- DL manuals
- IBM
- Network Card
- Safenet/400
- Reference Manual
IBM Safenet/400 Reference Manual
Summary of Safenet/400
Page 1
Safenet/400 reference guide version 8.50 ™ © 2008 mp associates of westchester, inc..
Page 2: How to Contact Us
How to contact us direct all inquiries to: kisco information systems 89 church street saranac lake, new york 12983 phone: (518) 897-5002 fax: (518) 897-5003 safenet/400 website: http://www.Kisco.Com/safenet safenet/400 support website: http://www.Kisco.Com/safenet/support visit the safenet/400 web s...
Page 3
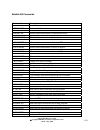
Table of contents chapter 1 - setting up users..................................................................................... 1.1 s etting the u ser l ogging l evels ......................................................................................... 1.2 s afe n et a dministrator ...........
Page 4
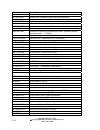
Chapter 7 - testing your security settings .................................................. 7.1 t esting s afe n et /400 settings based on your historical data with the on - line transaction tester .......................................................................................................
Page 5: Safenet/400
1.1 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 safenet/400 reference guide chapter 1 - setting up users navigating through the screens you can perform each of the steps outlined in this chapter by using the corresponding option on the safenet/400...
Page 6
1.2 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 setting the user logging levels the valid logging levels are: logging level a log all transactions logging level r log only rejected requests logging level n no logging as you set up your user loggin...
Page 7
1.3 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 safenet administrator you can set up a safenet/400 administrator, or ‘super admin’ from the safenet/400 special jobs menu or by using the wrksnadm command. This can also be found on the special jobs ...
Page 8
1.4 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 super trusted user control under special circumstances it may be necessary to have a user that should not be checked through all the safenet/400 security routines. Transactions from these users can b...
Page 9
1.5 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 entering user security levels if you plan on setting any of the server functions to level 3 or level 4, and anticipate doing anything other than simply logging all requests, the first step in configu...
Page 10
1.6 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 type 1 in the option column in front of each server this user will have access to. If they will have access to all the server functions, select *all active servers to remove access to a particular se...
Page 11
1.7 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 entering user authorities to objects once you have given the user access to the servers, the next step is to enter the level of authority the user has to objects on the system i5 if you plan on setti...
Page 12
1.8 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 4. In the library or folder column, enter the name of the library or folder, then tab to the object or sub-flr column and type in the name of the object or sub-folder. Note: allowed entries for libra...
Page 13
1.9 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 5. For data rights, type an x under the appropriate level of authority. Place an x for each data right that applies. 6. For existence rights, type an x if this user will be able to create, delete or ...
Page 14
1.10 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 exclusions to give all users read access to all objects in all libraries, but exclude them from any objects in the payroll library, give *public read authority to the library and exclude *public fro...
Page 15
1.11 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 if the paydept profile needs to use objects in the payroll library, grant user profile paydept read authority to the payroll library. This individual authority overrides the *public authority..
Page 16
1.12 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 entering user authorities to sql statements if you are going to set the sql servers to level 4 only, the next step is to authorize users to the sql statements they may need. 1. If you used f9 from t...
Page 17
1.13 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 if you would like to see the list of all users who have been defined within safenet/400, press f2. 5. When finished making all your selections, enter. 6. Press f9 to advance to the next step - setti...
Page 18
1.14 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 entering user authorities to ftp statements next you must authorize users to the ftp statements they may need if you are going to set the ftp server or ftp client to level 4. 1. If you used f9 from ...
Page 19
1.15 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 if you would like to see the list of all users who have been defined within safenet/400, press f2. 5. Press f4 to display the maintain special ftp settings for users screen note: special ftp setting...
Page 20
1.16 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 name format • *lib indicates that the user sees standard library/object os/400 style names • *path displays pc or *unix style file and directory names. List format • *dft user sees standard os/400 c...
Page 21
1.17 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 entering user authorities to cl commands next, if you plan on setting the ftp, ddm or remote command servers to level 4, you must authorize users to the cl commands they may need. 1. If you used f9 ...
Page 22
1.18 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 to remove authorization to a command, field exit through the line to blank it out. If you would like to see the list of all users who have been defined within safenet/400, press f2. 5. When finished...
