- DL manuals
- Raritan
- Gateway
- Command Center CC-SG
- Administrator's Manual
Raritan Command Center CC-SG Administrator's Manual
Summary of Command Center CC-SG
Page 1
Commandcenter ® secure gateway cc-sg administrator guide release 3.0 copyright © 2006 raritan, inc. Cca-0b-e may 2006 255-80-5140-00
Page 2
This page intentionally left blank..
Page 3
Copyright and trademark information this document contains proprietary information that is protected by copyright. All rights reserved. No part of this document may be photocopied, reproduced, or translated into another language without express prior written consent of raritan, inc. © copyright 2006...
Page 4
Safety guidelines to avoid potentially fatal shock hazard and possible damage to raritan equipment: • do not use a 2-wire power cord in any product configuration. • test ac outlets at your computer and monitor for proper polarity and grounding. • use only with grounded outlets at both the computer a...
Page 5
C ontents i contents chapter 1: introduction ....................................................................................................1 prerequisites ..............................................................................................................................1 intended au...
Page 6
Ii c ontents copy device configuration ..............................................................................................................57 upgrade device ...............................................................................................................................57 pin...
Page 7
C ontents iii edit policy ......................................................................................................................................111 delete policy..............................................................................................................................
Page 8
Iv c ontents inactivity timer configuration ........................................................................................................164 time/date configuration................................................................................................................165 modem con...
Page 9
C ontents v cc-sg & snmp ............................................................................................................................234 cc-sg & cc-noc ........................................................................................................................234 cc-sg in...
Page 10
Vi f igures figures figure 1 cc-sg front view ......................................................................................................................... 1 figure 2 cc-sg - rear panel .........................................................................................................
Page 11
F igures vii figure 52 add device selection screen .................................................................................................... 51 figure 53 add device screen for powerstrip............................................................................................. 51 figure...
Page 12
Viii f igures figure 105 configure ports screen for ipmi server................................................................................... 84 figure 106 configure outlet port screen ................................................................................................... 85 figure ...
Page 13
F igures ix figure 158 generate certificate signing request screen ....................................................................... 132 figure 159 certificate request generated............................................................................................... 132 figure 160 genera...
Page 14
X f igures figure 211 configuration settings device settings screen...................................................................... 174 figure 212 configuration settings device settings screen...................................................................... 175 figure 213 security manager...
Page 15
F igures xi figure 264 selecting network interface configuration ............................................................................. 209 figure 265 editing network interfaces ..................................................................................................... 210 figure 26...
Page 17
C hapter 1: i ntroduction 1 chapter 1: introduction congratulations on your purchase of commandcenter secure gateway (cc-sg), raritan’s convenient and secure method for managing various unix servers, firewalls, routers, load balancers, power management devices, and windows servers. Cc-sg provides ce...
Page 18
2 c ommand c enter s ecure g ateway a dministrator g uide product features and benefits • seamless management cc-sg offers seamless management of dominion series and paragon ® management appliances through paragon remote user stations (ust1r/ust2r) – leverage your embedded base with a cc-sg to draw ...
Page 19
C hapter 1: i ntroduction 3 • comprehensive logging − logs events locally. − can use an external syslog server for event logs (events are immediately posted or exported) and the ability to have other raritan products use it as a syslog server. − provides full auditing and tracking capabilities. − ke...
Page 20
4 c ommand c enter s ecure g ateway a dministrator g uide • cim (computer interface module)—is the hardware used to connect a target server and a raritan device. Each target requires a cim, except for the dominion kx101 which is attached directly to one target and therefore, does not require a cim. ...
Page 21
C hapter 1: i ntroduction 5 • ports —are connection points between a raritan device and a target system or server. Or, a port can be a device that is directly connected to a lan/cc-sg via in-band access. In cc- sg, you click on a port to access and manage the target. The port is essentially the dest...
Page 22
6 c ommand c enter s ecure g ateway a dministrator g uide new 3.0 features these administrator features are now available in cc-sg 3.0: note: if viewing a pdf file, click on the page number to navigate to the location in the document where the feature is described. F eature location import of catego...
Page 23
C hapter 2: a ccessing cc-sg 7 chapter 2: accessing cc-sg once you have configured cc-sg with an ip address and have defined at least one user, as described in raritan’s commandcenter secure gateway setup guide , the cc-sg unit can be placed at its final destination. Make all necessary hardware conn...
Page 24
8 c ommand c enter s ecure g ateway a dministrator g uide 2. You will be warned if you are using an unsupported java runtime environment version on your machine. From the window that pops up, select whether you will download the correct jre version from the cc-sg server (if available), download it f...
Page 25
C hapter 2: a ccessing cc-sg 9 standalone client access the standalone cc-sg client allows you to connect to cc-sg servers by launching a java application instead of running an applet through a web browser. 1. Install the standalone cc-sg client located on the included cd rom onto your pc. 2. Double...
Page 26
10 c ommand c enter s ecure g ateway a dministrator g uide 3. Click update configuration to submit the changes. A confirmation window asks if you wish to restart cc-sg in order to apply changes. 4. Click ok to log out from your current session and restart cc-sg. 5. Access cc-sg using the new ip addr...
Page 27
C hapter 2: a ccessing cc-sg 11 2. Select an application from the pull-down menu and note the number in the version field. If the firmware needs upgrading, see the previous section check and upgrade cc-sg firmware version and continue to step 3. 3. Select the application name that needs to be upgrad...
Page 28
12 c ommand c enter s ecure g ateway a dministrator g uide to access a remote target device that is connected via a serial port, click on the appropriate device in the devices selection tree, under the devices tab. If the port is configured for a console application, a security warning appears, indi...
Page 29
C hapter 2: a ccessing cc-sg 13 power down cc-sg if running cc-sg on the v1 platform and if it loses ac power while it is up and running, the v1 unit remembers its last power state. Once ac power is restored, the v1 unit automatically reboots. However, if a v1 unit loses ac power when it is turned o...
Page 30
14 c ommand c enter s ecure g ateway a dministrator g uide note: to make ports easier to find, right-click on the tree and select the desired listing method under port sorting options. Ports sorted by name will be listed alphabetically; ports sorted by status will be grouped in the order of: availab...
Page 31
C hapter 2: a ccessing cc-sg 15 main window components figure 13 cc-sg application window the cc-sg menu bar displays all operations and configuration commands. Active commands are based upon the privileges of the user, as established by the cc-sg administrator. The user’s privileges also determine ...
Page 32
16 c ommand c enter s ecure g ateway a dministrator g uide configuring cc-sg manager components in order to use cc-sg effectively, you must complete the following configuration steps, as described in this and the next chapter: • configure and install dominion series and ip-reach appliances (both ser...
Page 33
C hapter 2: a ccessing cc-sg 17 compatibility matrix the compatibility matrix lists the firmware versions of raritan devices and software versions of applications that are compatible with the current version of cc-sg. To view the compatibility matrix, on the devices menu, click compatibility matrix ...
Page 34
18 c ommand c enter s ecure g ateway a dministrator g uide.
Page 35
C hapter 3: e xample c onfiguration w orkflow 19 chapter 3: example configuration workflow create associations the association wizard guides you through steps to create categories and their associated elements. The wizard then automatically creates a port group for each element and a policy for each...
Page 36
20 c ommand c enter s ecure g ateway a dministrator g uide 2. After reading the overview, click next . The create category and elements screen of the wizard appears. Figure 16 association wizard - category and elements screen 3. Type the name of a category you wish to organize your ports by (for exa...
Page 37
C hapter 3: e xample c onfiguration w orkflow 21 5. To create another category, click add another category and repeat steps 3 and 4. To review categories and elements you have created, click previous or next to cycle through them. Figure 17 adding another category 6. When you are done creating categ...
Page 38
22 c ommand c enter s ecure g ateway a dministrator g uide 8. Cc-sg will show a progress bar while it is creating the associations, port groups and policies. When this is complete, the association wizard summary screen appears displaying the list what was created. Click done to exit the wizard. Figu...
Page 39
C hapter 3: e xample c onfiguration w orkflow 23 4. Click next to proceed. The add device description screen appears. Depending on the type of device you selected, you will see slightly different add device screens. Figure 21 add device powerstrip figure 22 add device sx 5. Type the device name in t...
Page 40
24 c ommand c enter s ecure g ateway a dministrator g uide device created successfully message confirms that device has been added. This step is very important. Make sure you select the correct associations and elements for the device. Some devices such as sx may take up to a minute to add. 9. Repea...
