- DL manuals
- IBM
- Server
- Novell 10 SP1 EAL4
- Design Manual
IBM Novell 10 SP1 EAL4 Design Manual
Summary of Novell 10 SP1 EAL4
Page 1
Suse linux enterprise server 10 sp1 eal4 high-level design version 1.2.1.
Page 2
Version author date comments 1.0 ejr 3/15/07 first draft based on rhel5 hld 1.1 ejr 4/19/07 updates based on comments from stephan mueller and klaus weidner 1.2 gcw 4/26/07 incorporated stephan's comment to remove racoon 1.2.1 gcw 10/27/08 added legal matter missing from final draft. Novell, the nov...
Page 3: Table Of Contents
Table of contents 1 introduction....................................................................................................................................................1 1.1 purpose of this document.............................................................................................
Page 4
4.1.2.1 dac....................................................................................................................................25 4.1.2.2 apparmor............................................................................................................................26 4.1.2.3 pro...
Page 5
5.1.5 discretionary access control (dac)..........................................................................................55 5.1.5.1 permission bits.....................................................................................................................56 5.1.5.2 access control l...
Page 6
5.3.3.2 common functions...............................................................................................................76 5.3.3.3 message queues....................................................................................................................77 5.3.3.4 semaphores......
Page 7
5.5.3 kernel memory management....................................................................................................142 5.5.3.1 support for numa servers................................................................................................142 5.5.3.2 reverse map virtual memory...
Page 8
5.8.3 securityfs....................................................................................................................................174 5.9 device drivers.....................................................................................................................................
Page 9
5.11.3.1 agetty................................................................................................................................203 5.11.3.2 gpasswd............................................................................................................................203 5.11.3.3 ...
Page 10
5.13.3.2 groupmod.........................................................................................................................232 5.13.3.3 groupdel...........................................................................................................................232 5.13.4 system ...
Page 11
6.1 identification and authentication.......................................................................................................251 6.1.1 user identification and authentication data management (ia.1).................................................251 6.1.2 common authentication mechanis...
Page 12
6.8 security enforcing interfaces between subsystems.............................................................................255 6.8.1 summary of kernel subsystem interfaces ..................................................................................256 6.8.1.1 kernel subsystem file and i/...
Page 13: 1 Introduction
1 introduction this document describes the high level design (hld) for the suse® linux® enterprise server 10 service pack 1 operating system. For ease of reading, this document uses the phrase suse linux enterprise server and the abbreviation sles as a synonym for suse linux enterprise server 10 sp1...
Page 14: 2 System Overview
2 system overview the target of evaluation (toe) is suse linux enterprise server (sles) running on an ibm eserver host computer. The sles product is available on a wide range of hardware platforms. This evaluation covers the sles product on the ibm eserver system x™, system p™, and system z™, and es...
Page 15
The toe system provides user identification and authentication (i&a) mechanism by requiring each user to log in with proper password at the local workstation, and also at any remote computer where the user can enter commands to a shell program (for example, remote ssh sessions). Each computer enforc...
Page 16
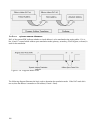
The common criteria for information technology security evaluation [cc] and the common methodology for information technology security evaluation [cem] demand breaking the toe into logical subsystems that can be either (a) products, or (b) logical functions performed by the system. The approach in t...
Page 17
The sles kernel includes the base kernel and separately-loadable kernel modules and device drivers. (note that a device driver can also be a kernel module.) the kernel consists of the bootable kernel image and its loadable modules. The kernel implements the system call interface, which provides syst...
Page 18
2.2.2 eserver system structure the system is an eserver computer, which permits one user at a time to log in to the computer console. Several virtual consoles can be mapped to a single physical console. Different users can login through different virtual consoles simultaneously. The system can be co...
Page 19
Network services, such as ssh or ftp, involve client-server architecture and a network service-layer protocol. The client-server model splits the software that provides a service into a client portion that makes the request, and a server portion that carries out the request, usually on a different c...
Page 20
Objects are passive repositories of data. The toe defines three types of objects: named objects, storage objects, and public objects. Named objects are resources, such as files and ipc objects, which can be manipulated by multiple users using a naming convention defined at the tsf interface. A stora...
Page 21
The local tsf interfaces provided by an individual host computer include: • files that are part of the tsf database that define the configuration parameters used by the security functions. • system calls made by trusted and untrusted programs to the privileged kernel-mode software. As described sepa...
Page 22
The sles operating system is distributed as a collection of packages. A package can include programs, configuration data, and documentation for the package. Analysis is performed at the file level, except where a particular package can be treated collectively. A file is included in the tsf for one o...
Page 23
11.
Page 24: 3 Hardware Architecture
3 hardware architecture the toe includes the ibm system x, system p, system z, and eserver 326. This section describes the hardware architecture of these eserver systems. For more detailed information about linux support and resources for the entire eserver line, refer to http://www.Ibm.Com/systems/...
Page 25
In this mode, applications may access: • 64-bit flat linear addressing • 8 new general-purpose registers (gprs) • 8 new registers for streaming single instruction/multiple data (simd) extensions (sse, sse2 and sse3) • 64-bit-wide gprs and instruction pointers • uniform byte-register addressing • fas...
Page 26
Usb (except keyboard and mouse), pcmcia, and ieee 1394 (firewire) devices are not supported in the evaluated configuration. 3.3 system z the ibm system z is designed and optimized for high-performance data and transaction serving requirements. On a system z system, linux can run on native hardware, ...
Page 27
For more details about z/architecture, refer to the z/architecture document z/architecture principles of operation at http://publibz.Boulder.Ibm.Com/epubs/pdf/dz9zr002.Pdf . Usb (except keyboard and mouse), pcmcia, and ieee 1394 (firewire) devices are not supported in the evaluated configuration. 3....
Page 28
Processor extensions are activated, allowing the processor to operate in one of two sub-modes of lma. These are the 64-bit mode and the compatibility mode. • 64-bit mode: in 64-bit mode, the processor supports 64-bit virtual addresses, a 64-bit instruction pointer, 64-bit general-purpose registers, ...
Page 29
17.
Page 30: 4 Software Architecture
4 software architecture this chapter summarizes the software structure and design of the sles system and provides references to detailed design documentation. The following subsections describe the toe security functions (tsf) software and the tsf databases for the sles system. The descriptions are ...
Page 31
System x: the system x servers are powered by intel processors. Intel processors provide four execution modes, identified with processor privilege levels 0 through 3. The highest privilege level execution mode corresponds to processor privilege level 0; the lowest privilege level execution mode corr...
Page 32
• when the processor is in kernel mode, the program has hardware privilege because it can execute certain privileged instructions that are not available in user mode. Thus, any code that runs in kernel mode executes with hardware privileges. Software that runs with hardware privileges includes: • th...
Page 33
4.1.2.1 dac the dac model allows the owner of the object to decide who can access that object, and in what manner. Like any other access control model, dac implementation can be explained by which subjects and objects are under the control of the model, security attributes used by the model, access ...
Page 34
4.1.2.3 programs with software privilege examples of programs running with software privilege are: • programs that are run by the system, such as the cron and init daemons. • programs that are run by trusted administrators to perform system administration. • programs that run with privileged identit...
Page 35
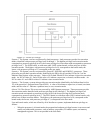
The concept of breaking the toe product into logical subsystems is described in the common criteria. These logical subsystems are the building blocks of the toe, and are described in the functional descriptions chapter of this paper. They include logical subsystems and trusted processes that impleme...