Page 23
1.19 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 entering long path names the default safenet/400 setting is to use long path names. If you choose to not use long path name support, you must first change the safenet/400 default setting. Use the ch...
Page 24
1.20 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 4. Enter the paths that the user is authorized to. Paths can be entered up to 256 positions in length, although only the first 60 positions are shown on the display. To enter and/or view a path over...
Page 25
1.21 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 copying an existing user to set up a new user in safenet/400 this will allow you to copy the authorities and settings from one user to another within safenet/400. The new user profile must already e...
Page 26
1.22 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 maintain all security for a user the wrkusrsec command, which is not found on any of the safenet/400 menus, gives you the ability to perform security maintenance for an individual user without enter...
Page 27
1.23 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 setting up time of day controls if you want to exclude users from server functions based on the day of the week or the time of day, use time of day controls. Safenet/400 checks authority in the foll...
Page 28
1.24 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 to set up the time of day controls for a specific user, use option 2 – work with user to server security from the safenet/400 main menu or the wrkusrsrv command. Type the user profile, enter and the...
Page 29
1.25 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 you can define up to three time ranges and can select which days to exclude by typing x in front of the day. You can also define holidays that will be used to control time of day access. Press f9 to...
Page 30
1.26 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008.
Page 31
2.1 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 chapter 2 - setting up servers the final step in configuring safenet/400 is to enter the security level settings for all the server functions. Important: if you do this step first and restrict access...
Page 32
2.2 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 safenet/400 server function security levels level 1: • ibm default • unlimited access, all requests accepted • requests can be logged, reporting available • performance impact - none level 2: • no ac...
Page 33
2.3 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 level 5: • this indicates that safenet/400 does not recognize a program assigned to the exit point or has detected a user-defined program assigned. (use wrkreginf command to review existing exit poin...
Page 34
2.4 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 setting the server function logging levels the valid logging levels are: logging level a log all transactions logging level r log only rejected requests logging level n no logging as you set up your ...
Page 35
2.5 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 basic server security - supported by all servers level 1 - ibm default level 2 - no access to server intermediate server security - supported by all servers level 3 - users must be authorized to the ...
Page 36
2.6 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 recommended server settings server description recommended setting central server - client management level 1, log none central server - conversion map level 1, log none central server - license mana...
Page 37
2.7 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 server description recommended setting distributed data management level 3, log all - limit user access or level 4, log all - limit users to specific objects and commands dhcp level 1, log none drda ...
Page 38
2.8 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 server description recommended setting original message server level 1, log none original remote sql server level 4, log all - limit user access to objects and sql statements original virtual print s...
Page 39
2.9 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 entering server function security levels 1. From the safenet/400 main menu select option 1 - work with server security settings or use wrksrv command the maintain server security screen is displayed....
Page 40
2.10 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 3. When you have finished entering information for all the servers, press enter. The screen is refreshed and any changes you made are reflected in the current columns..
Page 41
2.11 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 customer exit programs if you would like to use your own programs over these server exit points, f18 on the maintain server security screen gives you the ability to do so. Safenet/400 will look to s...
Page 42
2.12 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008.
Page 43
3.1 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 chapter 3 - telnet, tcp/ip address controls setting up telnet telnet control features are supported only when the server is set to level 3. You may use some or all of the features available with the ...
Page 44
3.2 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 controlling telnet access by ip address 1. Set the telnet server to level 3 using the wrksrv command. 2. From the safenet/400 main menu, select option 7 – work with tcp/ip address security or use the...
Page 45
3.3 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 setting the required password type this field must be set if the telnet server is set to level 3. You must enter the appropriate setting for all telnet ip address controls. As of os/400 v4r2, only a ...
Page 46
3.4 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 allow auto signon 1. Use the wrksrv command to set the telnet server to level 3 2. Use the wrktcpipa *telnet command to enter the ip address allowed for auto signon 3. Enter the password type (0 or 1...
Page 47
3.5 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 logging of telnet sessions under normal signon conditions (no auto signon allowed), each request for a telnet session is logged into the transaction history file (trapod) by ip address, and a user na...
