vpn: rsa: a public-key cryptosystem for encryption and authentication. Preshared key: the ike vpn must be defined with a preshared key. The key may be up to 128 bytes long. Isakmp (internet security association key management protocol): an extensible protocol-...
Page 128
128 des (data encryption standard): the data encryption standard developed by ibm in 1977 is a 64-bit block encryption block cipher using a 56-bit key. Triple-des (3des): the des function performed three times with either two or three cryptographic keys. Aes (advanced encryption standard): an ...
Page 129
Define the required fields of ipsec function to display the vpn connection status via icon。 chart -- meaning not be applied disconnect connecting name: the vpn name to identify the ipsec autokey definition. The name must be the only one and cannot be repeated. Gateway ip: the wan interface ip ...
Page 130
Define the required fields of pptp server function pptp server: to select enable or disable client ip range: setting the ip addresses range for pptp client connection i: to display the vpn connection status via icon。 chart -- meaning not be applied disconnect connecting user name: display th...
Page 131
Define the required fields of pptp client function to display the vpn connection status via icon。 chart -- meaning not be applied disconnect connecting user name: displays the pptp client user’s name when connecting to pptp server. Server ip or domain name: display the pptp server ip addresses...
Page 132
Define the required fields of tunnel function to display the vpn connection status via icon。 chart -- meaning not be applied disconnect connecting name: the vpn name to identify the vpn tunnel definition. The name must be the only one and cannot be repeated. Source subnet: displays the source ...
Page 133
133 we set up two vpn examples in this chapter: no. Suitable situation example page ex1 ipsec autokey setting ipsec vpn connection between two mh350 133 ex2 pptp setting pptp vpn connection between two mh350 146.
Page 134: Example
Example setting ipsec vpn connection between two mh350 preparation company a wan ip: 61.11.11.11 lan ip: 192.168.10.X company b wan ip: 211.22.22.22 lan ip: 192.168.20.X this example takes two mh350 as work platform. Suppose company a 192.168.10.100 create a vpn connection with company b 192.168.20....
Page 135
135 step 3 ﹒select remote gateway-fixed ip or domain name in to destination list and enter the ip address.(figure11-7) figure11-7 ipsec to destination setting step 4 ﹒select preshare in authentication method and enter the preshared key (max: 100 bits) (figure11-8) figure11-8 ipsec authentication met...
Page 136
Step 6﹒you can choose data encryption + authentication or authentication only to communicate in ipsec algorithm list: enc algorithm: 3des/des/aes/null auth algorithm: md5/sha1 here we select 3des for enc algorithm and md5 for auth algorithm to make sure the encapsulation way for data transmission (f...
Page 137
137.
Page 138
Step 9﹒enter the following setting in tunnel of vpn function: (figure11-13) enter a specific tunnel name. from source: select lan from source subnet / mask: enter 192.168.10.0 / 255.255.255.0. to destination: select to destination subnet / mask. to destination subnet / mask: enter 192.168.2...
Page 139
Step 10﹒enter the following setting in outgoing policy:(figure11-15) authentication user: select all_net. schedule: select schedule_1. qos: select qos_1. tunnel: select ipsec_vpn_tunnel. click ok.(figure11-16) figure11-15 setting the vpn tunnel outgoing policy figure11-16 complete the vpn t...
Page 140
Step 11﹒enter the following setting in incoming policy: (figure11-17) schedule: select schedule_1. qos: select qos_1. tunnel: select ipsec_vpn_tunnel. click ok.(figure11-18) figure11-17 setting the vpn tunnel incoming policy figure11-18 complete the vpn tunnel incoming policy setting 140
Page 141
The default gateway of company b is the lan ip of the mh350 192.168.20.1. Follow the steps below: 141 step 1.Enter the following setting in multiple subnet of system configure function: (figure11-19) figure11-19 multiple subnet setting step 2.Enter the default ip of gateway of company b’s mh350, 192...
