- DL manuals
- IBM
- Server
- SC34-6814-04
- Customization Manual
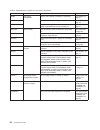
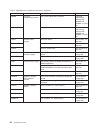
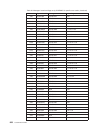
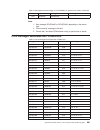
IBM SC34-6814-04 Customization Manual - Contents
Contents
Preface . . . . . . . . . . . . . . . . . . . . . . . . . . . xvii
What this book is about . . . . . . . . . . . . . . . . . . . . . xvii
Who this book is for . . . . . . . . . . . . . . . . . . . . . . . xvii
What you need to know to understand this book . . . . . . . . . . . . xvii
How to use this book . . . . . . . . . . . . . . . . . . . . . . xvii
Notes on terminology . . . . . . . . . . . . . . . . . . . . . . xvii
Syntax notation and conventions used in this book . . . . . . . . . . . xviii
Summary of changes . . . . . . . . . . . . . . . . . . . . . . xix
Changes for CICS Transaction Server for z/OS, Version 3 Release 2 . . . . . xix
Changes for CICS Transaction Server for z/OS, Version 3 Release 1 . . . . . xix
Changes for CICS Transaction Server for z/OS, Version 2 Release 3 . . . . . xx
Part 1. Customizing with user exit programs . . . . . . . . . . . . . . . . . . 1
Chapter 1. Global user exit programs . . . . . . . . . . . . . . . . 3
Writing global user exit programs
. . . . . . . . . . . . . . . . . . 3
Register conventions . . . . . . . . . . . . . . . . . . . . . . 3
31-bit addressing implications . . . . . . . . . . . . . . . . . . . 4
Using CICS services . . . . . . . . . . . . . . . . . . . . . . 4
Using channels and containers
. . . . . . . . . . . . . . . . . . 5
Assembler programs and LEASM
. . . . . . . . . . . . . . . . . 6
EDF and global user exits . . . . . . . . . . . . . . . . . . . . 6
The global work area . . . . . . . . . . . . . . . . . . . . . . 6
Making trace entries . . . . . . . . . . . . . . . . . . . . . . 6
Parameters passed to the global user exit program . . . . . . . . . . . 7
Returning values to CICS . . . . . . . . . . . . . . . . . . . . 10
Restrictions on the use of fields as programming interfaces
. . . . . . . 11
Exit programs and the CICS storage protection facility
. . . . . . . . . 11
Errors in user exit programs . . . . . . . . . . . . . . . . . . . 12
Defining, enabling, and disabling an exit program . . . . . . . . . . . . 12
Viewing active global user exits . . . . . . . . . . . . . . . . . . . 13
Invoking more than one exit program at a single exit . . . . . . . . . . . 13
Invoking a single exit program at more than one exit . . . . . . . . . . . 14
Making programs threadsafe . . . . . . . . . . . . . . . . . . . . 14
Sample global user exit programs . . . . . . . . . . . . . . . . . . 15
Basic sample and example programs
. . . . . . . . . . . . . . . 15
Sample programs for specific exits
. . . . . . . . . . . . . . . . 18
Alphabetical list of global user exit points . . . . . . . . . . . . . . . 25
Global user exit points by functional area . . . . . . . . . . . . . . . 32
Activity keypoint program exit XAKUSER . . . . . . . . . . . . . . 32
Application Associated Data exit, XAPADMGR, in the AP domain . . . . . 33
Basic Mapping Support exits XBMIN and XBMOUT . . . . . . . . . . 34
Bridge facility exit XFAINTU . . . . . . . . . . . . . . . . . . . 38
Data tables management exits XDTRD, XDTAD, and XDTLC . . . . . . . 40
DBCTL interface control program exit XXDFA
. . . . . . . . . . . . 45
DBCTL tracking program exits XXDFB and XXDTO . . . . . . . . . . 46
Dispatcher domain exits XDSBWT and XDSAWT . . . . . . . . . . . 47
DL/I interface program exits XDLIPRE and XDLIPOST . . . . . . . . . 48
Dump domain exits XDUREQ, XDUREQC, XDUCLSE, and XDUOUT. . . . 53
Enqueue EXEC interface program exits XNQEREQ and XNQEREQC. . . . 60
EXEC interface program exits XEIIN, XEIOUT, XEISPIN, and XEISPOUT
67
File control domain exits, XFCFRIN and XFCFROUT . . . . . . . . . . 72
© Copyright IBM Corp. 1977, 2011
iii
Summary of SC34-6814-04
Page 1
Cics transaction server for z/os customization guide version 3 release 2 sc34-6814-04.
Page 3
Cics transaction server for z/os customization guide version 3 release 2 sc34-6814-04.
Page 4
Note! Before using this information and the product it supports, be sure to read the general information under “notices” on page 923. This edition applies to version 3 release 2 of cics transaction server for z/os, program number 5655-m15, and to all subsequent versions, releases, and modifications ...
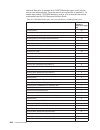
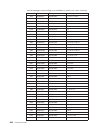
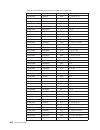
Page 5: Contents
Contents preface . . . . . . . . . . . . . . . . . . . . . . . . . . . Xvii what this book is about . . . . . . . . . . . . . . . . . . . . . Xvii who this book is for . . . . . . . . . . . . . . . . . . . . . . . Xvii what you need to know to understand this book . . . . . . . . . . . . Xvii how to...
Page 6
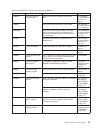
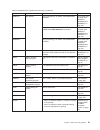
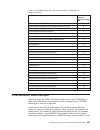
File control exec interface api exits xfcreq and xfcreqc . . . . . . 85 file control exec interface spi exits xfcareq and xfcareqc . . . . . 98 file control file state program exits xfcsreq and xfcsreqc . . . . . 111 file control open/close program exit xfcnrec . . . . . . . . . . . 121 file control...
Page 7
Recursion within a task-related user exit program. . . . . . . . . . . 290 purging tasks . . . . . . . . . . . . . . . . . . . . . . . . 290 using cics services in your task-related user exit program . . . . . . . 291 using channels and containers . . . . . . . . . . . . . . . . . 292 assembler prog...
Page 8
The define_program call . . . . . . . . . . . . . . . . . . 353 the acquire_program call . . . . . . . . . . . . . . . . . 356 the release_program call . . . . . . . . . . . . . . . . . 358 the delete_program call . . . . . . . . . . . . . . . . . . 359 log manager xpi functions . . . . . . . . . . ...
Page 9
Storage keys for plt programs . . . . . . . . . . . . . . . . . 430 part 3. Customizing with user-replaceable programs . . . . . . . . . . . . . 433 chapter 5. General notes about user-replaceable programs . . . . . . 435 rewriting user-replaceable programs . . . . . . . . . . . . . . . . 435 assemb...
Page 10
Coding for specific vtam sense codes . . . . . . . . . . . . . . 508 writing multiple neps . . . . . . . . . . . . . . . . . . . . . 508 dfhznepi macros . . . . . . . . . . . . . . . . . . . . . . 508 handling shutdown hung terminals in the node error program . . . . . . 510 using the node error pro...
Page 11
The sample autoinstall control program for appc connections . . . . . . . 550 default actions of the sample program . . . . . . . . . . . . . . . 550 resource definitions . . . . . . . . . . . . . . . . . . . . . 551 chapter 13. Writing a program to control autoinstall of ipic connections 553 autoin...
Page 12
Routing transactions dynamically . . . . . . . . . . . . . . . . . . 590 dynamic transactions . . . . . . . . . . . . . . . . . . . . . 590 when the dynamic routing program is invoked . . . . . . . . . . . . 590 information passed to the dynamic routing program . . . . . . . . . . 591 changing the t...
Page 13
When the distributed routing program is invoked . . . . . . . . . . . 632 changing the target cics region . . . . . . . . . . . . . . . . . 633 telling cics whether to route the method request . . . . . . . . . . 634 if an error occurs in route selection . . . . . . . . . . . . . . . . 634 invoking ...
Page 14
Event codes . . . . . . . . . . . . . . . . . . . . . . . . . 681 the ejb event sample program . . . . . . . . . . . . . . . . . . 682 actions of the default program . . . . . . . . . . . . . . . . . . 682 writing your own ejb event program . . . . . . . . . . . . . . . 682 chapter 25. Writing progr...
Page 15
Chapter 28. Cics monitoring . . . . . . . . . . . . . . . . . . 743 introduction to cics monitoring . . . . . . . . . . . . . . . . . . 743 how cics monitoring data is passed to smf . . . . . . . . . . . . 743 coding additional event-monitoring points . . . . . . . . . . . . . 744 application naming...
Page 16
Part 8. Examining and modifying resource attributes . . . . . . . . . . . . . 807 chapter 33. Using the programmable interface to ceda . . . . . . . . 809 when to use the programmable interface . . . . . . . . . . . . . . . 810 using dfhedap in a dtp environment . . . . . . . . . . . . . . . 810 cha...
Page 17
Appendix f. The example program for the xtsereq global user exit, dfh$xtse . . . . . . . . . . . . . . . . . . . . . . . . . 877 appendix g. Threadsafe xpi commands . . . . . . . . . . . . . . 893 bibliography . . . . . . . . . . . . . . . . . . . . . . . . . 895 the cics transaction server for z/os...
Page 18
Xvi customization guide.
Page 19: Preface
Preface what this book is about this book provides the information needed to extend and modify an ibm ® cics ® transaction server for z/os ® system to match your requirements. It describes how you can tailor your system by coding exit programs, by replacing specific cics-supplied default programs wi...
Page 21: Summary Of Changes
Summary of changes this book is based on the cics customization guide for cics transaction server for z/os, version 3 release 1, sc34-6429-00. Changes from that edition are marked by vertical bars in the left margin. Changes for cics transaction server for z/os, version 3 release 2 for information a...
Page 22
Changes for cics transaction server for z/os, version 2 release 3 the more significant changes for this edition were: v a new global user exit, xiceres, in the interval exec interface control program, was described in the xiceres global user exit and “using the xiceres exit to check the availability...
Page 23
Part 1. Customizing with user exit programs © copyright ibm corp. 1977, 2011 1.
Page 24
2 customization guide.
Page 25
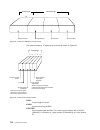
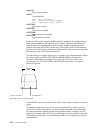
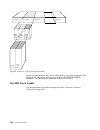
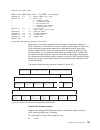
Chapter 1. Global user exit programs you can use the cics global user exit points, in conjunction with programs of a special type that you write yourself (global user exit programs), to customize your cics system. A global user exit point, sometimes referred to as a global user exit is a place in a ...
Page 26
V register 13 contains the address of the standard register save area where your exit program should store its own registers immediately after being invoked. This address is also in the field uepepsa in the parameter list pointed to by register 1. If you want to issue operating system requests that ...
Page 27
An exit program invoked at an exit that does not support the use of exec cics commands must not call a task-related user exit program (true). Calling a true is equivalent to issuing an exec cics command. Exceptions to this rule are programs invoked from the xfcfrin and xfcfrout exits, which may call...
Page 28
Assembler programs and leasm assembler programs translated with the leasm option cannot be used as global user exit programs. Leasm is used to produce language environment conforming main programs in assembler. For information about the leasm translator option, see the cics application programming g...
Page 29
V if your global user exit is in a domain, you can add extra trace calls to provide additional diagnostic information by setting the ap option of exec cics set tracetype to level 1 or 2. V depending on which exit point you are using, you might be able to use the xpi dfhtrptx trace_put macro to creat...
Page 30
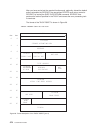
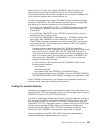
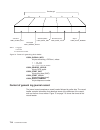
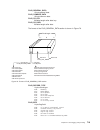
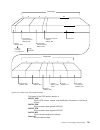
* (zero = no work area) uepgal ds a address of global work area length uepcrca ds a address of current return-code ueptca ds a reserved uepcsa ds a reserved uepepsa ds a address of register save area * for use by exit program uephmsa ds a address of save area used for * host module’s registers uepgi...
Page 31
Apart from register 15, which contains the return code value from the exit program, the values in this save area are used by cics to reload the registers when returning to the calling cics module. They should not be corrupted. This address is not passed to global user exit programs invoked from exit...
Page 32
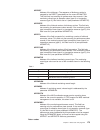
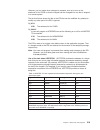
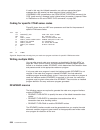
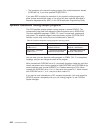
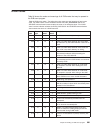
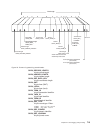
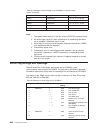
Table 1. Tcb indicators in dfhuepar (continued). Description symbolic value 2-byte code description ueptx9 x9 an x9 open tcb, used for c and c++ programs, compiled with the xplink option, that are in user key uepstack points to the kernel stack entry. This value must be moved to the exit program’s r...
Page 33
If you supply a return code value that is not expected at a particular exit point, the default return code indicating a normal response (usually uercnorm) is assumed, unless you set the return code uercpurg. You are strongly advised not to let the return code default to the normal response as the re...
Page 34
Storage. However, on an exec cics getmain command, the exit program can override the taskdatakey option by specifying either cicsdatakey or userdatakey. V when an exit program obtains storage using an xpi getmain call, the storage key depends on the value specified on the storage_class option, which...
Page 35
V otherwise, use the exec cics enable command to enable the user exit program. If you enable a global user exit program before it has been installed and lpa=yes is specified as a system initialization parameter, cics scans the lpa for the program. If message dfhld0109i is issued, it means that cics ...
Page 36
– if the new program supplies a different return code value from the current value addressed by uepcrca, cics ignores both values and resets the “current return code” to the default value, usually uercnorm, before calling any further exit programs for that exit point. – if the new program sets an el...
Page 37
If a cics db2 application program has been written and defined as threadsafe to obtain the benefits of the cics open transaction environment (ote), the benefit is lost if tcb switching is caused by a non-threadsafe exit program. You should pay particular attention to exit programs used on the mainli...
Page 38
V share a gwa between global user exit programs, thereby making the information it contains available to more than one program, and overcoming limitations on the size of gwas. V access information held in a global user exit program’s gwa. The gwa sample programs and copy books are: dfh$pcex a sample...
Page 39
V uses the start option of the exec cics enable command to make dfh$pcex available for execution. This causes dfh$pcex to be driven for all links and xctls. V links to the dummy program, dfh$pcpl, in order to drive dfh$pcex. V uses the stop option of the exec cics disable command to make dfh$pcex un...
Page 40
Example program as well as the sample programs supplied in source code, there is an example listing, dfh$xtse, that shows you how to: v use exec cics commands in a global user exit program v use exec cics commands and xpi calls in the same exit program v modify the command parameter list in exec int...
Page 41
Dfh$dtrd a sample global user exit program, designed to be invoked at the xdtrd exit. Dfh$dtad, dfh$dtlc, and dfh$dtrd are listed in the cics shared data tables guide. Related concepts: “data tables management exits xdtrd, xdtad, and xdtlc” on page 40 data tables management exits apply to both cics ...
Page 42
A batch update run that has overridden retained locks. See “dfh$fcbv sample global user exit program” on page 134. Dfh$fcld a sample exit program designed to be invoked at the xfcldel exit, which allows you to perform logical deletion of records from a vsam esds data set or a bdam data set, during b...
Page 43
Proxy=proxyurl this optional keyword stores the url (in the form http://proxyserver) of a proxy server into the web global work area, then enables the supplied dfh$wbex sample program as the xwbopen global user exit. Ldapbind=profilename this optional keyword stores the name of an ldap bind profile ...
Page 44
Racfcid=uuuuuuuu is the current userid, obtained from uepuser ibm-httprealm=rrrrrrrr is the http 401 realm, obtained from ueprealm (if this exists) labeleduri=xxxxxxxx is the target url, obtained by concatenating “http://” with the hostname from uephost and the path from ueppath cn=basicauth is an a...
Page 45
Note: it is not necessary to specify a pipeline in the dfhws-pipeline container. The pipeline is dynamically created by dfhpirt when channel(dfhwstc-v1) is specified on the command. V links to dfhpirt, specifying channel(dfhwstc-v1), after constructing all the required containers. This sends the req...
Page 46
Related concepts: “the sample xmeout global user exit programs” on page 171 the mro and appc session queue management sample exit program this sample program implements the same basic function provided by the queuelimit and maxqtime parameters on a connection resource definition. These parameters ar...
Page 47
Xpcta exit, to test whether the abend was caused by a storage protection exception condition. It is described on page “the sample xpcta global user exit program, dfh$pcta” on page 191. Related concepts: “the sample xpcta global user exit program, dfh$pcta” on page 191 the terminal-not-known sample e...
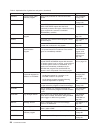
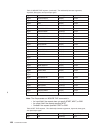
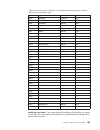
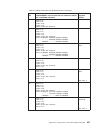
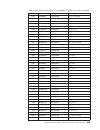
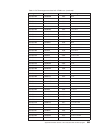
Page 48
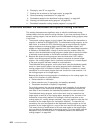
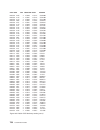
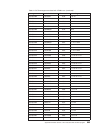
Table 2. Alphabetical list of global user exit points (continued) exit name module or domain where or when invoked topic xdtad data tables management when a write request is issued to a data table. “exit xdtad” on page 43 xdtlc at the completion of loading of a data table. “exit xdtlc” on page 44 xd...
Page 49
Table 2. Alphabetical list of global user exit points (continued) exit name module or domain where or when invoked topic xfcbfail file control recovery control program when an error occurs during the backout of a uow. “exit xfcbfail, file control backout failure exit” on page 127 xfcbout when cics i...
Page 50
Table 2. Alphabetical list of global user exit points (continued) exit name module or domain where or when invoked topic xicereq interval control exec interface program before cics processes an interval control api request. “exit xicereq” on page 146 xicereqc after an interval control api request ha...
Page 51
Table 2. Alphabetical list of global user exit points (continued) exit name module or domain where or when invoked topic xpcabnd program control program after a transaction abend and before a dump call is made. “exit xpcabnd” on page 192 xpceres before cics processes a program link or link3270 bridg...
Page 52
Table 2. Alphabetical list of global user exit points (continued) exit name module or domain where or when invoked topic xszarq front end programming interface after a fepi request has completed. “front end programming interface exits xszarq and xszbrq” on page 137 xszbrq before a fepi request is ac...
Page 53
Table 2. Alphabetical list of global user exit points (continued) exit name module or domain where or when invoked topic xwbauth web domain during processing of an exec cics web send command. “http client open and send exits: xwbauth, xwbopen and xwbsndo” on page 138 xwbopen during processing of an ...
Page 54
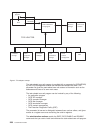
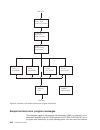
Global user exit points by functional area the exit points are grouped according to their functional relationships. This usually means according to the cics module or domain in which they occur. However, where exit points in different modules serve a similar function, the exits are grouped under a g...
Page 55
Return codes uercnorm continue processing. Xpi calls xpi must not be used. Api and spi calls the following commands are supported: v address cwa v address eib v link (but only to local programs; distributed program links may not be used). V return v write journalname. Application associated data exi...
Page 56
Uercnorm continue processing. Xpi calls all can be used. Api and spi calls all can be used, except for: v exec cics abend v exec cics perform shutdown sample exit program, dfh$apad cics provides a sample global user exit program, dfh$apad, for use at the xapadmgr exit point. The exit program is invo...
Page 57
V use the mapset name, map name, and field length defined in the map, and the actual length of field data placed in the outbound datastream v modify the data in each field v modify the attributes sent with each field. Both exits are passed four exit-specific parameters: 1. The address of the tctte a...
Page 58
Uepbmtct address of the tctte associated with the mapping request. Uepexecb address of the system eib associated with the task. Uepbmcnt address of the halfword binary number of “field elements” in the field element table. Uepbmtab address of the field element table. Return codes uercnorm continue p...
Page 59
Bmxactln is a halfword binary value which contains the actual length of the data received or transmitted in this field. Bmxdata is the address of the field data. In the xbmin exit, bmxdata points into a work area which bms has obtained for input mapping purposes. When the exit returns control, this ...
Page 60
When modifying data in the xbmin exit, the safest method is to use the length provided in bmxmapln, but to ensure that any pad characters added by bms are preserved. Bmxattr must be ignored in the xbmin exit; it always contains binary zeroes. Programming the xbmout exit this section contains some co...
Page 61
Exit-specific parameters uepfareq address of a 1-byte field that indicates why the exit has been called. Possible values are: uepfain initialization. Uepfatu tidy-up. Uepfatut address of a 1-byte field that indicates the type of tidy-up required. Possible values are: uepfantu normal tidy-up. Uepfaet...
Page 62
Return codes uercnorm continue processing. Xpi calls all can be used, except those that use recoverable resources. Api calls all can be used except those that invoke task-related user exits or use recoverable resources. Data tables management exits xdtrd, xdtad, and xdtlc data tables management exit...
Page 63
Note: for additional information about using these exits with cics shared data table support, see the cics shared data tables guide. Related concepts: “the data tables sample exit programs” on page 18 exit xdtrd the xdtrd user exit is invoked just before cics attempts to add to the data table a reco...
Page 64
Uepdtcmt (x'40') this is a cics-maintained table. Only meaningful if uepdtsdt is on. Uepdtopt (x'20') the exit has been invoked for table loading. This means that optimization by skipping can be requested. Uepdtcft(x'10') the exit has been invoked by coupling facility data table support. Uepdtumt (x...
Page 65
Xpi calls all can be used. Exit xdtad the xdtad user exit is invoked when a write request is issued to a data table. V for a user-maintained data table and coupling facility data table, the user exit is invoked once—before the record is added to the data table. V for a cics-maintained data table, th...
Page 66
Uepdtrbl the fullword length of the data table buffer. Uepdtrl the fullword length of the data record. Uepdtka the address of the data table key. Uepdtkl the fullword length of the data table key. Uepdtdsl the fullword length of the name of the source data set. Only meaningful if either uepdtsdt or ...
Page 67
Uepdtcmt (x'40') this is a cics-maintained table. Only meaningful if uepdtsdt is on. Uepdtcft(x'10') the exit has been invoked by coupling facility data table support. Uepdtumt (x'08') this is a user-maintained table. Only meaningful if uepdtsdt is on. Uepdtorc data table open result code. The possi...
Page 68
Uercabdu abend cics with a dump. Xpi calls transaction_dump must not be used. Dbctl tracking program exits xxdfb and xxdto exit xxdfb when invoked by the alternate cics when it receives a message from the active cics indicating that connection to dbctl has failed. The alternate and active cics syste...
Page 69
Exit-specific parameters uepdbxr address of cics xrf information for use with dbctl. The cics xrf information can be mapped using the dsect dfhdxuep. Return codes uercnoac take no action. Uercswch switch to the alternate dbctl. Uercabno abend cics without a dump. Uercabdu abend cics with a dump. The...
Page 70
Xpi calls must not be used. Exit xdsawt when invoked after an operating system wait issued by the quasireentrant cics tcb. Exit-specific parameters uepsysrc address of the 4-byte return code from the sysevent request made before the operating system wait. This return code will be in one of two diffe...
Page 71
1. The descriptions of the exits that follow show the general format of the application’s parameter list. For detailed information about the format of the call-level dl/i parameter list, refer to the ims/esa ® application programming: dl/i calls manual. 2. For all exec dli calls, the application’s p...
Page 72
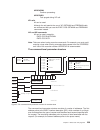
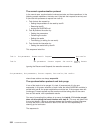
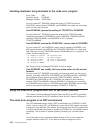
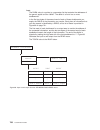
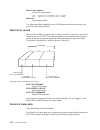
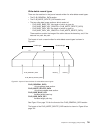
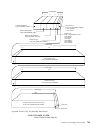
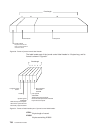
Uepaplist address of application’s parameter list. The general format for cobol and assembler language is: plist address --> parm1 address --> parm1 parm2 address --> parm2 parm3 address --> parm3 .............. Up to a maximum of 18 parameters excluding the optional parmcount. The general format fo...
Page 73
Ueppsb1 a psb exists. Ueppsbnm address of an area containing the 8-character psb name. The contents of the area can be overwritten by the exit, for all types of request including uepcship; the new contents are used when the dl/i request is processed. Uepsysdx address of the sysid existence flag byte...
Page 74
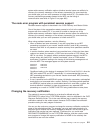
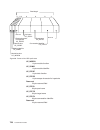
The general format for pl/i is: plist address --> parm1 address --> parm1 (parmcount) parm2 address --> locator descriptor --> parm2 parm3 address --> locator descriptor --> parm3 .............. Up to a maximum of 18 parameters. When uepctype is not uepcship, your exit program can change any of the ...
Page 75
Return codes uercnorm continue processing. Uercpurg task purged during xpi call. Xpi calls all can be used. Dump domain exits xdureq, xdureqc, xduclse, and xduout there are four exits in the dump domain. Related concepts: “the dump domain sample exit program” on page 19 exit xdureq when invoked imme...
Page 76
Uepdsyst a system dump was requested. Note: the dump-type identifier indicates the type of dump request that was passed to the dump domain. It does not reflect any modification that may have been made to the original request by a user entry in the dump table. Uepxdscp address of a 1-byte field indic...
Page 77
Uepxdmax address of a 4-byte field which contains the current dump table maximum setting. This field may be modified by the exit to change the current dump table maximum setting. A change to the maximum setting will not suppress this dump request. A return code of uercbyp may be used to suppress the...
Page 78
3. The field addressed by uepfmod contains '????????'—the failure was not in application code, but cics was unable to determine the name of the failing module. Return codes uercnorm continue processing. Uercbyp suppress dump. Uercpurg task purged during xpi call. Xpi calls wait_mvs can be used only ...
Page 79
Uepdumpt address of the 1-byte dump-type identifier, which contains one of the following values: uepdtran a transaction dump was requested. Uepdsyst a system dump was requested. Note: the dump-type identifier indicates the type of dump request that was passed to the dump domain. It does not reflect ...
Page 80
Uepxdno the cics system is not to shutdown. This field may be modified by the exit to update the dump table shutdown setting. Uepxdmax address of a 4-byte field which contains the current dump table maximum setting. This field may be modified by the exit to change the current dump table maximum sett...
Page 81
Exit xduclse when invoked immediately after a transaction dump data set has been closed. Exit-specific parameters ueptranid address of the 4-byte transaction id. Uepuser address of the 8-byte user id. Uepterm address of the 4-byte terminal id. Uepprog address of the 8-byte application program name. ...
Page 82
Uepdmpdy buffer is about to be written, and the cics dump data set is a dummy file or is closed. Uepdmpbf address of the dump buffer, whose length is addressed by the parameter uepdmplen. Uepdmplen address of the 2-byte dump-buffer length. Return codes uercnorm continue processing. Uercbyp suppress ...
Page 83
Uepnqtok address of a 4-byte area which can be used to pass information between xnqereq and xnqereqc for a single enqueue request. Ueprcode address of a 6-byte hexadecimal copy of the eib return code eibrcode. For details of eib return codes, see eib fields, in the cics application programming refer...
Page 84
Uepclps address of a copy of the command parameter list. See “the command-level parameter structure” on page 63. Uepnqtok address of a 4-byte area which can be used to pass information between xnqereq and xnqereqc for a single enqueue request. Ueprcode address of a 6-byte hexadecimal copy of the eib...
Page 85
Non-zero value. To help you set values for eibrcode, eibresp, and eibresp2, the values used by the enqueue domain are specified in dsect dfhnqued. Note: take care when issuing recursive commands not to cause a loop. For example, it is your responsibility to avoid entering a loop when issuing an enqu...
Page 86
Nq_funct one byte that defines the type of request: x'04' enq x'06' deq nq_bits1 existence bits that define which arguments were specified. To obtain the argument associated with a keyword, you need to use the appropriate address from the command-level parameter structure. Before using this address,...
Page 87
2. There are no output fields on exec cics enq and deq requests. Modifying the eid: it is not possible to modify the eid to make major changes to requests. It is not possible, for example, to change an enq request to a deq request. However, you can make minor changes to requests, such as to turn on ...
Page 88
1. Cics does not check changes to argument values, so any changes must be verified by the user exit program making the changes. 2. It is not advisable for xnqereqc to modify input arguments. Adding user arguments: global user exit programs can add arguments associated with the length and maxlifetime...
Page 89
– applies only to resource names of length equal to or greater than that of your replacement string. – is an alternative to method a when a resource name too long to allow the use of that method. Method c place a 4-character scope value in uepscope, and return uercscpe in r15. This will bypass any i...
Page 90
Xeiout invoked after the execution of any exec cics api or spi command. Xeispout invoked after the execution of any exec cics spi command except those listed for xeispin. The sequence is: command – edf – xeispout – xeiout – trace note: asynchronous processing of these exits may occur if the transact...