Page 48
3.6 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 setting up tcp/ip address controls safenet/400 allows you to specify which client ip addresses are either accepted or rejected by the telnet and the ftp servers. Turning on tcp/ip address checking to...
Page 49
3.7 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 setting up tcp/ip address control table 1. Use safenet/400 main menu option 7 or the wrktcpipa command 2. In ip addresses for server enter *ftpserver, *ftpclient or *telnet for the proper control tab...
Page 50
3.8 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008.
Page 51
4.1 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 chapter 4 - setting up ftp anonymous ftp logon to set up for anonymous logon, you must fill in the special ftp settings, and set the ftp logon server to level 3 and the ftp server validation to level...
Page 52
4.2 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 set the parameters for chgftpset command as follows. The default value is highlighted in bold. Parameter screen selections value description rlogon allow normal userid ftp logon *yes *no this paramet...
Page 53
4.3 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 guest allow anonymous guest password *yes *no to allow anonymous user logins with the password of guest, enter *yes here. You can choose guest or use an e-mail address. Note: if you select guest, the...
Page 54
4.4 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 password of *none and *user for the profile type. If you do this, no one can use this profile to sign on since the password is set to *none. Apwd password for above profile pword enter the password t...
Page 55
4.5 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 setting up for anonymous ftp example 1. Create a user profile on the system i5 called anonymous, with password *none and user class *user, and set the current library. 2. From the special jobs menu, ...
Page 56
4.6 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 if using long path support, use the wrkusrpth command to enter the correct path or paths for anonymous. 14. Select option 5 - work with user to ftp statement security or use the wrkusrftp commandto g...
Page 57
4.7 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 setting up for normal user ids and ftp servers example 1. From the special jobs menu select option 3 - change special ftp security settings or use chgftpset command 2. On the ftp security settings sc...
Page 58
4.8 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008.
Page 59
5.1 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 chapter 5 - dhcp controls and reporting dynamic host configuration protocol dhcp allows clients to obtain ip network configuration, including an ip address, from a central dhcp server. Dhcp servers c...
Page 60
5.2 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 working with dhcp dhcp functions are performed from the dhcp control and reports menu. From the safenet/400 main menu select option 13 – go to dhcp menu the dhcp control and reports menu appears. The...
Page 61
5.3 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 current dhcp activity to see current status, from the dhcp menu select option 1 – display current dhcp activity this screen displays bind and release information use function keys to switch views: f2...
Page 62
5.4 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 move your cursor to the name you want to change in the editable names column. Press enter to record the change. To use this function make sure you are looking at the currently active dhcp addresses b...
Page 63
5.5 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 maintaining mac addresses from the dhcp menu select option 5 – manually maintain mac addresses to user names this operates as a standard os/400 dfu program. Press f9 to use insert mode when editing p...
Page 64
5.6 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 fixed ip addresses to assign ip addresses to devices, from the dhcp menu select option 6 – manually maintain permanent, static ip addressed devices or use the sndhcppr command even if you are not usi...
Page 65
5.7 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 purging expired dhcp lease information the expired or released dhcp address information is cumulative and will remain in the system until you purge it. From the dhcp menu select option 8 – run purge ...
Page 66
5.8 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 ping checker you can use this option to ping a single ip address or a range of addresses. From the dhcp menu select option 10 – ip address range ping checker enter the range of ip addresses that you ...
Page 67
6.1 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 chapter 6 - reports safenet/400 reports are grouped into two categories: • setup reports provide information on server settings, user authorities to servers and to data, etc. • analysis reports provi...
Page 68
6.2 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 setup reports these reports are accessed through the safenet/400 main menu, option 11 – go to setup reports menu (go sn3 command) 1. Server status prints each server function and its security level s...
Page 69
6.3 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 usage reports these reports are accessed through the safenet/400 main menu, option 12 – go to analysis reports menu (go sn4 command). Menu sn4 options 2 through 7 also give you the ability to run aut...
Page 70
6.4 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008.
Page 71
7.1 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 chapter 7 - testing your security settings once you have planned your server function security level settings, safenet/400 gives you a method to test the settings to make sure they will provide the l...
Page 72
7.2 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 testing safenet/400 settings based on your historical data with the on-line transaction tester this is the preferred method if you would like immediate feedback. 1. From the safenet/400 main menu sel...