Page 142
142 step 4.Select remote gateway-fixed ip or domain name in to destination list and enter the ip address.(figure11-22) figure11-22 ipsec to destination setting step 5.Select preshare in authentication method and enter the preshared key (max: 100 bits) (figure11-23) figure11-23 ipsec authentication m...
Page 143
Step 7.You can choose data encryption + authentication or authentication only to communicate in ipsec algorithm list: enc algorithm: 3des/des/aes/null auth algorithm: md5/sha1 here we select 3des for enc algorithm and md5 for auth algorithm to make sure the encapsulation way for data transmission. (...
Page 144
144 ) step 10.Enter the following setting in tunnel of vpn function: (figure11-28 enter a specific tunnel name. from source: select lan from source subnet / mask: enter 192.168.20.0 / 255.255.255.0. to destination: select to destination subnet / mask. to destination subnet / mask: enter 192...
Page 145
145 ) step 11.Enter the following setting in outgoing policy: (figure11-30 authentication user: select all_net. schedule: select schedule_1. qos: select qos_1. tunnel: select ipsec_vpn_tunnel. click ok.(figure11-31) figure11-30 setting the vpn tunnel outgoing policy figure11-31 complete the...
Page 146
Step 12.Enter the following setting in incoming policy: (figure11-32) schedule: select schedule_1. qos: select qos_1. tunnel: select ipsec_vpn_tunnel. click ok.(figure11-33) figure11-32 setting the vpn tunnel incoming policy figure11-33 complete the vpn tunnel incoming policy setting 146.
Page 147
Step 13.Complete ipsec vpn connection. (figure11-34) figure 11-34 ipsec vpn connection deployment 147.
Page 148
148 setting pptp vpn connection between two mh350 preparation company a wan ip: 61.11.11.11 lan ip: 192.168.10.X company b wan ip: 211.22.22.22 lan ip: 192.168.20.X this example takes two mh350 as flattop. Suppose company b 192.168.20.100 is going to have vpn connection with company a 192.168.10.100...
Page 149
The default gateway of company a is the lan ip of the mh350 192.168.10.1. Follow the steps below: step 1.Enter pptp server of vpn function in the mh350 of company a. Select modify and enable pptp server: select encryption. client ip range: enter 192.44.75.1-254. idle time: enter 0. (figure11-3...
Page 150
Step 2.Add the following settings in pptp server of vpn function in the mh350 of company a: select new entry. (figure11-36) user name: enter pptp_connection. password: enter 123456789. client ip assigned by: select ip range. click ok. (figure11-37) figure 11-36 pptp vpn server setting figu...
Page 151
Step 3.Enter the following setting in tunnel of vpn function: (figure11-38) enter a specific tunnel name. from source: select lan from source subnet / mask: enter 192.168.10.0 / 255.255.255.0. to destination: select to destination subnet / mask. to destination subnet / mask: enter 192.168.2...
Page 152
Step 4.Enter the following setting in outgoing policy: (figure11-40) authentication user: select all_net. schedule: select schedule_1. qos: select qos_1. tunnel: select pptp_vpn_tunnel. click ok.(figure11-41) figure11-40 setting the vpn tunnel outgoing policy figure11-41 complete the vpn tu...
Page 153
Step 5.Enter the following setting in incoming policy: (figure11-42) schedule: select schedule_1. qos: select qos_1. tunnel: select pptp_vpn_tunnel. click ok.(figure11-43) figure11-42 setting the vpn tunnel incoming policy figure11-43 complete the vpn tunnel incoming policy setting 153.
Page 154
The default gateway of company b is the lan ip of the mh350 192.168.20.1. Follow the steps below: step 1.Add the following settings in pptp client of vpn function in the mh350 of company b: click new entry button. (figure11-44) user name: enter pptp_connection. password: enter123456789. serv...