Page 36
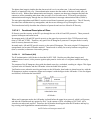
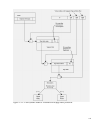
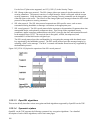
4.2.1.1 logical components the kernel consists of logical subsystems that provide different functionalities. Even though the kernel is a single executable program, the various services it provides can be broken into logical components. These components interact to provide specific functions. Figure ...
Page 37
• audit subsystem: this subsystem implements functions related to recording of security-critical events on the system. Implemented functions include those that trap each system call to record security critical events and those that implement the collection and recording of audit data. 4.2.1.2 execut...
Page 38
4.2.1.2.3 kernel modules and device drivers kernel modules are pieces of code that can be loaded and unloaded into and out of the kernel upon demand. They extend the functionality of the kernel without the need to reboot the system. Once loaded, the kernel module object code can access other kernel ...
Page 39
• the crontab program is the program used to install, deinstall, or list the tables used to drive the cron daemon. Users can have their own crontab files that set up the time and frequency of execution, as well as the command or script to execute. • the gpasswd command administers the /etc/group fil...
Page 40
• the chfn command allows users to change their finger information. The finger command displays that information, which is stored in the /etc/passwd file. • the date command is used to print or set the system date and time. Only an administrative user is allowed to set the system date and time. • th...
Page 41
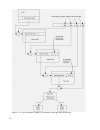
This section briefly describes the functional subsystems that implement the required security functionalities and the logical subsystems that are part of each of the functional subsystems. The subsystems are structured into those implemented within the sles kernel, and those implemented as trusted p...
Page 42
• gpasswd • chage • useradd, usermod, userdel • groupadd, groupmode, groupdel • chsh • chfn • openssl 4.4.5 user-level audit subsystem this subsystem contains the portion of the audit system that lies outside the kernel. This subsystem contains the auditd trusted process, which reads audit records f...
Page 43
31.
Page 44
5 functional descriptions the kernel structure, its trusted software, and its target of evaluation (toe) security functions (tsf) databases provide the foundation for the descriptions in this chapter. 5.1 file and i/o management the file and i/o subsystem is a management system for defining objects ...
Page 45
In order to shield user programs from the underlying details of different types of disk devices and disk-based file systems, the sles kernel provides a software layer that handles all system calls related to a standard unix file system. This common interface layer, called the virtual file system, in...
Page 46
The root directory is contained in the root file system, which is ext3 in this toe. All other file systems can be mounted on subdirectories of the root file system. The vfs allows programs to perform operations on files without having to know the implementation of the underlying disk-based file syst...
Page 47
Inode: stores general information about a specific file, such as file type and access rights, file owner, group owner, length in bytes, operations vector, time of last file access, time of last file write, and time of last inode change. An inode is associated to each file and is described in the ker...
Page 48
Figure 5-5 vfs pathname translation and access control checks 36 figure 5-5: vfs pathname translation and access control checks.
Page 49
5.1.1.2 open() the following describes the call sequence of an open() call to create a file: 1. Call the open() system call with a relative pathname and flags to create a file for read and write. 2. Open() calls open_namei(), which ultimately derives the dentry for the directory in which the file is...
Page 50
5.1.1.3 write() another example of a file system operation is a write() system call to write to a file that was opened for writing. The write() system call in vfs is very straightforward, because access checks have already been performed by open(). The following list shows the call sequence of a wri...
Page 51
• unbindable mount: this mount does not forward or receive propagation. This mount type can not be bind-mounted, and it is not valid to move it under a shared mount. • slave mount: a slave mount remains tied to its parent mount and receives new mount or unmount events from there. The mount or unmoun...
Page 52
5.1.2.1.1.1 access control lists acls provide a way of extending directory and file access restrictions beyond the traditional owner, group, and world permission settings. For more details about the acl format, refer to discretionary access control, section 5.1.5, of this document, and section 6.2.4...
Page 53
• ext3_group_desc: disk blocks are partitioned into groups. Each group has its own group descriptor. Ext3_group_desc stores information such as the block number of the inode bitmap, and the block number of the block bitmap. • ext3_inode: the on-disk counterpart of the inode structure of vfs, ext3_in...
Page 54
42 figure 5-8: new data blocks are allocated and initialized for an ext3 field.
Page 55
Figure 5-9 shows how for a file on the ext3 file system, inode_operations map to ext3_file_inode_operations. Similarly, for directory, symlink, and special-file types of objects, inode operations map to ext3_dir_inode_operations, ext3_symlink_inode_operations, and ext3_special_inode_operations, resp...
Page 56
From the superblock’s s_root field of the superblock, and then invokes isofs_find_entry() to retrieve the object from the cd-rom. On a cd-rom file system, inode_operations map to isofs_dir_inode_operations. 5.1.3 pseudo file systems 5.1.3.1 procfs the proc file system is a special file system that a...
Page 57
Since vm is volatile in nature, tmpfs data is not preserved between reboots. Hence this file system is used to store short-lived temporary files. An administrator is allowed to specify the memory placement policies (the policy itself and the preferred nodes to be allocated) for this file system. 5.1...
Page 58
5.1.3.6 binfmt_misc binfmt_misc provides the ability to register additional binary formats to the kernel without compiling an additional module or kernel. Therefore, binfmt_misc needs to know magic numbers at the beginning, or the filename extension of the binary. Binfmt_misc works by maintaining a ...
Page 59
Chown() system call. The owner and the root user are allowed to define and change access rights for an object. This following subsection looks at the kernel functions implementing the access checks. The function used depends on the file system; for example, vfs_permission() invokes permission() whic...
Page 60
• if the process is neither the owner nor a member of an appropriate group, and the permission bits for world allow the type of access requested, then the subject is permitted access. • if none of the conditions above are satisfied, and the effective uid of the process is not zero, then the access a...
Page 61
5.1.5.2.3 acl permissions an acl entry can define separate permissions for read, write, and execute or search. 5.1.5.2.4 relationship to file permission bits an acl contains exactly one entry for each of the acl_user_obj, acl_group_obj, and acl_other types of tags, called the required acl entries. A...
Page 62
5.1.5.2.8 acl enforcement the ext3_permission() function uses acls to enforce dac. The algorithm goes through the following steps: 1. Performs checks such as “no write access if read-only file system” and “no write access if the file is immutable.” 2. For ext3 file systems, the kernel calls the ext3...
Page 63
File by adding acls with the setfacl command. For example, the following command allows a user named john read access to this file, even if john does not belong to the root group. #setfacl –m user:john:4,mask::4 /aclfile the acl on file will look like: # owner: root # group: root user:: rw- user:joh...
Page 64
Application, the i/o scheduler is considered an important kernel component in the i/o path. Sles includes four i/o scheduler options to optimize system performance. 5.1.7.1 deadline i/o scheduler the deadline i/o scheduler available in the linux 2.6 kernel incorporates a per-request expiration-based...
Page 65
Requests. This capability makes it behaves similarly to the anticipatory i/o scheduler. I/o priorities are also considered for the processes, which are derived from their cpu priority. 5.1.7.4 noop i/o scheduler the noop i/o scheduler can be considered as a rather minimal i/o scheduler that performs...
Page 66
5.1.8.4 tasklets tasklets are dynamically linked and built on top of softirq mechanisms. Tasklets differ from softirqs in that a tasklet is always serialized with respect to itself. In other words, a tasklet cannot be executed by two cpus at the same time. However, different tasklets can be executed...