Page 73
7.3 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 3. In the security levels to check field: type c (current) to test transactions with your present safenet/400 server security levels type h (historical) to review the actual status received when the ...
Page 74
7.4 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 4. When you press enter and a transaction that meets your selection criteria is found, the on- line transaction testing mode screen is displayed. This describes: • the requested security level settin...
Page 75
7.5 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 • additional command keys are shown when rejections are displayed. These additional command keys will allow you to work directly with the appropriate user setting based on the rejection code. 5. You ...
Page 76
7.6 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 batch transaction test review/report – security report by user you can use this batch report to test all the historical transactions through current and future control file settings. With this report...
Page 77
7.7 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 2. Select the servers to include in the report • *all - all servers • *default - based on servers that were selected on menu sn2, option 1 - select default servers for security report • *select - dis...
Page 78
7.8 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 page down if you would like to print the report to an output file. When you have finished making your selections, enter to submit the report to batch..
Page 79
7.9 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 recommended approach to testing a recommended approach to using the on-line transaction testing program is: 1. Set all of the important server functions to security level 1, log all. This will log al...
Page 80
7.10 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 pcreview use the pcreview command or option 9 - on-line transaction review from the safenet/400 special jobs menu to review each transaction logged by safenet/400. This displays the historical trans...
Page 81
7.11 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 the on-line transaction review mode screen is displayed, supplying more detailed information about the specific transaction. You can use the roll up/roll down keys to scroll through the sequential t...
Page 82
7.12 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008.
Page 83
8.1 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 chapter 8 - backups and purges log file purge when safenet/400 is logging client requests, the information is kept in the trapod file in library pcsecdta. At times this file may grow to a considerabl...
Page 84
8.2 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 to perform a standard purge 1. Backup the trapod file to tape, if desired. You will need to issue the endtrp command before beginning the backup. 2. Select option 8 from the special jobs menu or use ...
Page 85
8.3 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 to purge the log and archive the records 1. Select option 8 from the special jobs menu or use the strprgarc command. 2. Enter the number of days to retain information in the trapod file or enter the ...
Page 86
8.4 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 automating the log file purge to automatically purge the log file, archive the purged records and generate the transaction report, use the following command or add it to the system job scheduler: sbm...
Page 87
8.5 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 automating and running the security report and the log file purge together use this method to automate both the safenet/400 security report and the log file purge. For this example, the purge is bein...
Page 88
8.6 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 this example runs the log file purge and retains only 1 day of data in the file. Saturday 1. Run security report and see entire contents of log prtsecrpt 2. Run purge and retain 1 day strprgarc days(...
Page 89
8.7 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 daily backup procedure modify your daily backup procedure to follow these guidelines: 1. Enter command chgspcset logall(*no) this prevents safenet/400 from attempting to log requests 2. Issue the end...
Page 90
8.8 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008.
Page 91
9.1 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 chapter 9 - de-activating and removing safenet/400 you must be signed on as a super admin in safenet/400 to perform any activate/de-activate processes. See ‘safenet administrator’ in chapter one of t...
Page 92
9.2 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 to activate or de-activate safenet/400: remember, you must be a safenet/400 super admin to perform this step. 1. From the special jobs menu select option 6 - activate/de-activate safenet/400 the serv...
Page 93
9.3 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 removing safenet/400 from your system if it becomes necessary to completely remove safenet/400 from your system i5, follow these steps. 1. Sign on to the system i5 as qsecofr or safenet. 2. De-activa...
Page 94
9.4 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008.
Page 95
10.1 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 chapter 10 - problem determination if safenet/400 is not working properly, there are a few general things to check. Error message received on the system i5 1. Did you perform an ipl after the initia...
Page 96
10.2 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 5. Have you made changes to server function security levels or user authority tables? If a particular request was working, and now it is not, make sure you have not inadvertently disabled a server f...
Page 97
10.3 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 error message received on the client if you receive an error message indicating a problem with a client or a communications request, or an exit program rejection and safenet/400 is active: check the...
Page 98
10.4 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 if you are unsure that safenet/400 is the source of the problem 1. Reset the security level in safenet/400 by following these directions: • from the safenet/400 main menu select option 1 – work with...