Page 155
Step 2.Enter the following setting in tunnel of vpn function: (figure11-46) enter a specific tunnel name. from source: select lan from source subnet / mask: enter 192.168.20.0 / 255.255.255.0. to destination: select to destination subnet / mask. to destination subnet / mask: enter 192.168.1...
Page 156
Step 3.Enter the following setting in outgoing policy: (figure11-48) authentication user: select all_net. schedule: select schedule_1. qos: select qos_1. tunnel: select pptp_vpn_tunnel. click ok.(figure11-49) figure11-48 setting the vpn tunnel outgoing policy figure11-49 complete the vpn tu...
Page 157
Step 4.Enter the following setting in incoming policy: (figure11-50) schedule: select schedule_1. qos: select qos_1. tunnel: select pptp_vpn_tunnel. click ok.(figure11-51) figure11-50 setting the vpn tunnel incoming policy figure11-51 complete the vpn tunnel incoming policy setting 157.
Page 158
158 ) step 5.Complete pptp vpn connection. (figure11-52 figure 11-52 pptp vpn connection deployment.
Page 159: Chapter 12 Policy
Chapter 12 policy policy every packet has to be detected if it corresponds with policy or not when it passes the mh350. When the conditions correspond with certain policy, it will pass the mh350 by the setting of policy without being detected by other policy. But if the packet cannot correspond with...
Page 160
(4) lan to dmz: the source ip is in lan network; the destination is in dmz network. The system manager can set all the policy rules of lan to dmz packets in this function (5) dmz to lan: the source ip is in dmz network; the destination is in lan network. The system manager can set all the policy rul...
Page 161
Define the required fields of policy source and destination: source ip and destination ip is according to the mh350’s point of view. The active side is the source; passive side is destination. Service: it is the service item that controlled by policy. The user can choose default value or the cus...
Page 162
Option: to display if every function of policy is enabled or not. If the function is enabled and then the chart of the function will appear (see the chart and illustration below) chart name illustration traffic log enable traffic log statistics enable traffic statistics authentication user enable ...
Page 163
163 max. Concurrent sessions: set the concurrent sessions that permitted by policy. And if the sessions exceed the setting value, the surplus connection cannot be set successfully. Qos: setting the guarantee bandwidth and maximum bandwidth of the policy (the bandwidth is shared by the users who ...
Page 164
164 we set up six policy examples in this chapter: no. Suitable situation example page ex1 outgoing set up the policy that can monitor the internal users. (take logging, statistics, alarm threshold for example) 163 ex2 outgoing forbid the users to access to specific network. (take specific wan ip an...
Page 165: Example
Example set up the policy that can monitor the internal users. (take logging, statistics, and alarm threshold for example) step 1﹒enter the following setting in outgoing policy: click new entry select logging select statistics click ok (figure12-1) figure12-1 setting the different policies 1...
Page 166
Step 2﹒complete the setting of logging, statistics, and alarm threshold in outgoing policy: (figure12-2) figure12-2 complete policy setting step 3﹒obtain the information in traffic of log functionif you want to monitor all the packets of the mh350. (figure12-3) figure12-3 traffic log monitor webui 1...
Page 167
Step 4﹒to display the traffic record that through policy to access to internet in policy statistics of statistics function. (figure12-4) figure12-4 statistics webui 167.
Page 168
Forbid the users to access to specific network. (take specific wan ip and content blocking for example) step 1﹒enter the following setting in url blocking, script blocking, p2p blocking, im blocking, and download blocking in content blocking function: (figure12-5, 12-6, 12-7, 12-8, 12-9) figure12-5 ...
Page 169
Figure12-8 im blocking setting figure12-9 download blocking setting 1. Url blocking can restrict the internal users only can access to some specific website. 2. Script blocking can restrict the internal users to access to script file of website. (java, cookies…etc.) 3. P2p blocking can restrict the ...