Page 67
5.2 process control and management a process is an instance of a program in execution. Process management consists of creating, manipulating, and terminating a process. Process management is handled by the process management subsystems of the kernel. The kernel interacts with the memory subsystem, t...
Page 68
The sles kernel maintains information about each process in a task_struct process type of descriptor. Each process descriptor contains information such as run-state of process, address space, list of open files, process priority, which files the process is allowed to access, and security relevant cr...
Page 69
Figure 5-12: the task structure the kernel maintains a circular doubly-linked list of all existing process descriptors. The head of the list is the init_task descriptor referenced by the first element of the task array. The init_task descriptor belongs to process 0 or the swapper, the ancestor of al...
Page 70
5.2.2.2.4 setresuid()and setresgid() these set the real user and group id, the effective user and group id, and the saved set-user and group id of the current process. Normal user processes (that is, processes with real, effective, and saved user ids that are nonzero) may change the real, effective,...
Page 71
5.2.5 scheduling scheduling is one of the features that is highly improved in the sles 2.6 kernel over the 2.4 kernel. It uses a new scheduler algorithm, called the o (1) algorithm, that provides greatly increased scheduling scalability. The o (1) algorithm achieves this by taking care that the time...
Page 72
For more information about hyperthreading, refer to http://www.Intel.Com/technology/hyperthread/ . 5.2.6 kernel preemption the kernel preemption feature has been implemented in the linux 2.6 kernel. This should significantly lower latency times for user-interactive applications, multimedia applicati...
Page 73
The following code snippet demonstrates the per-cpu data structure problem, in an smp system: int arr[nr_cpus]; arr[smp_processor_id()] = i; /* kernel preemption could happen here */ j = arr[smp_processor_id()]; /* i and j are not equal as smp_processor_id() may not be the same */ in this situation,...
Page 74
5.3.1 pipes pipes allow the transfer of data in a fifo manner. The pipe() system call creates unnamed pipes. Unnamed pipes are only accessible to the creating process and its descendants through file descriptors. Once a pipe is created, a process may use the read() and write() vfs system calls to ac...
Page 75
Pipe_inode_info: contains generic state information about the pipe with fields such as base (which points to the kernel buffer), len (which represents the number of bytes written into the buffer and yet to be read), wait (which represents the wait queue), and start (which points to the read position...
Page 76
The inode allocation routine of the disk-based file system does the allocation and initialization of the inode object; thus, object reuse is handled by the disk-based file system. 5.3.2.2 fifo open a call to the open() vfs system call performs the same operation as it does for device special files. ...
Page 77
• ipc_id: the ipc_id data structure describes the security credentials of an ipc resource with the p field, which is a pointer to the credential structure of the resource. • kern_ipc_perm: the kern_ipc_perm data structure is a credential structure for an ipc resource with fields such as key, uid, gi...
Page 78
5.3.3.3.3 msgget() this function is invoked to create a new message queue, or to get a descriptor of an existing queue based on a key. The newly created credentials of the message queue are initialized from the credentials of the creating process. 5.3.3.3.4 msgsnd() this function is invoked to send ...
Page 79
5.3.3.4.4 semctl() a function that is invoked to set attributes, query status, or delete a semaphore. A semaphore is not deleted until the process waiting for a semaphore has received it. Dac is performed by invoking the ipcperms() function. 5.3.3.5 shared memory regions shared memory regions allow ...
Page 80
5.3.4 signals signals offer a means of delivering asynchronous events to processes. Processes can send signals to each other with the kill() system call, or the kernel can internally deliver the signals. Events that cause a signal to be generated include keyboard interrupts via the interrupt, stop, ...
Page 81
Specifying the target address of the server. For an internet domain socket, the address of the server is its ip address and its port number. Sockets are created using the socket() system call. Depending on the type of socket, either unix domain or internet domain, the socket family operations vector...
Page 82
• the protocol-independent interface module provides an interface that is independent of hardware devices and network protocol. This is the interface module that is used by other kernel subsystems to access the network without having a dependency on particular protocols or hardware. Finally, the sys...
Page 83
The transport layer consists of the tcp, udp and similar protocols. The application layer consists of all the various application clients and servers, such as the samba file and print server, the apache web server, and others. Some of the application-level protocols include telnet, for remote login;...
Page 84
5.4.2 transport layer protocols the transport layer protocols supported by the sles kernel are tcp and udp. 5.4.2.1 tcp tcp is a connection-oriented, end-to-end, reliable protocol designed to fit into a layered hierarchy of protocols that support multi-network applications. Tcp provides for reliable...
Page 85
The following section introduces internet protocol version 6 (ipv6). For additional information about referenced socket options and advanced ipv6 applications, see rfc 3542. Internet protocol version 6 (ipv6) was designed to improve upon and succeed internet protocol version 4 (ipv4). Ipv4 addresses...
Page 86
5.4.3.2.3 flow labels the ipv6 header has a field to in which to enter a flow label. This provides the ability to identify packets for a connection or a traffic stream for special processing. 5.4.3.2.4 security the ipv6 specifications mandate ip security. Ip security must be included as part of an i...
Page 87
The phrase data integrity implies that the data received is as it was when sent. It has not been tampered, altered, or impaired in any way. Data authentication ensures that the sender of the data is really who you believe it to be. Without data authentication and integrity, someone can intercept a d...
Page 88
In tunnel mode, the entire ip datagram is encapsulated, protecting the entire ip datagram. An ip packet with tunnel mode ah 5.4.3.4.1.2 encapsulating security payload protocol (esp) the encapsulating security payload (esp) header is defined in rfc 2406. Besides data confidentiality, esp also provide...
Page 89
An ip packet with tunnel mode esp 5.4.3.4.1.3 security associations rfc2401 defines a security association (sa) as a simplex or one-way connection that affords security services to the traffic it carries. Separate sas must exist for each direction. Ipsec stores the sas in the security association da...
Page 90
5.4.3.4.1.8 cryptographic subsystem ipsec uses the cryptographic subsystem described in this section. The cryptographic subsystem performs several cryptographic-related assignments, including digital signature algorithm (dsa) signature verification, in-kernel key management, arbitrary-precision inte...
Page 91
5.4.4.1.1 address resolution protocol (arp) address resolution protocol (arp) is a protocol for mapping an ip address to a physical machine address that is recognized in the local network. For example, in ip version 4, the most common level of ip in use today, an address is 32 bits long. In an ether...
Page 92
The following subsections describe access control and object reuse handling associated with establishing a communications channel. 5.4.5.1 socket() socket() creates an endpoint of communication using the desired protocol type. Object reuse handling during socket creation is described in section 5.3....
Page 93
Similarly, for unix domain sockets, bind() invokes unix_bind(). Unix_bind() creates an entry in the regular ext3 file system space. This process of creating an entry for a socket in the regular file system space has to undergo all file system access control restrictions. The socket exists in the reg...
Page 94
5.4.5.6 generic calls read(), write() and close(): read(), write() and close() are generic i/o system calls that operate on a file descriptor. Depending on the type of object, whether regular file, directory, or socket, appropriate object-specific functions are invoked. 5.4.5.7 access control dac me...
Page 95
• a system call interface is provided to provide restricted access to user processes. This interface allows user processes to allocate and free storage, and also to perform memory-mapped file i/o. This section highlights the implementation of the system architecture requirements of a) allowing the k...
Page 96
5.5.1 four-level page tables before the current implementation of four-level page tables, the kernel implemented a three-level page table structure for all architectures. The three-level page table structure that previously existed was constituted, from top to bottom, for the page global directory (...