Page 91
This particular example of the danger of tampering with argument 0 does not apply to cobol or c application programs, but nevertheless you should not modify cics commands for application programs written in any supported language. Bypassing commands an xeiin or xeispin exit program can bypass execut...
Page 92
Uercpurg task purged during xpi call. Xpi calls all can be used. Exit xeispin when invoked before the execution of any exec cics spi command except: v exec cics enable v exec cics disable v exec cics extract exit v exec cics perform dump v exec cics resync entryname exit-specific parameters ueparg a...
Page 93
Xpi calls all can be used. Exit xeiout when invoked after the execution of any exec cics api or spi command. Exit-specific parameters ueparg address of the exec command parameter list. Uepexecb address of the system eib. Uepusid address of the 8-character userid. Ueppgm address of the 8-character ap...
Page 94
Exit-specific parameters ueparg address of the exec command parameter list. Uepexecb address of the system eib. Uepusid address of the 8-character userid. Ueppgm address of the 8-character application program name. Uepload address of the application program's load-point. Ueprsa address of the applic...
Page 95
V an internal cics request to process a system file. Note that: v if the exit program passes the request to cics file control (without choosing to redirect it to a remote region), it is not allowed to make changes to any of the parameters. V if the exit program intercepts the request and bypasses fi...
Page 96
Exit xfcfrin when invoked before the execution of a file control request. The request may have originated from: v the execution of an application request to process a user file v the receipt of a function-shipped request v an internal cics request to process a system file. Exit-specific parameters u...
Page 97
Uep_fc_buffer_l address of a fullword containing (for read, read next, and read prev requests) the value of the length of the buffer into which the record is to be read. Uep_fc_record_p address of one of the following: v if the request is a read, read next, or read prev with the set option, a fullwo...
Page 98
The full length of the record identifier is returned as a mandatory output field on read next and read prev requests. The value is used by cics function shipping. Uep_fc_record_id_type address of a byte containing (for read, write, delete, start br, read next, read prev, and reset br requests) the r...
Page 99
Uep_fc_sequential_write records are to be written in sequential mode. Uep_fc_direct_write records are to be written in direct mode. Uep_fc_read_integrity address of a byte containing (for non-update read, read next, and read prev requests) the read integrity setting. (in current versions of cics, th...
Page 100
Uep_fc_duplicate_key_code address of a 1-byte output area indicating whether the request found more than one record for the supplied key. The possible values are: v uep_fc_duplicate key v uep_fc_not_duplicate key uep_fc_accmeth_return_code address of a 4-byte output area in which access-method- depe...
Page 101
V uep_fc_reason_duplicate_record v uep_fc_reason_duplicate_reqid v uep_fc_reason_end_of_file v uep_fc_reason_file_disabled v uep_fc_reason_file_not_open v uep_fc_reason_file_not_found v uep_fc_reason_full_key_wrong_length v uep_fc_reason_generic_delete_not_ksds v uep_fc_reason_generic_key_too_long v...
Page 102
Uercbypl bypass cics processing of this request. If the exit program has been invoked for a function-shipped request, the mirror transaction must not terminate. Uercpurg task purged during xpi call. Xpi calls all can be used. Api and spi calls none can be used. Exit xfcfrout when invoked after the c...
Page 103
Uep_fc_buffer_p address of a fullword containing the address of the buffer provided by the originator of the request, in which the record is returned on completion of a read, read next, or read prev request with the into option. Uep_fc_buffer_l address of a fullword containing (for read, read next, ...
Page 104
Uep_fc_key vsam ksds or aix path access uep_fc_rba vsam esds or ksds via rba access uep_fc_rrn vsam rrds access uep_fc_debkey bdam deblocking by key (read, delete, start br, and reset br requests only) uep_fc_debrec bdam deblocking by relative record (read, delete, start br, and reset br requests on...
Page 105
Uep_fc_cr consistent read integrity. Uep_fc_fct_value read integrity according to the setting in the file definition. Uep_fc_nri no read integrity. Uep_fc_rr repeatable read integrity. Uep_fc_token address of a fullword containing the value of token. If the request is read, read next, or read prev w...
Page 106
Uep_fc_reason address of a 1-byte area containing, if the request completed with an exception response, the reason. The possible reasons are: v uep_fc_reason_abend v uep_fc_reason_accmeth_request_error v uep_fc_reason_bdam_delete v uep_fc_reason_bdam_length_change v uep_fc_reason_bdam_key_conversion...
Page 107
V uep_fc_reason_notauth v uep_fc_reason_not_extended v uep_fc_reason_previous_rls_failure v uep_fc_reason_rba_access_to_rls_ksds v uep_fc_reason_read_not_authorised v uep_fc_reason_readprev_in_generic_browse v uep_fc_reason_reclen_exceeds_logger_bfsz v uep_fc_reason_record_busy v uep_fc_reason_recor...
Page 108
Note: for information about the xfcareq and xfcareqc exits that are invoked for file control spi requests, see “file control exec interface spi exits xfcareq and xfcareqc” on page 98. Important the xfcreq and xfcreqc exits are not invoked, on the target region, for function-shipped requests. That is...
Page 109
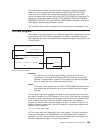
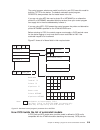
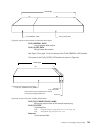
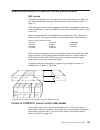
V the address of a 16-byte area that is used if the request has been function shipped. The command-level parameter structure the command-level parameter structure consists of a series of addresses. The first address points to the exec interface descriptor (eid), which consists of a bit string that d...
Page 110
Fc_group always x'06', indicating that this is a file control request. Fc_funct one byte that defines the type of request: x'02' read x'04' write x'06' rewrite x'08' delete x'0a' unlock x'0c' startbr x'0e' readnext x'10' readprev x'12' endbr x'14' resetbr fc_bits1 existence bits that define which ke...
Page 111
X'04' massinsert specified. X'02' rrn specified. X'01' set (and not into) was specified. Note: your program must test for keywords at the bit level, because there may be more than one of these keywords present. Fc_eidopt6 indicates whether certain keywords that do not take values were specified on t...
Page 112
X'08' xrba specified. If the xrba bit is on, fc_ridfld (described in dsect dfhfceds) points to an 8-byte extended relative byte address (xrba). Fc_addr1 is the address of an 8-byte area containing the name specified on the file keyword. Fc_addr2 is the address of one of the following: v a 4-byte add...
Page 113
Modifying fields in the command-level parameter structure some fields that are passed to file control are used as input to the request, some are used as output fields, and some are used for both input and output. The method your user exit program uses to modify a field depends on the usage of the fi...
Page 114
Modifying input fields: the correct method of modifying an input field is to create a new copy of it, and to change the address in the command-level parameter list to point to your new data. Note: you must never modify an input field by altering the data that is pointed to by the command-level param...
Page 115
X'04' repeatable specified. X'02' update specified on readnext or readprev. X'01' nosuspend specified (on read, readnext, readprev, write, delete, or rewrite). Bits in the eid should be modified in place. You should not modify the pointer to the eid: any attempt to do so is ignored by cics. The eid ...
Page 116
Use of the parameter uepfship uepfship contains the address of a 16-byte area. This area consists of 4 characters, followed by 3 fullwords. If the first byte contains 'y', this request has been function shipped to this region. In this case, if your exit program wants to bypass file control (by setti...
Page 117
In xfcreqc: 1. Check ‘ueprcode’ to make sure that the file control request completed without error. 2. Use uepfctok to find the address of the area. This area now holds the compressed data. 3. Decompress the data in place. 4. Copy the data from the new area to the user’s into area. Use the user-spec...
Page 118
Uepfship address of a 16 byte area. See “use of the parameter uepfship” on page 94. Ueprsrce address of an 8-character copy of the eib resource value, eibrsrce. Return codes uercnorm continue processing. Uercbyp the file control exec interface program should ignore this request. Uercpurg task purged...
Page 119
‘eibrcode’. For details of eib return codes, refer to eib fields, in the cics application programming reference manual. Uepresp address of a 4-byte binary copy of the eib response code ‘eibresp’. Note: if the file that has just been accessed is remote, the addressed field contains zeros (even if uep...
Page 120
3. Exit programs that issue exec cics commands, and that use the dfheient macro, should use the dfheiret macro to set a return code and return to cics. See “returning values to cics” on page 10. Example program cics supplies, in cicsts32.Cics.Sdfhsamp, an example program, dfh$xtse, that shows how to...
Page 121
4. Xfcareqc v for the inquire file command, only the xfcareq and xfcareqc exits are invoked: 1. Xfcareq 2. Xfcareqc exit xfcareq when invoked before cics processes a file control spi request. Exit-specific parameters uepclps address of a copy of the spi command parameter list. See “the command-level...
Page 122
Note: take care when using recursive commands. For example, you must avoid entering a loop when issuing a file control spi request from the xfcareq exit. Use of the recursion counter ueprecur is recommended. Exit xfcareqc when invoked after a file control spi request has completed, before return fro...
Page 123
Values into the application program’s exec interface block (eib) after the completion of xfcareqc or if you specify a return code of uercbyp in xfcareq. You must set valid file control responses. You must set all three of eibrcode, eibresp, and eibresp2 to a consistent set of values, such as would b...
Page 124
V fcis_bits4 v fcis_bits5 v fcis_bits6 v fcis_bits7 v fcis_bits8 fcis_group always x'4c', indicating that this is a file control spi request. Fcis_funct one byte that defines the type of request: x'02' inquire file x'04' set file. Fcis_eidopt2 not used by file control. Fcis_eidopt3 not used by file ...
Page 125
X'40' set if the request contains an argument for the add keyword. If set, fcis_addr10 is meaningful. X'20' set if the request contains an argument for the delete keyword. If set, fcis_addr11 is meaningful. X'10' set if the request contains an argument for the disposition keyword. If set, fcis_addr1...
Page 126
X'10' set if the request contains an argument for the exclusive keyword. If set, fcis_addr28 is meaningful. X'08' set if the request contains an argument for the blockkeylen keyword. If set, fcis_addr29 is meaningful. X'04' set if the request contains an argument for the blocksize keyword. If set, f...
Page 127
X'08' set if the request contains the loadtype keyword. X'04' set if the request contains the pool keyword. X'02' set if the request contains the tablename keyword. X'01' set if the request contains the updatemodel keyword. Fcis_bits8 x'80' set if the request contains the remotetable keyword. X'40' ...
Page 128
Fcis_addr15 is the address of a 4-byte area containing the cvda from enablestatus. Fcis_addr16 is the address of a 4-byte area containing the cvda from recovstatus. Fcis_addr17 is the address of a 4-byte area containing the cvda from accessmethod. Fcis_addr18 is the address of a 4-byte area containi...
Page 129
Fcis_addr37 to fcis_addr51 are not used by file control. Fcis_addr52 is the address of a 4-byte area containing the data from journalnum. Fcis_addr53 is the address of a 4-byte area containing the data from loadtype. Fcis_addr54 is the address of a 4-byte area containing the data from cfdtpool. Fcis...
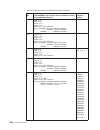
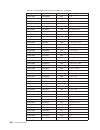
Page 130
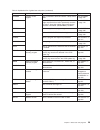
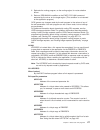
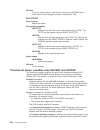
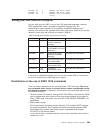
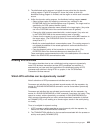
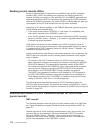
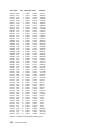
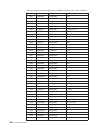
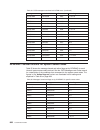
Table 5. Inquire file requests (continued). The relationship between arguments, keywords, data types, and input/output types. Argument keyword data type input/output arg16 recovstatus bin(31) output arg17 accessmethod bin(31) output arg18 type bin(31) output arg19 object bin(31) output arg20 remotes...
Page 131
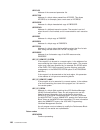
Table 6. Set file requests (continued). The relationship between arguments, keywords, data types, and input/output types. Argument keyword data type input/output arg2 dsname char(44) input arg3 fwdrecstatus bin(31) input arg4 strings bin(31) input arg5 * * * arg6 lsrpoolid bin(31) input arg7 read bi...
Page 132
Note: you must never modify an input field by altering the data that is pointed to by the command-level parameter list. To do so would corrupt storage belonging to the application program and would cause a failure when the program attempted to reuse the field. Modifying output fields: the technique ...
Page 133
Modifying user arguments user exit programs can modify user arguments as follows: v for input arguments, your exit program should obtain sufficient storage to hold the modified argument, set up the required value, and set the associated pointer in the parameter list to the address of the newly acqui...
Page 134
For a close wait command, the exits are invoked as follows. Xfcsreq is invoked, the task requests a closure of the file and waits for the closure to happen. When all activity against the file is complete, the file is closed, and xfcsreq and xfcsreqc are invoked under the task that closed it. Finally...
Page 135
Uepfsofb open for backout. If the first byte indicates a close request (uepfscls), the second byte shows the type of close: uepfsnc normal close uepfscp close pending uepfselm end of load mode close uepfsimm immediate close uepfsicp immediate close pending uepfsqu rls quiesce close. Uepfile address ...
Page 136
Uefjru journal read for update uefjwu journal write update uefjwa journal write add uefjdsn dsname has been journaled uefjsyn journal read synchronously uefjasy journal write asynchronously. Uefdsvjl one byte indicating a further automatic journaling option which applies to vsam files only. The valu...
Page 137
Uefacbcp this field is set to nulls in this exit. Note: only the first seven fields of uepfinfo are set for this exit. Of the remaining fields, urffrclg is set to blanks, and the others are set to nulls. Ueprecur address of a halfword recursion counter. The counter is set to 0 when the exit is first...
Page 138
Exit xfcsreqc when invoked after a file enable, disable, open, close, or cancel close command has completed. Note: the exit is not invoked for function-shipped requests. Exit-specific parameters uepfsreq address of a 2-byte field that indicates the type of file request. The first byte contains one o...
Page 139
Ueflname the 8-character file name. Uedsname the 44-character dsname of the data set associated with the file. Uefserv one byte indicating the servreq settings for this file. The possible values are: uefrdim read valid uefupdim update valid uefaddim add valid uefdelim delete valid uefbrzim browse va...
Page 140
Uefvsam vsam file uefbdam bdam file uefdtbl data table file uefdtum user data table file uefcfdt coupling facility data table uefbcrv one byte indicating the recovery attributes of the data set associated with this file. The possible values are: uefbcfr forward recovery specified uefbclog logging sp...
Page 141
Uepfbcas data set marked unavailable. Uefacbcp address of a read-only copy of the acb for a vsam file, or the dcb for a bdam file. Set only after completion of a successful open. If uefdtbl and uefdtum have been set on, then the storage addressed by uefacbcp is undefined. This pointer should not be ...
Page 142
Uercpurg task purged during xpi call. Xpi calls all can be used. Api and spi calls all except exec cics shutdown and exec cics xctl can be used. Note: 1. Take care when issuing recursive commands not to cause a loop. For example, it is your responsibility to avoid entering a loop when a file control...
Page 143
Associated with the file, as described by fields ueflname and uedsname in the dfhuefds dsect. 3. Issues a write operator command to write as much data as has been created in the 690 bytes of storage to the system console. 4. Returns a normal response of zero in register 15. The sample program contai...
Page 144
Xfcnrec. If the base cluster block is set as unrecoverable and a mismatch has been allowed, access may be allowed to the data set, via an unrecoverable file, before the data set is fully recovered. To provide a means of selecting which mismatches to accept and which to reject, three parameters are p...
Page 145
Exit xfcvsds when invoked invoked after vsam rls has informed cics that processing is required as a result of a data set-related action occurring in the sysplex. Exit-specific parameters uepdsnam address of a 44-byte field containing the name of the data set to which the action applies uepvsact addr...
Page 146
Cics is not to carry out the processing required for the vsam rls action, and is to cancel the action throughout the sysplex. A return code of uercpurg is not allowed. Xpi calls all can be used. Api and spi calls you can use cics api and spi commands at this exit. In general all can be used, with th...
Page 147
Uepqrcde address of a 1-byte field indicating the result of the quiesce or unquiesce. Possible values are: ueqok successful. Ueqrejec rejected—see uepqconf for the reason code. Uequnkno failed because data set not known to dfsms as a vsam data set. Ueqioerr failed because of rls error or smsvsam ser...
Page 148
File control recovery program exits xfcbfail, xfcbout, xfcbover, and xfcldel cics provides four global user exits that you can use in connection with file control recovery operations. These are: xfcbfail invoked when an error occurs during backout. Xfcbout invoked when cics is about to back out a fi...
Page 149
Point; the tbexits parameter allows only one exit program at each exit point. Pltpi processing is described in chapter 4, “writing initialization and shutdown programs,” on page 425. Exit xfcbfail, file control backout failure exit xfcbfail is invoked whenever there is a failure during backout of an...
Page 150
Uepfcrsp address of the file control response byte. This can have one of the following values: ueaixful no space in non-unique alternate index. Uecache rls cache failure or cache connectivity failure. Uenbwbak non-bwo backup in progress. Uedlock deadlock detected. Ueduprec duplicate key on unique al...
Page 151
Uercbyp ignore the error (do not invoke cics backout failure control) and continue. Setting this return code could be damaging to the integrity of your data. A return code of uercpurg is not allowed. There is no need to set a uercpurg return code, because the conditions under which this exit is invo...
Page 152
Record on the data set with the “before-image” held in the log record addressed by uepblogr. Use parameter uepfcrsp to determine which error occurred. Xbfewr an error response has been returned from the file control file-request-handler program while processing a write request. This request is issue...
Page 153
The sample program takes this step to demonstrate the use of the uercbyp return code. It is not recommended that you use uercbyp with important data sets. V examines the file control response code and issues a message to the console describing the procedure to be followed for this error. The sample ...
Page 154
Because the same backout code is executed following an emergency restart as at any other time, xfcbout replaces both xrcinpt and xdbin for file data. The address of an fbo entry is not supplied (there is no fbo table in cics transaction server for z/os, version 3 release 2). However, the file name i...
Page 155
Vsam rls locks individual records within a data set, and these locks are converted to retained locks for those uows that are not completed because of backout or in-doubt failures, thus preserving data integrity. To avoid corruption of a data set by a non-rls batch job, which is not aware of the reta...
Page 156
Uercnorm do not perform the backout of this log record. Any updates performed by the batch run should take precedence. Uercbcko perform the backout. It is known that the actions of the batch job could not have affected this update. A return code of uercpurg is not allowed. There is no need to set a ...
Page 157
– the data set name – the file control portion of the log record. V checks the data set name to see if it is one of those for which it is known that batch programs never update existing records, but only insert new records, or do not make updates at all. The sample program contains a table of such d...
Page 158
Uepflen address of a fullword containing the length of the data in the file control request. Return codes uercfail do not perform the logical delete, and treat this as a backout failure. This is the default action taken if the exit is not enabled. Uercldel perform the logical delete by reapplying th...
Page 159
– an eye-catcher ‘dfh$fcld entry’ – the unmarked file control request data – the file control portion of the log record. V issues an exec cics inquire file command to check the access method and type to confirm that the file is a vsam esds or bdam data set. The logical delete exit should have been i...
Page 160
Good morning message program exit xgmtext when invoked before the good morning message is transmitted. Exit-specific parameters ueptctte address of the terminal control table terminal entry (tctte). The tctte can be mapped using the dsect dfhtctte. Ueptioa address of the terminal input/output area (...
Page 161
If you already have an xiscona exit program, you may be able to modify it for use at the xzique exit point. The purpose of xiscona is to help you prevent the performance problems that can occur when function shipping or dpl requests awaiting free sessions for a connection are queued in the issuing r...
Page 162
V examine the type of request and the resource being accessed (which can be discovered by examining the request parameter list). The program could, for example, reject file read requests but queue file updates. Note: because a failure of the exit program could affect system availability, it is recom...
Page 163
Uepeippl address of the request parameter list. Uepconty a 1-byte field indicating the connection-type. Possible values are: uepmro (x'80') request for an mro connection ueplu6 (x'40') request for an lu6.1 connection uepluc (x'20') request for an lu6.2 connection. Uepnetnm an 8-character field conta...
Page 164
Note that this exit is invoked only if the request to be shipped is of type exec cics start nocheck. For exec cics requests other than those with the nocheck option (which is only available on start commands) the ‘sysiderr’ condition is raised in the application program. You can use the exit to spec...
Page 165
Uercpurg task purged during xpi call. Xpi calls all can be used. Important there is no ‘uercnorm’ return code at this exit point, because the exit is invoked after a failure. The choice is whether to take the system default action or to handle the error in some other way. Interval control program ex...
Page 166
Note: 1. The contents of the fields addressed by uepicqid and uepictid are unpredictable if the associated data items were not specified on the request. You must test the copy of tcaictr to determine whether they contain meaningful values. 2. Your exit program can change the values of the fields add...
Page 167
Exit xictenf when invoked exit xictenf is also invoked from the interval control program. However, this exit relates to the ‘terminal not known’ condition and so is considered in detail in “‘terminal not known’ condition exits xaltenf and xictenf” on page 224. Interval control exec interface program...
Page 168
V for dynamically-routed transactions—only dynamically-routed (non-terminal-related) start requests cause the exit to be invoked. Thus, a dynamically-routed transaction that was initiated by a terminal-related exec cics start command does not cause the exit to be invoked. V if it is disabled. V if a...
Page 169
Exit-specific parameters uepclps address of the command-level parameter structure. See “the uepclps exit-specific parameter” on page 152. Uepictok address of a 4-byte token to be passed to xicereqc. This allows you, for example, to pass a work area to exit xicereqc. Ueprcode address of a 6-byte hexa...
Page 170
Exec cics shutdown exec cics xctl note: take care when issuing recursive commands not to cause a loop. For example, it is your responsibility to avoid entering a loop when an interval control request is issued from the xicereq exit. Use of the recursion counter ueprecur is recommended. Exit xiceres ...
Page 171
Uercnorm continue processing. Uercpurg task purged during xpi call. Uercresu a required resource is unavailable. Setting this value causes cics to reject the routed request, and to return a value of 'f' (resource unavailable) in the dyrerror field of the routing program's communications area. Xpi ca...
Page 172
Uepdate address of a fullword copy of the eib date value, eibdate. Ueptime address of a fullword copy of the eib time value, eibtime. Uep_ic_remote_system if the request is to be sent to a remote region, is the address of an area containing the 4-byte name of the remote region. (the remote region ma...
Page 174
The request. The remaining addresses point to pieces of data associated with the request. For example, the second address points to the interval for start requests. You can examine the eid to determine the type of request and the keywords specified. You can examine the other parameters in the list t...
Page 175
Ic_group x'10' this is an interval control request. X'4a' this is an asktime or formattime command. Ic_funct one byte that defines the type of request. If ic_group = x'10': x'02' asktime x'04' delay x'06' post x'08' start x'0a' retrieve x'0c' cancel if ic_group = x'4a': x'02' asktime x'04' formattim...
Page 176
X'80' set if the request specifies rtermid, or if a formattime request specifies datesep. If set, ic_addr9 is meaningful. X'40' set if the request specifies queue. If set, ic_addra is meaningful. X'20' set if the request specifies hours. If set, ic_addrb is meaningful. X'10' set if the request speci...
Page 177
X'04' year was specified on a formattime command, or minutes was specified. X'02' time was specified on a formattime command, or protect was specified. X'01' timesep was specified on a formattime command, or nocheck was specified. Ic_eidopt7 indicates whether certain functions or keywords were speci...
Page 178
Ic_addr2 is the address of one of the following: v an 8-byte area containing the value of reqid (if the request is delay, post or start). V a halfword containing the value of length (if the request is retrieve). Warning: for requests that specify into, do not change the value of length to a value gr...
Page 179
V a fullword containing the value of daycount. Ic_addrb is the address of one of the following: v an area containing the value of hours. V a fullword containing the value of dayofweek. Ic_addrc is the address of one of the following: v an area containing the value of minutes. V a fullword containing...
Page 180
The following are always input fields: v interval v time v reqid v from v termid v sysid v hours v minutes v seconds v userid v channel the following are always output fields: v date v dateform v daycount v dayofmonth v dayofweek v ddmmyy v ddmmyyyy v fulldate v into v mmddyy v mmddyyyy v monthofyea...
Page 181
Abstime is an input field on a formattime request, and an output field on an asktime request. Datesep and timesep can be input fields on a formattime request. Modifying input fields: the correct method of modifying an input field is to create a new copy of it, and to change the address in the comman...
Page 182
X'40' the existence bit for queue x'20' the existence bit for hours x'10' the existence bit for minutes x'08' the existence bit for seconds. Ic_eidopt6 x'20' the secondary existence bit for hours x'10' the existence bit for fmh x'08' the secondary existence bit for seconds x'04' the secondary existe...
Page 183
Ic_eidopt8 x'20' unused by cics. The eid is reset to its original value before return to the application program. That is, changes made to the eid are retained for the duration of the interval control request only. Note: your user exit program is prevented from making major changes to the eid. Howev...
Page 184
1. Scan the global work area (gwa) to locate a suitable cics region (for example, the region currently processing the least number of start requests). 2. Having decided which system to route the request to, increment the use count for this system. 3. Obtain a 4-byte area in which to store the sysid ...
Page 185
These are both information-only exits. Any changes made to the exit parameters by the exit program are ignored by cics, as is any return code which it sets. Exit xldload when invoked after an instance of a program is brought into storage, and before the program is made available for use. Exit-specif...
Page 186
Uepprogl address of a 4-byte field containing the length, in bytes, of the program that is being freed. Uepldpt address of a 4-byte field containing the address at which the program resides in storage. Uepentry address of a 4-byte field containing the address of the program’s entry point. Ueptranid ...
Page 187
If you do not provide a journalmodel resource definition for dfhlog and dfhshunt, or if you use the cics definitions supplied in group dfhlgmod, the model log stream names default to &sysname.Dfhlog.Model and &sysname.Dfhshunt.Model. For example, if a cics region issues a request to create a log str...
Page 188
For information about the ixginvnt service, see the os/390 mvs authorized assembler services manual. An xlgstrm global user exit program can set explicit attributes for the log stream definition, and can also set a return code that causes the log stream definition to be bypassed. Note: if you want x...
Page 189
Uepsyslg the log stream is for a cics system log. Uepgenlg the log stream is for a general log (a forward recovery log, a user journal, or auto-journal). Return codes uercnorm cics continues and attempts to define the log stream. Uercbyp cics does not attempt to define the log stream. The process th...
Page 190
Note: to run the sample program “as is”, you must first create a model log stream called 'cicsad01.Dept0001.Model100'. However, you will probably want to tailor the sample to suit your own environment. The code contains comments to help you do this. Related concepts: “the log manager domain sample e...
Page 191
Important because of the danger of recursion, your xmeout exit program should not try to reroute: v any dfhtdxxxx messages, produced by the transient data program. V user domain messages in the range dfhus0002 - dfhus0006, plus message dfhus0150. V transaction manager messages dfhxm0212, dfhxm0213, ...
Page 192
Uepterm address of the 4-byte id of the terminal under which the current transaction is running. If the current transaction is not associated with a terminal, the addressed field contains hexadecimal zeroes. Uepprog address of the 8-byte application program name, or nulls if there is no current appl...
Page 193
Dfhfc0531 date time applid automatic journal journal journalname, opened for file filename is not of type mvs. Module module. The xmeout inserts are date, time, applid, journal, journalname, filename, and module. The fourth insert (journal) is the number specified for journal on the file definition....
Page 194
Dfh$sxp5 reroute a tdq message to another tdq dfh$sxp6 reroute a tdq message to a console. Related concepts: “the message domain sample exit programs” on page 23 monitoring domain exit xmnout xmnout is invoked at the following event points: v before an exception class monitoring record is passed to ...
Page 195
Uepdict address of the dictionary. The sequence of dictionary entries is mapped by the dsect generated from the macro dfhmctdr. This field only has meaning for performance class records. If the monitoring record type is exception class (type 4) or transaction resource (type 5), this field is set to ...
Page 196
Uercnorm continue processing. Uercbyp suppress monitor record output. Uercpurg task purged during xpi call. Xpi calls wait_mvs can be used. Do not use any other calls. Pipeline domain exits use the pipeline domain exits to customize the processing that occurs for inbound and outbound web services in...
Page 197
Uepapabn (x'40') the web service provider application completed its processing successfully. Uepapsf a 1-byte field indicating if the web service provider application set a soap fault. Valid values are as follows: uepapsfy (x'80') the web service provider application is returning a soap fault. Uepap...
Page 198
Note: 1. The attributes of the local program definition are not passed to the exit program. If the exit program needs to know, for example, the value of the remotesystem attribute, it can issue an exec cics inquire program command. 2. If you use xpcreq to change the target sysid, remember that: a. I...
Page 199
2. Reinvoke the routing program, on the routing region, for route selection failure. 3. Return a resunavail condition on the exec cics link command executed by the mirror on the target region. (this condition is not returned to the application program.) cics ignores any changes made by the exit prog...