Page 41
C hapter 3: e xample c onfiguration w orkflow 25 3. Click configure next to the serial port line item you wish to configure. The configure serial port screen appears. Figure 24 configure serial ports 4. Type a port name in port name field. Typically, you should name the port after the target server ...
Page 42
26 c ommand c enter s ecure g ateway a dministrator g uide kvm port 1. Click on the devices tab and select a kvm device, for example, dominion kx, from the devices tree. 2. On the devices menu, click port manager , and then click configure ports . Alternatively, you can right-click on the device and...
Page 43
C hapter 3: e xample c onfiguration w orkflow 27 5. Click on the application name drop-down menu and select name. This application, for example, raritan remote console (rrc), is used to manage the target system. All ports should use rrc except for those on an sx. 6. Select the associated category an...
Page 44
28 c ommand c enter s ecure g ateway a dministrator g uide 5. If using local authentication, type the new password into the password field (6-16 characters, alphanumeric characters and underscores). 6. If using local authentication, re-type password in retype password field. 7. Type a dial back numb...
Page 45
C hapter 3: e xample c onfiguration w orkflow 29 2. On the users menu, click add user group . Alternatively, right-click on a user group and select add user group . The add user group screen appears. Figure 28 add user group screen 3. Type the group name in the user group name field (1-16 characters...
Page 46
30 c ommand c enter s ecure g ateway a dministrator g uide create/edit port groups cc-sg uses port groups to control user access. Policies can be applied to specific user groups that allow only access to those ports specified in the port group. For example, if you wanted to restrict user access to o...
Page 48
32 c ommand c enter s ecure g ateway a dministrator g uide sundays, and custom to manually choose the days policy to be applied. If you choose custom, check on the days of the week to apply the policy. 9. Click on a permission value to select a permission type: deny, or control . 10. Click update to...
Page 49
C hapter 3: e xample c onfiguration w orkflow 33 6. Click ok to add the policy or policies to the group. A group policies updated successfully message confirms that policies have been updated. 7. Repeat steps 1 through 6 to edit other groups’ policies. Add users to user group you now need to add use...
Page 50
34 c ommand c enter s ecure g ateway a dministrator g uide 12. Type an email address for this user in the email address field, if desired. 13. Click ok to add this user to the system. A user created successfully message indicates the user has been added to the system. 14. Drag the new user icon to t...
Page 51
C hapter 4: c reating a ssociations 35 chapter 4: creating associations associations cc-sg provides powerful, highly customizable organizational capabilities. Associations provide this organizational capability and are used to organize your equipment. For example, you may have raritan devices that m...
Page 52
36 c ommand c enter s ecure g ateway a dministrator g uide other examples of typical association configurations of category and elements are as follows: c ategory e lements location new york city, philadelphia, dc1 os type unix, windows, linux department sales, it, engineering port type kvm, serial,...
Page 53
C hapter 4: c reating a ssociations 37 • devices —are raritan products such as dominion kx116, dominion sx48, dominion ksx440, ip-reach, paragon ii system controller, paragon ii umt832 with ustip, etc. That are managed by cc-sg. These devices control the target servers and systems that are connected...
Page 54
38 c ommand c enter s ecure g ateway a dministrator g uide add category 1. On the associations menu, click association manager . The association manager screen appears. Figure 36 association manager screen 2. Click add in the category panel to add a new category. The add category window appears. Fig...
Page 55
C hapter 4: c reating a ssociations 39 edit category 1. On the associations menu, click association manager . The association manager screen appears. 2. Click on the category name drop-down arrow and select the category to be edited. 3. Click edit in the category panel of the screen to edit the cate...
Page 56
40 c ommand c enter s ecure g ateway a dministrator g uide add element 1. On the associations menu, click association manager. The associations manager screen appears. Figure 40 association manager screen 2. Click add in the element for category panel to add a new element. The add element window app...
Page 57
C hapter 4: c reating a ssociations 41 edit element 1. On the associations menu, click association manager. The association manager screen appears. 2. Select the element to be edited from the element for category list and click edit in the elements for category panel. The edit element window appears...
Page 58
42 c ommand c enter s ecure g ateway a dministrator g uide association wizard the association wizard guides you through steps to create categories and their associated elements , as described in the association manager section above, then automates the creation of related port groups and policies fo...
Page 59
C hapter 4: c reating a ssociations 43 5. If you wish to create another category, click add another category and repeat steps 3 and 4. Figure 46 adding another category 6. When you are done creating categories, click next at the bottom of the screen. The confirm choices screen of the wizard appears....
Page 60
44 c ommand c enter s ecure g ateway a dministrator g uide 8. Cc-sg will show a progress bar while it is creating the associations, port groups and policies. When this is complete, the association wizard summary screen appears displaying the list what was created. Click done to exit the wizard. Figu...
Page 61
C hapter 4: c reating a ssociations 45 import categories, devices, ports from csv file to expedite configuration, you can import pre-defined categories, elements of those categories, and the ports and devices to which the categories apply from a csv file. After importing, you can have cc-sg validate...
Page 62
46 c ommand c enter s ecure g ateway a dministrator g uide csv file format the entries in the csv file are case-sensitive and each row in the csv file has this format: {tag},{value}[,{value},….] tag s ubsequent fields comments category category name,valuetype, applicability value type is string or i...
Page 63
C hapter 4: c reating a ssociations 47 once successfully imported, you should see something like: figure 50 analysis report screen if necessary, refer to appendix f: troubleshooting for problem resolution..
Page 64
48 c ommand c enter s ecure g ateway a dministrator g uide.
Page 65
C hapter 5: adding devices and device g roups 49 chapter 5: adding devices and device groups device manager device manager commands allow you to configure dominion series and ip-reach units and their individual ports. From a cc-sg perspective, connection to a remote target device is made via a seria...
Page 66
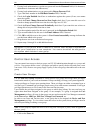
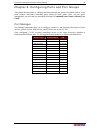
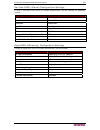
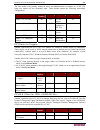
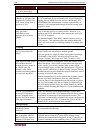
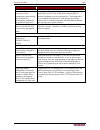
50 c ommand c enter s ecure g ateway a dministrator g uide device icons i con m eaning device available port available kvm port connected – in current user session port paused – because device is paused port unavailable – because device is unavailable port busy – other user connected to port serial ...
Page 67
C hapter 5: adding devices and device g roups 51 add device use this command to add a new device to the system. 1. Click on the devices tab. 2. On the devices menu, click device manager , and then click add device . The add device selection screen appears. Figure 52 add device selection screen 3. Cl...
Page 68
52 c ommand c enter s ecure g ateway a dministrator g uide figure 54 add device screen for raritan devices figure 55 add device screen for ilo, riloe.
Page 69
C hapter 5: adding devices and device g roups 53 figure 56 add device screen for ipmi server (v 1.5) figure 57 add device screen for generic device 5. Type the new device name in the device name field. 6. Type the ip address or hostname of the new device in the device ip or hostname field. For hostn...
Page 70
54 c ommand c enter s ecure g ateway a dministrator g uide kx devices with encryption cc-sg supports adding and managing dominion kx devices, such as kx101, that have been configured with: • ssl authentication and no data encryption • ssl authentication and data encryption • ssl authentication and s...
Page 71
C hapter 5: adding devices and device g roups 55 delete device 1. Click on the devices tab and select a device from devices tree. 2. On the devices menu, click device manager , and then click delete device . The delete device screen appears. Figure 59 delete device screen 3. Click ok to delete the d...
Page 72
56 c ommand c enter s ecure g ateway a dministrator g uide backup device configuration use this command to back up all user configuration and system configuration files. If anything happens to your system, you can restore your previous configurations from memory. Note: only for dominion sx 2.5 devic...
Page 73
C hapter 5: adding devices and device g roups 57 copy device configuration this command allows you to copy configurations from one device to another or multiple devices. Note: configuration can only be copied between dominion sx units and dsx units that have the same number of ports. 1. Click on the...
Page 74
58 c ommand c enter s ecure g ateway a dministrator g uide if the firmware version of the device is not compatible with cc-sg, a message will alert you and ask if you want to proceed (please see chapter 2: accessing cc-sg for additional information). Click yes to upgrade the device, or no to cancel ...
Page 75
C hapter 5: adding devices and device g roups 59 pause device you can pause a device to temporarily suspend cc-sg’s control of it without losing any of the configuration data stored within the cc-sg server. 1. Click on the devices tab and select a device from the devices tree. 2. On the devices menu...