Page 170
Step 2﹒enter as following in wan and wan group of address function: (figure12-10, 12-11) figure12-10 setting the wan ip that going to block figure12-11 wan address group the administrator can group the custom address in address. It is more convenient when setting policy rule. 170
Page 171
Step 3﹒enter the following setting in outgoing policy: click new entry destination address: select wan_group that set by step 2. (blocking by ip) action, wan port: select deny click ok (figure12-12) figure12-12 setting blocking policy 171.
Page 172
Step 4﹒enter the following setting in outgoing policy: click new entry select content blocking click ok (figure12-13) figure12-13 setting content blocking policy step 5﹒complete the setting of forbidding the users to access to specific network. (figure12-14) figure12-14 complete policy setting...
Page 173
Only allow the users who pass authentication to access to internet in particular time step 1﹒enter the following in schedule function: (figure12-15) figure12-15 add new schedule step 2﹒enter the following in auth user and auth user group in authentication function: (figure12-16) figure12-16 setting ...
Page 174
Step 3﹒enter the following setting in outgoing policy: click new entry authentication user: select laboratory schedule: select workingtime click ok (figure12-17) figure12-17 setting a policy of authentication and schedule step 4﹒complete the policy rule of only allows the users who pass auth...
Page 175
The external user control the internal pc through remote control software (take pcanywhere for example) step 1﹒set up a internal pc controlled by external user, and internal pc’s ip address is 192.168.1.2 step 2﹒enter the following setting in virtual server1 of virtual server function: (figure12-19)...
Page 176
Step 3﹒enter the following in incoming policy: click new entry destination address: select virtual server1 (61.11.11.12) service: select pc-anywhere (5631-5632) click ok (figure12-20) figure12-20 setting the external user control the internal pc policy step 4﹒complete the policy for the exte...
Page 177
Set a ftp server under dmz nat mode and restrict the download bandwidth from external and max. Concurrent sessions. Step 1﹒set a ftp server under dmz, which ip is 192.168.3.2 (the dmz interface address is192.168.3.1/24) step 2﹒enter the following setting in virtual server1 of virtual server function...
Page 178
Step 4﹒enter the following in wan to dmz policy: click new entry destination address: select virtual server1 (61.11.11.12) service: select ftp (21) qos: select ftp_qos max. Concurrent sessions: enter 100 click ok (figure12-24) figure12-24 add new policy step 5﹒complete the policy of rest...
Page 179
Set a mail server to allow the internal and external users to receive and send e-mail under dmz transparent mode step 1﹒set a mail server in dmz and set its network card’s ip address as 61.11.11.12. The dns setting is external dns server. Step 2﹒add the following setting in dmz of address function: ...
Page 180
Step 4﹒enter the following setting in wan to dmz policy: click new entry destination address: select mail_server service: select e-mail click ok (figure12-28) figure12-28 setting a policy to access mail service by wan to dmz step 5﹒complete the policy to access mail service by wan to dmz. (f...
Page 181
Step 6﹒add the following setting in lan to dmz policy: click new entry destination address: select mail_server service: select e-mail click ok (figure12-30) figure12-30 setting a policy to access mail service by lan to dmz step 7﹒complete the policy to access mail service by lan to dmz (figu...
Page 182
Step 8﹒add the following setting in dmz to wan policy: click new entry source address: select mail_server service: select e-mail click ok (figure12-32) figure12-32 setting the policy of mail service by dmz to wan step 9﹒complete the policy access to mail service by dmz to wan. (figure12-33) ...
Page 183: Alert Setting
183 chapter 13 alert setting alert setting when the mh350 had detected attacks from hackers and the internal pc sending large ddos attacks. The internal alert and external alert will start on blocking these packets to maintain the whole network. In this chapter, we will have the detailed illustratio...
Page 184
184 define the required fields of hacker alert detect syn attack: select this option to detect tcp syn attacks that hackers send to server computers continuously to block or cut down all the connections of the servers. These attacks will cause valid users cannot connect to the servers. 【syn floo...