Page 200
Ueprsrce address of an 8-character copy of the eib resource value, eibrsrce. Uep_pc_pbtok address of a 4-byte field containing the z/os workload manager (wlm) performance block token. An exit program can use this token to access information (such as the service class token, servcls) in the wlm perfo...
Page 201
Ueprecur address of a halfword recursion counter. Because the xpceres exit can never be called recursively in the same transaction, the value of this field is always 0. Uepresp address of a 4-byte copy of eibresp. Uepresp2 address of a 4-byte copy of eibresp2. Ueptstok address of a 4-byte token that...
Page 202
Uepclps address of the command parameter list. Ueppctok address of a 4-byte token passed from xpcreq. This allows xpcreq to, for example, pass a work area to xpcreqc. Ueprcode address of a 6-byte hexadecimal copy of eibrcode. Ueprecur address of a halfword recursion counter. The counter is set to 0 ...
Page 203
Uercpurg task purged during xpi call. Xpi calls all can be used. Although the exit permits the use of xpi getmain and freemain calls, we recommend that you use the exec cics getmain and freemain commands instead. Api and spi calls all can be used, except for: exec cics shutdown exec cics xctl note: ...
Page 204
Pc_addra. It is defined in the dsect pc_addr_list, which you should copy into your exit program by including the statement copy dfhpceds. The command-level parameter list is made up as follows: pc_addr0 is the address of a 7-byte area called the exec interface descriptor (eid), which is made up as f...
Page 205
Pc_exist7 (x'02 ') set if the request specifies the sysid parameter. If set, pc_addr7 is meaningful. Pc_exist8 (x'01 ') set if the request specifies the transid parameter. If set, pc_addr8 is meaningful. Pc_bits2 one byte containing one of the following values: pc_exist9 (x'80') not used. Pc_exista ...
Page 206
Pc_addra is the address of the 16-byte channel name, as specified on the channel parameter. Modifying fields in the command parameter structure: some fields that are passed to program control are used as input to the request, some are used as output fields, and some are used for both input and outpu...
Page 207
Bits in the eid should be modified in place. You should not modify the pointer to the eid. (any attempt to do so is ignored by cics.) the eid is reset to its original value before return to the application program. That is, changes made to the eid are retained for the duration of the program control...
Page 208
1. Scan the global work area (gwa) to locate a suitable cics region - for example, the region currently processing the least number of link requests. 2. Having decided which system to route the request to, increment the use count for this system. 3. Obtain a 4-byte area in which to store the sysid f...
Page 209
Terminal-related information, and that can be mapped using the dsect dfhpcue. When xpcftch is invoked, the following dfhpcue fields are significant: pcue_control_bits v 1-byte flag field. A setting of pcuecbte indicates that the transaction is linked to a terminal. V a setting of pcuenotx (x'40') in...
Page 210
Address. Set the top bit to specify that the alternative program is to run amode (31). Pcue_real_entry from z/os 1.7 onwards, this field provides the real entry point for language environment conforming programs. Previously only pcue_entry_point was available to you, but for language environment con...
Page 211
Bassm 15,0 using *,15 when invoked before a handle abend routine is given control. Exit-specific parameters ueppcds address of a storage area that contains program- and terminal-related information, and that can be mapped using the dsect dfhpcue. When xpchair is invoked, the following dfhpcue fields...
Page 212
Xpi calls all can be used. Exit xpcta xpcta is invoked immediately after a transaction abend, and before any processing that might modify the existing environment so that the task could not be resumed. You can use it to: v set a resume address, instead of letting cics process the abend v specify the...
Page 213
Pcue_logical_level fullword containing the number of chained dfhrsads blocks (that is, logical level). Pcue_branch_address fullword. You can use this field to supply a resume address. Set the top bit to specify that the resumed task is to run amode (31). Pcue_branch_execkey if storage protection is ...
Page 214
Dfh$pcta can be extended for transaction isolation. Related concepts: “the transaction-abend sample exit program” on page 24 exit xpcabnd xpcabnd is invoked after a transaction abend and before a transaction dump call: you can use it to suppress the dump. When invoked after a transaction abend and b...
Page 215
Uercbyp suppress the dump call. Uercpurg task purged during xpi call. Xpi calls all can be used. Resource manager interface program exits xrmiin and xrmiout exit xrmiin when invoked before a task-related user exit program is invoked due to an application program issuing an rmi api request. Exit-spec...
Page 216
Uercnorm continue processing. Uercpurg task purged during xpi call. Xpi calls all can be used. Api and spi commands all except exec cics shutdown and exec cics xctl can be used. However, calldli, exec dli, or exec sql commands must not be used. Exit xrmiout when invoked after a task-related user exi...
Page 217
Return codes uercnorm continue processing. Uercpurg task purged during xpi call. Xpi calls all can be used. Api and spi commands all except exec cics shutdown and exec cics xctl can be used. However, calldli, exec dli, or exec sql commands must not be used. Note: it is not recommended that your exit...
Page 218
Connection is a concatenation of a fepi node name and a fepi target name, each of which is 8 characters long (fixed length) with no separator. The exit is driven once for each individual resource in a group list installed during a cics initial or cold start. If you are concerned about the performanc...
Page 219
Ueiddb2e a db2 entry (db2entry) ueiddb2t a db2 transaction (db2tran) ueiddjar a deployed jar file (djar) ueiddoct a doctemplate ueidfeco a fepi connection ueidfeno a fepi node ueidfepo a fepi pool ueidfeps a fepi propertyset ueidfeta a fepi target ueidfile a file ueidipco an ipic connection ( “ipcon...
Page 220
Ueidpset a partitionset ueidrqmd a request model (iiop) ueidsess a session ueidstrm an mvs log stream ueidtcls a transaction class ueidtcps a tcp/ip service ueidtdqu a transient data queue ueidterm a terminal ueidtran a transaction ueidtsmd a temporary storage queue model. Ueidurim a uri map (urimap...
Page 221
Uercpurg task purged during xpi call. Xpi calls you can use all xpi calls. Important abends in a program enabled at the xrsindi exit point may cause cics to terminate, because for some resources the exit is driven during syncpoint. If the exit returns code uercpurg during syncpoint for these resourc...
Page 222
Ueptrmid address of the terminal id. Ueptctua address of the tct user area. Ueptctul address of the tct user area length. Ueptrmty address of the terminal-type byte. Uepsnflg address of a 2-byte field containing flags: table 8. Flags set in the uepsnflg field of xsnon flag equivalent meaning uepsnok...
Page 223
Ueptrmty address of the terminal-type byte. Uepsnflg address of a 2-byte field containing flags: uepsnok sign-off was successful uepsnfl sign-off failed uepsnnml normal sign-off uepsntim timeout sign-off. Return codes uercnorm continue processing. Uercpurg task purged during xpi call. Xpi calls all ...
Page 224
To use this program, add an entry to the first section of your pltpi table (that is, before the dfhdelim statement). For example: dfhplt type=initial,suffix=sn dfhplt type=entry,program=dfh$snpi dfhplt type=entry,program=dfhdelim dfhplt type=final end statistics domain exit xstout on invocation, xst...
Page 225
Uepstype address of the 3-byte character field statistics type. The values of the types are: int interval statistics eod end-of-day statistics req requested statistics rrt requested reset statistics uss unsolicited statistics. Uepsdate address of a 6-byte character field containing the collection da...
Page 226
Srp_error_type the 4-character error type—always ‘asrb’. Srp_sys_abcode 2 bytes containing the system abend code xxx in binary format (for example, d37). Srp_user_abcode 2 bytes containing the user abend code nnnn in binary format (for example, 0999). Srp_error_tranid 4-character field containing th...
Page 227
Srp_cics_error_reason 4-character field containing the mvs abend reason code. It contains a value only if flag srp_valid_reason is set. Srp_cics_error_data an area describing the last thing that cics did, prior to the abend. It contains the following: srp_cics_ec_psw 8-character field containing the...
Page 228
2. The format of srp_error_data is shown in the cics data areas manual. Return codes uercnoca abnormally terminate the task with abend code ‘asrb’. Do not cancel any program-level abend exits that are associated with this task. Uerccanc abnormally terminate the task with abend code ‘asrb’. Cancel an...
Page 229
Xpi calls all other xpi calls except write_journal_data can be used. However, their use is not recommended, because they could cause the task to lose control, thus allowing another task to write more monitoring data. Temporary storage domain exits xtsqrin, xtsqrout, xtsptin, and xtsptout the tempora...
Page 230
Uep_ts_queue_name address of a 16-byte field containing the queue name. Uep_ts_data_p address of a fullword containing the address of the data. (write and rewrite requests). Uep_ts_data_l address of a fullword containing the length of the data. (write and rewrite requests). Uep_ts_item_number addres...
Page 231
Uepterm address of the 4-byte terminal id. Uepprog address of the 8-byte application program name. Uep_ts_function address of a byte containing the function: v uep_ts_fun_write v uep_ts_fun_rewrite v uep_ts_fun_read_into v uep_ts_fun_read_set v uep_ts_fun_read_next_into v uep_ts_fun_read_next_set v ...
Page 232
Exit xtsptin when invoked before execution of a temporary storage interface request for a cics internal queue (for example, for interval control or bms queues). Exit-specific parameters ueptranid address of the 4-byte transaction id. Uepuser address of the 8-byte user id. Uepterm address of the 4-by...
Page 233
Return codes uercnorm normal. Uercpurg task purged during xpi call. Xpi calls all can be used. Api and spi calls none can be used. Exit xtsptout when invoked after execution of a temporary storage interface request for a cics internal queue (for example, for interval control or bms queues). After ex...
Page 234
V uep_ts_response_exception v uep_ts_response_disaster v uep_ts_response_invalid return codes uercnorm normal response. Uercpurg a purged response was received from an xpi request. Xpi calls all can be used. Api and spi calls none can be used. Temporary storage exec interface program exits xtsereq a...
Page 235
Exit xtsereq when invoked before cics processes a temporary storage api request. Exit-specific parameters uepclps address of a copy of the command parameter list. See “the command-level parameter structure” on page 215. Ueptqtok address of a 4-byte area which can be used to pass information between ...
Page 236
Note: take care when issuing recursive commands. For example, you must avoid entering a loop when issuing a temporary storage request from the xtsereq exit. Use of the recursion counter ueprecur is recommended. Exit xtsereqc when invoked after a temporary storage api request has completed, before re...
Page 237
Uercpurg task purged during xpi call. Xpi calls all can be used. Api and spi commands all can be used, except for: exec cics shutdown exec cics xctl you can update the copies of eibrsrce, eibrcode, eibresp, and eibresp2 that you are given in the parameter list. If you update the values, temporary st...
Page 238
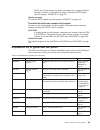
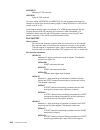
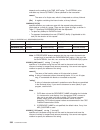
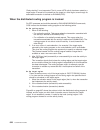
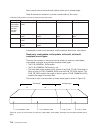
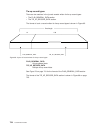
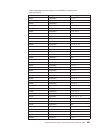
The command-level parameter list is made up as follows. Note: the relationship between arguments, keywords, data types, and input/output types is summarized for the temporary storage commands in the following tables: table 9. The relationship between arguments, keywords, data types, and input/output...
Page 239
X'02' set if the request contains an argument for the sysid keyword. If set, ts_addr7 is meaningful. Ts_bits2 two bytes not used by temporary storage. Ts_eidopt5 indicates whether certain keywords were specified on the request. X'80' qname was specified (otherwise queue). You can modify this bit in ...
Page 240
Ts_addr7 is the address of an area containing the value of sysid. Modifying fields in the command-level parameter structure: some fields that are passed to temporary storage are used as input to the request, some are used as output fields, and some are used for both input and output. The method your...
Page 241
However, you can make minor changes to requests, such as to turn on the existence bit for sysid so that the request can be changed into one that is shipped to a remote system. The list that follows shows the bits in the eid that can be modified. Any attempt to modify any other part of the eid is ign...
Page 242
Table 11. Readq ts: user arguments and associated keywords, data types, and input/output types argument keyword data type input/output type arg1 queue char(8) input arg1 qname char(16) input arg2 set data-area, ptr output arg2 into data-area output arg3 length bin(15) input/output arg4 numitems bin(...
Page 243
1. Obtain storage for the argument to be added 2. Initialize the storage to the required value 3. Select and set up the appropriate pointer from the parameter list 4. Select and set up the appropriate argument existence bit in the eid 5. Modify the parameter list to reflect the new end of list indic...
Page 244
Uepallen address of a fullword binary field containing the length of the from data; or hexadecimal zeros, in either of the following cases: v the aid was created by a start request without a from option. V the aid is associated with a channel (in which case the field pointed to by uepalchn will be s...
Page 245
Note: the xaltenf exit, used to handle the “terminal not known” condition, is also invoked from the terminal allocation program. Xaltenf is described on page “‘terminal not known’ condition exits xaltenf and xictenf” on page 224. Terminal control program exits xtcin, xtcout, and xtcatt exit xtcin wh...
Page 246
Xpi calls all can be used. However, note that you cannot use a getmain call to obtain terminal-class storage for use as a replacement tioa. Exit xtcatt when invoked before task attach. Exit-specific parameters ueptctte address of the terminal control table terminal entry (tctte). The tctte can be ma...
Page 247
In the local system. If the requested terminal is remote, the terminal allocation program ships an ati request to the remote system, which initiates transaction routing back to the local system. For guidance information about ati, refer to the cics intercommunication guide. ‘terminal not known’ cond...
Page 248
Uercnetn netname of tor returned uercsysi sysid of tor returned. For return codes uercnetn and uercsysi, the exit program must place the netname or sysid of the terminal-owning region in fields uepxxnto or uepxxsyo (where xx is al or ic). If the terminal-owning region is a member of a vtam generic r...
Page 249
Uepaltrn address of 4 bytes containing the name of the transaction to be run. Uepalrtr address of 4 bytes containing the name of the terminal on which the transaction should run. (if a transient data trigger level was reached and the transient data queue definition specified a system, then this woul...
Page 250
Run. It is important that your exit program supply a terminal netname if the tor to which it directs the ati request is a member of a vtam generic resource. Return codes uercteun terminal unknown, reject request. Uercnetn terminal known, netname returned in uepalnto. Uercsysi terminal known, sysid r...
Page 251
Uepicfn a start command was not being processed or a start was being processed but it was not function shipped. Uepictrn address of 4 bytes containing the name of the transaction to be run. Uepicrtr address of 4 bytes containing the name of the terminal on which the transaction should run. Uepicctr ...
Page 252
Run. It is important that your exit program supply a terminal netname if the tor to which it directs the ati request is a member of a vtam generic resource. Return codes uercteun terminal unknown, reject request. Uercnetn terminal known, netname returned in uepicnto. Uercsysi terminal known, sysid r...
Page 253
Dfhxtenf csect dfhvm xtenf entry dfhxtena dfhxtena ds 0h stm r14,r12,12(r13) save registers balr r11,0 set up base register using *,r11 * using dfhuepar,r1 dfhueh parameter list * * could check the terminal id at this point. In this * program we assume it is valid. We also choose to accept * start r...
Page 254
Important the example in figure 2 on page 231 is intended purely as a demonstration of some of the possibilities available, and would be impractical in a production environment. Related concepts: “the terminal-not-known sample exit program” on page 25 transaction manager domain exit xxmatt exit xxma...
Page 255
Transaction specified on dtrtran is attached and cics considers that the transaction has been found. Equated values are: ueatfnd the transaction was found. Ueatnfnd the transaction was not found. Uepattst the address of a 1 byte transaction definition state. Equated values for the definition state a...
Page 256
When the task being attached is for a task started by an immediate start command; that is, a start without an interval, the current task is the task that issues the start command, and the fields contain values associated with that task. Transient data program exits xtdreq, xtdin, and xtdout exit xtd...
Page 257
Ueptdlud address of the fullword length of the unmodified td data. Ueptdamd address of the td data modified by the exit program. Ueptdlmd address of the fullword length of the td data modified by the exit program. Return codes uercnorm continue td processing. Uercpurg task purged during xpi call. Xp...
Page 258
Note: if you return uerctdok to suppress the first line of a multiline message, the rest of the message is not presented to xtdout, but is also suppressed. Uercpurg task purged during xpi call. Xpi calls you can use: v inq_application_data v inquire_system v wait_mvs do not use any other calls. Tran...
Page 259
Exit xtdereq when invoked before cics processes a transient data api request. Exit-specific parameters uepclps address of the command-level parameter structure. See “the uepclps exit-specific parameter” on page 240. Ueptdtok address of the 4-byte token to be passed to xtdereqc. This allows you, for ...
Page 260
Note: take care when issuing recursive commands. For example, you must avoid entering a loop when issuing a transient data request from the xtdereq exit. Use of the recursion counter ueprecur is recommended. Exit xtdereqc when invoked after a transient data api request has completed, and before retu...
Page 261
Uercnorm continue processing. Uercpurg task purged during xpi call. Xpi calls all can be used. Although the exit permits the use of xpi getmain and freemain calls, we recommend that you use the exec cics getmain and freemain commands instead. Api and spi commands all can be used, except for: exec ci...
Page 262
You can examine the eid to determine the type of request and the keywords specified. You can examine the other parameters in the list to determine the values of the keywords. You can also modify values of keywords specified on the request. (for example, you could change the sysid specified in the re...
Page 263
X'04' readq x'06' deleteq. Td_bits1 existence bits that define which arguments were specified. To obtain the argument associated with a keyword, you need to use the appropriate address from the command-level parameter structure. Before using this address, you must check the associated existence bit....
Page 264
Td_addr4 is the address of a value intended for cics internal use only. It must not be used. Td_addr5 is the address of a value intended for cics internal use only. It must not be used. Td_addr6 is the address of a value intended for cics internal use only. It must not be used. Td_addr7 is the addre...
Page 265
Modifying fields used for both input and output: an example of a field that is used for both input and output is length on a readq request that specifies into. You can treat such fields in the same way as output fields, and they are considered to be the same. Modifying the eid: it is not possible to...
Page 266
You can update the copies of eibrsrce, eibrcode, eibresp, and eibresp2 that you are given in the parameter list. Transient data copies your values into the real eib after the completion of xtdereqc; or if you specify a return code of ‘ bypass’ in xtdereq. You must set valid transient data responses....
Page 267
When using xrcinit and xrcinpt, you should bear in mind that the exits may be invoked before recovery of temporary storage and transient data resources is complete. For further guidance information about exits for unit of work backout, refer to the cics recovery and restart guide. Coding the exit pr...
Page 268
Name6 are the names of your user exit programs for xrcinit, xrcinpt, xfcbfail, xfcldel, xfcbover, and xfcbout. V enable the exits during the first stage of initialization using a pltpi program. If you use the tbexits parameter to enable the exits, a global work area of 4 bytes is provided. If you us...
Page 269
Uepuowbo uow backed out uepuowif uow was in-flight uepuowid uow was in-doubt. Ueplgrec address of the log record just read. The journal control record can be mapped using the information supplied in chapter 27, “cics logging and journaling,” on page 709. Ueplglen address of a fullword containing the...
Page 270
Ueptpnl address of a 1-byte field containing the length of the tpn or dpn. Ueptran address of the 4-byte transaction id. Note: the exit program must not change the transid of tasks started by automatic transaction initiation (ati). (this is because cics needs to match the transid in its program cont...
Page 271
Ueptctte address of the terminal control table terminal entry (tctte). The tctte can be mapped using the dsect dfhtctte. Ueptioa address of the terminal input/output area (tioa). Your exit program should not change the address. The tioa can be mapped using the dsect dfhtioa. However, fields tioasal ...
Page 272
V the equivalent global user exit to control the number of queued requests for sessions on ip interconnectivity (ipic) connections is xisque: see “xisque exit for managing ipic intersystem queues” on page 258. V there are several methods that you can use to control the length of intersystem queues. ...
Page 273
Using the information passed in the parameter list, your global user exit program can decide (based on queue length, for example) whether cics is to queue the allocate request. Your program communicates its decision to cics by means of one of the return codes cics provides. These are: uercaque this ...
Page 274
V for specific modegroup allocate requests, use return code uercaklm. Uercaklm also returns sysiderr to all application programs waiting on the purged allocate requests. Cics sets the uepflag parameter to ueprc12 on subsequent calls to your xzique exit program to indicate that uercaklm was returned ...
Page 275
Each time an xzique global user exit program returns with a request to purge a queue, cics increments a new field in either the system entry or mode entry connection statistics. These fields are: a14eqpct the count of the number of times the queue has been purged for the connection as a whole. A20eq...
Page 276
Ueppad a 1-byte padding field. Uepfspl address of the 10-byte function shipping parameter list. Uepconst address of the 158-byte system entry statistics record (this can be mapped using dsect dfha14ds). Uepmodst address of the 84-byte modegroup statistics record for the modegroup specified in the re...
Page 277
Uepsacnt a half-word binary field containing the number of all non-specific allocates processed since the queue was started (see uepsaqts for the start time). Uepsarc8 a half-word binary field containing the number of sessions freed since the queue was last purged as a result of a uepcakll return co...
Page 278
Uercnorm resume normal operation of the link or modegroup. Uercapur reject the allocate request with sysiderr. Xpi calls all can be used. Designing an xzique global user exit program the functions of your xzique exit should be designed: 1. To control of the number of tasks (and the amount of associa...
Page 279
To control the existence and length of the queue of allocate requests. If you enable the exit, the parameters from the connection definition are passed to your xzique global user exit program, which can change the way in which these parameters are used. The exit program also demonstrates how to cont...
Page 280
Extensions to the sample program: the sample exit program does not attempt to control the queue length, or detect poor response for a particular modegroup differently from the whole connection. This kind of enhancement is something you might want to add to your own exit program if your applications ...
Page 281
Exit-specific parameters uepisdata address of the 78-byte area containing the information listed below. This area is mapped by the dsect in copybook dfhxiqds. Area addressed by uepisdata: uepreq a 2-byte origin-of-request code, which can have the following value: fs function shipping (includes distr...
Page 282
Uercaque queue the allocate request. Uercapur reject the allocate request with sysiderr. Uercakll reject this allocate request with sysiderr. Purge all other queued allocate requests and send an information message to the operator console. Cics also returns sysiderr to all application programs waiti...
Page 283
Number of allocates processed since the queue began, to determine the rate at which cics is processing requests. The relevant fields are: uepsaqts and uepsacnt. To determine whether cics is allocating requests for sessions on this ipconn at an acceptable rate, you can compare the calculated time wit...
Page 284
Isr_xisque_alloc_rejects each time an xisque global user exit program returns with a request to reject a request, cics increments this field, which is provided to help you tune the queue limit. Normally, if the number of sessions and the queue limit specified on the ipconn definition are correctly b...
Page 285
The exit, the parameters from the ipconn definition are passed to the xisque exit program, which can change the way in which these parameters are used. Overview of the sample exit program the program uses the exit-specific parameters passed by cics to determine the state of the ipconn, and to reques...
Page 286
V a predatory takeover. A “predatory takeover” can occur, if you are using vtam release 3.4.0 or above, and a vtam application with the same applid as that of the executing cics system assumes control of all the sessions of the executing cics system. Xxrstat gives you the choice of allowing the syst...
Page 287
V for xrf, in the event of a vtam failure: cics continues processing as if the exit program had not been invoked. V for vtam persistent sessions, in the event of a predatory takeover: cics abends without a dump. Uerccoig ignore. Uercabno abend cics without a dump. Uercabdu abend cics with a dump. Ue...
Page 288
266 customization guide.
Page 289
Chapter 2. Task-related user exit programs this chapter describes a special kind of user exit called a task-related user exit (true). The chapter is divided into the following sections: 1. “introduction to the task-related user exit mechanism (the adapter)” 2. “the stub program” on page 269 3. “writ...
Page 290
The task-related user exit program is provided with a parameter list (dfhuepar) by the cics management module that handles task-related user exits. This parameter list gives the task-related user exit access to information such as the addresses and sizes of its own work areas. The task-related user ...
Page 291
The administration routines may also contain commands to retrieve information about one of the exit program’s work areas (the exec cics extract exit command), and to resolve any inconsistency between cics and a non-cics resource manager after a system failure (the exec cics resync command). For prog...
Page 292
The application can use a parameter to determine whether the resource manager was called. For example, if the application sets a parameter to zero and the resource manager sets it to nonzero, the parameter value on return indicates whether the resource manager was invoked. Note: the only operands of...
Page 293
Writing a task-related user exit program the main function of the task-related user exit program is to translate the calling program’s parameters into a form acceptable to your non-cics resource manager, and then to pass control to the resource manager. You therefore need to be familiar with your re...
Page 294
Threadsafe restrictions an open api true must not treat the executing open tcb environment in such a way that it causes problems for: v other open api trues called by the same task v openapi programs called by the same task v application program logic that could run on the open tcb v future tasks th...
Page 295
Application program call (api)—uertappl for this call, cics always invokes the true on an l8 mode tcb cics syncpoint manager call—uertsync for this call, cics always invokes the true on an l8 mode tcb cics task manager call—uerttask for this call, the tcb on which cics invokes the true is further de...
Page 296
V the address of the kernel stack entry v the address of the appc unit of work (uow) identifier v the address of the user security block flag v the address of the user security block v the address of the resource manager qualifier name v the address of the resource manager’s “single-update” and “rea...
Page 297
Area, with the contents of registers 14 through 12 stored in the fourth and subsequent words. Its fifth word, representing the calling program's register 15, is cleared by cics before the task-related user exit program is invoked, so that it can be used to convey response codes from the resource man...
Page 298
Ueprmqua address of an 8-byte field into which the task-related user exit can move the qualifier name of the resource manager on each api request. This is useful where the same exit program is used to connect to more than one instance of a resource manager; the qualifier identifies the instance of t...
Page 299
Exit is called on the qr tcb with the ueptutcb bit set. For all other calls, cics abends the transaction without invoking the task-related user exit. The second and third bytes contain a value indicating the tcb mode of its caller. This is represented in dfhuepar as both a two-character code and a s...
Page 300
An exit program must make no assumptions about the contents of the performance block and must not attempt to modify it: if it does so, the results are unpredictable. Ueptrce address of a 1-byte trace flag indicating whether rmi tracing (the ri trace component) is active. Ueptrlv1 (x'80') rmi level 1...
Page 301
Caller parameter lists in addition to the dsects dfhuepar and dfhuertr, the inclusion of dfhuexit type=rm in the task-related user exit program provides some field definitions that are specific to the caller of the task-related user exit. The calling program’s parameter list is normally addressed by...
Page 302
Messages for resource recovery. They are presented explicitly because, after a system failure, the task driving the exit is not the task that originally scheduled the recoverable work. These additional parameters describe the original task’s environment and are accessed directly. The full parameter ...
Page 303
Task. But note that, on many invocations of the exit program, parameters 2 through 9 do not contain values. See note 1. Parameter 3 address of a 4-character field identifying the transaction that started the original task. See note 1. Parameter 4 address of a 4-character field identifying the termin...
Page 304
1. Parameters 2 through 8 contain values only if the cics syncpoint manager call is prompted by the issue of an exec cics resync command after a session or system failure, and operation byte 1 contains the bit settings uertcomm or uertback. Otherwise, they are set to x'00' (hexadecimal zero). For pr...
Page 305
Uertcaby (x'20') cics abend, retry possible, tcbs dispatchable uertcabn (x'10') cics abend, retry not possible, tcbs dispatchable uertopca (x'01') cics abend, retry not possible, tcbs not dispatchable. For further information about shutdown trues, see “coding a program to be invoked at cics terminat...
Page 306
Uepedfra (x'20') about to display command to edf. Uepedfrc (x'10') command has been displayed to edf. Uepedfsc (x'08') edf user has changed the screen. Uepedfws (x'04') edf user has changed working storage. Uepedfno (x'01') edf user has requested noop. Uepedffo the output flag byte. If the task-rela...
Page 307
Note: 1. Cics provides a list of named standard attribute bytes that you may want to use. These standard attribute bytes are contained within dfhbmsca, which must be copied into your program. For programming information, including a list of the attribute bytes and their meanings, refer to bms-relate...
Page 308
Cics spi application syncpoint task manager termination manager call context management call cics edf call call program call manager call call dfhuepar dfhuepar dfhuepar dfhuepar uepexn uepexn uepexn uepexn uepgaa uepgaa uepgaa uepgaa uepgal uepgal uepgal uepgal uephmsa uephmsa uephmsa uephmsa uepta...
Page 309
The schedule flag word the schedule flag word is a fullword indicator that the task-related user exit program uses to control its own invocation. It is also used by cics to schedule the first invocation of a task-related user exit program. The schedule flag word is accessed by the address parameter ...
Page 310
Flag word. When the calling application program subsequently issues a syncpoint command, or when end-of-task is reached, the cics syncpoint manager calls the exit program. Note: cics sets the syncpoint manager bit off after every call to the syncpoint manager. This is to avoid the cics syncpoint man...
Page 311
The calling program’s registers the calling program’s registers are stored at the address specified by uephmsa of dfhuepar. Where the calling program is a cics management program, for example the syncpoint manager, the only caller registers that have significance are registers 1 and 15. Register 1 a...