Page 76
60 c ommand c enter s ecure g ateway a dministrator g uide custom view you can customize the devices tree by organizing devices to appear in a particular format. You might want to view devices by country, by time zone, or by any other option that helps you differentiate between them. Set up a custom...
Page 77
C hapter 5: adding devices and device g roups 61 add custom view 1. Click on the devices tab. 2. On the devices menu, click change view, and then click custom view . The custom view screen appears. 3. In the custom view panel, click add . An add custom view window appears. Figure 69 add custom view ...
Page 78
62 c ommand c enter s ecure g ateway a dministrator g uide 5. In the custom view details panel, click on the drop-down arrow at the bottom of the panel. This list contains categories that you can use to filter custom views. Select a detail from the drop-down list and click add to add the detail to t...
Page 79
C hapter 5: adding devices and device g roups 63 topological view use the topological view command to view the structural setup of all the connected appliances in your configuration. 1. Click on the devices tab and select a device from the devices tree. 2. On the devices menu, click topological view...
Page 80
64 c ommand c enter s ecure g ateway a dministrator g uide special access to paragon ii system devices paragon ii system controller (p2-sc) paragon ii system integration users can add their p2-sc devices to the cc-sg devices tree and configure them via the p2-sc admin application from within cc-sg. ...
Page 81
C hapter 5: adding devices and device g roups 65 ip-reach and ust-ip administration you can also perform administrative diagnostics on ip-reach and ust-ip devices connected to your paragon system setup directly from the cc-sg interface. After adding the paragon system device to cc-sg, it appears in ...
Page 82
66 c ommand c enter s ecure g ateway a dministrator g uide device power manager before using the device power manager view, make a physical connection of a powerstrip to a dominion sx or dominion ksx unit. When you add the powerstrip device, define this connection in cc-sg. Once the powerstrip is ad...
Page 83
C hapter 5: adding devices and device g roups 67 discover devices use this command to initiate a search for all devices on your system. The search will automatically detect all newly attached, and previously existing raritan devices on your network, including paragon, p2-sc, ip-reach, dominion kx, d...
Page 84
68 c ommand c enter s ecure g ateway a dministrator g uide 7. Select a device from the list and click add to add the device to cc-sg or click close to exit without adding the device. If you clicked add , the add device screen appears. Figure 81 add device screen 8. Type the user name and password (t...
Page 85
C hapter 5: adding devices and device g roups 69 device group manager use the device groups manager screen to add, edit, assign, and remove device groups and the rules that govern them. First add a device group, then add a device rule(s) to make working with and viewing devices easier. Add device gr...
Page 86
70 c ommand c enter s ecure g ateway a dministrator g uide edit device group name 1. On the associations menu, click groups manager , and then click device group manager . The device group manager screen appears. Figure 84 device groups manager screen 2. Click on the groups drop-down arrow and selec...
Page 87
C hapter 5: adding devices and device g roups 71 delete device group 1. On the associations menu, click groups manager , and then click device group manager . The device groups manager screen appears. Figure 86 device groups manager screen 2. Click on the group names drop down arrow and select the d...
Page 88
72 c ommand c enter s ecure g ateway a dministrator g uide important: you can combine the application of two or more rules by using operators such as ‘&’ meaning ‘and’ or ‘ ⎜ ’ (vertical bar that shares the key on your keyboard) meaning ‘or.’ note: when you select a category, make sure you select a ...
Page 89
C hapter 5: adding devices and device g roups 73 search for devices cc-sg can search for a device name that satisfies the text entered in the search box. Searches are case-insensitive. 1. Click on the devices tab. Figure 91 search for devices 2. At the bottom of the window, enter a search string in ...
Page 90
74 c ommand c enter s ecure g ateway a dministrator g uide examples are as follows: e xample d escription kx? Locates kx1, and kxz, but not kx1z . Kx* locates kx1, kx, kx1, and kx1z . Kx[0-9][0-9]t locates kx95t, kx66t, but not kxz and kx5pt . Disconnect users administrators can terminate any user's...
Page 91
C hapter 6: c onfiguring p orts and p ort g roups 75 chapter 6: configuring ports and port groups this chapter discusses how to configure and edit ports and port groups. Procedures on how to use ports (connect, disconnect, bookmark ports, search for ports, create views, use port power management, us...
Page 92
76 c ommand c enter s ecure g ateway a dministrator g uide when you click on the ports tab, the ports tree displays information about the ports connected with cc-sg. Clicking on a port causes the view port screen to appear. Ports are arranged alphabetically by name, or grouped by availability status...
Page 93
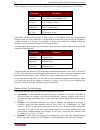
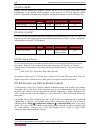
C hapter 6: c onfiguring p orts and p ort g roups 77 port icons for easier identification, different ports have different icons in the tree. In addition, availability status of each port also has a different icon. For a description of what the icons represent, please see the table below. I con m ean...
Page 94
78 c ommand c enter s ecure g ateway a dministrator g uide configure port configure a serial port click on the devices tab and select a serial device from the devices tree. 1. On the devices menu, click port manager , and then click configure ports . The configure ports screen appears. Figure 94 con...
Page 95
C hapter 6: c onfiguring p orts and p ort g roups 79 3. Click the configure button that corresponds to the serial port line item you wish to configure. The configure serial port screen appears. Figure 95 configure serial ports screen 4. Type a port name in port name field. For ease of use, you shoul...
Page 96
80 c ommand c enter s ecure g ateway a dministrator g uide 11. Click in-band parameters if you want to allow in-band access for this serial port. Figure 97 in-band parameters 12. Click on the in-band application drop-down arrow and select either remotedesktop viewer , ssh client , vnc viewer . Type ...
Page 97
C hapter 6: c onfiguring p orts and p ort g roups 81 configure a kvm port 1. Click on the devices tab and select a kvm device from the devices tree. 2. On the devices menu, click port manager , and then click configure ports . The configure ports screen appears. Figure 98 configure ports screen 3. T...
Page 98
82 c ommand c enter s ecure g ateway a dministrator g uide 5. Type a port name in the port name field. For ease of use, you should name the port after the server that is connected to the port. 6. Click on the application name drop-down arrow and either use the default application as configured in ap...
Page 99
C hapter 6: c onfiguring p orts and p ort g roups 83 configure a generic port with in-band access in-band access to generic devices, such as hubs, windows servers, cisco routers, can be managed with one of these in-band applications: • windows remote desktop (rdp) • secure shell (ssh) • virtual netw...
Page 100
84 c ommand c enter s ecure g ateway a dministrator g uide 7. Type a target username that the application will use as a start-up parameter. If a target name is supplied, then only a password is required when accessing a target. 8. Select the associated category and element from the port associations...
Page 101
C hapter 6: c onfiguring p orts and p ort g roups 85 3. Click the configure button that corresponds to the outlet port line item you wish to configure. A configure outlet port screen appears. Figure 106 configure outlet port screen 4. Type the port name in the port name field. For ease of use, you s...
Page 102
86 c ommand c enter s ecure g ateway a dministrator g uide delete ports delete a port to remove the port entry from the ports tree and cancel all accessibility of the remote target device. 1. Click on the ports tab and select a port to be deleted. 2. On the devices menu, click port manager , and the...
Page 103
C hapter 6: c onfiguring p orts and p ort g roups 87 bulk copy to save time, use the bulk copy command to duplicate port names or associations to other ports. 1. Click on the ports tab and select a port whose data you want to copy to another. 2. On the ports menu, click bulk copy . The bulk copy scr...
Page 104
88 c ommand c enter s ecure g ateway a dministrator g uide edit port edit a serial port 1. Click on the ports tab and select a serial port to be edited. 2. On the ports menu, click edit port . The edit serial port screen appears. Figure 109 edit serial port screen 3. Type the new port name in the po...
Page 105
C hapter 6: c onfiguring p orts and p ort g roups 89 edit a kvm port 1. Click on the ports tab and select a kvm port to be edited. 2. On the ports menu, click edit port . The edit kvm port screen appears. Figure 110 edit kvm port screen 3. Type a new port name in the port name field. 4. Click on the...
Page 106
90 c ommand c enter s ecure g ateway a dministrator g uide edit a generic port 1. Click on the ports tab and select a generic port to be edited. 2. On the ports menu, click edit port . The edit generic port screen appears. Figure 111 edit generic port screen 3. Type a new port name in the port name ...