Page 185
185 administrator can enter the maximum number of icmp packets per second from attacking source ip address that is allow to enter the network / mh350. If the value exceeds the setting one, and then the device will determine it as an attack. 【icmp flood threshold blocking time(per source ip)seconds...
Page 186
186 detect ping of death attack: select this option to detect the attacks of tremendous trash data in ping packets that hackers send to cause system malfunction. This attack can cause network speed to slow down, or even make it necessary to restart the computer to get a normal operation. Detect ip...
Page 187
Detect land attack: some systems may shut down when receiving packets with the same source and destination addresses, the same source port and destination port, and when syn on the tcp header is marked. Enable this function to detect such abnormal packets. After system manager enable external aler...
Page 188: Internet Alert
Internet alert mh350 alarm and to prevent the computer which being attacked to send ddos packets to lan network step 1﹒select internal alert in alert setting and enter the following settings: enter the threshold sessions of infected blaster (per source ip) (the default value is 30 sessions/sec) ...
Page 189
After complete the internal alert settings, if the device had detected the internal computer sending large ddos attack packets and then the alarm message will appear in the internal alarm in attack alarm or send netbios alert notification to the infected pc administrator’s pc (figure16-2, 16-3, 16-4...
Page 190
Figure16-4 netbios alert notification to administrator’s pc 190
Page 191
Figure16-5 e-mail virus alert 191.
Page 192: Attack Alarm
Chapter 14 attack alarm attack alarm mh350 has two alarm forms: internal alarm, and external alarm. Internal alarm: when the mh350 had detected the internal pc sending large ddos attacks and then the internal alarm will start on blocking these packets to maintain the whole network. External alarm: w...
Page 193
193 we set up two alarm examples in the chapter: no. Suitable situation example page ex 1 internal alarm to record the ddos attack alarm from internal pc 192 ex 2 external alarm to record the attack alarm about hacker attacks the mh350 and intranet 193.
Page 194: Internal Alarm
Internal alarm to record the ddos attack alarm from internal pc step 1﹒select internal alarm in attack alarm when the device detects ddos attacks, and then can know which computer is being affected. (figure17-1) figure17-1 internal alarm webui 194.
Page 195: External Alarm
External alarm to record the attack alarm about hacker attacks the mh350 and intranet step 1﹒select the following settings in external alert in alert setting function: (figure17-2) figure17-2 external alert setting webui 195.
Page 196
Step 2﹒when hacker attacks the mh350 and intranet, select external alarm in attack alarm function to have detailed records about the hacker attacks. (figure17-3) figure17-3 external alarm webui 196.
Page 197: Chapter 15 Log
Chapter 15 log log log records all connections that pass through the mh350’s control policies. The information is classified as traffic log, event log, and connection log. Traffic log’s parameters are setup when setting up policies. Traffic logs record the details of packets such as the start and st...
Page 198
198 we set up four log examples in the chapter: no. Suitable situation example page ex 1 traffic log to detect the information and protocol port that users use to access to internet or intranet by mh350. 197 ex 2 event log to record the detailed management events (such as interface and event descrip...
Page 199: Traffic Log
Traffic log to detect the information and protocol port that users use to access to internet or intranet by mh350 step 1﹒add new policy in dmz to wan of policy and select enable logging: (figure18-1) figure18-1 logging policy setting step 2﹒complete the logging setting in dmz to wan policy: (figrue1...
Page 200
Step 3﹒click traffic log. It will show up the packets records that pass this policy. (figure18-3) figure18-3 traffic log webui 200
Page 201
Step 4﹒click on a specific ip of source ip or destination ip in figure18-3, it will prompt out a webui about protocol and port of the ip. (figure18-4) figure18-4 the webui of detecting the traffic log by ip address 201.