Page 312
Dfhrmcal, the task-related user exit is invoked in amode 24. For this reason, task-related user exits which have been enabled without the linkeditmode option must reside below the 16mb line. Exit programs and the cics storage protection facility when you are running cics with the storage protection ...
Page 313
V before passing control to a task-related user exit program, cics inhibits: – the ability to purge tasks – the monitoring of runaway tasks v while control is in a task-related user exit program: – purge requests are deferred until control is returned from the task-related user exit program. – monit...
Page 314
V on each invocation of a task-related user exit program, a new exec environment is created, even when the program is being invoked from the same task. This means that cics operations, such as browse of a resource definition table, cannot be continued from one invocation of the exit program to the n...
Page 315
The local work area a local work area is associated with a single task and lasts only for the duration of the task. It is for the use of a single task-related user exit program. It can be thought of as a logical extension to the transaction work area (twa, twacoba) that is exclusively for the exit p...
Page 316
Piece of recoverable work to ensure that the cics syncpoint manager calls the exit program during syncpoint processing. (the identification of the current unit of recovery—or unit of work—is addressed by the 8-byte field uepurid. This is available on all invocations of your exit program in which rec...
Page 317
Manager’s parameter list and the true return codes. (the cics syncpoint manager parameters are described in “cics syncpoint manager parameters” on page 279.) table 15. Valid return codes for a true invoked by the cics syncpoint manager request-type return codes meaning uertprep uerfprep phase 1 of 2...
Page 318
As described in “increasing efficiency – single-update and read-only protocols” on page 294, if the uertonly bit is set (indicating that the resource manager is the only one to have updated resources) the exit program should cause the resource manager to perform a single-phase commit. If the commit ...
Page 319
On receiving a request to perform the first phase of a two-phase commit, the resource manager is expected to get into a state where recoverable changes made since the last syncpoint can be either committed or backed out on demand, even if there is an intervening system failure. For example, buffer c...
Page 320
Limitations if your exit program is invoked at end-of-task, you must be alert to possible limitations on exit program activity at task-detach. For example: v do not update any cics resources at all during a task-detach exit call, because the cics syncpoint manager is not invoked again for that task....
Page 321
Cics abend, retry possible, tcbs dispatchable (uertcaby) mvs has flagged the failure as being “eligible for retry”. Your exit program must follow the mvs rules for this type of failure, documented in the os/390 mvs authorized assembler services guide. Subtasks in the region (that is, task control bl...
Page 322
Jtrue1a csect termination true entrypoint stm 14,12,12(13) save registers using jtrue1a,r3 lr r3,r15 use r3 as base register using dfhuepar,r1 address dfhuepar parameter list l r2,uepexn using dfhuertr,r2 cli uertfid,uertcter cics termination call? Bne cont no, so continue l r10,uephmsa address host...
Page 323
Using edf with your task-related user exit program if your exit program sets the edf bit in the schedule flag word and edf is active, the exit program is invoked before and after each api request to format screens for edf to display. Communication between the task-related user exit and edf is contro...
Page 324
Table 16 describes each stage of the interface between the task-related user exit and edf, relating the descriptions to the (tn) and (en) expressions in figure 11. Table 16. Description of each stage of the task-related user exit/edf interface invocation description (t1) task-related user exit invok...
Page 325
Operators. This section lists what you must do before you can use the adapter, and describes the commands used by the supervisor to administer task-related user exit programs. What you must do before using the adapter a task-related user exit program must be both enabled and started before it is ava...
Page 326
Capable of waiting for in-doubt resolution. This applies to local resources such as files, and also other rmcs, such as lu6.1, lu6.2, or mro connections to other systems. V an inbound resync command from a resource manager that requests resynchronization for a uow that cics was in-doubt about, resul...
Page 327
Chapter 3. The user exit programming interface (xpi) this chapter describes the user exit programming interface (xpi) of cics transaction server for z/os, version 3 release 2. It is divided into the following sections: v “overview of the xpi” is an introduction to the xpi. V “making an xpi call” on ...
Page 328
– release all storage held by the search_ldap function—see “the free_search_results call” on page 324. V using the xpi dispatcher functions, you can: – obtain a suspend token for a task—see “the add_suspend call” on page 334 – suspend execution of the issuing task—see “the suspend call” on page 335 ...
Page 329
– inquire about the attributes of a specified program—see “the inquire_program call” on page 366 – inquire about the attributes of the program that is currently running—see “the inquire_current_program call” on page 373 – set selected attributes in the definition of a specified program—see “the set_...
Page 330
– inquire about an attached transaction—see “the inquire_transaction call” on page 414 – change the task priority and transaction class of the current task—see “the set_transaction call” on page 418. V using the xpi user journaling function, you can: – write a record to a cics journal—see “the write...
Page 331
Mandout2(value), ... [optout1(value),] [optout2(value),] ... Response, reason] xpi calls follow assembler-language coding conventions: v the “macro-name” must begin before column 16. V the continuation lines must begin in column 16. V there must be no embedded blanks apart from the blank between the...
Page 332
Note: failure to clear the parameter list can cause unpredictable results, such as program checks or storage violations. If you are building the parameter list incrementally, specify clear before specifying any parameters. If you are not building the parameter incrementally, specify clear when the c...
Page 333
Dfhxxyyx. You cannot assume that the arithmetic values of corresponding response codes are the same for all macro calls. The meanings of the response codes are as follows: ok the xpi request was completed successfully. Exception the function was not completed successfully for a reason which could be...
Page 334
If a dfhdssrx suspend or wait_mvs call does not specify an interval, and gets this response with a reason of ‘task_cancelled’ or ‘timed_out’, it indicates that the task has been purged by an operator or an application, or by the deadlock time-out facility. In this case, you must set a return code of...
Page 335
The xpi copy books there is a copy book for each xpi function, to provide the dsects associated with that function. These dsects allow you to map the parameters and the response and reason codes of an xpi call. You must include in your exit program a copy statement for each xpi function that you are...
Page 336
In the first 4 bytes of the lifo storage addressed by uepxstor. In this example, the initialization of the parameter list (using the clear option), the building of the parameter list, and the getmain call occur in a single macro. For details of how to build the parameter list incrementally, and how ...
Page 337
Title ’guexpi - global user exit program with xpi’ ************************************************************************* * the first three instructions set up the global user exit * * environment, identify the user exit point, prepare for the use of * * the exit programming interface, and copy i...
Page 338
************************************************************************** * before issuing an xpi function call, set up addressing to xpi * * parameter list. * ************************************************************************* * l r5,uepxstor set up addressing for xpi * parameter list * usin...
Page 339
************************************************************************* * test smmc_response -- if ok, then branch round error handling. * ************************************************************************* * * cli smmc_response,smmc_ok check response and... Be stok ...If ok, bypass error ro...
Page 340
An example showing how to build a parameter list incrementally in the following example, the parameter list is built incrementally. The initialization of the parameter list (using the clear option), the building of the parameter list, and the getmain call are separated into discrete steps. Dfhsmmcx ...
Page 341
Out, * address((r6)), * response(*), * reason(*) important you must set your parameters using only the xpi functions. Xpi syntax the xpi functions use special syntax. The description of each function defines only the options that are specific to that call. Options that are applicable to all function...
Page 343
(rn) a register, the contents of which specify in fullword binary the maximum number of bytes of data expression a decimal integer, or any arithmetic expression, including symbolic values, valid in assembler language; for example: l’area ; l’area+10 ; l’area+x’22’ ; symb/3+20 . * a required paramete...
Page 344
Cache_size(name4) a fullword that specifies the number of bytes available for caching ldap search results. A value of zero indicates an unlimited cache size. If cache_size is specified, cache_time_limit must also be specified. If neither parameter is specified, results will not be cached. Cache_time...
Page 345
Response reason kernerror none purged none note: for more detail, refer to the explanation of response and reason in “making an xpi call” on page 308. The end_browse_results call the end_browse_results call allows you to end the browse session that was started by the start_browse_results call. End_b...
Page 347
Response reason invalid none kernerror none purged none note: for more detail, refer to the explanation of response and reason in “making an xpi call” on page 308. The get_attribute_value call the get_attribute_value call allows you to retrieve the value associated with an attribute returned by the ...
Page 348
Value_array_position(name4) specifies the position of the requested value, in the value array for the current attribute. This parameter is only required if multiple values are expected. Array indexing starts at position 1. Response and reason values for get_attribute_value: response reason ok none e...
Page 349
Value_count(name4) a fullword containing the number of values returned for this attribute. There is usually one value returned. Response and reason values for get_next_attribute: response reason ok none exception browse_end invalid_buffer_length invalid_calling_sequence invalid_token not_found disas...
Page 350
Search_token(name4) the name of the fullword token that is returned by the search_ldap function. Response and reason values for get_next_entry: response reason ok none exception invalid_token invalid_buffer_length invalid_calling_sequence browse_end disaster none invalid none kernerror none purged n...
Page 351
Address of the data, and the second word contains the length in bytes of the data. For more information on block-descriptors, see “xpi syntax” on page 319. Ldap_response(name4) specifies the return code that is sent by the ldap api. Ldap_session_token(name4) the name of the fullword token that was r...
Page 353
This command is threadsafe. Ldap_response(name4) specifies the return code that is sent by the ldap api. Ldap_session_token(name4) the name of the fullword token that was returned by the bind_ldap function. Response and reason values for unbind_ldap: response reason ok none exception invalid_token l...
Page 354
The normal synchronization protocol in the normal case, synchronization involves two tasks and three operations. In the following sample operations, the tasks are a (the task that requests a service) and b (the task that processes a request from task a). 1. Task a starts the request by: v setting th...
Page 355
Because task-purging is effective only if performed between suspend and resume, suspend-fail precedes resume-fail. This means that, with the same constraints on serialization as in the normal synchronization protocol, the task-purge protocol can be logically reduced to: the difference is that set re...
Page 357
Name4 the name of a 4-byte field where the token is stored (rn) a register into which the token value is loaded. Response and reason values for add_suspend: response reason ok none exception none disaster none invalid none kernerror none purged none note: for more detail, refer to the explanation of...
Page 359
Name8 the name of the location where an 8-byte value is stored. String a string of characters without intervening blanks; if it is not 8 bytes long, it is extended with blanks or truncated as required. "string" a string of characters enclosed in quotation marks. Blanks are permitted in the enclosed ...
Page 360
Io waiting on an i/o operation or indeterminate i/o-related operation (locks, buffer, string, and so on). Lock waiting on a lock. Misc waiting on an unidentified resource. Note: this is the default reason given to the wait if you suspend a task and do not specify the wlm_wait_type parameter. Other_p...
Page 361
Attach) has expired. The token, however, remains suspended and must be the object of a resume before it can be the object of a delete_suspend. The resume call resume restarts execution of a task that is suspended or timed out. There must be only one resume request for each suspend. However, because ...
Page 362
2. ‘task_cancelled’ means that the task was canceled by operator action while it was suspended, and that the suspend token is available for use. The delete_suspend call delete_suspend releases a suspend token associated with this task. Delete_suspend dfhdssrx [call,] [clear,] [in, function(delete_su...
Page 364
Table 18. Wait_mvs call - response(purged) (continued) condition purge forcepurge dtimout interval purgeable (no) canceled proceeds normally canceled proceeds normally purgeable (yes) proceeds normally proceeds normally proceeds normally proceeds normally note: a forcepurge always assumes that the u...
Page 365
Milli_second the interval option specifies the number of milliseconds before timeout. Wlm_wait_type(name1) specifies, in a 1-byte location, the reason for suspending the task. This indicates the nature of the task’s wait state to the mvs workload manager. The equated values for the type of wait are ...
Page 366
Response and reason values for wait_mvs: response reason ok none exception none disaster none invalid none kernerror none purged task_cancelled timed_out note: 1. For more detail, refer to the explanation of response and reason in “making an xpi call” on page 308. 2. ‘timed_out’ is returned if the i...
Page 367
Literalconst a number in the form of a literal, for example b'00000000', x'ff', x'fcf4', "0" or an equate symbol with a similar value. Response and reason values for change_priority: response reason ok none disaster none invalid none kernerror none note: for more detail, refer to the explanation of ...
Page 369
The transaction_dump call transaction_dump causes a transaction dump to be taken. If the transaction dump code that you supply on input is in the transaction dump code table, the dump may be suppressed and, optionally, a system dump may be taken. For information about the dump table and how it works...
Page 371
Note: 1. For more detail, refer to the explanation of response and reason in “making an xpi call” on page 308. 2. ‘not_open’ means that the cics dump data set is closed. 3. ‘open_error’ means that an error occurred while a cics dump data set was being opened. 4. ‘partial’ means that the transaction ...
Page 372
Rather than enqueue name, allowing the nq domain to locate the enqueue control block directly, and hence more efficiently. Max_lifetime(dispatcher_task) max_lifetime(dispatcher_task) is required and specifies that all xpi enqueues are owned by the requesting dispatcher task. If you use the enqueue x...
Page 373
The enqueue_token, enqueue_name1, enqueue_name2, and max_lifetime(dispatcher_task) parameters are the same as in the enqueue function call. Response and reason values for dequeue response reason ok none exception enqueue_not_owned enqueue_locked kernel domain xpi functions the start_purge_protection...
Page 375
The define_program call define_program allows you to define new programs to the loader domain, or to change the details of programs that have already been defined. The details that you provide are recorded on the local catalog, and become immediately available. They are used on all subsequent acquir...
Page 376
Table 19. Summary of attributes defining dsa eligibility (continued) execution_key option reentrant above or below 16mb line dynamic storage area (dsa) cics yes below rdsa cics no above ecdsa cics yes above erdsa user no below udsa user yes below rdsa user no above eudsa user yes above erdsa new_pro...
Page 377
Private the program is in the dfhrpl or dynamic library concatenation. A private program need not be reentrant, and is given only limited protection from unauthorized overwriting. The degree of protection depends on the type of dynamic storage area (dsa) into which the program is loaded (see the exe...
Page 378
Response reason catalog_not_operational disaster none invalid none kernerror none purged none note: for more detail, refer to the explanation of response and reason in “making an xpi call” on page 308. The acquire_program call acquire_program returns the entry and load point addresses, the length, a...
Page 379
Name1 the name of a 1-byte location to receive the program attribute. (rn) a register in which the low-order byte receives the program attribute and the other bytes are set to zero. It can have the values reload, resident, reusable, or transient. Reload the program is not reusable, and therefore sev...
Page 380
Response and reason values for acquire_program: response reason ok none exception no_storage program_not_defined program_not_found disaster none invalid none kernerror none purged none note: 1. For more detail, refer to the explanation of response and reason in “making an xpi call” on page 308. 2. A...
Page 381
Name8 the name of a location containing an 8-byte program name. String a string of characters naming the program. "string" a string in quotation marks. The string length is set to 8 by padding with blanks or truncating. Program_token(name4), specifies a token identifying the program to be released. ...
Page 382
String a string of characters naming the program. "string" a string in quotation marks. The string length is set to 8 by padding with blanks or truncating. Response and reason values for delete_program: response reason ok none exception program_not_defined disaster none invalid none kernerror none p...
Page 384
Inquire_monitoring_data calls cannot be used in any exit program invoked from any global user exit point in dfhtcp or dfhzcp (that is, at any of the exit points named “xtcx...” or “xzcx...”). The monitor call the monitor xpi call is similar to the exec cics monitor command. It enables you to invoke ...
Page 385
Expression a valid assembler-language expression giving the fullword binary variable for this emp. Name4 the name of a 4-byte field containing the fullword binary variable for this emp. (ra) a register containing the fullword binary variable for this emp. * the value of this option is already presen...
Page 386
"string" a string, enclosed in quotation marks, and possibly containing blanks. This value is processed in the same way as the “string” above. Note: if, when defining the emp in the mct, you do not specify an entry name, the entry name defaults to ‘user’. Entryname likewise defaults to ‘user’ if not...
Page 387
The dfhmntds dsect that maps the data is of fixed format. Note that: v all the cics system-defined fields in the performance records (including fields that you have specified for exclusion using the exclude option of the dfhmct type=record macro) are listed. V no user-defined data fields are listed....
Page 388
Program management xpi functions there are eight xpi program management functions. These are the dfhpgisx calls: inquire_program inquire_current_program set_program start_browse_program get_next_program end_browse_program and the dfhpgaqx calls: inquire_autoinstall set_autoinstall used with the load...
Page 390
Threadsafe the program is defined as threadsafe, and is able to run under whichever tcb is in use by its user task when the program is given control. This could be either an open tcb or the cics qr tcb. Note: in the case of a language environment-conforming program, the concurrency as originally def...
Page 394
Not_applic not applicable. The program is remote. Private the program is to be loaded from the dfhrpl or dynamic library concatenation.. A private program need not be reentrant, and is given only limited protection against unauthorized overwriting. The degree of protection depends on the type of dyn...
Page 395
Response and reason values for inquire_program: response reason ok none exception program_not_defined_to_ld program_not_defined_to_pg disaster abend lock_error invalid invalid_program_token kernerror none purged none the inquire_current_program call inquire_current_program returns information about ...
Page 402
The get_next_program call get_next_program allows you to inquire on the next program definition during a browse sequence initiated by start_browse_program. The browsing sequence is alphabetical. The end of the alphabetic list of definitions is indicated by an 'end_list' exception response. Get_next_...
Page 403
New_program_token(name4) returns a token that identifies the next definition in the browse sequence. You can use it in the browse_token field of your next get_next_program call (or end_browse_program call, if you want to end the sequence). You can also use it in the program_token field of inquire_pr...
Page 406
State data access xpi functions the state data access functions allow you to inquire on and set certain system data in the ap domain. The inq_application_data call the inq_application_data call enables you to inquire on application system data in the ap domain. Inq_application_data dfhapiqx [call,] ...
Page 408
Name4 the name of a 4-byte area that is to receive the length, in bytes, of the twa. (rn) a register that is to receive the length of the twa. * the parameter list itself, name apiq_twasize, is used to hold the length of the twa. Response and reason values for inq_application_data: response reason o...
Page 411
Name2 the name of a 2-byte area that is to receive, as a half-word binary value, the level number of the mvs element of os/390. For example, os/390 release 3 mvs is represented by 03. Note: this field is supported for compatibility purposes only. The information is derived from the last two numbers ...
Page 414
Response and reason values for set_system: response reason ok none invalid invalid_function exception akp_size_error no_keypoint disaster set_failed purged none storage control xpi functions there are seven xpi storage control functions. These are the dfhsmmcx macro calls getmain, freemain, inquire_...
Page 417
2. ‘insufficient_storage’ is returned if the getmain request was specified with suspend(no), and there was not enough storage available to satisfy the request. 3. ‘purged’ is returned if the getmain request was specified with suspend (yes), there was not enough storage to satisfy the request, and th...
Page 420
Response and reason values for inquire_short_on_storage: response reason ok none disaster none kernerror none the inquire_task_storage call inquire_task_storage enables you to request details of all elements of task-lifetime storage belonging to a task. You can specify the transaction number of the ...
Page 421
Response reason no_transaction_environment disaster none invalid none kernerror none purged none the switch_subspace call switch_subspace causes cics to switch from a subspace to base space, if the task is not already executing in the base space. If the task is already in the base space, storage man...
Page 422
The trace_put call trace_put writes a trace entry to the active trace destinations. You should only make a trace_put call when ueptron indicates that tracing is active for the function containing the exit program (see ueptron in dfhuepar). You may prefer to make “exception” trace entries, in case of...
Page 423
Expression a valid assembler-language expression that results in the address name4 the name of a fullword containing the address (ra) a register containing the address. Response values for trace_put the response field is never set for the trace_put function. This is for performance reasons. It is no...
Page 424
Name8 the name of an 8-byte location to receive the name of the bridge exit program. Bridge_transaction_id(name4) returns the name of the bridge monitor transaction that issued a start brexit transid command to start this transaction. If context returns normal, the contents of this field are meaning...
Page 425
The inquire_dtrtran call inquire_dtrtran returns the name of the dynamic transaction routing (dtr) transaction definition. The dtr transaction definition provides common attributes for transactions that are to be dynamically routed and which do not have a specific transaction definition. It is speci...
Page 428
Name4 the name of a 4-byte location that is to receive the current maximum number of active tasks currently allowed for this transaction class, expressed as a binary value. (rn) a register to receive the current maximum number of active tasks currently allowed for this transaction class, expressed a...
Page 430
Xmxd_no a transaction dump is not required. Dynamic(name1) returns, in a 1-byte location (name1), an equated value indicating whether the transaction is defined for dynamic transaction routing. Xmxd_yes the transaction is to be dynamically routed to a remote cics. Xmxd_no the transaction is not to b...
Page 431
Name4 the name of a 4-byte location that contains the name of the transaction identifier. String a string of characters, without intervening blanks, naming the transaction identifier. ‘string’ a string of characters, within quotation marks, naming the transaction identifier. The string length is set...
Page 432
Xmxd_own the reserved name own is specified for the partitionset, which means tasks running under this transaction definition perform their own partitionset management. Partitionset_name(name8) returns the name of the partitionset defined on the transaction definition. Name8 the name of an 8-byte lo...
Page 434
Storage_clear(name1) returns, in a 1-byte location (name1), an equated value indicating whether task-lifetime storage, of tasks associated with this transaction definition, is to be cleared before it is freed by a freemain command. Xmxd_no task-lifetime storage need not be cleared before it's freed....
Page 435
Tclass(name1) returns, in a 1-byte location (name1), an equated value indicating whether the transaction belongs to a transaction class. Xmxd_no the transaction is not a member of a transaction class. Xmxd_yes the transaction is a member of the transaction class named in the tclass_name parameter. T...
Page 438
Xmiq_td the principal facility is a transient data queue. Xmiq_terminal the principal facility is a terminal. Netname(name8) returns the network name of the principal facility associated with this task. Name8 the name of an 8-byte location to receive the network name. Original_transaction_id(name4) ...
Page 439
Start_code(name1) returns, in a 1-byte location (name1), an equated value indicating how the task was started: c a cics internal attach. Xmiq_df the start code isn't yet known—to be set later. Xmiq_qd a transient data trigger level attach. Xmiq_s a start command without any data. Xmiq_sd a start com...
Page 440
Trannum(name4) returns the task number of the transaction. Name4 the name of a 4-byte location to receive the task number. Transaction_token(name8) specifies the transaction token for the task being inquired upon. This parameter is optional, and if omitted, the current task is assumed. If you issue ...
Page 441
Task_priority(name4) specifies the new task priority being set for the task identified by transaction_token. Name4 the name of a 4-byte location that contains the new task priority number, expressed as a binary value. Tclass_name(name8) specifies the new transaction class name that you want to assoc...
Page 443
Response reason journal_not_open length_error status_error disaster none invalid none kernerror none purged none note: for more detail, refer to the explanation of response and reason in “making an xpi call” on page 308. Chapter 3. The user exit programming interface (xpi) 421.
Page 444
422 customization guide.
Page 445
Part 2. Customizing with initialization and shutdown programs © copyright ibm corp. 1977, 2011 423.
Page 446
424 customization guide.
Page 447
Chapter 4. Writing initialization and shutdown programs you can write programs to run during the initialization and shutdown phases of cics processing. Any program that is to run at these times must be defined to cics in a program list table (plt). Information about how to code the plt is provided i...
Page 448
V first phase pltpi programs must not enable any task-related user exit program with the taskstart option. V because first-phase plt programs run so early in cics initialization, no resource definitions are available. This means that you cannot use installed program definitions (or the program autoi...
Page 449
Note: a pseudo-terminal: – must be a surrogate tctte that exists only in an aor – can be used only in a transaction routing environment – cannot exist with distributed program link (dpl) requests – cannot exist with any type of function shipping request – cannot exist in a distributed transaction. V...
Page 450
Writing shutdown programs any program that is to execute during cics shutdown must be defined in a program list table (plt), and the plt must be named on the program list table shutdown (pltsd) system initialization parameter. You can override the pltsd value by providing a plt name on the cemt perf...
Page 451
To be started, and they cannot communicate with terminals. Further, second phase plt programs must not cause any resource security checking or db2 calls to be performed. If a transaction abend occurs while the pltsd program is running, cics is left in a permanent wait state. To avoid this happening,...
Page 452
Program causes the relevant unit of work to be shunted. The pltpi program abends asp1, and cics runs the next program defined in the pltpi table, if any. V pltsd programs run under the transaction that issued the perform shutdown command. The cemt transaction is defined with wait(yes). Therefore, if...
Page 453
1. Create a separate program resource definition using the same jvmclass attribute value and specify execkey(cics). 2. Add the program resource definition to the plt. The original program resource definition with execkey(user) can then be used subsequently. Data storage key for plt programs the stor...
Page 454
432 customization guide.
Page 455
Part 3. Customizing with user-replaceable programs © copyright ibm corp. 1977, 2011 433.
Page 456
434 customization guide.
Page 457
Chapter 5. General notes about user-replaceable programs the comments in this chapter apply to all the user-replaceable programs described in part 3 of this book. The chapter is divided into the following sections: 1. “rewriting user-replaceable programs” 2. “assembling and link-editing user-replace...
Page 458
Assembling and link-editing user-replaceable programs the source for the cics-supplied user-replaceable programs is installed in the cicsts32.Cics.Sdfhsamp library. If you intend changing any of these programs, take a copy of the cicsts32.Cics.Sdfhsamp library and update the copy only. If the origin...
Page 459
2 the library into which the load module will be link-edited. 3 optionally, the name of a library containing your local assembler macros and copy members. 4 these options are required for dfhxcurm, and for the supplied sample versions of dfhtep and dfhznep. 5 your_sourcelib is the name of the librar...
Page 460
Data storage key for user-replaceable programs the storage key of storage used by user-replaceable programs depends on how the storage is obtained: v the communication area passed to the user-replaceable program by its caller is always in cics key. V any working storage obtained for the user-replace...
Page 461
Chapter 6. Writing a program error program considerations common to all user-replaceable programs note that the comments contained in chapter 5, “general notes about user-replaceable programs,” on page 435 apply to this chapter. The cics-supplied default program error program (dfhpep) contains code ...
Page 462
V the program status word (psw) at the time of the (current) abend, at pep_com_psw. The full contents of pep_com_psw are significant for abend codes ‘asra’, ‘asrb’, and ‘asrd’ only; the last four characters (the psw address) apply also to code ‘aica’. V the gp registers (0-15) at the time of the (cu...
Page 463
Dfheistg dsect , * * insert your own storage definitions here * dfhpcom type=dsect *********************************************************************** * * * * * p r o g r a m e r r o r * * * * * * * * * * p r o g r a m * * * * * *******************************************************************...
Page 464
Dfhpep_commarea dsect * * standard header section * pep_com_standard ds 0f pep_com_function ds cl1 always ’1’ pep_com_component ds cl2 always ’pc’ pep_com_reserved ds c reserved * * abend codes and eib * pep_com_current_abend_code ds cl4 current abend code pep_com_original_abend_code ds cl4 original...
Page 465
The sample program error programs two source-level versions of the default program are provided: dfhpep, coded in assembler language, and dfhpepd, coded in c. Both are in the cicsts32.Cics.Sdfhsamp library. There is an assembler-language macro, dfhpcom, and a corresponding c copy book, dfhpcomd, tha...
Page 466
444 customization guide.
Page 467
Chapter 7. Writing a transaction restart program the transaction restart user-replaceable program (dfhrest) enables you to participate in the decision as to whether a transaction should be restarted or not. Cics invokes dfhrest when a transaction abends, if restart(yes) is specified in the transacti...
Page 468
V the transaction abend which caused the transaction to be terminating abnormally must have been detected before the commit point of the implicit syncpoint at the end of the transaction has been reached. V the transaction must be defined as restartable in its transaction definition. V the transactio...
Page 469
The equated values for this parameter are: xmrs_write_yes means a terminal write has been performed by the transaction. Xmrs_write_no means a terminal write has not been performed by the transaction. Xmrs_syncpoint indicates, in a 1-byte field, whether the transaction has performed any syncpoints. T...
Page 470
V afcw, indicating that the transaction abended due to a vsam-detected deadlock (rls only). The source of the cics-supplied default transaction restart program, dfhrest, is supplied in assembler language only, in the cicsts32.Cics.Sdfhsamp library. The assembler copybook for mapping the communicatio...
Page 471
Chapter 8. Writing a terminal error program considerations common to all user-replaceable programs note that the comments contained in chapter 5, “general notes about user-replaceable programs,” on page 435 apply to this chapter. This chapter contains information about the cics terminal error progra...
Page 472
Version of the terminal error program (dfhtep, either cics-supplied or user-written), so that it can take the appropriate action. Terminal control program when the terminal from which the error was detected has been put out of service, the terminal control program creates a terminal abnormal conditi...
Page 473
The communication area the communication area is the basic interface used by the sample dfhtep, and should be used by a user-written dfhtep to: v address the tacle v indicate the course of action to be taken on return to dfhtacp. Before giving control to dfhtep, dfhtacp establishes which default act...
Page 474
Of as the number of error occurrences that are permitted for a given type of error on a given terminal before the sample dfhtep accepts the dfhtacp default actions. Optionally, the number of occurrences can be controlled and accounted for over prescribed time intervals (for example, if more than thr...