Page 99
10.5 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 if you receive a message on the system i5 about a safenet/400 or pcseclib program, or you still cannot resolve a client error or client application error, check to see if the system was ipl'd since ...
Page 100
10.6 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 if you still cannot resolve the problem 1. Check all the joblogs for the jobs in the subsystems: qsyswrk qserver 2. You may have to change the qdftjobd job description to capture the joblogs of cert...
Page 101
10.7 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 examples of client error messages some common error messages you may see on a windows95 client: this message was received on the client when the server function was set to level 2 - function disable...
Page 102
10.8 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 this message was received on the client when the user was not authorized to the sql select statement..
Page 103
10.9 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 error codes which appear in the log 1 accepted 0 rejected reason unavailable a rejected server is turned off b rejected no authority to server c rejected no authority to object d rejected no authori...
Page 104
10.10 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 r rejected auto-signon requires password s rejected telnet requires password t rejected encrypted password required u rejected no devices available v rejected unauthorized cl command x rejected err...
Page 105
10.11 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 additional troubleshooting tips pcreview command use the pcreview commands to easily view historical network transactions. You can select various filters to display only the records from the log fi...
Page 106
10.12 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008.
Page 107
11.1 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 chapter 11 - special safenet/400 considerations this section contains information on procedures that will help you manage and automate certain safenet/400 functions. Resetting level 5 within safenet...
Page 108
11.2 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 follow the instructions to de-activate the program found in chapter 9 in this guide, ‘de- activating and removing safenet/400’. 6. Re-activate safenet/400 select option 6 - activate/de-activate safe...
Page 109
11.3 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 pre-power down program point you can create a power down cl program to be called whenever the pwrdwnsys command is issued. Safenet/400 will call this program and log the request whenever the command...
Page 110
11.4 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 using automatic alert notification alert notification continually monitors network activity and can issue warning messages to up to five different message queues whenever an attempt is made to acces...
Page 111
11.5 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 activating safenet/400 alert notification 1. From the safenet/400 special jobs menu select option 7 - change alert notification status or use the chgnotify command and press f4. 2. Type *on for para...
Page 112
11.6 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 profile swapping profile swapping allows you to assign an alternate or a "swapped" user profile to be interrogated by safenet/400 and passed to os/400 for security lookups. When profile swapping is ...
Page 113
11.7 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 setting up a swap profile make sure that you have set the swapu parameter on the chgspcset command to allow profile swapping. Then follow these steps to set up your alternate profiles. 1. From the s...
Page 114
11.8 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 journaling safenet/400 security files you may wish to journal all changes made to any of the safenet/400 security files for audit purposes. Three programs are provided to assist with the journaling ...
Page 115
11.9 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 files contained in safenet/400 these files are available for you to use for any additional reporting requirements you may have. All are located in library pcsecdta. Dhcpblog contains dhcp bindings l...
Page 116
11.10 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 trapod file all logged network requests are placed in this file. This file will grow significantly over time, depending on network traffic. Be sure to pay close attention to its size and establish ...
Page 117
11.11 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 safenet/400 commands commands description addsnadm maintain safenet administrators addsnusr allows batch maintenance of safenet/400 users addusrcmd allows batch maintenance of users to commands add...
Page 118
11.12 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 commands description prtsqlusg reports sql statement usage and auto-enrollment prtsrvusg reports server usage and auto-enrollment rmvsnusr removes a user from all safenet/400 enrollments rmvsnusr1 ...
Page 119
11.13 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 commands description wrkswpprt work with swap profiles wrktcpipa work with tcp/ip address control wrkusrcmd work with user to cl commands wrkusrftp work with user to object ftp statement security w...
Page 120
11.14 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008.
Page 121
12.1 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 chapter 12 - server function descriptions this section lists all the current system i5 server functions, their descriptions and information on how they are used. The servers are alphabetized within ...
Page 122
12.2 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 original servers these servers have been provided by ibm since pc support/400 became available. Support for these original servers was designed for and is still used to service the original clients:...
Page 123
12.3 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 distributed data management description: distributed data management - 100 security checking is performed when a remote user or system accesses a system i5 file or issues an incoming remote command ...