Page 97
The creation and insertion of a new level, the pud level, immediately below the top-level pgd directory aims to maintain portability and transparency once all architectures have an active pgd at the top of hierarchy and an active pte at the bottom. The pmd and pud levels are only used in architectur...
Page 98
The larger kernel virtual address space allows the system to manage more physical memory. Up to 64 gb of main memory is supported by sles on x86-compatible systems. The larger user virtual address space allows applications to use approximately 30% more memory (3.7—3.8 gb), improving performance for ...
Page 99
5.5.2.1.1 segmentation the segmentation unit translates a logical address into a linear address. A logical address consists of two parts: a 16 bit segment identifier called the segment selector, and a 32-bit offset. For quick retrieval of the segment selector, the processor provides six segmentation...
Page 100
5.5.2.1.2 paging the paging unit translates linear addresses into physical addresses. It checks the requested access type against the access rights of the linear address. Linear addresses are grouped in fixed-length intervals called pages. To allow the kernel to specify the physical address and acce...
Page 101
In extended paging, 32 bits of linear address are divided into two fields: • directory: the most significant 10 bits represents directory. • offset: the remaining 22 bits represents offset. Each entry of the page directory and of the page table is represented by the same data structure. This data st...
Page 102
User-supervisor flag: this flag contains the privilege level that is required for accessing the page or page table. The user-supervisor flag is either 0, which indicates that the page can be accessed only in kernel mode, or 1, which indicates that it can always be accessed. 5.5.2.1.2.1 paging in the...
Page 103
For more information about call gates, refer to the http://www.Csee.Umbc.Edu/~plusquel/310/slides/micro_arch4.Html web site. 5.5.2.1.2.3 translation lookaside buffers the system x processor includes other caches, in addition to the hardware caches. These caches are called translation lookaside buffe...
Page 104
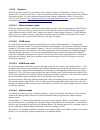
The ps flag in the page directory entry (pde.Ps) selects between 4 kb and 2 mb page sizes. 5.5.2.2 system p linux on power5 system p systems runs only in logical partitioning (lpar) mode. The system p offers the ability to partition one system into several independent systems through lpar. Lpar divi...
Page 105
Figure 5-34: logical partitions on system p systems without logical partitions, the processor has two operating modes, user and supervisor. The user and supervisor modes are implemented using the pr bit of the machine state register (msr). Logical partitions on system p systems necessitate a third m...
Page 106
• 0 the processor is not in hypervisor state. • 1 if msrpr= 0 the processor is in hypervisor state; otherwise, the processor is not in hypervisor state. The hypervisor takes the value of 1 for hypervisor mode and 0 for user and supervisor mode. The following table describes the privilege state of th...
Page 107
Just as certain memory areas are protected from access in user mode, some memory areas, such as hardware page tables, are accessible only in hypervisor mode. The powerpc and power architecture provides only one system call instruction. This system call instruction, sc, is used to perform system call...
Page 108
Hardware address of the memory. This translation is done by the hypervisor, which keeps a logical partition unaware of the existence of other logical partitions. 5.5.2.2.1 address translation on lpars on system p systems running with logical partitions, the effective address, the virtual address, an...
Page 109
5.5.2.2.4 virtual mode addressing operating systems use another type of addressing, virtual addressing, to give user applications an effective address space that exceeds the amount of physical memory installed in the system. The operating system does this by paging infrequently used programs and dat...
Page 110
5.5.2.2.7 run-time abstraction services system p hardware platforms provide a set of firmware run-time abstraction services (rtas) calls. In lpar, these calls perform additional validation checking and resource virtualization for the partitioned environment. For example, although there is only one p...
Page 111
For further information about powerpc 64 bit processor, see powerpc 64-bit kernel internals by david engebretson, mike corrigan & peter bergner at http://lwn.Net/2001/features/ols/pdf/pdf/ppc64.Pdf . You can find further in formation about system p hardware at http://www-1.Ibm.Com/servers/eserver/ps...
Page 112
• to access a particular memory location, the cpu transforms an effective address into a physical address using one of the following address translation mechanisms. • real mode address translation, where address translation is disabled. The physical address is the same as the effective address. • bl...
Page 113
• dr: data address translation. The value of 0 disables translation, and the value of 1 enables translation. 5.5.2.3.2 page descriptor pages are described by page table entries (ptes). The operating system generates and places ptes in a page table in memory. A pte on sles is 128 bits in length. Bits...
Page 114
• vs: supervisor mode valid bit. Used with msr[pr] to restrict translation for some block addresses. • vp: user mode valid bit. Used with msr[pr] to restrict translation for some block addresses. • pp: protection bits for block. 5.5.2.3.5 address translation mechanisms the following simplified flowc...
Page 115
Real mode address translation: real mode address translation is not technically the translation of any addresses. Real mode address translation signifies no translation. That is, the physical address is the same as the effective address. The operating system uses this mode during initialization and ...
Page 116
Page address translation begins with a check to see if the effective segment id, corresponding to the effective address, exists in the segment lookaside buffer (slb). The slb provides a mapping between effective segment ids (esids) and virtual segment ids (vsids). If the slb search fails, a segment ...
Page 117
105 figure 5-48: page address translation and access control.
Page 118
5.5.2.4 system z sles on system z systems can run either in native mode or in lpar. Additionally, it can run as z/vm guests, which is specific to this series. This section briefly describes these three modes and how they address and protect memory. For more detailed information about system z archit...
Page 119
Absolute address: an absolute address is the address assigned to a main memory location. An absolute address is used for a memory access without any transformations performed on it. Effective address: an effective address is the address that exists before any transformation takes place by dynamic ad...
Page 120
5.5.2.4.7.1 dynamic address translation bit 5 of the current psw indicates whether a virtual address is to be translated using paging tables. If it is, bits 16 and 17 control which address space translation mode (primary, secondary, access-register, or home) is used for the translation. The followin...
Page 121
Figure 5-51: address translation modes each address-space translation mode translates virtual addresses corresponding to that address space. For example, primary address-space mode translates virtual addresses from the primary address space, and home address space mode translates virtual addresses b...
Page 122
5.5.2.4.7.2 prefixing prefixing provides the ability to assign a range of real addresses to a different block in absolute memory for each cpu, thus permitting more than one cpu sharing main memory to operate concurrently with a minimum of interference. Prefixing is performed with the help of a prefi...
Page 123
For a detailed description of prefixing as well as implementation details, see z/architecture principles of operation at http://publibz.Boulder.Ibm.Com/epubs/pdf/dz9zr002.Pdf . 5.5.2.4.8 memory protection mechanisms in addition to separating the address space of user and supervisor states, the z/arc...
Page 124
5.5.2.4.8.2 page table protection the page table protection mechanism is applied to virtual addresses during their translation to real addresses. The page table protection mechanism controls access to virtual storage by using the page protection bit in each page-table entry and segment-table entry. ...
Page 125
113 figure 5-54: 31-bit dynamic address translation with page table protection.
Page 126
114 figure 5-55: 64-bit dynamic address translation with page table protection.
Page 127
5.5.2.4.8.3 key-controlled protection when an access attempt is made to an absolute address, which refers to a memory location, key-controlled protection is applied. Each 4k page, real memory location, has a 7-bit storage key associated with it. These storage keys for pages can only be set when the ...
Page 128
5.5.2.5 eserver 326 eserver 326 systems use amd opteron processors. The opteron processors can either operate in legacy mode to support 32-bit operating systems, or in long mode to support 64-bit operating systems. Long mode has two possible sub modes, the 64-bit mode, which runs only 64-bit applica...