Page 475
An ese records the occurrence of a particular type of error associated with the terminal. The contents of an error status element are described in the tepcd dsect (generated by the dfhtepm type=initial macro) under the comment “error status element format”. The number of eses per teb remains constan...
Page 476
Figure 22 on page 456 gives an overview of the structure of the sample terminal error program. Entry and initialization on entry, the sample tep uses dfheient to establish base registers and addressability to exec interface components. It obtains addressability to the communication area passed by df...
Page 477
General exit control is passed to a general exit routine from each error processor. This routine determines whether the terminal is to remain in service. If the terminal is to be put out of service, the terminal error block and all error status elements for that terminal are deleted from the tep err...
Page 478
Sample terminal error program messages the messages logged to the transient data destination csmt (or, optionally, to the destination specified in the options operand of dfhtepm type=initial) are of six types, each identified by a unique message prefix. You can control the selection dfhtacp entry an...
Page 479
Of each type of message by using the appropriate parameters specified on the print operand of dfhtepm type=initial. These messages are: dfhtep, error – error text during dfhtep module generation, the print parameter specified errors. This message can be suppressed by using the noerrors option. The e...
Page 480
This message contains the symbolic terminal id of the device associated with the error. This message can be suppressed by using the notid option. Dfhtep, decb - decb information during the dfhtep module generation, the print parameter specified decb. This two-line message contains the decb (printed ...
Page 481
Macros are related and care must be taken to ensure compatibility. The parameters concerned are identified in the descriptions of the macros later in this chapter. If you use the sample terminal error program (dfhxtep), you can generate the required program and transaction definitions by using the c...
Page 483
Time this type of threshold testing is supported. Notime this type of threshold testing is not supported. Print=print-information specifies which types of information are to be logged to the transient data destination each time an error occurs. If notd is specified on the options operand, all print ...
Page 485
Type=errproc indicates that a cics-supplied error processor routine is to be replaced with the user-written error processor that immediately follows the macro. This macro is optional; if used, it must follow the dfhtepm type=initial macro. One dfhtepm type=errproc macro must precede each user-writte...
Page 486
Dfhtept–generating the sample dfhtep tables the following macros are required to generate the terminal error program tables: v dfhtept type=initial—to establish the control section. V dfhtept type=permtid—to define permanently reserved terminal error blocks (tebs) for specific terminals. V dfhtept t...
Page 487
Dfhtept type=initial–establishing the control section the dfhtept type=initial macro necessary to establish the control section for the tep tables is: type=initial establishes the beginning of the generation of the tep tables. Maxtids=number specifies the total number of permanent and reusable termi...
Page 488
Type=permtid defines permanently reserved terminal error blocks for specific terminals. Permanent tebs are defined for terminals that are critical to system operation to ensure that error processors are always executed in the event of errors associated with that terminal. If no permanent tebs are to...
Page 489
Default actions to be taken. If the number of occurrences is less than the threshold, the error processor normally takes a logic path that overrides the dfhtacp default actions. The updating and testing of the current threshold counts are normally performed by a dfhtep subroutine that sets a conditi...
Page 491
Dfhtept type=final–terminating dfhtept entries the dfhtept type=final macro terminates the generation of the dfhtep tables. Dfhtept–examples of how the macros are used 1. The following is an example of the minimum number of statements required to generate the tep tables: dfhtept type=initial,maxtids...
Page 492
Writing your own terminal error program you can write your own terminal error program in any of the languages supported by cics. However, cics-supplied code is provided in assembler language only. The names of the supplied source files and macros, and the libraries in which they can be found, are li...
Page 493
Addressing the contents of the communication area after your terminal error program receives control from dfhtacp, it should obtain the address of the communication area by means of an exec cics address commarea command. You generate the communication area dsect by coding dfhtepca type=dsect in your...
Page 494
Abortwr (x'08') abend write, free terminal storage relttioa (x'04') release tcam incoming message. (tcam is no longer supported.) signoff (x'02') call sign-off program. On entry to dfhtep, the above flags represent the default actions set by dfhtacp. The write-abend bit (communication area field abo...
Page 495
And dfhtacp writes the ‘dfhtc2522 intercept required’ message to csmt; if the task is not marked nonpurgeable, it is abended with code ‘aexy’ or, rarely, ‘aexz’. V abend write has no effect if the tctte was associated with a read request. In this case the normal result is that, if the line and termi...
Page 496
After you have carried out the required functions and, optionally, altered the default actions scheduled by dfhtacp, the user-written dfhtep must return control to dfhtacp by issuing the exec cics return command. Dfhtacp then performs the actions specified in the tacle and causes the error processin...
Page 497
Example of a user-written terminal error program the “dfhtep recursive retry routine” on page 476 is an example of the logic steps necessary to design a portion of the terminal error program. In figure 28 on page 477, 10 retries are provided for each terminal; however, the logic could be used for an...
Page 498
(pcicnt) represents a user-defined field used to accumulate the count of recursive errors. It should be in the process control information (pci) area of the tctte. System count (tctteni) represents the 6-byte field in the tctte that contains the terminal input and output counts (tctteni+tctteno). In...
Page 499
*asm xopts(noprolog noepilog sp) ************************************************************************ * * * dfhtep recursive retry routine * * * ************************************************************************ dfheistg dfheiend dfhtepca type=dsect commarea passed by tacp copy dfha06ds st...
Page 500
Note that the code in figure 28 on page 477 is intended only as an illustration of a recursive error handling technique and of the steps necessary to establish addressability to the applicable control blocks. Exec cics collect statistics terminal(tepcatid) set(statbar) * get statistics for this term...
Page 501
Chapter 9. Writing a node error program considerations common to all user-replaceable programs note that the comments contained in chapter 5, “general notes about user-replaceable programs,” on page 435 apply to this chapter. This chapter contains information about the node error program (nep) of ci...
Page 502
Background to cics-vtam error handling in general, errors detected by cics-vtam terminal control are queued for handling by a special task, the cics node error handler (transid csne). (note that cics finds it convenient to use the same technique for some housekeeping work, such as sending “good morn...
Page 503
Redirecting to another. With messages sent with exception-response only, cics may not have the data available to send it again, but the requesting application might be able to re-create it. For example, if an error were signaled during the sending of a document to a printer, it might be able to rest...
Page 504
The action flags can be set or reset within dfhznep. The action flags set by dfhznac for specific error codes and sense codes are listed in appendix b, “default actions of the node abnormal condition program,” on page 855. The default nep the cics-supplied default nep, dfhznep, sets the “print tctte...
Page 505
Other, reusable nebs for general use. If you expect to accumulate error statistics about 10 lus concurrently, you need 10–12 nebs. Each neb may contain multiple recording areas, one being used for each group of errors you want to distinguish. The error groups correspond to those in the nep. That is,...
Page 506
Will then locate the correct esb within a selected neb. The latter may be permanently dedicated to the lu in error (a named neb), or may be one taken from the general pool. The initial code then invokes the appropriate user logic for that error group. The initial code also sets up pointers to the co...
Page 507
The 3270 sample code is not intended to cover all error conditions. Note that the code is not suitable for sna 3270s (lu session type 2). Error conditions arising from these result in different dfhznac error codes and may require different handling. You may find that the cics-supplied code is not su...
Page 508
You also have to provide the sub-neps for the various nep transaction classes, including, of course, one for the default nepclass(0). Each of these sub-neps needs a separate program definition. You have the same choice in coding each sub-nep as you had when there was just one; you can code your own,...
Page 509
Dfhznac assumes that system sense codes are available upon receipt of an exception response from the logical unit. Thus, analysis is performed to determine the reason for the response. Decisions, such as which action flags to set and which requests are needed, are made based upon the system sense co...
Page 510
The significance of each section of the communication area is described below: header a 4-byte header common to all user-replaceable programs. Error_being_processed identifiers of the error code and the terminal associated with the error. User option bytes flags that indicate the default actions set...
Page 511
********************************************************************** ** header ** ** these fields are read only ** ********************************************************************** nepcahdr ds 0xl4 standard header nepcafnc ds xl1 function code always ’1’ nepcacmp ds xl2 component code always ...
Page 512
********************************************************************** ** vtam information - any vtam sense and rpl codes ** ** these fields are read only ** ********************************************************************** twavtam ds 0xl12 vtam information twarplcd ds h vtam rpl feedback codes...
Page 513
The next sections describe fields in the parameter list that can be reset within dfhznep. See also “coding for the 3270 ‘unavailable printer’ condition” on page 506, which describes the use of the flags in the “unavailable printer return code” field, and “using the node error program with xrf or per...
Page 514
Causes cics to take a system dump when there is no task attached to the terminal at the time of error detection, if the flag twaoat in twaopt2 is also set on. Setting the twaonqn flag causes the network qualified name to be printed after any message that contains the action flag. Similarly setting t...
Page 515
“good morning” message transaction is initiated (the transaction specified by the system initialization parameter gmtran). The flags are: twaoas (x'80') abandon any send for this terminal twaoar (x'40') abandon any receive for this terminal twaoat (x'20') abend any task attached to tctte twaoct (x'1...
Page 516
Twaoncn (x'10') normal clsdst (no reset allowed) twaoscn (x'08') normal clsdst (reset allowed) twaonegr (x'04') send negative response twaoos (x'02') keep node out of service twaocn (x'01') clsdst node. Do not set this flag when processing error codex'49' (tczclsin). Twaonint forces twaocn. Twaonegr...
Page 517
Twanld of the communication area, and the length of the data in field twanldl. The data is logged to the csne transient data queue for future inspection. Note: no data in excess of 220 bytes is logged. You can also send user-written messages to the csne log using the transient data facility. To writ...
Page 518
The sample node error program the sample node error program provides a general environment for the execution of error processing routines (error processors), each of which is specific to certain error codes generated by the node abnormal condition program. Sufficient optional error processors for no...
Page 519
V optional error processors for 3270 or interactive logical units. A node error program cannot be generated with both 3270 and interactive logical unit error processors. The components are described in the sections that follow. Entry section on entry, the sample nep uses dfheient to establish base r...
Page 520
Optional common subroutines the common subroutines are addressed via the csvt and provide error processors with the following functions: v locate or assign nebs and esbs on the basis of node id and error group index. V time stamp an error, update an error count, and test an error count against numer...
Page 521
Optional error processor for interactive logical units only one error processor is supplied for interactive lus: group index 1, with error code x'dc'. This error code, in combination with a user sense value of x'081b', indicates a ‘receiver in transmit mode’ condition. The action flags in twanpfw ar...
Page 522
Dfhsnep type=ustor to define storage, then both it and dfhsnep type=ustorend must be coded before dfhsnep type=initial. The dfhsnep type=ustorend macro has the following format: this macro indicates the end of user storage definitions. Its use is mandatory if dfhsnep type=ustor has been coded. If yo...
Page 523
Dfhsnep type=errproc,group=1,code=(d9,dc,dd,f2) sense/status error processor code. Dfhsnep type=errproc,group=2,code=42 unavailable printer error processor code. Dfhsnep type=defilu—including error processors for intlus the dfhsnep type=defilu macro has the following format: type=defilu specifies th...
Page 524
In the range x'01' through x'ff' (a leading zero can be omitted). The error processor name has the form neprocxx, where “xx” is the error group index. A csect statement of this name is generated, which causes the error processor code to be assembled at the end of the node error program module and to...
Page 525
4. Registers 4 through 9 can be saved by common subroutines in an area reserved in exec interface storage at label nepcsrs. They must be restored before return from the subroutines. Dfhsnet—generating the node error table the dfhsnet macro is used to generate a node error table. Each node error tabl...
Page 526
Specified in the count operand is not exceeded before this time interval elapses, the error count is reset to 0. Specify “units” as sec, min, or hrs. The maximum values for “interval” are as follows: (86400,sec), (1440,min), or (24,hrs). This operand is optional, and the default is set to (7,min). D...
Page 527
Csvtesbl ds a nepesbl - esb locate routine csvtnebd ds a nepnebd - neb delete routine csvtecup ds a nepecup - error count update routine writing your own node error program you can write your own nep in any of the cics-supported languages. However, cics-supplied nep code is provided in assembler lan...
Page 528
V updates to recoverable resources. If the resources are locked by another task, the csne unit of work could be suspended or shunted. You should also note that you cannot use the nep to suppress dfhznac messages. Entry and addressability on entry, your nep should issue the commands: exec cics addres...
Page 529
Before linking to the node error program, dfhznac inserts the primary and secondary printer netnames and terminal ids into the communication area, indicating also whether either printer is eligible for a print request. Dfhznac links to the node error program with no default actions set. On return fr...
Page 530
If used in this way, the initiated transaction can write an appropriate signon message when the session has been acquired. Note, however, that if logonmsg=yes is specified on the ceda define typeterm command, the cics “good morning” message is also initiated when the session is opened. Refer to “res...
Page 531
Dfhznepi type=initial—specifying the default routine the dfhznepi type=initial macro specifies the name of the default transaction-class routine to be used for the dfnznepi module. Default=name specifies the name of the default transaction-class routine to be used. A link is made to this default rou...
Page 532
Handling shutdown hung terminals in the node error program error code: x'6f' symbolic name: tczsdas message number: dfhzc2351 for error code x'6f', dfhznac passes the setting of tcsactn and the dfhzc2351 reason code to dfhznep, and dfhznep can modify the force-close action for the current terminal. ...
Page 533
System-wide recovery notification options (whether terminal users are notified of a recovery, the recovery message, or the recovery transaction) for some terminals, you should write your own error processor to handle code x'3f'. (for details of the recovery notification parameters passed to the nep,...
Page 534
Changing the recovery message if you define a terminal with recovnotify(message) in its typeterm definition, a recovery message is sent to the terminal after takeover. By default, for an xrf takeover, this is the following cics-supplied message in bms map dfhxrc1 of map set dfhxmsg: cics/esa has rec...
Page 535
The others have all been shut down), the issue pass command does not fail with an invreq. Instead, the terminal is logged off and message dfhzc3490 is written to the csne log. You may want to code your node error program to deal with the situation when message dfhzc3490 (dfhznac error code x'c3') is...
Page 536
514 customization guide.
Page 537: Terminals
Chapter 10. Writing a program to control autoinstall of terminals considerations common to all user-replaceable programs note that the comments contained in chapter 5, “general notes about user-replaceable programs,” on page 435 apply to this chapter. This chapter describes how to write a program to...
Page 538
V create some model terminal definitions. V define the terminals to vtam, so that their definitions in vtam match the model terminal definitions in cics. V if you are using model terminal support (mts), define the mts tables to vtam. V use the default autoinstall control program for terminals (dfhza...
Page 539
Coding entries for mts you need to define model names (mdltab, mdlent, and mdlplu macros) and printer and associated printer names (asltab, aslent, and aslplu macros) to vtam. The autoinstall control program for terminals in addition to managing your resource definition, your autoinstall control pro...
Page 540
V autoinstall processing has been completed to a point where information (a terminal identifier and autoinstall model name) from the control program is required to proceed. The communication area at install for terminals the layout of the communication area is shown in figure 36. The parameter list ...
Page 541
The control program selects one model from this list, and cics uses this model to build the tctte for the device. The default autoinstall control program, dfhzatdx, always selects the first model name in the list. If you are not using mts but need a printer id or netname (or an alternative printer i...
Page 542
Model name into the model name list (autinstmodelname_1), and also into the model name field (modelname) in the selection list addressed by fullword 4 of the parameter list. If cics is unable to find an mts model name in the mts control vector, or the named model does not exist or is invalid, it bui...
Page 543
Used to name a connection. It should therefore conform to the naming standards for a connection (rather than a terminal) as defined in connection definition attributes, in the cics resource definition guide. The user program could identify an lu6.2 autoinstall request in one of the following ways: –...
Page 544
As a general rule, all the models in the list passed to your program match the vtam data for the terminal. That is, a viable tct entry usually results from the use of any of the models. (the exception to this rule involves the vtam rusize; if this value is incompatible, cics issues an error message....
Page 545
However, you may be in a situation where you must continue to use unique and predictable terminal names for your terminals. Your control program must be able to assign the right terminal name to each terminal, every time the user logs on. Two possible approaches to this problem are: v devise another...
Page 546
Satisfactory, cics schedules the new resource for opndst in order to complete the logon request. If the installation process fails, then the control program is driven again, as though a delete had occurred. (see the section “the autoinstall control program at delete” on page 525 for details.) this i...
Page 547
The autoinstall control program at delete to provide symmetry of control over the autoinstall process, the autoinstall control program is also invoked when: v a session with a previously automatically-installed resource has been ended v an autoinstall request was accepted by the user program, but th...
Page 548
Table 27. Autoinstall control program’s parameter list at delete (continued) 1st byte 2nd byte 3rd byte 4th byte third fullword length of netname to be deleted first two bytes of netname next 15 bytes remainder of netname note that the named resource has been deleted by the time the control program ...
Page 549
If cics attempts to bind, compare the device’s cinit ru to the cics bind, and make corrections accordingly. It is very important that you ensure that the vtam logmode table entries for your terminals are correct, rather than defining new autoinstall models to fit incorrectly coded entries. Bear in m...
Page 550
The default action of the sample program, on install, is to select the first model in the list, and derive the terminal identifier from the last four nonblank characters of the netname, set the status byte, and return to cics. If there are no models in the list, it returns with no action. The defaul...
Page 551
* register conventions = * * r0 used by dfheical expansion * * r1 -------"-------"------"---- * * r2 base for input parameters * * r3 base for code addressability * * r4 base for model name list * * r5 base for output parameter list * * r6 work register * * r7 -----"------- * * r8 -----"------- * * ...
Page 552
Cobol figure 41 on page 531, in cobol, redefines the netname, so that the last four characters are used to select a more suitable model than that selected in the sample control program. * r7 now points to model name validt cli selected_modelname,c’ ’ mts model name supplied? Bne validm1 yes lh r6,mo...
Page 553
Pl/i figure 42 on page 532, in pl/i, extracts information from the vtam cinit ru, which carries the bind image. Part of this information is the screen presentation services information, such as the default screen size and alternate screen size. The alternate screen size is used to determine the mode...
Page 554
Dcl 1 cinit based(install_cinit_ptr), 2 cinit_leng fixed bin(15), 2 cinit_ru char(256); dcl save_cinit char(256); /* temp save area for cinit ru */ dcl 1 scrnsz based(addr(save_cinit)), 2 spare char(31), /* bypass first part of cinit and reach */ /* into bind image carried in cinit */ 2 dhgt bit(8),...
Page 555
/* now access the screen ps area in the portion of the bind image presented in the cinit ru */ /* using the screen alternate height as a guide to the model of terminal attempting logon. If this cannot be determined then default to the first model in the table */ select (ahgt); /* now get scrn altern...
Page 556
534 customization guide.
Page 557: Consoles
Chapter 11. Writing a program to control autoinstall of consoles considerations common to all user-replaceable programs note that the comments contained in chapter 5, “general notes about user-replaceable programs,” on page 435 apply to this chapter. This chapter describes how to write a program to ...
Page 558
Note: 1. You can have only one active autoinstall control program to handle terminals, consoles, and appc connections. You specify the name of the active program on the aiexit system initialization parameter. 2. Your autoinstall program must be able to recognise the console install and delete parame...
Page 559
The parameter list contains the following information: 1. A standard header. Byte 1 indicates the request type (this is hexadecimal character x'fd' for install), and bytes 2 to 3 contain the component code, which is always zc for consoles. (byte 4 is reserved.) 2. A pointer to a 2-byte length field,...
Page 560
How cics builds the list of autoinstall models cics builds the list of autoinstall models by selecting from its complete list of terminal models those models that define console devices. The complete list of autoinstall models available to cics at any time comprises all the definitions with autinstm...
Page 561
If you want an install request to proceed, perform these steps in your autoinstall control program: v return an autoinstall model name in the first 8 bytes of the area addressed by fullword 4 of the parameter list. V supply a cics terminal name (termid) in the next four bytes of the return area. Dfh...
Page 562
Cics action on return from the control program when cics receives control back from the autoinstall control program, it examines the return code field: v if the return code is zero, and the other required information supplied is satisfactory, cics schedules the transaction specified on the modify co...
Page 563
The sample autoinstall control programs for consoles ibm supplies a default autoinstall control program, written in each of the supported programming languages, all of which contain the necessary support for handling consoles. For details of these, see “the sample autoinstall control programs for te...
Page 564
542 customization guide.
Page 565: Connections
Chapter 12. Writing a program to control autoinstall of appc connections considerations common to all user-replaceable programs note that the comments contained in chapter 5, “general notes about user-replaceable programs,” on page 435 apply to this chapter. This chapter describes how to write a pro...
Page 566
Like autoinstall for other resources, autoinstall for appc connections requires model definitions. However, unlike the model definitions used to autoinstall terminals, those used to autoinstall appc links do not need to be defined explicitly as models. Instead, cics can use any previously-installed ...
Page 567
The autoinstall control program for appc connections the purpose of the autoinstall control program is to provide cics with any extra information it needs to complete an autoinstall request. For appc connections, the control program selects the template to be used, and provides a name for the new co...
Page 568
Install_appc_standard header a fullword input field comprising the following information: install_appc_exit_function a 1-byte field that defines the install request type. The equated values are: install_appc_ps_cinit x'f2' represents an install request for an appc parallel-session connection from a ...
Page 569
Install_appc_ss_bind x'f4' represents an install request for an appc single-session connection via a bind. Note: the values x'f0' and x'f1' represent, respectively, install and delete requests for terminals (including appc single-session devices). See chapter 10, “writing a program to control autoin...
Page 570
Your control program can use the template_netname field to specify the netname of the template. For connections between generic resources, your program can accept the suggested template passed by cics, or specify a different one—either in this field or by overwriting the suggested template with blan...
Page 571
The autoinstall control program at delete to provide symmetry of control over the autoinstall process, the autoinstall control program is also invoked when an autoinstalled appc connection is deleted. Invoking the control program at delete enables you to reverse the processes carried out at the inst...
Page 572
Synclevel 1 connections installed via a bind synclevel 1-only appc connections autoinstalled via a bind request (except for limited resource connections installed on a cics generic resource member—see next section) are implicitly deleted at the following times: v when the connection is released v if...
Page 573
Note: this type of request cannot be received by cics transaction server for z/os, version 3 release 2. Install_appc_ps_bind (x'f3') an incoming bind for an appc parallel-session connection. Specify a template. This is done in one of two ways: v for connections between two generic resources, by acce...
Page 574
552 customization guide.
Page 575: Connections
Chapter 13. Writing a program to control autoinstall of ipic connections considerations common to all user-replaceable programs note that the comments contained in chapter 5, “general notes about user-replaceable programs,” on page 435 apply to this information. This section describes how to write a...
Page 576
You can use any installed ipconn definition as a template but, for performance reasons, your template must be an installed definition that is not in use. The definition is locked while cics is copying it, and, if you have a large number of ipconns being autoinstalled at one time you might notice the...
Page 577
If the default user program is not adequate for your purposes, you can write a customized version of the default program or create your own program to provide enhanced function. Cics supplies the source code of the default program in several programming languages; see “the sample autoinstall user pr...
Page 578
Isaic_networkid (input) an 8-character field containing the network id of the system trying to connect, as sent on the connect flow. Isaic_port (input/output) the call back port number for the client. -1 means that no call back is allowed. The autoinstall user program can modify this for the same re...
Page 579
Isaic_function (input) the function for which the user program has been invoked: x'f1' after deletion of an ipconn. Isaic_ipconn (input) the name of the autoinstalled ipconn. Isaic_applid (input) the applid (of the remote system) specified on the autoinstalled ipconn. Isaic_networkid (input) the net...
Page 580
Default actions of the sample program the role of the autoinstall user program in installing ipconns is to choose the ipconn template to be used and to supply the name of the new connection. Optionally, the program can modify the values of the applid, host, and port attributes of the new connection ...
Page 581: Shipped Terminals
Chapter 14. Writing a program to control autoinstall of shipped terminals considerations common to all user-replaceable programs note that the comments contained in chapter 5, “general notes about user-replaceable programs,” on page 435 apply to this chapter. This chapter describes how to write a pr...
Page 582
Cics-generated aliases the autoinstall control program is invoked once for each shipped terminal or connection definition to be installed. If cics detects that the name on a shipped definition clashes with the name of a remote terminal, local terminal, or connection already installed in the aor, it ...
Page 583
Terminal. If, during the delay interval, the terminal definition is deleted, re-shipped, and re-installed with a different local termid, the started transaction could fail because the termid no longer exists. If your application programs record termids in this way, your autoinstall program may need ...
Page 584
Autoinstall control program at install” on page 536. The parameter list passed at install of local appc connections initiated by bind requests is described in “the communication area at install for appc connections” on page 545. The parameter list passed at install of client virtual terminals is des...
Page 585
(the value of the terminal or connection attribute on the shipped definition) is already in use in the aor to identify an installed remote terminal or connection. N the name by which the terminal or connection is known in the tor is not in use in the aor to identify a remote terminal or connection. ...
Page 586
Installed, and stored within the definition. Thus, if the definition is shipped to another region, the value of the token is shipped too. The correlation id is used by cics during attach processing, to check whether existing shipped definitions in an aor are up-to-date, or whether they need to be de...
Page 587
Delete_shipped_term (x'fa') a shipped terminal delete_shipped_rse (x'fb') a shipped connection (remote system entry). Delete_shipped_termid a 4-character field containing the identifier (termid) of the terminal or connection in the tor. Delete_shipped_applid an 8-character field containing the netna...
Page 588
566 customization guide.
Page 589: Terminals
Chapter 15. Writing a program to control autoinstall of virtual terminals virtual terminals are used by the external presentation interface (epi) and terminal emulator functions of the cics clients products, as well as the cics link3270 bridge. In a bridged environment, these virtual terminals repla...
Page 590
Termids generated by cics for client terminals consist of a 1-character prefix and a 3-character suffix. The default prefix is '\', but you can specify a different prefix using the vtprefix system initialization parameter. The suffix can have the values 'aaa' through '999'. That is, each character i...
Page 591
Same aor. However, if you are using cics-generated termids, your server programs must not rely on termids being allocated consistently to particular client terminals. A client terminal can be deleted by a client sending a cics_epidelterminal request, by an end user shutting down a client terminal em...
Page 592
If a name clash occurs in an aor, the autoinstall control program is invoked in the aor. It can resolve the conflict by allocating an alias terminal identifier to the shipped definition. How bridge facility virtual terminals are autoinstalled bridge facility virtual terminals are defined to cics tra...
Page 593
V the userid of the first transaction in a pseudoconversation can be obtained using exec cics assign userid. V the transid of the first transaction in a pseudoconversation can be obtained from eibtrnid. The autoinstall control program can use the userid and transid values to derive new termid and ne...
Page 594
Note: the communications area for install of virtual terminals is the same as that for install of shipped terminals and connections—that is why the field names contain the word “shipped”. Install_shipped_standard a fullword input field containing the following information: install_shipped_exit_funct...
Page 595
Selected_shipped_termid a 4-character field used to specify the name by which the virtual terminal will be known to cics. If the name is less than 4 characters long, it must be padded with trailing blanks. For a list of the characters you can use in terminal names, see terminal definition attributes...
Page 596
Install_brfac_standard a fullword input field containing the following information: install_brfac_exit_function a 1-byte field that indicates the type of resource being installed. For install of bridge facility virtual terminals. The equated values are: install_link_brfac (x'0f') the autoinstall pro...
Page 597
Return_ok (x'00') install the virtual terminal. This is the default value. Your user program must return this value if the resource is to be autoinstalled. Reject (x'01') do not install the virtual terminal. Selected_brfac_netname an 8-character field used to specify the netname of the bridge facili...
Page 598
Delete_shipped_exit_function a 1-byte field that indicates the type of resource being deleted. The equated value for client virtual terminals is delete_shipped_term (x'fc'). Note: a value of x'f1' represents the deletion of a local terminal, or an appc single-session device that was autoinstalled vi...
Page 599
Install_link_brfac (x'10') the autoinstall program was called during installation of a bridge facility to be used by the link3270 bridge. Install_start_brfac (x'12') the autoinstall program was called during installation of a bridge facility to be used by the start bridge. Delete_brfac_exit componen...
Page 600
578 customization guide.
Page 601: Programs
Chapter 16. Writing a program to control autoinstall of programs considerations common to all user-replaceable programs note that the comments contained in chapter 5, “general notes about user-replaceable programs,” on page 435 apply to this chapter. This chapter describes the user-replaceable progr...
Page 602
V cics calls any user-replaceable program other than the program or terminal autoinstall program. V a program is named in the pltpi or pltsd list. Autoinstall model definitions like autoinstall for terminals, program autoinstall uses model definitions, together with a user-replaceable control progra...
Page 603
Note: this assumes that the autoinstall control program chooses not to install a definition. If no definition is installed because autoinstall fails, the dynamic routing program is not invoked. Autoinstall processing of mapsets table 30 shows the differences in mapset processing between cics regions...
Page 604
Faster startup times warm and emergency starts if you are using program autoinstall with cataloging, restart times are similar to those of restarting a cics region that is not using program autoinstall. This is because, in both cases, resource definitions are reinstalled from the catalog during the ...