Page 107
C hapter 6: c onfiguring p orts and p ort g roups 91 port group manager add port group 1. On the associations menu, click groups manager and then click port group manager . The port groups manager screen appears. Figure 112 port groups manager screen 2. Click add in the group panel to add a new grou...
Page 108
92 c ommand c enter s ecure g ateway a dministrator g uide edit port group 1. On the associations menu, click groups manager and then click port group manager . The port groups manager screen appears. 2. Click on the group name drop-down arrow and select a group to edit. Click edit in the group pane...
Page 109
C hapter 7: a dding u sers and u ser g roups 93 chapter 7: adding users and user groups user manager commands are listed in the users menu and allow you to define the cc-sg user list and assign user privileges for performing various functions. Cc-sg maintains a centralized user access list. Only an ...
Page 110
94 c ommand c enter s ecure g ateway a dministrator g uide 8. Check the force change password on next login check box if you want this user to be forced to change password the next time he or she logs in to cc-sg. 9. Check the force change password periodically check box if you want this user to hav...
Page 111
C hapter 7: a dding u sers and u ser g roups 95 5. Check the force change password periodically check box if you want this user to have to change his or her password from time to time and specify an expiration period for this user’s password in the expiration period field. 6. Check the force strong ...
Page 112
96 c ommand c enter s ecure g ateway a dministrator g uide 2. Type your old password in the old password field. 3. Type your new password in the password field. You cannot re-use your old password. 4. Re-type your password in the retype password field. 5. Click ok to change your password or cancel t...
Page 113
C hapter 7: a dding u sers and u ser g roups 97 logoff user(s) use this command to disconnect any logged-in user from cc-sg. 1. Click on the users tab and select a user from the users tree. Note: to select more than one user, hold the ctrl key and click on additional users. 2. On the users menu, cli...
Page 114
98 c ommand c enter s ecure g ateway a dministrator g uide bulk copy to save time, use the bulk copy command to duplicate user profiles or port assignments when creating new users. 1. Click on the users tab and select a user from the users tree whose properties you want to copy to another user(s). 2...
Page 115
C hapter 7: a dding u sers and u ser g roups 99 add user to group to manage users with similar privileges, you can assign them to groups. When you add a user to any group, you are assigning the group’s privileges to that user (please see the section add user group in this chapter for more informatio...
Page 116
100 c ommand c enter s ecure g ateway a dministrator g uide add user group use the add user group command to create specific groups and assign them different privileges, depending on the needs of your work environment. Groups can help you keep your system organized. Assign privileges, or features, t...
Page 117
C hapter 7: a dding u sers and u ser g roups 101 edit user group this command allows you to rename group and modify its features. Important: please remember that you must be an administrator to modify user groups. The category users not in group cannot be modified. Members of that group have observa...
Page 118
102 c ommand c enter s ecure g ateway a dministrator g uide apply (edit) user group policies groups can be assigned policies, or permissions, that allow them to view and/or control devices and ports. Depending on which policies are assigned to them, groups might have: no rights, some rights, control...
Page 119
C hapter 7: a dding u sers and u ser g roups 103 delete user group this command allows you to remove a group name from the system. Users from the deleted group will be re-assigned to the category users not in group , displayed at the base of the users tree. 1. Click on the users tab and select a gro...
Page 120
104 c ommand c enter s ecure g ateway a dministrator g uide 6. Click ok to assign users to the group or cancel to exit without saving. A users assigned successfully message confirms that users have been assigned. 7. Repeat steps 1 through 6 to assign users to other groups. Search for users cc-sg can...
Page 121
C hapter 7: a dding u sers and u ser g roups 105 supported wildcards these wildcards are supported: w ildcard d escription ? Indicates any character. [-] indicates a character in range. * indicates zero or more characters. Example: e xample d escription root? Locates root1, and rootn, but not root1n...
Page 122
106 c ommand c enter s ecure g ateway a dministrator g uide.
Page 123
C hapter 8: c reating p olicies 107 chapter 8: creating policies controlling user access with policies using policies to control user access to ports is entirely optional. You could decide to assign all users to the default system administrators user group, which grants full access to all configurat...
Page 124
108 c ommand c enter s ecure g ateway a dministrator g uide user groups user groups are used to define a group of users and cc-sg privileges they possess. When a user logs on, they will see the cc-sg interface. The user group privileges define what the user can do with cc-sg. The default system admi...
Page 125
C hapter 8: c reating p olicies 109 policies policies define what you can do, what you can do it to, and when you can do it. Policies allow specification of days and times, port/device access, and if it was granted control access (read/write), or deny access (none). Policies specify a port group or ...
Page 126
110 c ommand c enter s ecure g ateway a dministrator g uide policy manager policy manager commands allow you to add, edit, delete, and assign policies to device and port groups. Policies give users rights to allow or deny access to groups. Please see appendix c: initial setup process overview for mo...
Page 127
C hapter 8: c reating p olicies 111 10. Click update to add the policy. The update policy window appears figure 134 update policy window 11. Click yes to add the policy or no to close the window. 12. Click close to close the policy manager screen. 13. Repeat steps 1 through 12 to add other policies....
Page 128
112 c ommand c enter s ecure g ateway a dministrator g uide delete policy 1. On the associations menu, click policy manager . The policy manager screen appears. 2. Click on the name drop-down arrow to select a policy to be deleted. Click delete to delete the policy. The delete policy window appears....
Page 129
C hapter 9: c onfiguring r emote a uthentication 113 chapter 9: configuring remote authentication authentication and authorization users of cc-sg can be locally authenticated and authorized on the cc-sg or remotely authenticated using the following supported directory servers: • microsoft active dir...
Page 130
114 c ommand c enter s ecure g ateway a dministrator g uide establish order of authentication databases the general properties allow you to set the order of your authentication databases. If the first checked option is unavailable, cc-sg will try the second, then the third, and so on, until it is su...
Page 131
C hapter 9: c onfiguring r emote a uthentication 115 base dn you also enter a distinguished name (dn) to specify where the search for users begins. Enter a dn in the base dn field to specify an active directory container in which the users can be found. For example, entering: ou=dcadmins,ou=it,dc=xy...
Page 132
116 c ommand c enter s ecure g ateway a dministrator g uide 2. On the active directory server, set up your users under the users organizational unit (ou). These users will log into the cc-sg but are authenticated on the active directory server. Note that the display name of joe raritan can be differ...
Page 133
C hapter 9: c onfiguring r emote a uthentication 117 setup on cc-sg 1. On cc-sg, click security manager from the setup menu. When the security manager screen appears, click add external aa server . 2. In the add module screen, select ad from the module type pulldown menu. Figure 142 specifying a nam...
Page 134
118 c ommand c enter s ecure g ateway a dministrator g uide general settings on cc-sg 1. Type the ip address/hostname of the active directory server. For hostname rules, see terminology/acronyms in chapter 1: introduction . Figure 143 specifying general values for active directory server 2. Check an...
Page 135
C hapter 9: c onfiguring r emote a uthentication 119 advanced settings on cc-sg 1. If you want to configure advanced settings, click on the advanced tab. Figure 144 specifying advanced values for active directory server 2. Specify a port (default is 389 ) on which the active directory server is list...
Page 136
120 c ommand c enter s ecure g ateway a dministrator g uide 5. Specify a base dn (directory level/entry) under which the authentication search query will be executed. E xample d escription dc=raritan,dc=com the search query for the user entry will be made over the whole directory structure. Cn=admin...
Page 137
C hapter 9: c onfiguring r emote a uthentication 121 group settings on cc-sg use to retrieve groups from the ad server and import into cc-sg local database for authorization purposes. 1. Click on the groups tab. Figure 145 specifying group values for active directory server 2. Specify a base dn (dir...
Page 138
122 c ommand c enter s ecure g ateway a dministrator g uide 5. On cc-sg, in the security manager screen, click import groups… to retrieve a list of user group values stored on the active directory server. If any of the user groups are not already on the cc-sg, you can import them here and assign the...
Page 139
C hapter 9: c onfiguring r emote a uthentication 123 10. Verify the policy of the group that was imported by clicking the users tab, right-clicking on the group and selecting edit user group policies . Look under selected policies to confirm the policy that the correct policy was assigned to the gro...
Page 140
124 c ommand c enter s ecure g ateway a dministrator g uide ldap (netscape) once the cc-sg applet is started and a user name and password are entered, a query is forwarded either through cc-sg or directly to the ldap server. If the username and password match those in the ldap directory, the user is...