Page 202
Step 5﹒click on download logs and select save in file download webui. And then choose the place to save in pc and click ok; the records will be saved instantly. (figure18-5) figure18-5 download traffic log records webui 202.
Page 203
Step 6﹒click clear logs and click ok on the confirm webui; the records will be deleted from the mh350 instantly. (figure18-6) figure18-6 clearing traffic log records webui 203.
Page 204: Event Log
Event log to record the detailed management events (such as interface and event description of mh350) of the administrator step 1﹒click event log of log. The management event records of the administrator will show up (figure18-7) figure18-7 event log webui 204.
Page 205
Step 2﹒click on download logs and select save in file download webui. And then choose the place to save in pc and click ok; the records will be saved instantly. (figure18-8) figure18-8 download event log records webui 205.
Page 206
Step 3﹒click clear logs and click ok on the confirm webui; the records will be deleted from the mh350. (figure18-9) figure18-9 clearing event log records webui 206.
Page 207: Connection Log
Connection log to detect event description of wan connection step 1﹒click connection in log. It can show up wan connection records of the mh350. (figure18-10) figure18-10 connection records webui 207.
Page 208
Step 2﹒click on download logs and select save in file download webui. And then choose the place to save in pc and click ok; the records will be saved instantly. (figure18-11) figure18-11 download connection log records webui 208.
Page 209
Step 3﹒click clear logs and click ok on the confirm webui, the records will be deleted from the mh350 instantly. (figure18-12) figure18-12 clearing connection log records webui 209.
Page 210: Log Backup
Log backup to save or receive the records that sent by the mh350 step 1﹒enter setting in system, select enable e-mail alert notification function and set up the settings. (figrue18-13) figure18-13 e-mail setting webui step 2﹒enter log backup in log, select enable log mail support and click ok (figur...
Page 211
Step 3﹒enter log backup in log, enter the following settings in syslog settings: select enable syslog messages enter the ip in syslog host ip address that can receive syslog enter the receive port in syslog host port click ok complete the setting (figure18-15) figure18-15 syslog messages s...
Page 212: Accounting Report
212 chapter 16 accounting report accounting report administrator can use this accounting report to inquire the lan ip users and wan ip users, and to gather the statistics of downstream/upstream, first packet/last packet/duration and the service of all the user’s ip that passes the mh350..
Page 213
Define the required fields of accounting report accounting report setting: by accounting report function can record the sending information about intranet and the external pc via mh350. Accounting report can be divided into two parts: outbound accounting report and inbound accounting report outbou...
Page 214
Inbound accounting report it is the statistics of downstream / upstream for all kinds of communication services; the inbound accounting report will be shown when wan user uses mh350 to connect to lan service server. Source ip: the ip address used by wan users who use mh350 destination ip: the ip...
Page 215: Outbound
215 outbound step 1﹒enter outbound in accounting report and select top users to inquire the statistics of send / receive packets, downstream / upstream, first packet/last packet/duration and the service from the lan or dmz user’s ip that pass the mh350. (figure19-1) top: select the data you want to ...
Page 216
Figure19-1 outbound source ip statistics report 216.
Page 217
217 step 2 ﹒enter outbound in accounting report and select top sites to inquire the statistics website of send/receive packets, downstream/upstream, first packet/last packet/duration and the service from the wan server to pass the mh350. (figure19-2) top:select the data you want to view, it presen...
Page 218
Figure19-2 outbound destination ip statistics report 218.
Page 219
Step 3﹒enter outbound in accounting report and select top services to inquire the statistics website of send / receive packets, downstream/upstream, first packet/last packet/duration and the service from the wan server to pass the mh350. (figure19-3) top:select the data you want to view. It presen...