Page 605
The autoinstall control program at install on invocation, cics passes a parameter list to the autoinstall control program by means of a communication area addressed by dfheicap. The communications area is mapped by a copybook that is supplied in each of the languages supported by cics. The assembler...
Page 606
If you do not set this field, the autoinstall routine uses the language defined in the model, if one is specified. However, when control is passed to the program, cics determines the language from the program itself, and overrides any specification provided. You should not need to specify the langua...
Page 607
Pgac_execution_set allows you to specify, in a 1-byte field, whether or not the program is restricted to using the distributed program link (dpl) subset of the cics api. The equated values are: pgac_dplsubset the program is to be restricted to the dpl subset of the exec cics api. Pgac_fullapi the pr...
Page 608
Shared resources it takes into account the possibility that other programs may be executing concurrently and attempting to modify the same resources. Pgac_jvm allows you to specify, in a 1-byte field, whether the program is to be run under a jvm. The equated values are: pgac_jvm_yes the program is a...
Page 609
If you customize the supplied control program, or write your own version, you should note the following: v input:the first two fields of the parameter list are input-only fields and should not be altered by your program. V output:the remaining fields on the parameter list are input/output or output ...
Page 610
Group containing the definitions in your startup grouplist. If you specify an invalid name for the control program, cics disables the program, thus disabling the program autoinstall function. The following program resource definitions are supplied by cics for the autoinstall control program; the def...
Page 611
Chapter 17. Writing a dynamic routing program considerations common to all user-replaceable programs note that the comments contained in chapter 5, “general notes about user-replaceable programs,” on page 435 apply to this chapter. This chapter describes the cics default dynamic routing program and ...
Page 612
3. “routing bridge requests dynamically” on page 603 4. “routing by user id” on page 607 5. “parameters passed to the dynamic routing program” on page 607 6. “naming your dynamic routing program” on page 621 7. “testing your dynamic routing program” on page 621 8. “dynamic transaction routing sample...
Page 613
V after the routed transaction has completed, if the routing program has requested to be reinvoked at termination. V if the routed transaction abends, if the routing program has requested to be reinvoked at termination. Figure 57 shows the points at which the dynamic routing program is invoked. Info...
Page 614
Sometimes, the dynamic routing program may be invoked for transactions that are routed statically. This happens if a transaction defined as dynamic(yes) is initiated by automatic transaction initiation (ati)—for example, by the expiry of an interval control start request—but the transaction is ineli...
Page 615
Important to route a transaction defined by the dtrtran definition, your dynamic routing program must set the dyrdtrrj field of the communications area to 'n' (the default is 'y'). If you leave dytdtrrj set to 'y', the transaction is rejected. You can test the dyrdtrxn field to check if the transact...
Page 616
If the system is unavailable or unknown the dynamic routing program is invoked again if the remote system name that you specify on the route selection call is not known or is unavailable. When this happens, you have a choice of actions: v you can tell cics not to continue trying to route the transac...
Page 617
Modifying the initial terminal data the dynamic routing program should not perform an exec cics receive or an exec cics gds receive command, because this prevents the routed-to transaction from obtaining the initial terminal data. The cics relay program, dfhaprt, places a copy of the user’s initial ...
Page 618
May also need to change the input communications area passed to the routed application. Field dyracmaa of the routing program’s communications area enables you to do this; it is a pointer to the application’s communications area. See also “modifying the application’s containers” on page 607. Receivi...
Page 619
Result of logic in the routed transaction. You should also consider carefully the effect of exec cics syncpoint and abend commands on appc transaction routing. V if you want to keep information about how transactions are routed, it must be done in the user routing program, perhaps by writing the inf...
Page 620
V distributed computing environment (dce) remote procedure calls (rpcs) v onc/rpc calls. A program-link request received from outside cics can be dynamically routed by: v defining the program to cics transaction server for z/os as dynamic(yes) v coding your dynamic routing program to route the reque...
Page 621
Changing the target cics region the communications area passed to the dynamic routing program initially contains the system identifier (sysid) and netname of the default cics region to which the link request is to be routed. These are derived from the value of the remotesystem option of the installe...
Page 622
Alternative program is to be linked. You can specify a local or remote program, depending on the region to which the request is to be routed. Changing the transaction id a transaction identifier is always associated with each dynamic program-link request. Cics obtains the transaction id using the fo...
Page 623
Been set to ‘n’—the request is not to be queued—for this error to occur), issue a return code of ‘0’ in dyrretc, and try to route the request again. V you can change the sysid, and issue a return code of ‘0’ in dyrretc to try to route the request again. Note that if you change the sysid, you may als...
Page 624
For information about writing an xpceres global user exit program, see the xpceres global user exit. If a required resource is unavailable on the target region, but the xpceres exit is unavailable or disabled (or is enabled but does not set the uercresu return code), the client program receives an e...
Page 625
V the dynamic routing program can be rmode any but must be amode 31. Unit of work considerations the client program, the dynamic routing program, and possibly the server program constitute a single unit of work. Any recoverable resources owned by the dynamic routing program could therefore be affect...
Page 626
V if an error occurs in route selection, for example, if the target region returned by the routing program on its initial (route selection) call is unavailable. This allows the routing program to specify an alternate target. This process iterates until the routing program selects a target that is av...
Page 627
V if the sysids are the same (or the returned sysid is blank) cics executes the link request locally. V if the two sysids are not the same, cics routes the request to the remote cics region, using the returned transaction name. Changing the bridge request transid the transid of the target user trans...
Page 628
To use the xpceres exit, both the routing region and the target region must support the “resource unavailable” condition (resunavail). All the following support the “resource unavailable” condition: v cics ts os/390, version 1.3, with apar pq73107 applied v cics ts for z/os, version 2.2, with apar p...
Page 629
Resources, because changes to those resources may be committed or backed out inadvertently as a result of logic in the routed program. V if you want to keep information about how link requests are routed, it must be done in the user routing program, perhaps by writing the information to a temporary ...
Page 630
Important the same communications area is passed to both the dynamic routing program and the distributed routing program. Some parameters are meaningful to one routing program but not to the other. Some parameter-values may be passed to one routing program but never to the other. The following list ...
Page 631
Under the dyrfunc parameter the value x'5' is not listed because it is never passed to the dynamic routing program—it occurs only on a route initiate call to the distributed routing program. If you use the same program as both a dynamic routing program and a distributed routing program, for descript...
Page 632
When your routing program is invoked because the routed transaction has abended (dyrfunc=4), the information in the communications area, or in the dfhroute container, is not meaningful. Your routing program can alter the data in any application’s communications area, or dfhroute container, addressed...
Page 633
Dyrbrtk is the 8-byte bridge facility token associated with a link3270 bridge request. This field is valid only when dyrtype=8. Dyrcabp indicates whether or not you want cics to continue standard abend processing. Note: this field applies only to dynamic transaction routing, not to the routing of pr...
Page 634
N the transaction is not rejected. This indicator is always set to the reject condition when the dynamic routing program is invoked. To dynamically route a transaction defined by the dtrtran definition, you must change this to the accept condition. If you reject the transaction, message dfhac2001—“t...
Page 635
2 the selected system is in service, but no sessions are available. 3 an allocate request has been rejected, and sysiderr returned to the application program. This error occurs for one of the following reasons: 1. An xzique global user exit program requested that the allocate be rejected, or 2. Cics...
Page 636
3 invoked for notification of the destination of a statically-routed request. This applies in the following cases: ati requests a transaction defined as dynamic(yes) has been initiated by a terminal-related automatic transaction initiation (ati) request—for example, by the expiry of an interval cont...
Page 637
Note: this mixed level of operation, in which different cics regions in the same logical server are at different levels of cics, is intended to be used only for rolling upgrades. It should not be used permanently, because it increases the risk of failure in some interoperability scenarios. The norma...
Page 638
N the dynamic routing program is not to be reinvoked. This is the default. Y the dynamic routing program is to be reinvoked. You can specify this option for transactions, link requests, or bridge requests that are routed to remote cics regions and also for those that are executed locally. Dyrproccmp...
Page 639
8 terminate the transaction with either a message or an abend. Whenever the routing program is invoked, dyrretc is set to ‘0’. When it is invoked for route selection or because an error occurs in route selection, if you want cics to continue processing the transaction, you must leave it set to ‘0’. ...
Page 640
Client that the dynamic routing program has rejected the request, and a compcode that gives details of the reason the last attempt to route the request failed. You do not need to set a return code when the routing program is invoked for notification or at transaction termination. (any code you set i...
Page 641
– if dyrerror is set to ‘2’ (no session available) and you want cics to retry routing, you must change dyrsysid or change the value of dyrqueue to ‘y’ (queue the request until a session is available). V when dyrfunc is set to ‘2’ (termination of a routed request), dyrsysid contains the name of the c...
Page 642
2. If the original value was not obtained from the transid option of an exec cics link command. A value specified on the transid option of a link command cannot be overridden by the routing program. Dyrtype is the type of routing request for which the program is being invoked. For transaction routin...
Page 643
Dyrusern is a 1024-byte user area. Cics initializes this user area to zeroes before invoking the dynamic routing program for a given task. This user area can be modified by the dynamic routing program; the modified area is passed to subsequent invocations of the dynamic routing program for the same ...
Page 644
V the invocation of the dynamic routing program if the routed transaction abends (dyrfunc=4), if you have specified dyropter=y. If you want edf to display the execution of your dynamic routing program only, either choose dual-terminal mode, or use one of the other methods described in execution diag...
Page 645
Chapter 18. Writing a distributed routing program you can write your own distributed routing program or use the default program that is provided with cics. You must be familiar with the principles of dynamic and distributed routing that are described in the cics intercommunication guide, the cics bu...
Page 646
6. “routing by user id” on page 644 7. “dealing with an abend on the target region” on page 644 8. “some processing considerations” on page 645 9. “parameters passed to the distributed routing program” on page 645 10. “naming your distributed routing program” on page 656 11. “distributed transaction...
Page 647
3. The distributed routing program is invoked at more points than the dynamic routing program. Figure 60 on page 627 shows the points at which the distributed routing program is invoked, and the region on which each invocation occurs. 4. Unlike the dynamic routing program, the distributed routing pr...
Page 648
“daisy-chaining” is not supported. That is, once a bts activity has been routed to a target region it cannot be re-routed from the target to a third region, even though its associated transaction is defined as dynamic(yes). When the distributed routing program is invoked for bts processes and activi...
Page 649
Changing the target cics region the dyrsysid field of the communications area passed to the distributed routing program initially contains the system identifier (sysid) of the default target region to which the process or activity is to be routed. This is derived from the value of the remotesystem o...
Page 650
Returning a value in dyrretc has no effect when the routing program is invoked for notification, routing complete, transaction initiation, transaction termination, or abend. If an error occurs in route selection if an error occurs in route selection—for example, if the sysid returned by the distribu...
Page 651
Routing method requests for enterprise beans and corba stateless objects this section describes how to use a distributed routing program to dynamically route method requests for enterprise beans and corba stateless objects. It assumes that you have read the introduction to the distributed routing of...
Page 652
1. Client connections can be balanced across the listener regions, using any of the following methods: v connection optimization by means of dynamic domain name system (dns) registration. V ip routing. V a combination of connection optimization and ip routing. 2. Ots transactions can be balanced acr...
Page 653
On the local ejb/corba server, that issues a request for another bean. What happens next depends on whether or not the target object belongs to the local ejb/corba server: v if the request is for an object owned by the local ejb/corba server (that is, the corbaserver name on the requestmodel definit...
Page 654
– whether or not the target object implements costransactions::transactionalobject. V whether or not the client has an ots transaction when it issues the method request; and, if so, whether it has issued a previous method request to the same target object within the scope of the same ots transaction...
Page 655
This invocation signals that (unless the routing region and the target region are one and the same) the routing region’s responsibility for this request has been discharged. On the target region: these invocations occur only if the target region is cics ts for z/os, version 2.1 or later and the rout...
Page 656
When it is invoked for route selection, the distributed routing program can change the target region by changing the value in dyrsysid. If the specified sysid is invalid, or cannot be found, sysiderr is returned to the distributed routing program—which may deal with the error by returning a differen...
Page 657
If the routing program sets dyropter to 'y', it is re-invoked on the target region: 1. When the routed method starts on the target region. That is, when the cics transaction specified on the requestmodel definition starts. 2. V if the routed method is part of an ots transaction, if the ots transacti...
Page 658
In general, you should follow the guidelines in updating enterprise beans in a production region, in the java applications in cics manual about how to organize beans, corbaservers, and transaction ids to facilitate maintenance. One way of dealing with a disabled corbaserver is as follows: 1. If your...
Page 659
Performing a rolling upgrade of an ejb/corba server the dyrlevel field of the communications area is a migration aid, intended to help you perform a “rolling upgrade” of a multi-region logical server, whereby one region at a time is upgraded from one release of cics to the next, without bringing dow...
Page 660
Distributed routing program is invoked for notification only—it cannot route the request. Unless the sysid option of the start command specifies a remote region explicitly, the start request is function-shipped to the target region named in the remotesystem option; if remotesystem is not specified, ...
Page 661
Figure 63 shows the points at which the distributed routing program is invoked, and the region on which each invocation occurs. Note that the “target region” is not necessarily remote—it could be the local (routing) region, if the routing program chooses to execute the start request locally. Changin...
Page 662
Returning a value in dyrretc has no effect when the routing program is invoked for notification, routing complete, transaction initiation, transaction termination, or abend. If an error occurs in route selection if an error occurs in route selection—for example, if the sysid returned by the distribu...
Page 663
Invoking the distributed routing program on the target region the route selection, notification, route selection error, and routing complete invocations of the distributed routing program all occur on the routing region. If the routing program wants to be re-invoked on the target region, it must set...
Page 664
Region, even though the transaction is defined as routable(yes) and dynamic(yes). The transaction may, however, be statically routed from the target region to a third region. When the distributed routing program is invoked for inbound web service requests that are eligible for enhanced routing, cics...
Page 665
Changing the target cics region the dyrsysid field of the communications area passed to the distributed routing program initially contains the system identifier (sysid) of the default target region to which the request is to be routed. This is derived from the value of the remotesystem option of the...
Page 666
If an error occurs in route selection if an error occurs in route selection—for example, if the sysid returned by the distributed routing program is unavailable or unknown—the routing program is invoked again. When this happens, you have a choice of actions: 1. You can try to route the request to a ...
Page 667
The recommended way of dealing with an abend on the target region is as follows: 1. Code your routing program so that, on each route selection (and route selection error) call, it specifies that it is to be reinvoked (for transaction initiation, termination, and abend) on the target region—see “invo...
Page 668
Important the same communications area is passed to both the distributed routing program and the dynamic routing program. Some parameters are meaningful to one routing program but not to the other. Some parameter-values may be passed to one routing program but never to the other. The following list ...
Page 669
Under the dyrtype parameter the value x'4' is not listed because it is never passed to the distributed routing programit occurs only on a program-link-related call to the dynamic routing program. If you use the same program as both a distributed routing program and a dynamic routing program, for des...
Page 670
Dyractid is the cics-assigned, 52-character activity identifier of the bts activity being routed. (when a process is being routed, dyractid returns the identifier of the root activity.) this field applies only to the routing of bts processes and activities. Dyractn is the name of the bts activity be...
Page 671
This field is not used by the distributed routing program. On invocation, it is set to 'n'. Dyrerror has a value only when dyrfunc is set to 1. It indicates the type of error that occurred during the last attempt at route selection. The possible values are: 0 the selected sysid is unknown. 1 the sel...
Page 672
Resource is unavailable on the target region. This error code may be set for program-link, link3270 bridge, and non-terminal-related start requests. Dyrfunc tells you the reason for this invocation of the distributed routing program. The possible values are: 0 invoked for route selection. This invoc...
Page 673
6 invoked because cics has finished trying (successfully or unsuccessfully) to route the request to the target region. This invocation occurs on the routing region. It signals that (unless the routing region and the target region are one and the same) the routing regions responsibility for this tran...
Page 674
Dyrnetnm is not used by the distributed routing program. On invocation, it is set to null characters. Note: to set the target region, the distributed routing program must use the dyrsysid field. Dyropter specifies whether the distributed routing program is to be reinvoked on the target region when t...
Page 675
Dyrproct is the process-type of the bts process to which the process or activity being routed belongs. This field applies only to the routing of bts processes and activities. Dyrprty is not used by the distributed routing program. On invocation, it is set to zeroes. Dyrqueue identifies whether or no...
Page 676
The distributed routing program can accept the value of dyrsysid or change it before returning to cics. If the sysid you return to cics is the same as the local sysid, cics executes the request on the local region. V when dyrfunc is set to 1 (route selection error), dyrsysid contains the cics region...
Page 677
Note that this is the name by which the transaction is known in the routing region. Unlike the dynamic routing program, the distributed routing program: 1. Is passed the local, not the remote, transaction name 2. Cannot specify an alternative remote transaction name, for forwarding to the target reg...
Page 678
V for non-terminal-related start requests, dyruserid contains: – the userid specified on the userid option of the exec cics start command, or – if userid is not specified, the userid under which the transaction that issued the start command is running. By examining this field when it is invoked for ...
Page 679
Note: a sample definition is provided for dfhdsrp, but you must install a new resource definition for a customized distributed routing program. Distributed transaction routing sample programs the cics-supplied sample distributed routing program is named dfhdsrp. The corresponding copy book that defi...
Page 680
658 customization guide.
Page 681
Chapter 19. Writing a cics–dbctl interface status program considerations common to all user-replaceable programs note that the comments contained in chapter 5, “general notes about user-replaceable programs,” on page 435 apply to this chapter. The cics–dbctl interface status program dfhdbuex is a us...
Page 682
Dbudisc (x'02') disconnected. Dbureas reason for disconnection. Contains flags: dbumenu (x'01') disconnected from menu dbudbcc (x'02') checkpoint freeze input to dbctl dbudraf (x'03') dra failure has taken place dbudbcf (x'04') dbctl failure has taken place. Dbusuff dra startup table suffix. Dbudbct...
Page 683
Chapter 20. Writing a 3270 bridge exit program considerations common to all user-replaceable programs note that the comments contained in chapter 5, “general notes about user-replaceable programs,” on page 435 apply to this chapter. The 3270 bridge provides an interface so that you can run 3270-base...
Page 684
662 customization guide.
Page 685
Chapter 21. Writing a security exit program for iiop considerations common to all user-replaceable programs note that the comments contained in chapter 5, “general notes about user-replaceable programs,” on page 435 apply to this chapter. Incoming requests using the internet inter-orb protocol (iiop...
Page 686
* 1–character reserved field piiopdata contains the address of the first megabyte of the unconverted iiop buffer. If the incoming request is fragmented, this field contains a pointer to: v the first megabyte of the first fragment, if the first fragment is greater than 32k v a 32k buffer containing d...
Page 687
Sslclientuserid 1–byte field showing the derivation of the user id if ssltype clientauth is specified in the tcpipservice definition, where: 0 user id set from dfltuser 1 user id set from ssl certificate * 2–byte reserved field return_code contains the return code. Reason_code contains the reason co...
Page 688
If you write your own security exit program, it should return all fields other than userid and return_code unchanged, or unpredictable results will occur. Dfheburm dfheburm is for use with the ejb bank account sample program. It alters the user id under which the sample runs from the default cics us...
Page 689
Chapter 22. Writing programs to customize jvms this chapter describes how to write programs to customize a java virtual machine (jvm). The normal way to customize jvms is by specifying options in the jvm profile, and system properties in the jvm properties file. There are three additional ways to cu...
Page 690
For a jvm to use an output redirection class that you have modified or written, the class must be present in a directory on an appropriate class path in the jvm profile or properties file. The directory containing the jar file for the sample output redirection class is automatically included on an a...
Page 691
By one provided in a subclass. It does not implement a writerecord method, and such a method must be provided by any subclass to control the output redirection process.You could imitate this in your own class structure. The initialization of output redirection can also be performed using a construct...
Page 692
The sample classes trap all errors in this way, this means that the calling programs do not need to handle any exceptions thrown by the output redirection class. You can use this method to avoid making changes to your calling programs. Be careful that you do not send the output redirection class int...
Page 693
Cics checks the length of the runtime options before passing them to language environment. If the length is greater than 255 bytes, cics does not attempt to start the jvm. Error messages are written to csmt in this case. Note that the values you specify are not checked by cics before being passed to...
Page 694
You cannot call dfhjvmat for a continuous jvm, that is, with a jvm profile that specifies reuse=yes (for example, the default cics-supplied jvm profile, dfhjvmpr). If you specify invoke_dfhjvmat=yes for this type of jvm, then invoke_dfhjvmat=yes is ignored and dfhjvmat is not called. The values spec...
Page 695
1. Except where explicitly stated as being for information only, you can reset the values of these variables. 2. All environment variables and values are case sensitive, and should be set as shown. 3. Cics ignores any values that it does not recognize as a valid option. 4. For the options beginning ...
Page 696
Table 34. Jvm profile options available to dfhjvmat (continued) option specifies xrs reduces the use of operating system signals by the jvm xrundllname loads the specified dynamic link library (dll) and passes it the specified options xss size of stack for each new java thread xverify level of verif...
Page 697: Of Enterprise Beans
Chapter 23. Writing a distinguished name program for clients of enterprise beans considerations common to all user-replaceable programs note that the comments contained in chapter 5, “general notes about user-replaceable programs,” on page 435 apply to this chapter. Use the distinguished name user-r...
Page 698
Ejdn_common_name_ptr a pointer to the proposed common name of the client, derived from the username associated with the client’s userid in the external security manager’s database. Ejdn_common_name_len a binary fullword containing the length of the client’s common name. Ejdn_title_ptr a pointer to t...
Page 699
Sample programs and copy books the default distinguished name program is an assembler-language program named dfhejdnx. The source of the default program is provided in assembler-language and c. The corresponding copy book that defines the communications area is provided in assembler-language, c, cob...
Page 700
678 customization guide.
Page 701
Chapter 24. Writing an ejb event program you can write your own ejb event program or use the program provided with cics, dfhejep. You must be familiar with the methods of defining corbaserver and djar resources and know how to deploy enterprise beans, as described in java applications in cics. The r...
Page 702
The dfhejep communications area the dfhejep communications area is mapped by the ejev_commarea dsect, which is supplied in the dfhejeph copybook. The information passed in the communications area is as follows: ejev_beanname the 240-byte name of the bean involved in this event. For some events (for ...
Page 703
Event codes table 36 shows the codes and meanings of all ejb events that may be passed to the ejb event program. Table 36. Ejb event codes. The table shows the event type and meaning of each event code. The “bean name” column indicates whether the ejev_beanname field in the dfhejep communications ar...
Page 704
Table 36. Ejb event codes (continued). The table shows the event type and meaning of each event code. The “bean name” column indicates whether the ejev_beanname field in the dfhejep communications area contains the name of an enterprise bean. The “djar name” column indicates whether the ejev_djar fi...
Page 705
Table 37. Ejb event programs and copy books (continued) language member name library copy books: v assembler v c v cobol v pl/i v dfhejepd v dfhejeph v dfhejepo v dfhejepl v sdfhmac v sdfhc370 v sdfhcob v sdfhpl1 you can use the supplied program as the basis of your own ejb event program. Your progr...
Page 706
684 customization guide.
Page 707
Chapter 25. Writing programs to customize language environment run-time options for xplink programs considerations common to all user-replaceable programs note that the comments contained in chapter 5, “general notes about user-replaceable programs,” on page 435 apply to this chapter. This chapter d...
Page 708
686 customization guide.
Page 709
Part 4. Customizing the xrf overseer program © copyright ibm corp. 1977, 2011 687.
Page 710
A general note about user-written programs: on return from any user-written program, cics must always receive control in primary-space translation mode, with the original contents of all access registers restored, and with all general purpose registers restored (except for those which provide return...
Page 711
Chapter 26. The extended recovery facility overseer program the information in this chapter is of interest only to users of the extended recovery facility (xrf). Details of xrf are provided in the cics/esa 3.3 xrf guide. The xrf overseer program has two major functions: v to display the current stat...
Page 712
End to terminate the sample program open to ask the overseer to try to open cics availability manager (cavm) data sets that it has previously failed to open. The full format of the operator command entered at the mvs console is: modify overseer-jobname,command-identifier where “command-identifier” i...
Page 713
Takeover. That system is the current active, and the information displayed for the alternate is marked as old until a new alternate is signed on and running normally. An example of the status display is shown, for guidance purposes, in the cics operations and utilities guide. Note: an ‘x’ following ...
Page 714
Active-alternate pairs are not to be automatically restarted in place, regardless of whether restart processing is enabled or disabled. This is described in “how to tell the overseer which actives and alternates to monitor” on page 693. The restart command works like an on/off switch. Restart in pla...
Page 715
This problem arises only if the overseer is initialized before all the cavm data sets have been formatted. If it occurs, the operator can use the open command (see open ) to retry the opening of those cavm data sets on which the open previously failed. The overseer retries an open only if the previo...
Page 716
The sample overseer program reads the dfhosd records in key sequence and builds a table of entries. Each active-alternate pair is known by its generic applid on this data set. Every entry on the data set contains the following information: v a 12-byte key field, containing the 4-byte value ‘gnbb’ fo...
Page 717
2 the last three entries are for three related mro regions that are identified by the related system name of mrosys. One of these is not allowed to restart in place and is indicated by the letter n. The dfhwosm macros the dfhwosm macros invoke the cics module dfhwos to provide services to the overse...
Page 718
By the overseer program and passed back to dfhwos as input to the open, close, read, qjjs, and term macros. Dfhwosm func=build macro the dfhwosm func=build macro must be issued by the overseer program to initialize its communication with dfhwos. No other macro can be issued by the overseer program u...
Page 719
Dfhwosm func=dsect macro the dfhwosm func=dsect macro generates a number of dsects, including the dsect of the dblid definitions. Dfhwosm func=jjc macro the dfhwosm func=jjc macro issues a jes cancel for a named job with a jes job identifier. Input the parm value is a pointer to the addresses of the...
Page 720
For func=qjjs, the parm value is a pointer to the addresses of the following: v an 8-byte job name v an 8-byte jes job id v a 256-byte ssob return area v a doubleword area to hold two ecbs. The func=qjjs macro requires 2 ecbs: the first is posted when the jes call completes; the second is posted if ...
Page 721
8 access already initialized for this generic applid or for this ddname 9 version numbers of the named cavm data sets do not match c data set open failure 10 showcb failure. A register 15 return code value of ‘0’ through ‘5’ indicates that a dfhwosm func=read macro can now be issued. A return code v...
Page 722
Input the parm value is a pointer to a parameter list that contains the addresses of the generic applid and the “dbllist”. The dbllist is a list of one or more doublewords. In the first two bytes of the second word of each of these doublewords you supply the dblid of the information you require. Eac...
Page 723
Note: 1. The data structures of the status information pointed to by items x'0024' and x'0124' are provided in dsect dfhxrhds of cicsts32.Cics.Sdfhmac. 2. The data structures of the status information pointed to by items x'0025' and x'0125' are provided in dsect dfhxrgds of cicsts32.Cics.Sdfhmac. 3....
Page 724
0 read successful, active and alternate signed on 1 read successful, active signed on 2 read successful, alternate signed on. 3 read successful, nothing signed on 4 same smf mvs name; ipl time of active earlier than mvs ipl time 5 same smf mvs name; ipl time of alternate earlier than mvs ipl time 8 ...
Page 725
Dfhwosm func=term macro the dfhwosm func=term macro terminates communication between the overseer program and dfhwos, and releases any associated storage. It must be issued before the overseer program completes to ensure an orderly termination. Input the token value is the build token. Output regist...
Page 726
The associated dsects are provided in member dfh$xrds of cicsts32.Cics.Sdfhsamp. There are several ways in which you can change the supplied code to make the overseer program more suitable for your installation. Here are some customization suggestions: v if the supplied display of status information...
Page 727
User exit program to request a cics abend, and thereby initiate a takeover, and for the overseer program to issue the perform takeover command while acting on the same information. – at particular times of the day, perhaps when fewer operational staff are available than at other times, you may find ...
Page 728
Link-edit job step requires the entry name dfhxrona. If you change any of the dsects used by the sample overseer program, you should reassemble the four modules. 706 customization guide.
Page 729
Part 5. Cics journaling, monitoring, and statistics © copyright ibm corp. 1977, 2011 707.
Page 730
A general note about user-written programs: the following comment applies to all user-written programs mentioned in part 5 of this book: v upon return from any user-written program, cics must always receive control in primary-space translation mode, with the original contents of all access registers...
Page 731
Chapter 27. Cics logging and journaling this chapter is divided into the following sections: 1. “the cics log manager” 2. “log stream storage” 3. “enabling, disabling, and reading journals” on page 711 4. “structure and content of compat41-format journal records” on page 729 5. “format of journal re...
Page 732
Data sets managed by the storage management subsystem (sms). Each log stream, identified by its log stream name (lsn), is written to its own log data sets. 3. Tertiary storage—a form of archive storage, used as specified in your hierarchical storage manager (hsm) policy. Optionally, older records ca...