Page 124
12.4 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 3. For version 4 of safenet/400, if *ddm is set to level 4, you must authorize each user to the cl commands they may issue to the system i5. 4. Most system i5 systems, by default, use the quser prof...
Page 125
12.5 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 original data queue server description: original data queue server - 100 a data queue is a system i5 object that is used by system i5 application programs for communications. Applications can use da...
Page 126
12.6 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 original transfer function server description: original file transfer function - 100 the client access transfer function transfers data between the system i5 system and a personal computer. Where us...
Page 127
12.7 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 4. Full control of library, object and data rights allowed. 5. At level 4, to select or extract a list of objects from within a library, you must enter the name of the library and use *all in the ob...
Page 128
12.8 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 original license management server description: original license management server - 100 the license management server ensures valid licenses are available for client access, ibm and non-ibm license...
Page 129
12.9 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 original message server description: original message server - 100 the message function server allows users to communicate with each other by sending messages. Users can communicate with other users...
Page 130
12.10 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 original remote sql server description: original remote sql server - 100 the remote sql server processes requests that are received from client access products that are using the high-level languag...
Page 131
12.11 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 original virtual print server description: original virtual print server - 100 the virtual print server is used to print data from pc application programs on system i5 printers. Where used: client ...
Page 132
12.12 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 example 2: to grant authority to only the payroll printer, enter: library or folder object or sub-folder read qusrsys payroll x.
Page 133
12.13 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 optimized servers this server support, provided by ibm with client access (now iseries access for windows) beginning with os/400 version 3 release 1, services optimized clients: windows 3.1 (16 bit...
Page 134
12.14 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 central server - client management description: central server - client mgmt - 100 the central server provides the ability to update the client management database on the system i5. Iseries access ...
Page 135
12.15 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 central server - conversion map description: central server - conversion map - 100 the central server provides support for retrieving conversion maps for clients that need them. These conversion ma...
Page 136
12.16 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 central server - license management description: central server - license mgmt - 100 the license management support provided by this server is very similar to the support in the original license ma...
Page 137
12.17 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 db2 for system i5 database access request - drda description: drda db2/400 database access request this server is used whenever a client requests a drda conversation connection. Where used: rumba a...
Page 138
12.18 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 database server - data base access - 100 description: database server - data base access - 100 this server function manipulates data base files on the system i5. It allows operations to data base f...
Page 139
12.19 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 database server - data base access - 200 description: database server - data base access - 200 this server function enables the addition of library list entries. Where used: iseries access for wind...
Page 140
12.20 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 database server - entry description: database server - entry - 100 this server function is used at server initiation request. It is the request that always comes first. All other database server re...
Page 141
12.21 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 database server - object information - 100 description: database server - object information - 100 this server function is used for requests to retrieve information about certain objects from the d...
Page 142
12.22 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 notes: 1. List retrievals from *usrlibl automatically allowed. 2. Data rights enforced. 3. At levels 3 and 4 users must be authorized to the server function. 4. At level 4 the user must be authoriz...
Page 143
12.23 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 database server - object information - 200 description: database server - object information - 200 this server function is used for requests to retrieve additional information about certain objects...
Page 144
12.24 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 database server - sql access description: database server - sql access - 100 database server – sql access – 200 (for v4r1 and above) this server function is used when certain sql requests are recei...
Page 145
12.25 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 notes: 1. At levels 3 and 4 users must be authorized to the server function. 2. At level 4 the user must be authorized to the object/library and the sql statement. Data authority requirements are d...
Page 146
12.26 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 data queue server description: data queue server - 100 a data queue is a system i5 object that is used by system i5 application programs for communications. Applications can use data queues to pass...
Page 147
12.27 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 dhcp address binding notify description: dhcp address binding notification - 100 this server assigns ip addresses to specific client hosts. Where used: any device on a tcp/ip network whenever it re...
Page 148
12.28 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 dhcp address release notify description: dhcp address release notification - 100 this server releases an ip address from its specific client host assignment binding. Where used: any device on a tcp...
Page 149
12.29 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 file server description: file server - 100 the file server function allows clients to store and access information, such as files and programs, on the system i5 in various formats. This server repl...