Page 141
C hapter 9: c onfiguring r emote a uthentication 125 2. In add module screen, select ldap from the pulldown menu, specify a name for the server, and click next . Figure 151 security manager ldap screen general tab 3. Type the ip address or hostname of the ldap server in the ip address/hostname field...
Page 142
126 c ommand c enter s ecure g ateway a dministrator g uide 11. Click test connection to test the ldap server using the given parameters. You should receive a confirmation of a successful connection. If not, review the settings carefully for errors and try again. 12. Click on the advanced tab to set...
Page 143
C hapter 9: c onfiguring r emote a uthentication 127 sun one ldap (iplanet) configuration settings if using a sun one ldap server for remote authentication, use this example for parameter settings: p arameter n ame sun o ne ldap p arameters ip address/hostname user name cn= password basedn o=organiz...
Page 144
128 c ommand c enter s ecure g ateway a dministrator g uide tacacs+ cc-sg users who are remotely authenticated by a tacacs+ server need to be created on the tacacs+ server and on cc-sg. The user’s user name on the tacacs+ server and on cc-sg must be the same, although the passwords may be different....
Page 145
C hapter 9: c onfiguring r emote a uthentication 129 2. In the add module screen, select tacacs+ from the pulldown menu, specify a name for the server, and click next . Figure 154 specifying a tacacs+ server 3. Type the ip address or hostname of the tacacs+ server in the ip address/hostname name fie...
Page 146
130 c ommand c enter s ecure g ateway a dministrator g uide radius cc-sg users who are remotely authenticated by a radius server need to be created on the radius server and on cc-sg. The user’s user name on the radius server and on cc-sg must be the same, although the passwords may be different. Ple...
Page 147
C hapter 9: c onfiguring r emote a uthentication 131 3. Type the ip address or hostname of the radius server in the ip address/hostname field. For hostname rules, see terminology/acronyms in chapter 1: introduction . 4. Type the port number in the port number field. 5. Type and confirm the shared ke...
Page 148
132 c ommand c enter s ecure g ateway a dministrator g uide generate certificate signing request the following explains how to generate a csr and a private key on cc-sg. The csr will be submitted to the certificate server who will issue a signed certificate. A root certificate will also be exported ...
Page 149
C hapter 9: c onfiguring r emote a uthentication 133 11. Type raritan in the password field if the csr was generated by cc-sg. If a different application generated the csr, use that password for that application. Note: if the imported certificate is signed by a root and subroot ca (certificate autho...
Page 150
134 c ommand c enter s ecure g ateway a dministrator g uide ip-acl this feature restricts access to cc-sg based on ip addresses. Specify an ip-access control list (ip-acl) by entering an ip address range, the group to which it applies, and an allow/deny privilege. 1. On the setup menu, click securit...
Page 151
C hapter 10: g enerating r eports 135 chapter 10: generating reports reports can be sorted by clicking on the column headers. Click on a column header such as user name, access time, etc., to sort report data by that value. The data will refresh in ascending order alphabetically, numerically, or chr...
Page 152
136 c ommand c enter s ecure g ateway a dministrator g uide 3. Click manage report data… to save or print the report. Click save to save the report to a location of your choice or print to print the report. Figure 163 manage report window 4. Click close to close the manage report window. 5. Click cl...
Page 153
C hapter 10: g enerating r eports 137 asset management report the asset management report displays data on current devices. 1. On the reports menu click asset management report. The asset management report is generated. Figure 165 asset management report 2. Click on the device type drop-down arrow t...
Page 154
138 c ommand c enter s ecure g ateway a dministrator g uide audit trail report the audit trail report displays audit logs and access in cc-sg. It captures actions such as adding, editing, or deleting devices or ports, and other modifications. Cc-sg maintains an audit trail of the following events: •...
Page 155
C hapter 10: g enerating r eports 139 6. The audit trail report is generated, displaying data about sessions that occurred during the designated time period. Figure 167 audit trail report 7. Click manage report data… to save or print the report. Click save to save the records that are displayed to a...
Page 156
140 c ommand c enter s ecure g ateway a dministrator g uide error log report cc-sg stores error messages in a series of error log files, which can be brought up and used to help troubleshoot system problems. You can filter the search criteria by date, message type, username, class, host, and level. ...
Page 157
C hapter 10: g enerating r eports 141 6. The error log report is generated, displaying data about sessions that occurred during the designated time period. Figure 169 error log report 7. Click manage report data… to save or print the report. Click save to save the records that are displayed to a csv...
Page 158
142 c ommand c enter s ecure g ateway a dministrator g uide ping report the ping report displays the status of all connections, showing devices by name and ip address. This report gives you the full accessibility picture for all devices on your system, and will supply information that could be usefu...
Page 159
C hapter 10: g enerating r eports 143 accessed devices report run the accessed devices report to view information about any accessed devices, when they were accessed, and the user who accessed them. Filters will help you define the search criteria for a more concise report. 1. On the reports menu, c...
Page 160
144 c ommand c enter s ecure g ateway a dministrator g uide 5. Click ok to run the report. Figure 172 accessed devices report 6. The accessed devices report is generated, displaying data about devices accessed during the designated time period. 7. Click manage report data… to save or print the repor...
Page 161
C hapter 10: g enerating r eports 145 group data report the group data report displays user, port, and device group information. View user groups by name and description, view port groups by name, and view device groups by name, all in one screen. 1. On the reports menu, click group data . The group...
Page 162
146 c ommand c enter s ecure g ateway a dministrator g uide user data report the user data report displays certain data on all users in the cc-sg database. From user name field you can see names of users currently in session and view details of users currently not in session. From phone field you ca...
Page 163
C hapter 10: g enerating r eports 147 users in groups report the users in group report displays data on users and the groups with which they are associated. 1. On the reports menu, click users in groups. The users in groups report is generated. Use the scroll bar to scroll through the list and view ...
Page 164
148 c ommand c enter s ecure g ateway a dministrator g uide query port report the query port report displays all ports according to port status. 1. On the reports menu, click query port. The query port screen appears. Figure 176 query port report 2. Click on one or more checkboxes to customize the p...
Page 165
C hapter 10: g enerating r eports 149 view stored reports the view stored reports displays reports that were scheduled in the task manager see section task manager in chapter 12: advanced administration . 1. On the reports menu, click view stored reports. Figure 177 view stored reports 2. Click get ...
Page 166
150 c ommand c enter s ecure g ateway a dministrator g uide locked out users report the locked out users report displays users who are currently locked out of cc-sg. You can unlock them from this report. 1. On the reports menu, click locked out users. Figure 178 locked out users report 2. Highlight ...
Page 167
C hapter 10: g enerating r eports 151 cc-noc synchronization report the cc-noc synchronization report lists all targets, along with their ip addresses, that the cc- sg subscribes to and are monitored by a cc-noc given a particular discovery date. Any new targets that are discovered in the configured...
Page 168
152 c ommand c enter s ecure g ateway a dministrator g uide.
Page 169
C hapter 11: s ystem m aintenance 153 chapter 11: system maintenance reset cc-sg use the reset commandcenter command to reset cc-sg database data – please note that this command will not reset system configuration data, such as the ip address of cc-sg. 1. On the setup menu, click reset commandcenter...
Page 170
154 c ommand c enter s ecure g ateway a dministrator g uide restore cc-sg 1. On the setup menu, click restore commandcenter. 2. When the restore commandcenter screen appears, choose if you want to click on the backup that you want to restore to your cc-sg unit, and then click ok . Figure 182 restore...
Page 171
C hapter 11: s ystem m aintenance 155 saving and uploading backup files you can also save and load cc-sg backups to and from your local pc using the restore commandcenter screen. 1. Click on the backup you wish to save to your pc, and then click download. 2. Specify a location to save your cc-sg bac...
Page 172
156 c ommand c enter s ecure g ateway a dministrator g uide refresh cc-sg display any edits or modifications made to users, ports, categories, elements, and other system components are not reflected in the system until the database is updated. If you are logged in while another user is updating the ...
Page 173
C hapter 11: s ystem m aintenance 157 upgrade cc-sg note: if you are operating a cc-sg cluster, you must remove the cluster first and upgrade each node separately.Before you can upgrade cc-sg, you must be in maintenance mode. See section maintenance mode in chapter 11: system maintenance for additio...