Page 733
Enabling, disabling, and reading journals journal records are written to a log stream either directly from a user application program, or from a cics management program on behalf of a user application. Journal records can be written from a user application using the exec cics write journalname comma...
Page 734
Reading journal records offline access to journaled data in log streams is provided through an mvs subsystem interface (ssi), logr. Your existing user programs can read the general log streams, providing you specify, in your batch job jcl, the subsys parameter and supporting options on the dd for lo...
Page 735
System logs are always presented in cics transaction server for z/os format.. Each general log comprises a stream of contiguous blocks of journaled data. Each block comprises a block header followed by a variable number of cics journal records. Each cics journal record comprises a record header foll...
Page 736
Lgbh_global_info 8-bytes containing '>dfhtrnn', where: t = log type r = reserved nn = block version number lgbh_generic_applid 8-byte cics applid. Lgbh_start_gmt 8-byte start time (gmt). Lgbh_start_local 8-byte start time (local). Lgbh_block_number 8-byte sequence number. Format of general log journ...
Page 737
Glrh_record_length 4-byte record length. Glrh_header_length 4-byte header length. Glrh_rec_data_len 4-byte record data length. Glrh_gmt 8-byte time (gmt). Glrh_local 8-byte time (local). Glrh_tran_id 4-byte transaction identifier. Glrh_task_id 4-byte task identifier. Glrh_term_id 4-byte terminal ide...
Page 738
Start of task indicator 1-byte which may contain: x’8n’ equivalent to jcspsotk (start of task) x’4n’ equivalent to jcsplstk (start of uow) reserved 3-byte reserved field. The caller data differs depending on the cics component issuing the record, and on the function being journaled. Start-of-run rec...
Page 739
Journal records can be written by any of the following cics components: the logger, journal control (in the case of a request issued by a user), file control, the front end programming interface (fepi), and terminal control. The field glrh_rec_compid in the record header tells you which component ha...
Page 740
Some records have a third and fourth section which are of variable length. Table 38 outlines the sections in a journal record written by file control. Table 38. Fljb sections in journal records issued by file control record type first section second section third section fourth section read-only rea...
Page 741
Fljb_general_data 12-byte general data. Fljb_common_data 16-byte common data. Fljb_cd_key variable-length caller data key. Fljb_cd_data variable-length caller data. The format of the fljb_general_data section is shown in figure 79. Fljb_record_type 1-byte record type: x’80’ readonly x’81’ read updat...
Page 742
Fljb_file_name 8-byte file name. Reserved 2-byte reserved field. The format of the fljb_common_data section is shown in figure 80. Fljb_cd_base_esds_rba 4-byte relative byte address of record in base data set for esds (0 if file does not refer to esds, or if is an extended addressing esds). Fljb_cd_...
Page 743
Write-delete record types there are four sections in the journal records written for write-delete record types: v the fljb_general_data section, v the fljb_write_delete_data section, and v the two caller data image sections, which consist of: – fljb_wdd_base_key (the length of which is given by fljb...
Page 744
Fljb_wdd_base_esds_rba 4-byte relative byte address of record in base data set for esds (0 if file does not refer to esds, or if it is an extended addressing esds). Fljb_wdd_base_key_length 2-byte base key length. (the key length is 4 for an rrds, a vrrds, or a standard esds; 8 for an extended addre...
Page 745
Fljb_general_data 12-byte general data section. Fljb_close_data 28-byte close data section. See figure 79 on page 719 for the format of the fljb_general_data section. The format of the fljb_close_data section is shown in figure 84. Fljb_fcd_fwdrecovlog_name 26-byte log stream name of the forward rec...
Page 746
Tie-up record types there are two sections in the journal records written for tie-up record types: v the fljb_general_data section v the tie_up_record_data section. The format of such a record written for tie-up record types is shown in figure 85. Fljb_general_data 12-byte general data. Tie_up_recor...
Page 747
Fljb_tur_base_ci_size 4-byte ci size of base data set. 4 4 4 2 1 1 26 2 44 44 2 fljb_ tur_ bits fixed length fixed length fixed length fixed length log stream name of forward recovery log fljb_tur_fwdrecovlog_name fljb_tur_path_dsname fljb_tur_base_dsname fljb_tur_base_dsname_length fljb_tur_record_...
Page 748
Fljb_tur_maximum_lrecl 4-byte maximum record length. Fljb_tur_base_key_position 4-byte base key position in record. Fljb_tur_base_key_length 2-byte base key length. Fljb_tur_dataset_type 1-byte data set type: x’c5’ standard esds x’d2’ ksds x’d7’ path x’d9’ rrds x’e5’ vrrds x’e7’ extended esds fljb_t...
Page 749
Function id 1-byte function identifier. Module id 1-byte module identifier. Inbound vtam sn 2-byte inbound vtam sequence number. Outbound vtam sn 2-byte outbound vtam sequence number. Jcaup tid 4-byte terminal identifier (padded with blanks if unused). Fepi prefix data each fepi journal record conta...
Page 750
Up_modfn 1-byte module function up_svmid 1-byte module identifier up_fepdf 1-byte data function up_fepes 1-byte escape character for keystroke reserved 2-byte reserved field up_feppl 8-byte pool name up_feptg 8-byte target name up_fepcv 8-byte conversation identifier reserved 4-byte reserved field f...
Page 751
Structure and content of compat41-format journal records smf records the following description does not apply to journal records written to an smf data set. These are described on page “format of journal records written to smf” on page 737. Cics allows you to format journal records so that they are ...
Page 752
The label header part of the journal control label header is 10 bytes long, and its format is shown in figure 91. Jcrll 2-byte length of record. X'0000' 2-bytes containing x'0000'. 32 fixed length label prefix label header 10 4 length of block not presented unless the caller is reading data blocks r...
Page 753
Jcrstrid 2-byte system-type identifier. For a user journal request, this is x'0000'. Otherwise, it consists of a 1-byte function id followed by a 1-byte module id. Jcrutrid 2-byte user-type identifier. For a cics journal request, this is x'0000'. Otherwise, it contains the code specified by the jtyp...
Page 754
The system header is 10 bytes long. Its format is shown in figure 94. Jcrll 2-byte length of record. X'0000' 2-bytes containing x'0000'. Jcrstrid 2-byte system-type identifier. For a user journal request, this is x'0000'. Otherwise, it consists of a 1-byte function id followed by a 1-byte module id....
Page 755
Jcrutrid 2-byte user-type identifier. For a cics journal request, this is x'0000'. Otherwise, it contains the code specified by the jtypeid keyword of the user request. Jcrlrn 2-byte record number within the block. The field jcrstrid (the system-type id) and the field jcrutrid (the user-type id) in ...
Page 756
Reserved 2-byte reserved field. Jcspf1 1-byte flag field: x’01’ user prefix present x’02’ physical start-of-task, jcspsotk x’04’ logical start-of-task, jcsplstk jcsptask 3-byte task number. Jcsptime 4-byte time of request. Jcsptran 4-byte transaction identifier. Jcspterm 4-byte terminal identifier. ...
Page 757
Jcrll - (system header (10) bytes + jcspll + user prefix) not all journal records contain journaled data. The cics components that issue journaling requests are journal control, file control, fepi, and terminal control. Chapter 27. Cics logging and journaling 735.
Page 758
*********************************************************************** * * f u n c t i o n i d e n t i f i e r s * * *********************************************************************** * * * x’20’ plus x’8-’ ...Use for automatic journaling * * x’40’ plus x’8-’ ...Use for automatic logging * ***...
Page 759
Note: 1. Records created by automatic journaling and automatic logging are identified by values of x'20' (fidajrn) and x'40' (fidalog) respectively, added to the “base” value of the function identifier. 2. A file control write-delete record created by the forward recovery process (where the write-de...
Page 760
Journal records written to smf can be read offline by user-written programs. Such programs can map journal records by including an include dfhlgmsd statement. This generates the assembler version of the dsect. The smf block header this block describes the system creating the output. Its format is sh...
Page 761
The format of the smf block header is: smfh_length 2-byte record length. Smfh_seg 2-byte segment descriptor (x'0000'). Smfh_flg 1-byte operating system indicator. Smfh_rty 1-byte record type. Smfh_tme 4-byte (local) time record moved. Smfh_dte 4-byte date record moved. Smfh_sid 4-byte system id. Smf...
Page 762
Smfh_nps 2-byte number of cics product section. Smfh_ass 4-byte offset to cics data section. Smfh_asl 2-byte length of cics data section. Smfh_asn 2-byte number of cics data sections. Note: cics sets only the subsystem-related bits of the operating system indicator flag byte in the smf header (smfh_...
Page 763
The format of the cics product section is: smfps_vrm 2-byte cics version, release, and modification information, in the format x'0vrm'. Smfps_prn 8-byte product name (generic applid). Smfps_spn 8-byte product name (specific applid). Smfps_mfl 2-byte record maintenance indicator. Reserved 54-byte res...
Page 764
Smfps_jnm 8-byte journal name. Smfps_jbn 8-byte job name. Smfps_rsd 4-byte job date. Smfps_rst 4-byte job time (local). Smfps_uif 8-byte user id. Smfps_pdn 8-byte operating system product-level. The cics data section this section contains a variable number of cics journal records. Each record compri...
Page 765
Chapter 28. Cics monitoring this section describes the monitoring facilities of cics transaction server for z/os, version 3 release 2, and tells you how to: v control the types of monitoring data collected by cics. V gather more performance data about specific transactions than is provided automatic...
Page 766
Or when there is an immediate shutdown of cics, the transaction resource records are not written to smf and the data is lost. Exception records are passed directly to smf when the exception condition completes. Each exception record describes one exception condition. You can link performance records...
Page 767
Invoked, displays a menu screen from which the user can choose a specific application. It is then possible to run all the elements of the application under the common menu transaction id. This is very effective from the application users point of view, because they do not have to use a large number ...
Page 768
This example shows 4 bytes of user data, typically the transaction id, being moved using the dfhappl.1 emp. The data starts at offset 0, and the data length defaults to the length specified in the application naming emp in the mct. In this example, cics monitoring domain uses the default length defi...
Page 769
The monitoring control table (mct) you can use the monitoring control table (mct): v to tell cics about the emps that are invoked by your application programs and about the data that is to be collected at these points. The dfhmct type=emp macro can do this. V to tell cics that you want specific syst...
Page 770
Dfhmct type=emp there must be a dfhmct type=emp macro definition for every user-coded emp. The perform operand of the dfhmct type=emp macro tells cics which user count fields, user clocks, and character values to expect at the identified user emp, and what operations to perform on them. The dfhmct t...
Page 771
Example 1: starting a user clock example 1 shows a user clock being started by an application that is identified as prog3. This is the eleventh emp in this application. To prevent confusion with the eleventh emp in another application, this emp is uniquely identified by the empid prog3.11. The clock...
Page 772
The dbctl data recorded by these event monitoring points can be mapped using the ims macro dfsdsta dsect=yes, which is available in the ims genlibs. For more information about monitoring in dbctl, see the cics ims database control guide. Cics monitoring record formats this section describes the form...
Page 773
The label ‘mnsmfds’ is the default dsect name, and smf is the default prefix value, so you could also generate the dsect simply by coding: dfhmnsmf the mnsmfds dsect has the format shown in figure 105 on page 752. Chapter 28. Cics monitoring 751.
Page 774
Note: 1. Cics sets only the subsystem-related bits of the operating system indicator flag byte in the smf header (smfmnflg). Smf sets the remainder of the byte according to the operating system level and other * start of the smf header * mnsmfds dsect smfmnlen ds xl2 record length smfmnseg ds xl2 se...
Page 775
Factors. For an explanation of the setting of the other bits, refer to the z/os mvs system management facilities (smf) manual. 2. Fields smfmndca smfmndcl, and smfmndcn apply to performance class records only. 3. For dictionary class monitoring records (described in “dictionary data sections” on pag...
Page 776
Cics data section the cics data section can be made up of a dictionary data section, a performance data section, an exception data section, or a transaction resource data section. You can identify which of these you are dealing with by looking at the value of field smfmncl in the smf product section...
Page 777
Whenever the monitoring of performance class data is switched on, whether at cics initialization or while cics is running, a dictionary data section is written. So, if the monitoring of performance class data is switched on and off three times during a single cics run, there are three separate, but ...
Page 778
C byte-string p packed decimal number s clock t time stamp 756 customization guide.
Page 779
Field-name size connector offset nickname dfhtask c001 4 x’0001’ x’0000’ tran dfhterm c002 4 x’0002’ x’0004’ term dfhcics c089 8 x’0003’ x’0008’ userid dfhtask c004 4 x’0004’ x’0010’ ttype dfhcics t005 8 x’0005’ x’0014’ start dfhcics t006 8 x’0006’ x’001c’ stop dfhtask p031 4 x’0007’ x’0024’ trannum...
Page 780
Field-name size connector offset nickname dfhstor a106 4 x’004b’ x’0314’ scusrhwm dfhstor a116 4 x’004c’ x’0318’ sc24chwm dfhstor a119 4 x’004d’ x’031c’ sc31chwm dfhstor a095 8 x’004e’ x’0320’ scusrstg dfhstor a107 8 x’004f’ x’0328’ scusrstg dfhstor a118 8 x’0050’ x’0330’ sc24cocc dfhstor a121 8 x’0...
Page 781
Field-name size connector offset nickname dfhtask a346 4 x’0086’ x’0410’ icstrcct dfhtask a347 4 x’0087’ x’0414’ icstrcdl dfhsync a060 4 x’0088’ x’0418’ spsyncct dfhcics a025 4 x’0089’ x’041c’ cfcapict dfhfepi a150 4 x’008a’ x’0420’ szalloct dfhfepi a151 4 x’008b’ x’0424’ szrcvct dfhfepi a152 4 x’00...
Page 782
Field-name size connector offset nickname dfhsock a298 4 x’00c2’ x’0500’ sototct dfhsock a301 4 x’00c3’ x’0504’ somsgin1 dfhsock a302 4 x’00c4’ x’0508’ sochrin1 dfhsock a303 4 x’00c5’ x’050c’ somsgou1 dfhsock a304 4 x’00c6’ x’0510’ sochrou1 dfhdata a179 4 x’00c7’ x’0514’ imsreqct dfhdata a180 4 x’00...
Page 783
Performance data sections each performance data section is made up of a string of field connectors, followed by one or more performance data records. All of the performance records produced by a single cics run have the same format. The default length of the performance records is given in the topic...
Page 784
Performance records changes if you add user data at user event monitoring points (emps), or if you exclude any system-defined data from the monitoring process. All of the system-defined data fields in the performance records are described in performance class data: listing of data fields , in the ci...
Page 785
Figure 114 illustrates the relationship between the dictionary record, the field connectors, and the performance records. How the string of field connectors is constructed when cics is initialized, a unique connector value is assigned to every dictionary entry. Cics then examines the mct entries for...
Page 786
Record type, and they do not change between cics runs. There is more information about field identifiers in the cics resource definition guide. Field offsets in the performance record allow you to build a table for fast selection of required fields in your monitoring data processing programs. Except...
Page 787
For further information about exception class data, see exception class data, in the cics performance guide, which lists all the system-defined data that can be produced by cics monitoring. Transaction resource data sections each transaction resource data section is made up of one or more transactio...
Page 788
Queues for which resource data can be collected for any one transaction. For example, if you specify file=10 in the dfhmct type=initial macro, the file resource data section can have up to 960 bytes of file resource data. All the system-defined data fields in the transaction resource monitoring reco...
Page 789
Dfhmnrds dsect , transaction resource monitoring record mnr_length ds h length of resource data mnr_id_equate equ 79 monitoring domain id mask mnr_id dc al2(mnr_id_equate) monitoring domain id mnr_version equ x’02’ dsect version mask mnr_dsect_vers ds cl1 dsect version number ds cl3 reserved * mnr_h...
Page 790
Mnr_id_acmeth_tcam equ x’04’ tcam/dcb (supported for remote terminals only) mnr_id_acmeth_bgam equ x’06’ bgam mnr_id_acmeth_console equ x’07’ console mnr_id_devcode ds xl1 device type code * see typeterm rdo attribute mnr_id_termcnnm ds cl4 terminal connection name mnr_id_res_flags ds 0xl4 resource ...
Page 791: Programs
Chapter 29. Writing statistics collection and analysis programs this chapter describes how you can customize the collection and analysis of cics statistics. It is divided into the following sections: 1. “writing a program to collect cics statistics” describes how user programs can use exec cics comm...
Page 792
Resetting statistics counters statistics counters are reset in the following circumstances: v at cics startup v when interval statistics are written (but not when an interval occurs and no statistics are written) v at end of day v when requested reset statistics are written. However, you can cause s...
Page 793
V dfh0stgn v dfh0stlk v dfh0stpr v dfh0stsy v dfh0sttp v dfh$stas v dfh$stcn v dfh$sttb the sample programs produce a report showing critical system parameters from the cics dispatcher, together with loader statistics and an analysis of the cics storage manager. Dfh$stas, dfh$stcn, and dfh$sttb are ...
Page 794
Note: 1. Cics sets only the subsystem-related bits of the operating system indicator flag byte in the smf header (smfstflg). Smf sets the remainder of the byte according to the operating system level and other factors. For an explanation of the setting of the other bits, refer to the z/os mvs system...
Page 795
3. Fields smfstint and smfstino are only relevant if smfstrqt is ‘int’. Otherwise both values should be ignored. 4. For ts data sharing, the record subtype is x'0003' and certain fields are not set or are used in a different way. Smfstprn and smfstspn contain the server prefix (dfhxq) and the pool n...
Page 796
Figure 124 on page 775. For further guidance information about the fields within the statistics data records, see cics statistics in dsects and dfhstup report, in the cics performance guide. Stivers takes the value ‘1’ for this release of cics. 774 customization guide.
Page 797
Stid stid symbolic value copy book type of record name stismd 5 dfhsmdds storage mgr domain subpool id stismt 6 dfhsmtds storage manager task subpool id stixmg 10 dfhxmgds transaction manager (globals) id stixmr 11 dfhxmrds transaction manager (trans) id stixmc 12 dfhxmcds transaction manager (tclas...
Page 798
The ts data sharing statistics use no symbolic names, but relate to the stid values as follows: the coupling facility data table server statistics use no symbolic names, but relate to the stid values as follows: the named sequence number server statistics use no symbolic names, but relate to the sti...
Page 799
Processing the output from cics statistics there are several utilities to help you process statistics output: the cics-supplied dfhstup program for information about how to run dfhstup, refer to the cics operations and utilities guide. For information about how to interpret the report produced by df...
Page 800
778 customization guide.
Page 801
Part 6. Customizing cics compatibility interfaces © copyright ibm corp. 1977, 2011 779.
Page 802
A general note about user-written programs: the following comment applies to all user-written programs mentioned in part 6 of this book: v upon return from any customer-written program, cics must always receive control in primary-space translation mode, with the original contents of all access regis...
Page 803
Chapter 30. The dynamic allocation sample program this chapter suggests ways in which you can customize the dynamic allocation sample application program, used to allocate or deallocate data sets dynamically. It is divided into the following sections: 1. “overview of the dynamic allocation program” ...
Page 804
The application uses a 3270 display screen terminal, and adjusts its formatting to suit the screen size. Bms is not required. The program is designed so that the installation can easily modify the functions supported to suit installation standards. Installing the program and transaction definitions ...
Page 805
Containing “?” is entered, no dynalloc svc is issued. “?” is recognized only in the positions specified above; the rest of the command is ignored. The dynamic allocation program—values values are classified as follows: keyword value keyword values must be specified for some keywords. For example, th...
Page 806
The dynamic allocation sample program does not support negative numbers. It does not cross-check operand keywords; errors of this type usually cause dynalloc to return error codes of the form 03xx. Abbreviation rules for keywords keywords can be abbreviated. A word in the command matches a keyword i...
Page 807
Following successful tokenizing, the main program calls dfh99fp to analyze the verb keyword. Dfh99fp calls dfh99lk to look up the verb keyword in the table, dfh99t. Dfh99lk calls dfh99mt if an abbreviation is possible. Upon finding the matching verb, dfh99fp puts the address of the operand section o...
Page 808
At the end of processing the command, the main program calls dfh99mp with no parameters, which causes it to send the output buffer to the terminal, and initialize it to empty. 786 customization guide.
Page 809
Part 7. Customizing cics security processing © copyright ibm corp. 1977, 2011 787.
Page 810
General notes: the following comments apply to the chapters in part 7 of this book: v the only aspects of cics security processing covered are: – invoking a user-written external security manager. – writing a “good night” transaction. Customization of password expiry templates for http basic authent...
Page 811
Chapter 31. Invoking an external security manager cics provides an interface to an external security manager (esm), which may be the resource access control facility (racf), a vendor product, or user-written. This chapter gives an overview of the cics-esm interface, and describes how you can use the...
Page 812
You can use the router exit to pass control to your own esm. If you do use racf, you could use the exit for preprocessing before racf is invoked. The mvs router exit routine is invoked whenever cics (or another component of your system) issues a racroute macro. The router passes a parameter list (ge...
Page 813
Table 44. Mvs router exit return codes code meaning 0 the exit has completed successfully. Control proceeds to the racf front-end routine for further security processing and an invocation of racf. C8 the exit has completed successfully. The mvs router translates this return code to a router return c...
Page 814
For non-racf users — the esm parameter list cics (or another caller) passes information to your external security manager in the esm parameter list, the address of which can be calculated using field safpracp of the mvs router parameter list. When the caller is cics, the “instln” field of the esm pa...
Page 815
Table 46. Obtaining the address of the installation data parameter list (continued) racroute request type racf exit exit list mapping macro parameter list field name extract not available not available none note: 1. The “xxxinstl” field points to the installation parameter list only if you specify i...
Page 816
Default_sign_on (x'01') signon of default userid preset_sign_on (x'02') signon of preset security terminal irc_sign_on (x'03') link signon for irc (mro) links lu61_sign_on (x'04') link signon for lutype6.1 links lu62_sign_on (x'05') link signon for appc links xrf_sign_on (x'06') xrf tracking of sign...
Page 817
Link_command_check (x'51') command checking for link edf_command_check (x'52') command checking for edf user_resource_check (x'60') resource checking for user link_resource_check (x'61') resource checking for link edf_resource_check (x'62') resource checking for edf user_surrogate_check (x'68') surr...
Page 818
Uxplunam address of an area containing the vtam lu name. The address may be zero if no terminal is associated with the request, or the area may be blank if the terminal is not a vtam terminal. Uxptctua address of the tct user area. Uxptctul address of a fullword containing the length of the tctua. U...
Page 819
V when an invalid password, or a passticket is presented, or an exec cics verify password command is issued. Racroute request=fastauth issued during resource checking, on behalf of a user who is identified by an acee. It is the high-performance form of request=auth, using in-storage resource profile...
Page 820
Cics defers the creation of the accessor environment element until the racroute request=verify macro with the envir=create option is issued to perform the normal verification routine. The envir=create version of the macro is issued by the security manager domain running in supervisor state. Cics pas...
Page 821
Using cics api commands in an early verification routine an early verification routine can use cics application programming interface (api) commands, provided it obeys the following interface rules: v the routine must be written in assembler. V entry to the routine must be via the dfheient macro, wh...
Page 822
800 customization guide.
Page 823
Chapter 32. Writing a “good night” program you can use the gntran system initialization parameter to specify a “good night” transaction that you want cics to invoke when a user’s terminal-timeout period expires. The default value for gntran is 'no', which means that cics does not schedule a “good ni...
Page 824
Gntran_start_transid the identifier of the transaction that started the “good night” transaction. If it was started by cics because of a terminal timeout, gntran_start_transid is set to 'cegn'. Your program should examine this field to check that timeout processing is appropriate (that is, that the ...
Page 825
Pseudoconversational sequence. (if the terminal did not time out during a pseudoconversational sequence, the value of this field is meaningless.) gntran_screen_length the length of the screen buffer. Gntran_cursor_position the cursor position. Gntran_screen_width the width of the screen in use when ...
Page 826
C. Writes the communication area, if any, to a temporary storage queue. D. Displays a screen asking the user to input his or her password, and sets the flag indicating that this has been done. E. Issues exec cics return with transid gnit and the commarea option, to continue the timeout process as a ...
Page 827
Logoff the terminal is both signed off and logged off. V specify the identifier (transid) of your “good night” transaction on the gntran system initialization parameter. If you have customized the sample program, dfh0gnit, specify the supplied sample transaction definition, gnit. If you have written...
Page 828
806 customization guide.
Page 829
Part 8. Examining and modifying resource attributes © copyright ibm corp. 1977, 2011 807.
Page 830
A general note about user-written programs: the following comment applies to all user-written programs mentioned in part 8 of this book: v upon return from any customer-written program, cics must always receive control in primary-space translation mode, with the original contents of all access regis...
Page 831
Chapter 33. Using the programmable interface to ceda this chapter describes a programmable interface to the resource definition online (rdo) transaction, ceda. The functions provided by rdo can be invoked from application programs, by a command such as: exec cics link program(’dfhedap’) commarea(ced...
Page 832
Request input from its associated terminal, whereas an automatically initiated transaction must first send data to the terminal. An attempt to start ceda under ceci by an exec cics start command fails for similar reasons. 2. The rdo command passed in address 1 of the cedaparm parameter list must be ...
Page 833
Be prevented by all dtp applications issuing a syncpoint request when they get into send state (on all of their sessions) and before they issue the link dfhedap command. Do not attempt to use link dfhedap when more than a pair of dtp application programs are involved—that is, one front end and one b...
Page 834
812 customization guide.
Page 835: Program (Dfhcsdup)
Chapter 34. User programs for the system definition utility program (dfhcsdup) this chapter tells you how to write programs for use with the cics system definition utility program (dfhcsdup). It is divided into the following sections: 1. “an overview of dfhcsdup” contains background information. 2. ...
Page 836
V as a batch program. The next section refers to this method. V from a user program running either in batch mode or in a tso environment. “invoking dfhcsdup from a user program” on page 821 describes this method. Invoking a user program from dfhcsdup this section refers to dfhcsdup as a batch progra...
Page 837
2. If you specify the objects option, all the attributes of the resource definitions are also extracted. Userprogram is the name of the user-written program that is to process the data retrieved by the extract command. You must supply a userprogram value. When the user program is invoked the user pr...
Page 838
8 keyword detail call 10 object end call 12 group end call 14 list end call 16 final call. Workarea ptr this is the address of a field containing the address of a fullword to be used by the user application to store the address of any user-acquired work area. Back translated command ptr the address ...
Page 839
Table 48. Sample extract user programs for the dfhcsdup utility program (continued) program names languages description dfh$fora dfh0forc dfh$forp assembler cobol pl/i formats the group or list of resource definitions you specify on the extract command into a form suitable for the db2 table load uti...
Page 840
The csd cross-referencing program the cics-supplied sample csd cross-referencing program produces a cross-reference listing of objects and keywords on the csd. The data gathered by the extract command is passed to the sample program, where it is saved in a cross-reference table. On the final call to...
Page 841
V for distribution, in part or as a whole, to other cics installations v to recreate or add resource definitions to any csd using dfhcsdup. The program must be run against an extract command of the form: extract group(group name) objects userprogram(program-name) or: extract list(list name) objects ...
Page 842
An assembler-language version the sample job in figure 129 shows the link-edit statements you need for an assembler-language version of a dfhcsdup user program. Notes for the assembler job: 1 specify the entry name as dfhextra, which is the entry name in the cics-supplied stub, dfhexai. (see 3.) 2 t...
Page 843
Notes for the language environment job: 1 specify the entry name as dfhextra, which is the entry name in the cics-supplied stub, dfhexle (see 3). 2 the cics-supplied stub, dfhexle, is generated with a link to the user program using a dummy csect name (exitep). Use the link-edit change statement to c...
Page 844
Message number ‘dfh5618’ to the put-message exit (see “the put-message exit” on page 827), where this is available, and also to the default output file: an attention interrupt was requested during dfhcsdup processing your put-message exit routine can terminate dfhcsdup, if desired. (note that you mu...
Page 845
Note that if you specify both replacement ddnames and replacement dcbs, the alternative dcbs are used, but the alternative ddnames are disregarded. Exits the addresses of a set of user exit routines to be invoked during processing of dfhcsdup. The structure of the parameter list is shown in figure 1...
Page 846
First three subentries of the ddnames parameter. The fourth, fifth, and sixth subentries, if present, replace the ddnames of dfhcsd, sysin, and sysprint, respectively. V in the dcbs functional data, each subentry consists of two fullwords. The first word is not used by cics. The second word contains...
Page 847
Dfhuexit dsect uepexn ds a address of exit number uepgaa ds a address of global area uepgal ds a address of global area length uepcrca ds a address of current return-code ueptca ds a address of tca uepcsa ds a address of csa uephmsa ds a address of save area used by host uepstack ds a address of ker...
Page 848
Uepcmda pointer to the address of a command. Uepcmdl address of a halfword containing the length of the command text. The maximum length that can be specified is 1536 bytes. Return codes uercnorm (x'00') continue processing. Uercdone (x'04') no more commands to process. (this is equivalent to reachi...