Page 129
The segment selector specifies an entry in either the global or local descriptor table. The specified descriptor- table entry describes the segment location in virtual-address space, its size, and other characteristics. The effective address is used as an offset into the segment specified by the sel...
Page 130
• requestor privilege level (rpl):rpl represents the privilege level of the program that created the segment selector. The rpl is stored in the segment selector used to reference the segment descriptor. • descriptor privilege level (dpl):dpl is the privilege level that is associated with an individu...
Page 131
Calls. If the code segment is non-conforming (with conforming bit c set to zero in the segment descriptor), then the processor first checks to ensure that cpl is equal to dpl. If cpl is equal to dpl, then the processor performs the next check to see if the rpl value is less than or equal to the cpl....
Page 132
The eserver 326 supports a four-level page table. The uppermost level is kept private to the architecture- specific code of sles. The page-table setup supports up to 48 bits of address space. The x86-64 architecture supports page sizes of 4 kb and 2 mb. Figure 5-61 illustrates how paging is used to ...
Page 133
When the page size is 2 mb, bits 0 to 20 represent the byte offset into the physical page. That is, page table offset and byte offset of the 4 kb page translation are combined to provide a byte offset into the 2 mb physical page. Figure 5-62 illustrates how paging is used to translate a 64-bit linea...
Page 134
Each entry of the page map level-4 table, the page-directory pointer table, the page-directory table, and the page table is represented by the same data structure. This data structure includes fields that interact in implementing access control during paging. These fields are the read/write (r/w) fl...
Page 135
• read/write flag: this flag contains access rights of the physical pages mapped by the table entry. The r/w flag is either read/write or read. If set to 0, the corresponding page can only be read; otherwise, the corresponding page can be written to or read. The r/w flag affects all physical pages m...
Page 136
5.5.3.1 support for numa servers numa is an architecture wherein the memory access time for different regions of memory from a given processor varies according to the nodal distance of the memory region from the processor. Each region of memory, to which access times are the same from any cpu, is ca...
Page 137
Systems, this operation is unacceptably slow. With rmap vm, additional memory management structures have been created that enable a physical address to be back-translated to its associated virtual address quickly and easily. For more information about rmap vm, see http://lwn.Net/articles/23732/ and ...
Page 138
Huge tlb file system (hugetlbfs) is a pseudo file system, implemented in fs/hugetlbfs/inode.C. The basic idea behind the implementation is that large pages are being used to back up any file that exists in the file system. During initialization, init_hugetlbfs_fs() registers the file system and moun...
Page 139
5.5.3.4 remap_file_pages remap_file_pages is another memory management feature that is suitable for large memory and database applications. It is primarily useful for x86 systems that use the shared memory file system (shmemfs). A shmemfs memory segment requires kernel structures for control and map...
Page 140
5.5.3.6 memory area management memory areas are sequences of memory cells having contiguous physical addresses with an arbitrary length. The sles kernel uses the buddy algorithm for dealing with relatively large memory requests, but in order to satisfy kernel needs of small memory areas, a different...
Page 141
Address returned by arch_get_unmapped_area() to contain a linear address that is part of another process’s address space. In addition to this process compartmentalization, the do_mmap() routine also makes sure that when a new memory region is inserted it does not cause the size of the process addres...
Page 142
5.5.5 symmetric multiprocessing and synchronization the sles kernel allows multiple processes to execute in the kernel simultaneously (the kernel is reentrant). It also supports symmetric multiprocessing (smp), in which two or more processors share the same memory and have equal access to i/o device...
Page 143
5.5.5.3 spin locks spin locks provide an additional synchronization primitive for applications running on smp systems. A spin lock is just a simple flag. When a kernel control path tries to claim a spin lock, it first checks whether or not the flag is already set. If not, then the flag is set, and t...
Page 144
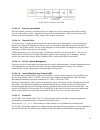
Figure 5-69: audit framework components 5.6.1.1 audit kernel components linux audit of the sles kernel includes three kernel-side components relating to the audit functionality. The first component is a generic mechanism for creating audit records and communicating with user space. The communication...
Page 145
The kernel checks the effective capabilities of the sender process. If the sender does not possess the right capability, the netlink message is discarded. 5.6.1.1.2 syscall auditing the second component is a mechanism that addresses system call auditing. It uses the generic logging mechanism for cre...
Page 146
5.6.1.1.5 audit context fields • login id: login id is the user id of the logged-in user. It remains unchanged through the setuid() or seteuid() system calls. Login id is required by the controlled access protection profile to irrefutably associate a user with that user’s actions, even across su() c...
Page 147
• serial: a unique number that helps identify a particular audit record. Along with ctime, it can determine which pieces belong to the same audit record. The (timestamp, serial) tuple is unique for each syscall and it lives from syscall entry to syscall exit. • ctime: time at system call entry. • ma...
Page 148
When a filesystem object the audit subsystem is watching changes, the inotify subsystem calls the audit_handle_event() function. Audit_handle_event() in turn updates the audit subsystem's watch data for the watched entity. This process is detailed in section 5.6.3.1.3. 5.6.1.3 user space audit compo...
Page 149
5.6.2 audit operation and configuration options 5.6.2.1 configuration there are many ways to control the operation of the audit subsystem. The controls are available at compilation time, boot time, daemon startup time, and while the daemon is running. At compilation time, sles kernel provides three ...
Page 150
Option description possible values log_file name of the log file log_format how to flush the data from auditd to the log. Raw. Only raw is supported in this version. Priority_boost the nice value for auditd. Used to run auditd at a certain priority. Flush method of writing data to disk. None, interv...
Page 152
7. If audit is enabled, the kernel intercepts the system calls, and generates audit records according to the filter rules. Or, the kernel generates audit records for watches set on particular file system files or directories. 8. Trusted programs can also write audit records for security relevant ope...
Page 153
5.6.3.1.2 syscall audit record generation once attached, every security-relevant system call performed by the process is evaluated in the kernel. The process’s descendants maintain their attachment to the audit subsystem. 1. All security-relevant system calls made by the process are intercepted at t...
Page 154
Generates the audit record, and sends the record to netlink socket. Both audit_syscall_entry() and audit_syscall_exit() call audit_filter_syscall() to apply filter logic, to check whether to audit or not to audit the call. Filtering logic allows an administrative user to filter out events based on t...
Page 155
5.6.3.1.4 socket call and ipc audit record generation some system calls pass an argument to the kernel specifying which function the system call is requesting from the kernel. These system calls request multiple services from the kernel through a single entry point. For example, the first argument t...
Page 156
Timestamp of the record and the serial number are used by the user-space daemon to determine which pieces belong to the same audit record. The tuple is unique for each syscall and lasts from syscall entry to syscall exit. The tuple is composed of the timestamp and the serial number. Each audit recor...
Page 157
Event description laf audit events startup and shutdown of audit functions daemon_start, daemon_end are generated by auditd modification of audit configuration files daemon_config, daemon_reconfig are generated by auditd. Syscalls open, link, unlink, rename, truncate, write on configuration files su...
Page 158
Event description laf audit events execution of the test of the underlying machine and the result of the test audit message from amtu utility: audit record type: user. Changes to system time syscall settimeofday, adjtimex setting up a trusted channel sycall exec (of stunnel program) table 5-4: audit...
Page 159
Lower-layer functions, such as scheduling and interrupt management, cannot be modularized. Kernel modules can be used to add or replace system calls. The sles kernel supports dynamically-loadable kernel modules that are loaded automatically on demand. Loading and unloading occurs as follows: 1. The ...