Page 174
158 c ommand c enter s ecure g ateway a dministrator g uide 5. Click ok to restart cc-sg or cancel to exit the screen without restarting. Once you restart cc-sg, your broadcast message appears. Figure 187 info window 6. Click ok to restart cc-sg. 7. Cc-sg will restart, and is ready for use. Shut dow...
Page 175
C hapter 11: s ystem m aintenance 159 end cc-sg session log out to exit cc-sg at the end of a session, or to refresh the database in case you or another user has made changes while you were logged in, log off from cc-sg entirely, then log in again. 1. On the session menu, click logout . The logout w...
Page 176
160 c ommand c enter s ecure g ateway a dministrator g uide scheduled tasks scheduled tasks cannot execute while cc-sg is in maintenance mode ─ please see section task manager in chapter 12: advanced administration for additional information on scheduled tasks. When cc-sg exits maintenance mode, sch...
Page 177
C hapter 12: advanced administration 161 chapter 12: advanced administration configuration manager network configuration 1. On the setup menu, click configuration manager . When the configuration manager screen appears, click on the network setup tab. Figure 192 configuration manager network setting...
Page 178
162 c ommand c enter s ecure g ateway a dministrator g uide a. Choose primary/backup mode to implement network failover and redundancy. In this mode, only one nic is active at a given point of time and only one network ip address assignment is possible. Figure 193 primary/backup network typically, b...
Page 179
C hapter 12: advanced administration 163 in this mode, cc-sg acts as a “router” or “traffic cop” between two separate ip domains; particularly when proxy mode is being used (please see connection mode, later in this chapter, for additional information). In proxy mode, active/active mode is required ...
Page 180
164 c ommand c enter s ecure g ateway a dministrator g uide 3. Click on the level to forward drop-down arrow to select a level. 4. Repeat steps 2 and 3 for secondary server fields (note that secondary server is optional). 5. Click update configuration to save the server addresses to the system. 6. C...
Page 181
C hapter 12: advanced administration 165 time/date configuration cc-sg’s time and date stamps must be accurately maintained in order to provide credibility for its device-management capabilities. Important! This time is used when scheduling tasks in task manager ⎯ see section task manager in chapter...
Page 182
166 c ommand c enter s ecure g ateway a dministrator g uide modem configuration use this screen to access cc-sg from a client machine over a dial-up connection. This method of accessing cc-sg can be used in emergency situations. Note: a modem is not available and cannot be configured on the v1 platf...
Page 183
C hapter 12: advanced administration 167 4. Click on the advanced tab. Figure 200 extra initialization commands 5. Type an initialization command in extra initialization commands that will be used by your modem to set the “carrier detection” flag. For example, type at&c for a softk56 data fax modem....
Page 184
168 c ommand c enter s ecure g ateway a dministrator g uide 4. Click next . Figure 202 new connection wizard 5. Click connect to the network at my workplace . 6. Click dial-up connection . 7. Type a name for cc-sg, for example commandcenter . Figure 203 connection name 8. Type the phone number used ...
Page 185
C hapter 12: advanced administration 169 10. In the next screen, typically you want to click my use only in the next screen to make the connection available only to yourself. 11. Click finish in the last screen to save the connection settings. Configure the call-back connection if the cc-sg uses a c...
Page 186
170 c ommand c enter s ecure g ateway a dministrator g uide transmit "ccclient^m" endproc connect to cc-sg with modem to connect to cc-sg: 1. On the start menu, click my network places . 2. Click view network connections under network tasks . 3. Double-click on the commandcenter connection. Figure 2...
Page 187
C hapter 12: advanced administration 171 7. If show terminal window was checked as described in section configure the call-back connection earlier in this chapter, then a window similar to the one below will be displayed: figure 208 after dial terminal 8. Wait 1 or 2 minutes and in a supported brows...
Page 188
172 c ommand c enter s ecure g ateway a dministrator g uide connection mode when connected to a device, you have the option to pass data back and forth directly with that device ( direct mode ) or to route all the data through your cc-sg unit ( proxy mode ). While proxy mode increases the bandwidth ...
Page 189
C hapter 12: advanced administration 173 iii. Click the add button to add the net address and mask to the screen. You may have to use the scroll bar on the right side of the screen to view the add/remove/update buttons) figure 210 configuration manager connection screen – both.
Page 190
174 c ommand c enter s ecure g ateway a dministrator g uide device settings 1. On the setup menu, click configuration manager. When the configuration manager screen appears, click on the device settings tab. 2. To update device default port, select a device type in the table and double-click on the ...
Page 191
C hapter 12: advanced administration 175 snmp simple network management protocol allows cc-sg to push snmp traps (event notifications) to an existing snmp manager on the network. Only a cc-sg administrator trained in handling an snmp infrastructure should configure cc-sg to work with snmp. Cc-sg als...
Page 192
176 c ommand c enter s ecure g ateway a dministrator g uide system log traps, which include notifications for the status of the cc unit itself, such as a hard disk failure, and application log traps for notifications generated by events in the cc application, such as modifications to a user account....
Page 193
C hapter 12: advanced administration 177 strong password rules strong password rules require users to observe strict guidelines when creating passwords, which makes the passwords more difficult to guess and, in theory, more secure. Administrators can enable or disable this feature ⎯ see the previous...
Page 194
178 c ommand c enter s ecure g ateway a dministrator g uide 6. Type an email address in lockout notification email so notification is sent to the address informing the recipient that lockout has occurred. If the field is blank, notification is not sent. 7. Type a phone number in administrator’s phon...
Page 195
C hapter 12: advanced administration 179 4. Click ok to add the new application or cancel to close the window. If you clicked ok , a search window appears. Figure 218 search window 5. Click on the look in drop-down arrow and navigate to locate the application in your system. When you find the applic...
Page 196
180 c ommand c enter s ecure g ateway a dministrator g uide 6. Modify parameters in the parameters panel and click the update button in the details panel of the screen. The parameters will be updated. 7. Click close to close the application manager screen. Delete application deleting an application ...
Page 197
C hapter 12: advanced administration 181 2. Click add to add a new firmware file. A search window appears. Figure 222 search window 3. Click on the look in drop-down arrow and navigate to locate the firmware file in your system. When you find the firmware, select it, and click open . The firmware na...
Page 198
182 c ommand c enter s ecure g ateway a dministrator g uide add a cc-noc note: to create a valid connection, the time settings on both the cc-noc and cc-sg should be synchronized. The best method of achieving this synchronization, it to use a common ntp (network time protocol) server. For this reaso...
Page 199
C hapter 12: advanced administration 183 3. Select a software version of cc-noc you want to add and click next . Version 5.1 has fewer integration features than 5.2 and only requires adding a name and an ip address. For additional information on cc-noc 5.1, please see www.Raritan.Com/support . Click...
Page 200
184 c ommand c enter s ecure g ateway a dministrator g uide to stop cc-noc from monitoring a device, it can be unmanaged – see the commandcenter noc administrator guide . Note: use the cc-noc synchronization report to view targets that the cc-sg is subscribing to. The report also displays any new ta...
Page 201
C hapter 12: advanced administration 185 important: to increase security, you must enter the passcodes in cc-noc within five minutes after they are generated on cc-sg. This will minimize the window of opportunity for intruders to breach the system with a brute-force attack. Avoid transmitting the pa...
Page 202
186 c ommand c enter s ecure g ateway a dministrator g uide 2. Highlight a cc-noc in the list and click edit . The edit cc-noc configuration screen appears. Figure 229 edit cc-noc configuration screen 3. Refer to the previous section add a cc-noc for field details. Launch cc-noc to launch cc-noc fro...
Page 203
C hapter 12: advanced administration 187 delete a cc-noc to remove and unregister a cc-noc in cc-sg, do the following. 1. On the commandcenter noc menu, click configuration . The cc-noc configuration screen appears. Figure 231 delete cc-noc screen 2. Highlight a cc-noc in the list and click delete ....
Page 204
188 c ommand c enter s ecure g ateway a dministrator g uide create a cluster in the event of a failover, the administrator should send an email to all cc-sg users, notifying them to use the ip address of the “new” primary cc-sg node. Important: it is recommended to backup your configuration on both ...
Page 205
C hapter 12: advanced administration 189 set secondary cc-sg node 1. Click discover commandcenters to scan and display all cc-sg appliances on the same subset as your one you are currently using. Alternatively, you can add a cc-sg, perhaps from a different subnet, by specifying an ip address in comm...
Page 206
190 c ommand c enter s ecure g ateway a dministrator g uide remove secondary cc-sg node 1. To remove secondary node status from a cc-sg unit and reassign it to a different unit in your configuration, select the secondary cc-sg node in the cluster configuration table and click remove “backup” node. 2...