Page 220
Figure19-3 outbound services statistics report figure19-4 according to the downstream / upstream report of the selected top numbering to draw the protocol distribution chart press to return to accounting report window. 220
Page 221: Inbound
221 inbound step 1﹒enter inbound in accounting report and select top users to inquire the statistics website of send / receive packets, downstream / upstream, first packet/last packet / duration and the service from the wan user to pass the mh350. (figure19-5) top:select the data you want to view....
Page 222
Figure19-5 inbound top users statistics report 222.
Page 223
223 enter inbound in accounting report and select top sites to inquire the statistics website of send / receive packets, downstream / upstream, first packet/last packet / duration and the service from the wan user to pass the mh350. (figure19-6) top:select the data you want to view. It presents 10...
Page 224
Figure19-6 inbound destination ip statistics report 224.
Page 225
Step 2﹒enter inbound in accounting report and select top services to inquire the statistics website of send/receive packets, downstream/upstream, first packet/last packet/duration and the service from the wan server to pass the mh350. (figure19-7) top:select the data you want to view. It presents ...
Page 226
Figure19-7 inbound services statistics report figure19-8 according to the downstream / upstream report of the selected top numbering to draw the protocol distribution chart 226.
Page 227: Chapter 17 Statistics
227 chapter 17 statistics statistics wan statistics: the statistics of downstream / upstream packets and downstream/upstream traffic record that pass wan interface policy statistics: the statistics of downstream / upstreampackets and downstream/upstream traffic record that pass policy in this chapte...
Page 228
228 define the required fields of statistics: statistics chart: y-coordinate:network traffic(kbytes/sec) x-coordinate:time(hour/minute) source ip, destination ip, service, and action: these fields record the original data of policy. From the information above, the administrator can know which ...
Page 229: Wan Statistics
Wan statistics step 1﹒enter wan in statistics function, it will display all the statistics of downstream/upstream packets and downstream/upstream record that pass wan interface. (figure20-1) figure20-1 wan statistics function time: to detect the statistics by minutes, hours, days, months, or years...
Page 230
Step 3﹒statistics chart (figure20-2) y-coordinate:network traffic(kbytes/sec) x-coordinate:time(hour/minute) figure20-2 to detect wan statistics 230
Page 231: Policy Statistics
Policy statistics step 1﹒if you had select statistics in policy, it will start to record the chart of that policy in policy statistics. (figure20-3) figure20-3 policy statistics function if you are going to use policy statistics function, the system manager has to enable the statistics in policy fir...
Page 232
Step 3﹒statistics chart (figure20-4) y-coordinate:network traffic(kbytes/sec) x-coordinate:time(hour/minute/day) figure20-4 to detect policy statistics 232.
Page 233: Chapter 18 Status
233 chapter 18 status status the users can know the connection status in status. For example: lan ip, wan ip, subnet netmask, default gateway, dns server connection, and its ip…etc. interface: display all of the current interface status of the mh350 authentication: the authentication information...
Page 234: Interface
234 interface step 1﹒enter interface in status function; it will list the setting for each interface: (figure21-1) pppoe con. Time: the last time of the mh350 to be enabled mac address: the mac address of the interface ip address/ netmask: the ip address and its netmask of the interface rx p...
Page 235
Figure21-1 interface status 235.
Page 236: Authentication
Authentication step 1 ﹒enter authentication in status function, it will display the record of login status: (figure21-2) ip address: the authentication user ip auth-user name: the account of the auth-user to login login time: the login time of the user (year/month/day hour/minute/second) figru...
Page 237: Arp Table
Arp table step 1﹒enter arp table in status function; it will display a table about ip address, mac address, and the interface information which is connecting to the mh350: (figure21-3) netbios name: the identified name of the network ip address: the ip address of the network mac address: the i...
Page 238: Dhcp Clients
Dhcp clients step 1 ﹒in dhcp clients of status function, it will display the table of dhcp clients that are connected to the mh350: (figure21-4) ip address: the dynamic ip that provided by dhcp server mac address: the ip that corresponds to the dynamic ip 238 leased time: the valid time of the...