Page 160
Structure object task_struct task(process) linux_binprm program super_block file system inode pipe, file, or socket file open file sk_buff network buffer(packet) net_device network device kern_ipc_perm semaphore, shared memory segment, or message queue msg_msg individual message table 5-5: kernel da...
Page 161
Lsm adds a general security system call that simply invokes the sys_security hook. This system call and hook permits security modules to implement new system calls for security-aware applications. 5.7.2 lsm capabilities module the lsm kernel patch moves most of the existing posix.1e capabilities log...
Page 162
● administrative utilities provide a mechanism for administrators to configure, query, and control apparmor. For background information on apparmor which was originally named subdomain, subdomain: parsimonious server security by crispin cowan, steve beattie, greg kroahhartman, calton pu, perry wagl...
Page 163
● px discrete profile execute ● px discrete profile execute after scrubbing the environment ● ix inherit execute ● m allow prot_exec with mmap(2) calls ● l – link for more information about complete apparmor profile syntax, please see the apparmor.D man page. Apparmor profiles are loaded int...
Page 164
5.9 device drivers a device driver is a software layer that makes a hardware device respond to a well-defined programming interface. The kernel interacts with the device only through these well-defined interfaces. For detailed information about device drivers, see linux device drivers, 2nd edition, ...
Page 165
Guest program or interpreted machine. The interpreted and host machines execute guest and host programs, respectively. The interpretive-execution facility is invoked by executing the start interpretive execution (sie) processor instruction, which causes the cpu to enter the interpretive-execution mo...
Page 166
• conditional interceptions refer to functions that are executed for the guest unless a specified condition is encountered that causes control to be returned to the host by the process that called the interception. Following are some of the controls that can cause interception when the related funct...
Page 167
This extra level of indirection is needed for character devices, but not for block devices, because of the large variety of character devices and the operations they support. The following diagram illustrates how the kernel maps the file operations vector of the device file object to the correct set...
Page 168
5.10 system initialization when a computer with sles is turned on, the operating system is loaded into memory by a special program called a boot loader. A boot loader usually exists on the system's primary hard drive, or other media device, and has the sole responsibility of loading the linux kernel...
Page 169
The system runlevel by controlling pid 1. For more information on the /etc/inittab file, please see the inittab(5) man page. For more information on the init program, please see the init(8) manpage. The init program generally follows these startup steps: 1. Gets its own name. 2. Sets its umask. 3. C...
Page 170
5.10.2.1 boot methods sles supports booting from a hard disk, a cd-rom, or a floppy disk. Cd-rom and floppy disk boots are used for installation, and to perform diagnostics and maintenance. A typical boot is from a boot image on the local hard disk. 5.10.2.2 boot loader a boot loader is a program th...
Page 171
14. The boot loader sets the idt with null interrupt handlers. It puts the system parameters obtained from the bios and the parameters passed to the operating system into the first page frame. 15. The boot loader identifies the model of the processor. It loads the gdtr and idtr registers with the ad...
Page 172
160 figure 5-79: system x sles boot sequence.
Page 173
5.10.3 system p this section briefly describes the system initialization process for system p servers. 5.10.3.1 boot methods sles supports booting from a hard disk or from a cd-rom. Cd-rom boots are used for installation and to perform diagnostics and maintenance. A typical boot is from a boot image...
Page 174
1. Yaboot allows an administrator to perform interactive debugging of the startup process by executing the /etc/sysconfig/init script. 2. Mounts the /proc special file system. 3. Mounts the /dev/pts special file system. 4. Executes /etc/rc.D/rc.Local, which was set by an administrator to perform sit...
Page 175
5.10.4 system p in lpar sles runs in a logical partition on an system p system. The hypervisor program creates logical partitions, which interacts with actual hardware and provides virtual versions of hardware to operating systems running in different logical partitions. As part of an initial progra...
Page 176
5.10.4.1 boot process for an individual computer, the boot process consists of the following steps when the cpu is powered on or reset: 1. The hypervisor assigns memory to the partition as a 64 mb contiguous load area and the balance in 256 kb chunks. 2. The boot loader loads the sles kernel into th...
Page 177
• starts the agetty program. For more details about services started at run level 3, see the scripts in /etc/rc.D/rc3.D on a sles system. Figure 5-81 schematically describes the boot process of system p lpars. 165 figure 5-81: system p lpar sles boot sequence.
Page 178
5.10.5 system z this section briefly describes the system initialization process for system z servers. 5.10.5.1 boot methods linux on system z supports three installation methods: native, lpar, and z/vm guest installations. Sles only supports z/vm guest installation. The process described below corr...
Page 179
4. Executes /etc/rc.D/rc.Local, which was set by an administrator to perform site-specific setup functions. 5. Performs run-level specific initialization by executing startup scripts defined in /etc/inittab. The scripts are named /etc/rc.D/rcx.D, where x is the default run level. The default run lev...
Page 180
5.10.6 eserver 326 this section briefly describes the system initialization process for eserver 326 servers. For detailed information on system initialization, see amd64 architecture, programmer’s manual volume 2: system programming, at http://www.Amd.Com/us-en/assets/content_type/white_papers_and_t...
Page 181
5.10.6.2 boot loader after the system completes the hardware diagnostics setup in the firmware, the first program that runs is the boot loader. The boot loader is responsible for copying the boot image from hard disk and then transferring control to it. Sles supports grub, which lets you set pointer...
Page 182
17. X86_64_start_kernel() completes the kernel initialization by initializing page tables, memory handling data structures idt tables, slab allocator (described in section 5.5.3.6), system date, and system time. 18. Uncompress the initrd initial ram file system, mounts it, and then executes /linuxrc...
Page 183
5.11 identification and authentication identification is when a user possesses an identity to a system in the form of a login id. Identification establishes user accountability and access restrictions for actions on the system. Authentication is verification that the user’s claimed identity is valid...
Page 184
Provides a way to develop programs that are independent of the authentication scheme. These programs need authentication modules to be attached to them at run-time in order to work. Which authentication module is to be attached is dependent upon the local system setup and is at the discretion of the...
Page 185
6. Each authentication module performs its action and relays the result back to the application. 7. The pam library is modified to create a user_auth type of audit record to note the success or failure from the authentication module. 8. The application takes appropriate action based on the aggregate...
Page 186
• pam_passwdqc.So: performs additional password strength checks. For example, it rejects passwords such as “1qaz2wsx” that follow a pattern on the keyboard. In addition to checking regular passwords it offers support for passphrases and can provide randomly generated passwords. • pam_env.So: loads a...
Page 187
5.11.2 protected databases the following databases are consulted by the identification and authentication subsystem during user session initiation: • /etc/passwd: for all system users, it stores the login name, user id, primary group id, real name, home directory, and shell. Each user’s entry occupi...
Page 188
• /etc/ftpusers: the ftpusers text file contains a list of users who cannot log in using the file transfer protocol (ftp) server daemon. The file is owned by the root user and root group, and its mode is 644. • /etc/apparmor/* and /etc/apparmor.D/*: the directories /etc/apparmor and /etc/apparmor.D ...
Page 189
6. Execs the login program. The steps that are relevant to the identification and authorization subsystem are step 5, which prompts for the user’s login name, and step 6, which executes the login program. The administrator can also use a command-line option to terminate the program if a user name is...
Page 190
17. Sets effective, real, and saved user id. 18. Changes directory to the user’s home directory. 19. Executes shell. 5.11.3.4 mingetty mingetty, the minimal linux getty, is invoked from /sbin/init when the system transitions from single-user mode to multi-user mode. Mingetty opens a pseudo tty port,...