Page 207
C hapter 12: advanced administration 191 set advanced settings to configure advanced settings of a cluster configuration: 1. Select the primary node just created. 2. Click advanced . The advanced settings window appears. Figure 236 cluster configuration advanced settings 3. For time interval , enter...
Page 208
192 c ommand c enter s ecure g ateway a dministrator g uide • outlet port power management (power on/off/recycle outlet ports) • generate all reports (html or csv formats) • purge logs scheduling sequential tasks you may want to schedule tasks sequentially to confirm that expected behavior was actua...
Page 209
C hapter 12: advanced administration 193 create a new task to schedule a new task: 1. On the setup menu, click task manager . Figure 237 task manager 2. Click new . Figure 238 create task 3. In the main tab, type a name (1-32 characters, alphanumeric characters or underscores, no spaces) and descrip...
Page 210
194 c ommand c enter s ecure g ateway a dministrator g uide 4. Click on the task data tab and from the pulldown menu, select the task to be scheduled, such as upgrade device firmware . Note that the fields requiring data will vary according to the task selected. With the exception of restart device ...
Page 211
C hapter 12: advanced administration 195 8. Change own password in chapter 7: adding users and user groups . If an email was not configured, then this field is blank. By default, email is sent if the task was successful. To notify the recipient of failed tasks, click the on failure checkbox. Figure ...
Page 212
196 c ommand c enter s ecure g ateway a dministrator g uide 4. To view the history of a task, select a task and click task history . Figure 243 task history 5. To view details of a task, double-click on a task. Figure 244 task details note: if a task is changed or updated, its prior history no longe...
Page 213
C hapter 12: advanced administration 197 notification manager use notification manager to configure an external smtp server so notifications can be sent from cc-sg. Notifications are used to email reports that have been scheduled, email reports if users are locked out, email status of failed or succ...
Page 214
198 c ommand c enter s ecure g ateway a dministrator g uide ssh access to cc-sg use secure shell (ssh) clients, such as putty or openshh client, to access a command line interface to ssh (v2) server on cc-sg. Only a subset of cc-sg commands is provided via ssh to administer devices and cc-sg itself....
Page 215
C hapter 12: advanced administration 199 4. A shell prompt appears. Type ls to display all commands available from ssh. Figure 248 cc-sg commands via ssh 5. Typing help or ? Provides the syntax and description of all available commands. Figure 249 ssh help.
Page 216
200 c ommand c enter s ecure g ateway a dministrator g uide 6. Typing the command with the –h switch displays help for that command, such as listfirmwares –h. Figure 250 ssh listfirmwares help command tips the following describes several nuances of the ssh commands: • for commands that pass an ip ad...
Page 217
C hapter 12: advanced administration 201 create a ssh connection to an sx device you can create an ssh connection to an sx device to perform administrative operations on the device. Once connected, the administrative commands supported by the sx device are available. Note: before you can connect, en...
Page 218
202 c ommand c enter s ecure g ateway a dministrator g uide connect to a serial port connect to a serial port to access a target server. You can access serial ports on a sx, ksx, or ip- reach device. The ssh connection to the serial ports are in proxy mode. 1. Type listports to view the port ids. Fi...
Page 219
C hapter 12: advanced administration 203 3. Once connected to the port, type the default escape keys of ‘ ~ ’ followed by a dot ‘ . ’. An intermediate prompt, typically named after port name, is displayed, for example testport> . At this intermediate prompt, you can enter specific commands or aliase...
Page 220
204 c ommand c enter s ecure g ateway a dministrator g uide diagnostic console the diagnostic console is a standard, non-graphical interface that provides local access to cc- sg. It can be accessed from a serial or kvm port, or from secure shell (ssh) clients, such as putty or openssh client. Two lo...
Page 221
C hapter 12: advanced administration 205 accessing status console entering a password to access the status console is not required, but can be enforced if desired. 1. After login as: , type status . Figure 256 login to status console the read-only status console is displayed. This screen dynamically...
Page 222
206 c ommand c enter s ecure g ateway a dministrator g uide accessing administrator console at the time of logging into administrator console, all information displayed is “static”. If configuration changes occur through the cc-sg gui or the diagnostic console, you need to re- login to administrator...
Page 223
C hapter 12: advanced administration 207 navigating administrator console press.. T o … ctrl+c or ctrl+q to exit diagnostic console. Ctrl+l refresh screen and update information. Tab move to next available option. Space select current option. Arrow keys allows you to move to various options. Mouse a...
Page 224
208 c ommand c enter s ecure g ateway a dministrator g uide 3. Click save as default at the bottom of the screen or press the tab key and press enter once save as default is highlighted. Press ^q or ^c to exit. The pre-login and message of the day have three separate buffers or areas: • admin consol...
Page 225
C hapter 12: advanced administration 209 figure 263 edit status console config 3. Click save at the bottom of the screen or press the tab key and press enter once save is highlighted. Press ^q or ^c to exit. Editing network interfaces configuration (network interfaces) in network interface configura...
Page 226
210 c ommand c enter s ecure g ateway a dministrator g uide 2. If this is the first time accessing cc-sg and the network interfaces have not been configured, it is strongly recommended to use cc-sg gui to configure them instead of configuring them here. If the network interfaces have already been co...
Page 227
C hapter 12: advanced administration 211 ping an ip address (network interfaces) use ping to check that the connection between your computer and a particular ip address (domain) is working correctly. 1. To ping an ip address or hostname, click operation , network interfaces , then ping . Figure 266 ...
Page 228
212 c ommand c enter s ecure g ateway a dministrator g uide using traceroute (network interfaces) traceroute is often used for network troubleshooting. By showing a list of routers traversed, it allows you to identify the path taken from your computer to reach a particular destination on the network...
Page 229
C hapter 12: advanced administration 213 active/active network settings where each interface is attached to a separate ip domain-see section network configuration in chapter 12: advanced administration for additional information. Click with the mouse or use the tab , ↓↑ keys to navigate and press th...
Page 230
214 c ommand c enter s ecure g ateway a dministrator g uide 2. Click with the mouse or use the ↓↑ keys to navigate and press the enter key to select a log file (marked with an x) . More than one log file can be viewed at a time. (some log files are not available; a warning dialog will appear and the...
Page 231
C hapter 12: advanced administration 215 3. When view is selected with merged windows, the logviewer displays: figure 272 selecting log files to view 4. While viewing log files, type ctrl+c to return to the previous screen. 5. If desired, you can change colors in a log file to highlight what is impo...
Page 232
216 c ommand c enter s ecure g ateway a dministrator g uide 7. If desired, you can filter the log file with a regular expression. Type e to add or edit a regular expression and select a log from the list if you have chosen to view several. Figure 275 adding expressions in log files 8. Type a to add ...
Page 233
C hapter 12: advanced administration 217 9. Select f1 to get help on all logviewer options. Pressing ctl+c and ctl+q (as well as a plain q ) terminates this logviewer session. Figure 277 getting help (f1) restarting cc-sg (admin) you can restart cc-sg, which will log off all current cc-sg users and ...
Page 234
218 c ommand c enter s ecure g ateway a dministrator g uide 2. Either click restart cc-sg application or press enter. Figure 279 restarting cc-sg in diagnostic console rebooting cc-sg (admin) this option will reboot the entire cc-sg, which simulates a power cycle. Users will not receive a notificati...
Page 235
C hapter 12: advanced administration 219 2. Either click reboot system or press enter to reboot cc-sg. A screen to confirm this action appears and needs to be acknowledged before this operation will commence. Figure 281 rebooting cc-sg in diagnostic console changing passwords (admin) this option pro...
Page 236
220 c ommand c enter s ecure g ateway a dministrator g uide in password configuration , enter the number of passwords that will be remembered. This is the password history, which discourages password reuse and ensures that the new password has not been used within the specified number of previous pa...
Page 237
C hapter 12: advanced administration 221 account configuration by default, the status account does not require a password, but you can configure it to have one here. Other aspects of the admin password can be configured and the field support accounts can be enabled or disabled. 1. To configure accou...
Page 238
222 c ommand c enter s ecure g ateway a dministrator g uide 4. For the admin and status accounts, you can configure: s etting d escription user \ user name this is the current user name or id for this account. (this may be operator changeable in a future release.) last changed (read-only). This is t...