Page 849
Data is being extracted. This value is set on ‘group start’, ‘group end’, ‘object start’, ‘object end’, and ‘keyword’ calls. Extract_csd_object_type_ptr address of a 12-byte field that identifies the type of object (such as transaction, program, and so on). This value is set only on ‘object start’, ...
Page 850
Uepmdom reserved uepinsn address of a 2-byte field containing the number of insert fields uepinsa address of the following message structure: ds f reserved ins_1_text_ptr ds a address of insert 1 ins_1_len_ptr ds a address of a fullword containing the length of insert 1 ds f reserved ds f reserved i...
Page 851
Uercnorm (x'00') continue processing. Uercerr irrecoverable error. This causes dfhcsdup to terminate with a return code of ‘8’. Xpi calls must not be used. The sample program, dfh$cus1 the cics-supplied sample program, dfh$cus1, illustrates how dfhcsdup can be invoked from a user program. It is writ...
Page 852
830 customization guide.
Page 853: Part 9. Appendixes
Part 9. Appendixes © copyright ibm corp. 1977, 2011 831.
Page 854
832 customization guide.
Page 855
Appendix a. Coding entries in the vtam logon mode table this appendix shows you what to code in your vtam logon mode table for a terminal to be automatically installed. It is divided into the following sections: 1. “overview of the vtam logon mode table” 2. “typeterm device types and pointers to rel...
Page 856
Note that table 49 is a complete list of typeterm device types; not all of these can be used with autoinstall. Those that cannot are marked with an asterisk (*). For details about coding typeterm definitions, and for a list of terminals that can be autoinstalled, see the cics resource definition gui...
Page 857
Table 49. Typeterm device types, with cross-references to vtam logmode entries (continued) typeterm device type reference number in table 50 on page 836 device(3650) sessiontype(pipeln) * 21 device(3650) sessiontype(userprog) bracket(yes) 6 device(3650) sessiontype(userprog) bracket(no) 7 device(365...
Page 858
Table, such as pservic for some reference numbers, are not tested by cics. Any bit settings that do not matter to cics during bind analysis for autoinstalled terminals appear as periods (.). Note: some fields in the pservic data for lutype0, lutype2, and lutype3 devices have values that depend on th...
Page 859
Table 50. Logon mode table and istinclm entries (continued) rn vtam modeent macro entries that are needed for related cics typeterm definitions suitable supplied entries 7 fmprof=x’04’ tsprof=x’04’ priprot=x’b0’ secprot=x’30’ comprot=b’0100.000 00000.00’ 8 fmprof=x’03’ tsprof=x’03’ priprot=x’b1’ sec...
Page 860
Table 50. Logon mode table and istinclm entries (continued) rn vtam modeent macro entries that are needed for related cics typeterm definitions suitable supplied entries 14 fmprof=x’03’ tsprof=x’04’ priprot=x’b1’ secprot=x’b0’ comprot=b’0111.000 10000.00’ pservic=b’00000001 00110001 00011000 0100000...
Page 861
Table 50. Logon mode table and istinclm entries (continued) rn vtam modeent macro entries that are needed for related cics typeterm definitions suitable supplied entries 19 fmprof=x’03’ tsprof=x’03’ priprot=x’b1’ secprot=b’10..0000’ comprot=b’0011.000 10000.00’ pservic=b’00000011 10000000 00000000 0...
Page 862
Pservic screen size values for lutypex devices table 51 is to help you decide what screen size values you should specify on the pservic operand of the vtam modeent macro, for lutype0, lutype2, and lutype3 devices. If, on your cics typeterm definition, you code the values shown in columns 1 through 4...
Page 863
Table 52. Equivalent pservic screen size values (continued) bytes 20—24 of cics model bind valid screen size values on pservic definition xxxx 0000 7e plus, if xxxx=1850 0000 0000 00 xxxx 0000 7e 0000 0000 02 xxxx yyyy 7f 0000 0000 00 xxxx yyyy 7f where: xxxx indicates 2 bytes containing the default...
Page 864
Ati ==> yes tti ==> yes autoconnect ==> no logonmsg ==> yes bind sent by cics depends on pservic value on logmode definition above: either : 01020271 40200000 00000080 00000000 00000000 00000002 00009300 00300000 or : 01020271 40200000 00000080 00000000 00000018 502b507f 00009300 00300000 or : 01020...
Page 865
Terminal definition ************************* autinstname ==> m3770 autinstmodel ==> only group ==> pdatd typeterm ==> t3770 inservice ==> yes typeterm definition ************************* typeterm ==> t3770 group ==> pdatd device ==> 3770 sessiontype ==> batchdi pagesize ==> 12,80 discreq ==> yes a...
Page 866
Ati ==> yes tti ==> yes pagesize ==> 50,80 autopage ==> yes logonmsg ==> no ldclist ==> ldc1 needs ldc declaration in tct : ldcs dfhtct type=ldc,ldc=system ldc1 dfhtct type=ldc,local=initial dfhtct type=ldc,dvc=(blucon,01),profile=default,ldc=pc, pgesize=(50,80),pgestat=autopage dfhtct type=ldc,dvc=...
Page 867
Bracket ==> yes ioarealen ==> 256 ati ==> yes tti ==> yes bind sent by cics : 010404b1 b0708000 00858580 00000000 ****************************************************************** 6) 3790 batch data interchange ****************************************************************** s3790b modeent logmod...
Page 868
Autinstmodel ==> only group ==> pdatd typeterm ==> t3790c inservice ==> yes typeterm definition ************************* typeterm ==> t3790c note that ceda changes device=3790, group ==> pdatd sessiontype=scsprt to device=scsprint, device ==> 3790 sessiontype=blanks, printertype=3284. Sessiontype =...
Page 869
Terminal definition ************************* autinstname ==> m3650a autinstmodel ==> only group ==> pdatd typeterm ==> t3650a inservice ==> yes typeterm definition ************************* typeterm ==> t3650a group ==> pdatd device ==> 3650 sessiontype ==> userprog routedmsgs ==> specific fmhparm ...
Page 870
Tsprof=x’03’, priprot=x’b1’, secprot=x’90’, comprot=x’6000’ terminal definition ************************* autinstname ==> m3650b2 autinstmodel ==> only group ==> pdatd typeterm ==> t3650b2 inservice ==> yes typeterm definition ************************* typeterm ==> t3650b2 group ==> pdatd device ==>...
Page 871
Tsprof=x’07’, priprot=x’b0’, secprot=x’b0’, comprot=x’50b1’, psndpac=x’00’, srcvpac=x’00’, ssndpac=x’00’, rusizes=x’8585’, pservic=x’060200000000000000002c00’ terminal definition ************************* autinstname ==> mlu62 autinstmodel ==> only group ==> pdatd typeterm ==> sinlu62 inservice ==> ...
Page 872
Userarealen ==> 32 ati ==> yes tti ==> yes logonmsg ==> yes errhilight ==> blink receivesize ==> 1024 bind sent by cics : 010303b1 90308000 00878780 00028000 00000018 503ea07f 00000000 00000000 ****************************************************************** 15) 3601 with a 3604 attached *********...
Page 873
Dfhlu3 modeent logmode=dfhlu3, lu type 3 printer. Type=1, fmprof=x’03’, tsprof=x’03’, priprot=x’b1’, secprot=x’b0’, comprot=x’3080’, rusizes=x’8585’, pservic=x’038000000000000000000200’ dfhscsp modeent logmode=dfhscsp, lu type 1 scs printer type=1, fmprof=x’03’, tsprof=x’03’, priprot=x’b1’, secprot=...
Page 874
Dfhlu0m2 modeent logmode=d4b32782, lu0 model 2 nonqueryable fmprof=x’02’, tsprof=x’02’, priprot=x’71’, secprot=x’40’, comprot=x’2000’, rusizes=x’0000’, pservic=x’000000000000185000007e00’ dfhlu0m3 modeent logmode=d4b32783, lu0 model 3 nonqueryable fmprof=x’02’, tsprof=x’02’, priprot=x’71’, secprot=x...
Page 875
Dfhlu2m3 modeent logmode=d4a32783, lu2 model 3 nonqueryable fmprof=x’03’, tsprof=x’03’, priprot=x’b1’, secprot=x’90’, comprot=x’3080’, rusizes=x’87c7’, pservic=x’020000000000185020507f00’ dfhlu2m4 modeent logmode=d4a32784, lu2 model 4 nonqueryable fmprof=x’03’, tsprof=x’03’, priprot=x’b1’, secprot=x...
Page 876
854 customization guide.
Page 877: Program
Appendix b. Default actions of the node abnormal condition program this appendix describes the default actions of the node abnormal condition program, dfhznac. The actions vary, depending on the terminal error code and system sense codes received from vtam. In most cases, dfhznac issues messages and...
Page 878
Table 53. Messages issued and flags set by dfhznac for specific error codes (continued) error code symbolic label message action flags set x'20' tczvtami dfhzc2417 none x'21' tczlucf1 dfhzc4902 3 7 9 10 11 24 x'22' tczlucf2 dfhzc4903 3 7 9 10 11 24 x'23' tczfsmbe dfhzc4904 3 7 9 10 11 24 x'24' tczfs...
Page 879
Table 53. Messages issued and flags set by dfhznac for specific error codes (continued) error code symbolic label message action flags set x'49' tczclsin dfhzc3462 7 x'4a' tczopacb dfhzc3463 none x'4b' tczicput dfhzc2498 none x'4c' tczdspcl dfhzc3481 2 3 7 9 10 11 24 x'4d' tczslsrl dfhzc3473 none x'...
Page 880
Table 53. Messages issued and flags set by dfhznac for specific error codes (continued) error code symbolic label message action flags set x'75' tczsese1 dfhzc2424 3 7 9 10 11 15 24 x'76' tczlgna dfhzc2487 3 x'77' tczdmry dfhzc2488 none x'78' tczsdre2 dfhzc2430 3 9 11 22 x'79' tczpsraf dfhzc0145 3 6...
Page 881
Table 53. Messages issued and flags set by dfhznac for specific error codes (continued) error code symbolic label message action flags set x'a7' tczboeb dfhzc2449 2 3 7 11 18 22 24 x'a8' tczfmhle dfhzc2471 2 3 4 7 10 11 22 24 x'a9' tczracrf dfhzc2472 11 x'aa' tczsdse9 dfhzc2473 3 9 11 x'ab' tczluerr...
Page 882
Table 53. Messages issued and flags set by dfhznac for specific error codes (continued) error code symbolic label message action flags set x'd3' tczdmpd dfhzc2463 none x'd4' tczcxrr dfhzc2453 1 2 3 9 10 x'd5' tczcxe2 dfhzc2452 3 7 9 10 11 18 24 x'd6' tczsxc2 dfhzc2441 none x'd7' tczsxc1 dfhzc2440 no...
Page 883
Table 53. Messages issued and flags set by dfhznac for specific error codes (continued) error code symbolic label message action flags set x'ff' tczpspe dfhzc0149 7 note: 1. See message dfhzc2497 or dfhzc3493, depending on the device type. 2. “good morning” message to be sent. 3. Cancel task, and cl...
Page 884
Table 54. Cics messages associated with vtam errors (continued) message symbolic label error code action flags set dfhzc2410 tcztxcu x'd1' 2 3 7 9 10 11 24 dfhzc2411 tczdmsn x'e0' none dfhzc2412 tczdmra x'e1' none dfhzc2413 tczdmcl x'e2' 2 dfhzc2414 tczsrcsp x'80' none dfhzc2416 tczsrcvh x'13' 7 18 ...
Page 885
Table 54. Cics messages associated with vtam errors (continued) message symbolic label error code action flags set dfhzc2450 tczssxar x'83' none dfhzc2451 tczsrcci x'cc' 2 3 9 10 11 dfhzc2452 tczcxe2 x'd5' 3 7 9 10 11 18 24 dfhzc2453 tczcxrr x'd4' 1 2 3 9 10 dfhzc2454 tczsrccx x'cd' 2 3 9 10 11 dfhz...
Page 886
Table 54. Cics messages associated with vtam errors (continued) message symbolic label error code action flags set dfhzc3429 tczstrmm x'ec' 2 3 7 dfhzc3430 tczston x'ed' 2 3 dfhzc3431 tczstin x'ef' 2 3 dfhzc3432 tczstler x'ea' 2 3 dfhzc3433 tczermgr x'58' 7 dfhzc3434 tczunbis x'54' 2 3 7 9 10 11 24 ...
Page 887
Table 54. Cics messages associated with vtam errors (continued) message symbolic label error code action flags set dfhzc3489 tczluinh x'c8' 7 18 24 dfhzc3490 tczcpfal x'c3' 7 24 dfhzc3491 tczexro x'b0' 7 15 24 dfhzc3492 tczdmit x'16' none dfhzc3495 tcznotna x'6b' 7 24 dfhzc3499 tczdwegf x'c0' none d...
Page 888
Table 54. Cics messages associated with vtam errors (continued) message symbolic label error code action flags set dfhzc4939 tczlupun x'8c' 2 3 5 7 24 dfhzc4940 tczluskn x'8f' 2 3 5 7 24 dfhzc4941 tczluplk x'8d' 2 3 5 7 24 dfhzc4942 tczlupex x'8e' 2 3 5 7 24 dfhzc4943 tczfsmrb x'f8' 3 7 9 10 11 24 d...
Page 889
Table 55. Messages issued and flags set by dfhznac for specific sense codes (continued) sense code message action flags set x'0811' dfhzc2464 9, 10, 11 x'0812' dfhzc2465 2, 3 x'081b' dfhzc2483 2, 3 3 x'081c' dfhzc2466 2, 3, 9, 10, 11 x'0824' dfhzc2475 3, 9, 10, 11 x'0825' dfhzc2484 2, 3, 9, 10, 11 x...
Page 890
Table 55. Messages issued and flags set by dfhznac for specific sense codes (continued) sense code message action flags set x'40ff' dfhzc3453 2, 3, 7, 9, 10, 11, 23, 24 x'8000' dfhzc3435 2, 3, 7, 9, 10, 11, 18, 24 x'8005' dfhzc3435 2, 3, 7, 9, 10, 11, 18, 24 x'80ff' dfhzc3435 2, 3, 7, 9, 10, 11, 18,...
Page 891
Table 56. Meanings of action flags set by dfhznac (continued) flag field bit mask hex bit setting action 11 ..1. .... X'20' abend any task attached to tctte 12 ...1 .... X'10' cancel any task attached to tctte 13 .... 1... X'08' good morning message to be sent 14 .... .1.. X'04' purge any bms pages ...
Page 892
870 customization guide.
Page 893
Appendix c. Analyzing cics restart information you can programmatically determine the type of cics shutdown that occurred and whether it is safe to override the next restart type and perform a cold restart of the cics system. Dfhrmutl provides the set_auto_start keywords to allow a cics system to be...
Page 894
872 customization guide.
Page 895: Program (Dfh$Tdwt)
Appendix d. Using the transient data write-to-terminal program (dfh$tdwt) dfh$tdwt is a sample program that sends transient data messages to a terminal or printer. You can use it to send messages from a single transient data queue, or from several queues, to one terminal. In the definition for the t...
Page 896
874 customization guide.
Page 897
Appendix e. Uppercase translation this appendix describes how to translate lower- and mixed-case characters to uppercase. “translating national characters to uppercase” describes how to translate national characters that cics cannot handle by standard means. “translating ts data sharing messages to ...
Page 898
Note: if you are already using a customized tct rather than dfhtctdy (that is, something other than 'no' or 'dy' is specified on the sit tct parameter), you must add your translation code to the tct you are using. Figure 133 shows a suggested way to code the assembler source statements to translate ...
Page 899: User Exit, Dfh$Xtse
Appendix f. The example program for the xtsereq global user exit, dfh$xtse this appendix lists the example global user exit program, dfh$xtse. The example shows you how to: v use exec cics commands in a global user exit program v use exec cics commands and xpi calls in the same exit program v modify...
Page 900
* * * it is not safe to use the following storage: * * program storage (dfheistg) since this is freed as soon * * as the exit program returns control to cics. * * * * 2) when adding or removing a field in the command parameter list, * * you must remember: * * a) to set/clear the field’s existence bi...
Page 901
*---------------------------------------------------------------------* * the ts routing table is made up of a set of entries. Each entry * * can be mapped by the table_entry dsect * *---------------------------------------------------------------------* table_entry dsect entry_name ds cl8 new_name ...
Page 902
* registers: * * r1 = uepar plist (set on entry) * * = work register * * r2 = uepar plist * * r3 = program base register (set by dfheient) * * r6 = linkage register * * r11= eib register * * r13= eistg register (set by dfheient) * * r15= work register * * user exit return code * * * * logic: * * dfh...
Page 903
*=====================================================================* * ts_request - invoked at xtsereq exit point * * determine the ts queue name and scan the ts_routing_table for * * a match. If an entry exists in the table, then check the action * * field and call the route_request or local_req...
Page 904
*=====================================================================* ts_request ds 0h * check for possible recursion l r1,ueprecur address of recursive count lh r1,0(r1) fetch count ltr r1,r1 has exit been invoked recursively? Bnz error2 ..Yes branch to error routine * * extract pointer to the ei...
Page 905
*=====================================================================* * ts_request_complete - invoked at xtsereqc exit point * * free any shared storage that was acquired during previous * * invocation at xtsereq. * * * * registers: * * r1 = work register * * r6 = linkage register * * r8 = command...
Page 906
*=====================================================================* * local_request: process local ts queues * * an entry has been found in the ts_routing table for this ts * * queue name. If required, rename the ts queue name, but do not * * modify the sysid. * * * * registers: * * r1 = work re...
Page 907
*=====================================================================* * route_request: ship request to remote system * * an entry has been found in the ts_routing table for this ts * * queue name. The request is modified by adding a sysid to the * * command and renaming the queue if required. * * ...
Page 908
* update the sysid in clps route1 ds 0h mvc shared_sysid,new_sysid copy sysid into shared storage l r8,uepclps address the clps.. Using ts_addr_list,r8 ..With register 8 l r1,ts_addr0 address the eid.. Using ts_eid,r1 ..With register 1 oi ts_bits1,ts_sysid_v indicate sysid now present in clps drop r...
Page 909
* logic: * * entry_not_found: * * call getmain_shared * * copy default_sysid into shared storage * * address the command plist * * update addr7 to point to the address of the default sysid * * set the sysid existence bit in the eid * * set the hi-order bit in last address in clps * * return * *=====...
Page 910
*=====================================================================* * getmain_shared - obtain shared storage * * * * registers: * * r0 = used by exec cics call * * r1 = used by exec cics call * * work register * * r6 = link register - return address * * r11= eib register (set on entry) * * r12= ...
Page 911
*=====================================================================* * freemain_shared - free shared storage * * free the shared storage associated with this command. * * registers: * * r0 = used by exec cics call * * r1 = used by exec cics call * * r6 = link register - return address * * r11= ei...
Page 912
Using dfhtrpt_arg,r1 trace_entry ds 0h l r1,uepxstor prepare for xpi call dfhtrptx clear, x point_id(tr_entry) b issue_trace trace_exit ds 0h l r1,uepxstor prepare for xpi call dfhtrptx clear, x point_id(tr_exit) b issue_trace trace_error ds 0h l r1,uepxstor prepare for xpi call dfhtrptx clear, x po...
Page 913
Error4 ds 0h mvi tr_error_n,4 b trace_error error5 ds 0h mvi tr_error_n,5 b trace_error error6 ds 0h mvi tr_error_n,6 b trace_error error7 ds 0h mvi tr_error_n,7 b trace_error error8 ds 0h mvi tr_error_n,7 b trace_error error9 ds 0h mvi tr_error_n,7 b trace_error eject , drop r2 drop dfhuepar drop r...
Page 914
Before using the sample program in a production environment, you would need to customize it to suit your installation. Ts_routing_table ds 0d entry_name_1 dc cl8’aaaaaaaa’ rename queue aaaaaaaa as new_name_1 dc cl8’bbbbbbbb’ bbbbbbbbb qor_sysid_1 dc cl4’ ’ action_1 dc xl1’01’ local request filler_1 ...
Page 915
Appendix g. Threadsafe xpi commands most, but not all, xpi commands are threadsafe. Issuing any of the non-threadsafe commands causes cics to use the qr tcb to ensure serialization. The xpi commands that are threadsafe are indicated in the command syntax diagrams in chapter 3, “the user exit program...
Page 916
Non-threadsafe commands: v dfhdudux transaction_dump 894 customization guide.
Page 917: Bibliography
Bibliography the cics transaction server for z/os library the published information for cics transaction server for z/os is delivered in the following forms: the cics transaction server for z/os information center the cics transaction server for z/os information center is the primary source of user ...
Page 918
Cics transaction server for z/os migration from cics ts version 3.1, gc34-6858 cics transaction server for z/os migration from cics ts version 1.3, gc34-6855 cics transaction server for z/os migration from cics ts version 2.2, gc34-6856 cics transaction server for z/os installation guide, gc34-6812 ...
Page 919
Cicsplex sm application programming guide, sc34-6848 cicsplex sm application programming reference, sc34-6849 diagnosis cicsplex sm resource tables reference, sc34-6850 cicsplex sm messages and codes, gc34-6851 cicsplex sm problem determination, gc34-6852 cics family books communication cics family:...
Page 920
Short title full title data areas volume 1 os/390 mvs data areas, vol 1 (abep-dalt), sy28-1164 data areas volume 2 os/390 mvs data areas, vol 2 (dccb-ittcte), sy28-1165 data areas volume 3 os/390 mvs data areas, vol 3 (ivt-rcwk), sy28-1166 data areas volume 4 os/390 mvs data areas, vol 4 (rd-srra), ...
Page 921
Updates to the softcopy are clearly marked by revision codes (usually a # character) to the left of the changes. Bibliography 899.
Page 922
900 customization guide.
Page 923: Accessibility
Accessibility accessibility features help a user who has a physical disability, such as restricted mobility or limited vision, to use software products successfully. You can perform most tasks required to set up, run, and maintain your cics system in one of these ways: v using a 3270 emulator logged...
Page 924
902 customization guide.
Page 925: Index
Index special characters “good night” transaction customizing the sample program 804 overview 801 sample program, dfh0gnit 803 numerics 3270 bridge bridge exit 661 bridge exit program 661 3270 information display system error processors (optional) 498 unavailable printer dfhznep 506 a abends transac...
Page 926
Automatic installation of ipic connections introduction 553 preliminary considerations 553 automatic installation of programs benefits of 581 control program parameter list at install 583 testing 588 installation of mapsets 581 introduction 579 model definitions 580 requirements for 582 supplied res...
Page 927
Communications area autoinstall control program appc connections 545 programs 583 terminals 518 autoinstall user program ipconns 555 cicsdbctl interface status program 659 distributed routing program 645 dynamic routing program 607 node error program 487 program error program 441 terminal error prog...
Page 928
Dfhcsdup, system definition utility program (continued) sample programs (continued) dfh$crfa 816 dfh$crfp 816 dfh$fora 817 dfh$forp 817 dfh0cbdc 817 dfh0crfc 816 dfh0forc 817 dfhdbuex, cics–dbctl interface status program communications area 659 introduction to 659 sample program 660 dfhddapx macro 3...
Page 929
Dfhsaiqx macro 386, 391 dfhsmfds, smf header dsect 750 dfhsmmcx macro 392 dfhsmsrx macro 397 dfhsnep macro type=def3270 500 type=defilu 501 type=errproc 484, 501 type=final 501 type=initial 483, 500 type=ustor 499 type=ustorend 499 dfhsnep, sample node error program 499 dfhsnet macro 503 count opera...
Page 930
Distributed program link (dpl) (continued) dynamic routing of requests (continued) eligibility for routing 597 error handling 600 terminating a request 600 when the routing program is invoked 598 distributed routing of bts activities changing the target region 627 eligibility for routing 625 error h...
Page 931
Dynamic routing program (dfhdyp) (continued) changing bridge parameters 604 changing the program name 593, 599 changing the target region 592, 599 communications area 607 error handling 594, 600 information passed to 591 invoking on abend 594, 602 modifying application’s communications area 595, 602...
Page 932
Functional list of glues 32 g generic resources, vtam 547 node error program 512 get_attribute_value function of the xpi 325 get_next_attribute function of the xpi 326 get_next_entry function of the xpi 327 get_next_program function of the xpi 380 getmain function of the xpi 393 global user exits ex...
Page 933
Global user exits (continued) sample programs (continued) dfh$wbx1 21 dfh$wbx2 22 dfh$xdrq 19 dfh$xisq 24 dfh$xnqe 19, 66 dfh$xziq 24 dfh$zcat 16 dfhxis 140 dfhxtenf 230 summary of 15 trace table entries 6 with storage protection data storage key 11 execution key 11 glues 3 glues, alphabetical list ...
Page 934
Log manager functions of the xpi 360 logical units (lus) node error program 486 logon mode table, vtam 833 lu alias names 523 m maxerrs operand dfhtept type=initial 465 maxtids operand dfhtept type=initial 465 mct (monitoring control table) entries for dbctl 749 entries for emps 747 model definition...
Page 935
Nep (node error program) (continued) sample (continued) dfhsnep type=initial macro 500 dfhsnep type=ustor macro 499 dfhsnep type=ustorend macro 499 error processor vector table (epvt) 497, 501 error processors for intlu, dfhsnep type=defilu 501 error processors, dfhsnep type=def3270 500 error status...
Page 936
Nonpurgeable task 472 notation, syntax xviii o options operand dfhtepm type=initial 460 dfhtept type=initial 465 overseer program customizing the sample program 703 including the cebt command 704 loop or wait detection in the active 705 dfh$axro 693 dfhosd data set 693 dfhwosm macros 695 func=build ...
Page 937
S sample programs “good night” transaction (dfh0gnit) 803 cics–dbctl interface status program (dfhdbuex) 660 for automatic installation of appc connections 550 for automatic installation of ipconns 557 for automatic installation of programs 586 for automatic installation of terminals 527 for distrib...
Page 938
Syntax notation xviii system autoinstall 581 system definition utility program (dfhcsdup) as a batch program extract command 814 link-edit statements for user program 819 parameters passed from dfhcsdup to the user program 815 when the user program is invoked 815 writing a program for extract proces...
Page 939
Task-related user exits (continued) uephmsa, address of register save area 275 ueppbtok, address of performance block token 277 ueprmqua, address of the resource manager qualifier name 276 ueprmstk, address of the kernel stack entry 275 uepsecblk, address of a fullword addressing the user security b...
Page 940
Terminal error program (tep) (continued) replace error processors, dfhtepm type=errproc 462 sample action flag names 457 common subroutines 455 components 451 decb information 458 decb operand 458 dfhtepm type=initial 459 entry and initialization 454 error processing execution 454 error processor se...
Page 941
User-written node error programs 505 utility programs shutdown assist, dfhcesd 429 v virtual terminals, automatic installation of 567 vtam dynamic lu alias 523 w work areas in task-related user exits 292 write journal data function of the xpi 419 x xalcaid, global user exit 221 xaltenf, global user ...
Page 942
Xpcreq, global user exit (continued) description 175 example of use 185 parameter list and return codes 177 uepclps parameter 181 xpcreqc, global user exit command parameter structure 181 description 177 example of use 185 parameter list and return codes 179 uepclps parameter 181 xpcta, global user ...
Page 943
Xrmmi, global user exit 193 xrsindi, global user exit 196 xsnex, global user exit 201 xsnoff, global user exit 200 xsnon, global user exit 199 xsrab, global user exit 203 xsterm, global user exit 206 xstout, global user exit 202, 776 xszarq, global user exit 137 xszbrq, global user exit 137 xtcatt, ...
Page 944
922 customization guide.
Page 945: Notices
Notices this information was developed for products and services offered in the u.S.A. Ibm may not offer the products, services, or features discussed in this document in other countries. Consult your local ibm representative for information on the products and services currently available in your a...
Page 946
The licensed program described in this document and all licensed material available for it are provided by ibm under terms of the ibm customer agreement, ibm international programming license agreement, or any equivalent agreement between us. 924 customization guide.
Page 947: Trademarks
Trademarks ibm, the ibm logo, and ibm.Com are trademarks or registered trademarks of international business machines corp., registered in many jurisdictions worldwide. A current list of ibm trademarks is available on the web at copyright and trademark information at www.Ibm.Com/legal/copytrade.Shtml...
Page 948
926 customization guide.
Page 949
Readers’ comments — we'd like to hear from you cics transaction server for z/os customization guide version 3 release 2 publication no. Sc34-6814-04 we appreciate your comments about this publication. Please comment on specific errors or omissions, accuracy, organization, subject matter, or complete...
Page 950
Readers’ comments — we'd like to hear from you sc34-6814-04 sc34-6814-04 cut or fold along line cut or fold along line fold and tape please do not staple fold and tape fold and tape please do not staple fold and tape place postage stamp here ibm united kingdom limited user technologies department (m...
Page 952
Product number: 5655-m15 sc34-6814-04.
Page 953
Spine information: ci c s t ra n sa cti on s erv er fo r z/o s c u st omiz at io n g ui de ve rs io n 3 r el ease 2.