Page 191
16. Sets up signals. 17. Forks a child. 18. Parent waits on child's return; child continues: 19. Adds the new gid to the group list. 20. Sets the gid. 21. Logs an audit record. 22. Starts a shell if the -c flag was specified. 23. Looks for the shell environment variable or, if shell is not set defau...
Page 192
4. Processes command-line arguments. 5. Sets up the environment variable array. 6. Invokes pam_start() to initialize the pam library, and to identify the application with a particular service name. 7. Invokes pam_set_item() to record the tty and user name. 8. Validates the user that the application ...
Page 193
Cryptography can be used to neutralize some of these attacks and to ensure confidentiality and integrity of network traffic. Cryptography can also be used to implement authentication schemes using digital signatures. The toe supports a technology based on cryptography called openssl. Openssl is a cr...
Page 194
5.12.1.1 concepts ssl is used to authenticate endpoints and to secure the contents of the application-level communication. An ssl-secured connection begins by establishing the identities of the peers, and establishing an encryption method and key in a secure way. Application-level communication can ...
Page 195
Data confidentiality can be maintained by keeping the algorithm, the key, or both, secret from unauthorized people. In most cases, including openssl, the algorithm used is well-known, but the key is protected from unauthorized people. 5.12.1.1.1.1 encryption with symmetric keys a symmetric key, also...
Page 196
If encryption is done with a public key, only the corresponding private key can be used for decryption. This allows a user to communicate confidentially with another user by encrypting messages with the intended receiver’s public key. Even if messages are intercepted by a third party, the third part...
Page 197
5.12.1.1.2 message digest a message digest is text in the form of a single string of digits created with a one-way hash function. One- way hash functions are algorithms that transform a message of arbitrary length into a fixed length tag called a message digest. A good hash function can detect even ...
Page 198
The ssl architecture differentiates between an ssl session and an ssl connection. A connection is a transient transport device between peers. A session is an association between a client and a server. Sessions define a set of cryptographic security parameters, which can be shared among multiple conn...
Page 199
1. Client hello message: the ciphersuite list, passed from the client to the server in the client hello message, contains the combinations of cryptographic algorithms supported by the client in order of the client's preference (first choice first). Each ciphersuite defines both a key exchange algori...
Page 200
For the list of cipher suites supported, see fcs_cop.1(2) in the security target. 5. Ssl change cipher spec protocol: the ssl change cipher spec protocol signals transitions in the security parameters. The protocol consists of a single message, which is encrypted with the current security parameters...
Page 201
• blowfish: blowfish is a block cipher that operates on 64-bit blocks of data. It supports variable key sizes, but generally uses 128-bit keys. • data encryption standard (des): des is a symmetric key cryptosystem derived from the lucifer algorithm developed at ibm. Des describes the data encryption...
Page 202
Md2, md4, and md5 are cryptographic message-digest algorithms that take a message of arbitrary length and generate a 128-bit message digest. In md5, the message is processed in 512-bit blocks in four distinct rounds. Mdc2 is a method to construct hash functions with 128-bit output from block ciphers...
Page 203
unencrypted_packet) where unencrypted_packet is the entire packet without mac (the length fields, payload and padding), and sequence_number is an implicit packet sequence number represented as uint32. The sequence number is initialized to zero for the first packet,...
Page 204
5.12.3 very secure file transfer protocol daemon very secure file transfer protocol daemon (vsftpd) provides a secure, fast, and stable file transfer service to and from a remote host. The behavior of vsftpd can be controlled by its configuration file /etc/vsftpd/vsftpd.Conf. The remainder of this s...
Page 205
For background on cups labeled printing, please see: http://free.Linux.Hp.Com/~mra/docs/ . Cups uses the internet printing protocol (ipp) that was designed to replace the line printer daemon (lpd) protocol, as a basis for managing print jobs. Cups also supports lpd, server message block (smb), and a...
Page 206
24. Check for input or output requests with select(). 25. If select() fails, logs error messages, notifies clients, and exits the main loop for shutdown processing. 26. Gets the current time. 27. Checks print status of print jobs. 28. Updates cgi data. 29. Updates notifier messages. 30. Expires subs...
Page 207
Cryptography standards that they require. The openssl command can be used by an administrative user for the following: • creation of rsa, dh, and dsa parameters. • generation of 1024-bit rsa keys. • creation of x.509 certificates, csrs, and crls. • calculation of message digests. • encryption and de...
Page 208
# service-level configuration # --------------------------- [ssmtp] accept = 465 connect = 25 the above configuration secures localhost-smtp when someone connects to it via port 465. The configuration tells stunnel to listen to the ssh port 465, and to send all info to the plain port 25 on localhost...
Page 209
14. Invokes pam_chauthok() to rejuvenate user’s authentication tokens. 15. Exits. 5.13.1.2 chfn the chfn program allows users to change their finger information. The finger command displays the information, stored in the /etc/passwd file. Refer to the chfn man page for detailed information. Chfn gen...
Page 210
11. Invokes setpwnam() to update appropriate database files with the new shell. 12. Exits. 5.13.2 user management 5.13.2.1 useradd the useradd program allows an authorized user to create new user accounts on the system. Refer to the useradd man page for more information. Useradd generally follows th...
Page 211
6. Processes command-line arguments. 7. Ensures that the user account being modified exists. 8. Invokes open_files() to lock and open authentication database files. 9. Invokes usr_update() to update authentication database files with updated account information. 10. Generates audit record to log act...
Page 212
5.13.3 group management 5.13.3.1 groupadd the groupadd program allows an administrator to create new groups on the system. Refer to the groupadd man page for more detailed information on usage of the command. Groupadd generally follows these steps: 1. Sets language. 2. Invokes getpwuid (getuid()) to...
Page 213
5.13.3.2 groupmod the groupmod program allows an administrator to modify existing groups on the system. Refer to the groupmod man page for more information. Groupmod generally follows these steps: 1. Sets language. 2. Invokes getpwuid (getuid()) to obtain application user’s passwd structure. 3. Invo...
Page 214
202.
Page 215
5.13.4 system time management 5.13.4.1 date the date program, for a normal user, displays current date and time. For an administrative user, date can also set the system date and time. Refer to the date man page for more information. Date generally follows these steps: 1. Sets language. 2. Parses co...
Page 216
This tool works from a premise that it is working on an abstract machine that is providing functionality to the tsf. The test tool runs on all hardware architectures that are targets of evaluation and reports problems with any underlying functionalities. For more detailed information on the abstract...
Page 217
5.13.5.1.5.1 system p the instruction set for the powerpc processor is given in the book at the following url: http://www.Ibm.Com/chips/techlib/techlib.Nsf/techdocs/852569b20050ff778525699600682cc7/$file/booke _rm.Pdf for each instruction, the description in the book lists whether it is available on...
Page 218
To test cpu control registers, use movl %cs, 28(%esp). This overwrites the value of the register that contains the code segment. The register that contains the address of the next instruction (eip) is not directly addressable. Note that in the intel documentation of mov it is explicitly stated that ...
Page 219
2. Gets its euid and uid. 3. Transforms old-style command line argument syntax into new-style syntax. 4. Processes the command line arguments. 5. Sets up signal handling. 6. Initializes the fifo. 7. Initializes any remote connection. 8. Sets back the real uid. 9. Opens the archive. 10. Initializes d...