Page 239
C hapter 12: advanced administration 223 2. Either click refresh or press enter to refresh the display. Refreshing the display is especially useful when upgrading or installing and you want to see the progress of the raid disks as they are being rebuilt and being synchronized. Figure 287 displaying ...
Page 240
224 c ommand c enter s ecure g ateway a dministrator g uide 2. View the total running, sleeping, total number and processes that have stopped. Figure 289 displaying cc-sg processes in diagnostic console 3. Type h to bring up an extensive help screen for the top command. The standard f1 help key is n...
Page 241
A ppendix a: s pecifications 225 appendix a: specifications (g1, v1) g1 platform general specifications form factor 1u dimensions (dxwxh) 22.1”x 17.32” x 1.75” 563mm x 440mm x 44mm weight 24.07lb (10.92kg) power redundant, hot-swappable power supplies, auto-sensing 110/220 v – 2.0a mean time between...
Page 242
226 c ommand c enter s ecure g ateway a dministrator g uide n on -o perating temperature 0 - 30 deg c; 32 – 104 deg f humidity 10% - 90% rh altitude operate properly at any altitude between 0 to 10,000 feet, storage 40,000 feet (est.) vibration 5-55-5 hz, 0.38mm, 1 minutes per cycle; 30 minutes for ...
Page 243
A ppendix a: s pecifications 227 v1 platform general specifications form factor 1u dimensions (dxwxh) 24.21”x 19.09” x 1.75” 615mm x 485mm x 44mm weight 23.80lb (10.80kg) power single supply (1 x 300 watt) operating temperature 10 ℃ - 35 ℃ (50 ℉ - 95 ℉ ) mean time between failure (mtbf) 36,354 hours...
Page 244
228 c ommand c enter s ecure g ateway a dministrator g uide n on -o perating temperature -40 - +60 (-40 -140 ) humidity 5% - 95% rh altitude operate properly at any altitude between 0 to 10,000 feet, storage 40,000 feet (estimated) vibration 5-55-5 hz, 0.38mm,1 minutes per cycle; 30 minutes for each...
Page 245
A ppendix b : cc - sg and network configuration 229 appendix b: cc-sg and network configuration introduction this appendix discloses network requirements (addresses, protocols and ports) of a typical commandcenter secure gateway (cc-sg) deployment. It provides what you need to know and how to config...
Page 246: Cc-Sg
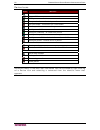
230 c ommand c enter s ecure g ateway a dministrator g uide figure 290 cc-sg deployment elements internet (unsecured network) cc-sg cluster peer cc clients internal network firewall cc-noc cc clients raritan device serial kvm out-of-band target access in-band access vpn raritan device cc-sg internal...
Page 247
A ppendix b : cc - sg and network configuration 231 cc-sg communication channels the communication channels are partitioned as follows: • cc-sg ↔ raritan devices • cc-sg ↔ cc-sg clustering (optional) • cc-sg ↔ infrastructure services • clients ↔ cc-sg • clients ↔ targets (direct mode) • clients ↔ ta...
Page 248
232 c ommand c enter s ecure g ateway a dministrator g uide each cc-sg in the cluster may be on a separate lan. However, the inter-connection between the units should be very reliable and not prone to periods of congestion. Communication direction port number protocol purpose configurable? Cc-sg → l...
Page 249
A ppendix b : cc - sg and network configuration 233 the first mode is the primary means for users and administrators to connect to cc-sg. The other two modes are less frequently used. These modes require the following networking configuration: communication direction port number protocol purpose con...
Page 250
234 c ommand c enter s ecure g ateway a dministrator g uide cc-sg & snmp simple network management protocol (snmp) allows cc-sg to push snmp traps (event notifications) to an existing snmp manager on the network. Cc-sg also supports snmp get/set operations with third-party enterprise management solu...
Page 251
A ppendix b : cc - sg and network configuration 235 security and open port scans as part of the cc-sg quality assurance process, several open port scanners are applied to the product and raritan computer makes certain that its product is not vulnerable to these known attacks. All the open or filtere...
Page 253
A ppendix c: i nitial s etup p rocess o verview 237 appendix c: initial setup process overview pre-requisites: • add devices with category/element clearly identified. • add ports with category/element clearly identified. Create group(s)/add user(s) 1. Add device group with rule based on category/ele...
Page 254
238 c ommand c enter s ecure g ateway a dministrator g uide.
Page 255
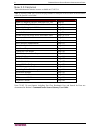
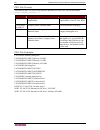
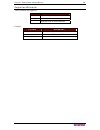
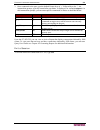
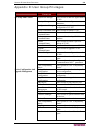
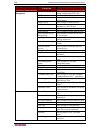
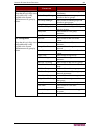
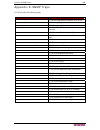
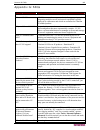
A ppendix d: u ser g roup p rivileges 239 appendix d: user group privileges u sers g roup p rivilege a vailable c ommands u ser c apability application manager users are able to add new application to cc-sg. Security manager users are able to configure security parameters. Configuration manager user...
Page 256
240 c ommand c enter s ecure g ateway a dministrator g uide u sers g roup p rivilege a vailable c ommands u ser c apability configuration manager users are able to change general device settings configuration of cc-sg. Add device users are able to add new devices. Edit device users are able to modif...
Page 257
A ppendix d: u ser g roup p rivileges 241 u sers g roup p rivilege a vailable c ommands u ser c apability association manager users are able to associate categories and elements. Device group manager users are able to rename groups and add rules to device groups. Port group manager users are able to...
Page 258
242 c ommand c enter s ecure g ateway a dministrator g uide.
Page 259
A ppendix e: snmp t raps 243 appendix e: snmp traps cc-sg provides the following traps: snmp t rap d escription ccdeviceupgrade cc-sg has upgraded the firmware on a device. Ccimageupgraderesults cc-sg image upgrade results. Ccimageupgradestarted cc-sg image upgrade started. Ccincompatibledevicefirmw...
Page 260
244 c ommand c enter s ecure g ateway a dministrator g uide.
Page 261
A ppendix f: t roubleshooting 245 appendix f: troubleshooting • in order to launch cc-sg from your web browser, it requires a java plug-in. If your machine has an incorrect version, cc-sg will guide you through the installation steps. If your machine does not have a java plug-in, cc-sg cannot automa...
Page 262
246 c ommand c enter s ecure g ateway a dministrator g uide port and policy group creation failure the default port groups and policies created in the association wizard are named after the elements of a category. If the element names are not unique, the default port groups and policies cannot be cr...
Page 263
A ppendix g: faq s 247 appendix g: faqs q uestion a nswer general what is cc-sg? Cc-sg is a network management device for aggregating and integrating multiple servers and network equipment typically deployed in a datacenter and which are connected to a raritan ip-enabled product. Why would i need cc...
Page 264
248 c ommand c enter s ecure g ateway a dministrator g uide q uestion a nswer to add a console/serial port to cc-sg? The following conditions are met: - the dominion unit is active. - the dominion unit has not reached the maximum number of configured user accounts. Which version of java will raritan...
Page 265
A ppendix g: faq s 249 q uestion a nswer if we had more than 1,000 users, how would this be managed? That is, do you support active directory? Cc-sg works with microsoft active directory, sun iplanet or novell edirectory. If a user account already exists in an authentication server, then cc-sg suppo...
Page 266
250 c ommand c enter s ecure g ateway a dministrator g uide q uestion a nswer track down to who switched on or off a power plug? Through the cc-sg gui can be logged to audit logs. Performance as a cc-sg administrator, i added over 500 ports and assigned all of them to me. Now it takes a long time to...
Page 267
A ppendix g: faq s 251 q uestion a nswer or simply box level? Switches, the tightness of integration will vary. How would i mitigate the restriction of four simultaneous paths through any ip-reach box, including the roadmap for the potential 8-path box? Currently, the best possible implementation is...
Page 268
252 c ommand c enter s ecure g ateway a dministrator g uide 255-80-5140-00
Page 269
A ppendix g: faq s 253.
Page 270
North american headquarters raritan 400 cottontail lane somerset, nj 08873 u.S.A. Tel. (732) 764-8886 or (800) 724-8090 fax (732) 764-8887 email: sales@raritan.Com website: raritan.Com raritan nc 4901 waters edge dr. Suite 101 raleigh, nc 27606 tel. (919) 277-0642 email: sales.Nc@raritan.Com website...