Page 150
12.30 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 library or folder object or sub-folder *allflr *all to enter *allflr/ *all you must be signed on as qsecofr. Proper data rights must be selected also..
Page 151
12.31 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 3. At level 4, to authorize a user for access to a non-ibm folder within the qdls file system (shared folders), you must enter two records in the object/user security file. Example 1: a user requir...
Page 152
12.32 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 systems qopensys, qfilesys.400 and home, key in the first 10 positions of each file system name only. Example: network request: /qfilesys.400/qsys.Lib/payroll.Lib/salary.Fil entries required: libra...
Page 153
12.33 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 ftp client request validation description: ftp client request validation this function is used whenever the system i5 is a client, issuing ftp commands to a remote system. Where used: system i5 com...
Page 154
12.34 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 using ftp client: • sending an object to a remote system an ftp put of object abc in an ftp client session requires *read authority to object abc on the local machine. • get an object from a remote...
Page 155
12.35 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 ftp logon server description: ftp logon server 1 - 100 this server is used any time the system i5 answers an ftp start request from another system or user. It is available in os/400 versions v3r7 t...
Page 156
12.36 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 ftp logon server description: ftp logon server 2 - 200 this server is used any time the system i5 answers an ftp start request from another system or user. It is available in os/400 versions v4r2 a...
Page 157
12.37 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 ftp logon server description: ftp logon server 3 – 300 this server is used any time the system i5 answers an ftp start request from another system or user. It is available in os/400 versions v5r1 o...
Page 158
12.38 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 ftp server request validation description: ftp server request validation this function is used whenever the system i5 receives an ftp command it must act upon. Where used: internets and intranets m...
Page 159
12.39 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 network print server - entry description: network print server - entry - 100 this server function is used when the network print server is started. Where used: iseries access for windows server ide...
Page 160
12.40 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 network printer server - spool file description: network print server - spool file - 100 this server function is used after the network print server receives a request to process an existing spoole...
Page 161
12.41 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 pre-power down description: pre-power down server this program is called whenever the pwrdwnsys or endsys command is issued where used: any interface, command line or program that can issue the pwr...
Page 162
12.42 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 remote command and distributed program call server description: remote command/program call - 100 the remote command and distributed program call server is provided to allow client users and applic...
Page 163
12.43 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 rexec logon server description: rexec logon server 1 - 100 this server is used to validate a client request to start the rexec server. It is available in all versions of os/400. Where used: windows...
Page 164
12.44 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 rexec logon server description: rexec logon server 2 - 200 this server is used to validate a client request to start the rexec server. It is available in os/400 versions v5r1 and above. Where used:...
Page 165
12.45 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 rexec request validation server description: rexec request validation server this server is initiated whenever a client issues a rex statement to the system i5. Where used: windows and os/2 desktop...
Page 166
12.46 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 showcase strategy** validation server description: showcase strategy validation server this server is initiated by a client utilizing the showcase strategy** product with the proper exit point adde...
Page 167
12.47 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 tcp signon server description: tcp signon server - 100 the signon server provides security for clients that use tcp/ip communications support. This security function prevents access to the system i...
Page 168
12.48 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 telnet device initialization telnet device termination description: telnet device initialization - *telneton telnet device termination - *telnetoff the telnet servers provide for security when usin...
Page 169
12.49 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 tftp server request validation description: tftp server request validation clients utilizing tftp (trivial file transfer protocol), such as the ibm net station use this server. Where used: ibm net ...
Page 170
12.50 safenet/400 reference guide © copyright 2008 mp associates of westchester, inc. V8.50 - may 2008 user profile servers description: add user profile change user profile delete user profile restore user profile these servers are called each time a user profile command is issued. Where used: any ...
Page 171
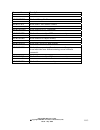
Index a administrator ...................................................................... 1.3 alert notification ........................................... 11.4, 11.5, 11.11 anonymous ................................................... 4.1, 4.2, 4.3, 4.4 anonymous ftp ..............................
Page 172
U user profiles *public .......... 1.5, 1.7, 1.10, 1.11, 1.12, 1.14, 1.17, 1.19 group............................................................................ 1.1 swapping ................................................ 10.10, 11.6, 11.7 users copying ...............................................