Page 220
5.13.6 i&a support 5.13.6.1 pam_tally the pam_tally utility allows administrative users to reset the failed login counter kept in the /var/log/faillog. Please see the /usr/share/doc/packages/pam/modules/readme.Pam_tally file on a sles system for more information. 5.13.6.2 unix_chkpwd the unix_chkpwd...
Page 221
The crontab program is used to install, deinstall, or list the tables used to drive the cron daemon in vixie cron. The crontab program allows an administrator to perform specific tasks on a regularly-scheduled basis without logging in. Users can have their own crontabs that allow them to create jobs...
Page 222
Commands that are to be executed. Information stored in this job file, along with its attributes, is used by the atd daemon to recreate the invocation of the user’s identity while performing tasks at the scheduled time. 5.14.2 batch processing daemons 5.14.2.1 cron the cron daemon executes commands ...
Page 223
5.15 user-level audit subsystem the main user-level audit components consist of the auditd daemon, the auditctl control program, the libaudit library, the auditd.Conf configuration file, and the auditd.Rules initial setup file. There is also the /etc/init.D/auditd init script that is used to start a...
Page 224
2. Processes the command line arguments. 3. Attempts to raise its resource limits. 4. Sets its umask. 5. Resets its internal counters. 6. Emits a title. 7. Processes audit records from an audit log file or stdin, incrementing counters depending on audit record contents. 8. Prints a message and exits...
Page 225
5.16 supporting functions trusted programs and trusted processes in an sles system use libraries. Libraries do not form a subsystem in the notation of the common criteria, but they provide supporting functions to trusted commands and processes. A library is an archive of link-edited objects and thei...
Page 226
Library description /lib/libc.So.6 c run time library functions. /lib/libcrypt.So.1 library that performs one-way encryption of user and group passwords. /lib/libcrypt.So.O.9.8b replacement library for libcrypt.So.1 supports bigcrypt and blowfish password encryption. /lib/security/pam_unix.So module...
Page 227
5.16.2 library linking mechanism on sles, a binary executable automatically causes the program loader /lib/ld-linux.So.2 to be loaded and run. This loader takes care of analyzing the library names in the executable file, locating the library in the system directory tree, and making requested code av...
Page 228
System initialization, and sets the idt entry corresponding to vector 128 (ox80) to invoke the system call exception handler. When compiling and linking a program that makes a system call, the libc library wrapper routine for that system call stores the appropriate system call number in the eax regi...
Page 229
Passed as system-call parameters. For the sake of efficiency, and satisfying the access control requirement, the sles kernel performs validation in a two-step process, as follows: 1. Verifies that the linear address (virtual address for system p and system z) passed as a parameter does not fall with...
Page 230: Design
6 mapping the toe summary specification to the high-level design this chapter provides a mapping of the security functions of the toe summary specification to the functions described in this high-level design document. 6.1 identification and authentication section 5.11 provides details of the sles i...
Page 231
6.2.3 audit record format (au.3) section 5.6.3.2 describes information stored in each audit record. 6.2.4 audit post-processing (au.4) section 5.15.2 describes audit subsystem utilities provided for post-processing of audit data. 6.3 discretionary access control sections 5.1 and 5.2 provide details ...
Page 232
6.5.1 roles (sm.1) section 5.13 provides details on various commands that support the notion of an administrator and a normal user. 6.5.2 access control configuration and management (sm.2) sections 5.1.1 and 5.1.2.1 provide details on the system calls of the file system that are used to set attribut...
Page 233
6.7.4 trusted processes (tp.4) section 4.2.2 provides details on the non-kernel trusted process on the sles system. 6.7.5 tsf databases (tp.5) section 4.3 provides details on the tsf databases on the suse linux enterprise server system. 6.7.6 internal toe protection mechanisms (tp.6) section 4.1.1 d...
Page 234
• kernel modules • device drivers • trusted process subsystems: • system initialization • identification and authentication • network applications • system management • batch processing • user-level audit subsystem 6.8.1 summary of kernel subsystem interfaces this section identifies the kernel subsy...
Page 235
6.8.1.1.2 internal interfaces 6.8.1.1.3 internal function interfaces defined in permission this document, section 5.1.1.1 vfs_permission this document, sections 5.1.1.1 and 5.1.5.1 get_empty_filp this document, section 5.1.1.1 fget this document, section 5.1.1.1 do_mount this document, section 5.1.2...
Page 236
Read_inode write_super read_inode2 write_super_lockfs dirty_inode unlockfs write_inode statfs put_inode remount_fs delete_inode clear_inode dentry operations: note that they are not used by other subsystems, so there is no subsystem interface: • d_revalidate • d_hash • d_compare • d_delete • d_relea...
Page 237
System calls are listed in the functional specification mapping table. 6.8.1.2.2 internal interfaces internal function interfaces defined in current understanding the linux kernel, chapter 3, 2nd edition, daniel p. Bovet, marco cesati, isbn# 0-596-00213-0 request_irq linux device drivers, o’reilly, ...
Page 238
6.8.1.3.1 external interfaces (system calls) • tsfi system calls • non-tsfi system calls system calls are listed in the functional specification mapping table. 6.8.1.3.2 internal interfaces internal function interfaces defined in do_pipe understanding the linux kernel, chapter 19, 2nd edition, danie...
Page 239
6.8.1.4 kernel subsystem networking this section lists external interfaces, internal interfaces and data structures of the networking subsystem. 6.8.1.4.1 external interfaces (system calls) • tsfi system calls • non-tsfi system calls system calls are listed in the functional specification mapping ta...
Page 240
System calls are listed in the functional specification mapping table 6.8.1.5.2 internal interfaces internal interfaces interfaces defined in get_zeroed_page linux device drivers, o’reilly, chapter 7, 2nd edition june 2001, alessandro rubini /this document, chapter 5.5.2.1 __vmalloc linux device dri...
Page 241
• audit_sockaddr • audit_ipc_perms 6.8.1.6.3 data structures • audit_sock: the netlink socket through which all user space communication is done. • audit_buffer: the audit buffer is used when formatting an audit record to send to user space. The audit subsystem pre-allocates audit buffers to enhance...
Page 242
Driver methods for character device drivers and block device drivers, see [rubn]. Chapter 3 describes the methods for character devices and chapter 6 describes the methods for block devices. 6.8.1.7.2.1 character devices possible character device methods are: llseek flush read release write fsync re...
Page 243
6.8.1.7.3 data structures device_struct fs/devices.C file_operations include/linux/fs.H block_device_operati ons include/linux/fs.H 6.8.1.8 kernel subsystems kernel modules this section lists external interfaces, internal interfaces, and data structures of the kernel modules subsystem. 6.8.1.8.1 ext...
Page 244: 7 References
7 references [cc] common criteria for information technology security evaluation, ccimb-99-031, version 2.1, august 1999 [cem] common methodology for information technology security evaluation, cem-99/045, part 2 – evaluation methodology, version 1.0, 1999 [bovt] understanding the linux kernel, 2nd ...
Page 245
[rsa] "a method for obtaining digital signatures and public-key cryptosystems," communications of the acm, v. 21, n. 2, feb 1978, pp. 120-126, r. Rivest, a. Shamir, and l. M. Adleman, [dh1] "new directions in cryptography," ieee transactions on information theory, v.It-22, n. 6, jun 1977, pp. 74-84,...
Page 246
The following are trademarks or registered trademarks of the international business machines corporation in the united states and/or other countries. For a complete list of ibm trademarks, see www.Ibm.Com/legal/copytrade.Shtml: bladecenter, eserver, power, power architecture, powerpc, pr/sm, s/390, ...