TANDBERG Border Controller User Manual - page 117
TANDBERG Border Controller User Guide
Page 117 of 118
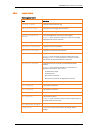
25.Index
—A—
about ...........................................................................97
account
Administrator Account ........................................19
Root Account .......................................................19
Active Directory...........................................................99
alias .................................. 20, 21, 39, 75, 76, 91, 107
alias transformation...................................................27
Allow List ....................................................... 39, 76, 88
alternates ................................................21, 24, 76, 85
ARQ ............................................................................107
Assent protocol ............................................. 31, 32, 84
authentication.......24, 39, 41, 42, 43, 56, 59, 81, 88
authentication and CPL .............................................56
authentication credential...........................................75
authentication mode..................................................75
automatic discovery ............................................ 16, 76
—B—
backups................................................................ 19, 68
bandwidth control............................24, 33, 35, 36, 88
BIND.............................................................................98
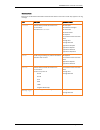
—C—
CA certificate......................................................43, 102
cables ..........................................................................15
call disconnection................................................ 55, 90
call policy.....................................................................56
call routed mode.................................................. 54, 81
call transfer................................................... 54, 81, 88
calls to unknown IP addresses..................................29
central log server........................................................67
certificates ..................................................................43
clear.............................................................................97
command line interface...................................... 17, 56
command reference...................................................71
concurrent calls ..........................................................12
CPL (Call Processing Language)......................... 57, 59
CPL examples ...................................................... 59, 60
—D—
default ENUM zone.....................................................47
default IP address ............................................... 16, 89
default links ................................................................89
default password................................................. 16, 19
Deny List........................................................ 39, 76, 89
dial plan
enforced ...............................................................42
flat.........................................................................21
hierarchical ..........................................................21
structured.............................................................21
directory gatekeeper ..................................................21
disconnect call............................................................90
DNS............................................ 16, 23, 44, 47, 53, 76
DNS lookup .......................................................... 47, 76
DNS zone............................................................47, 107
documentation ........................................................... 15
domain ..................................................................16, 76
domain, local ........................................................20, 76
down-speed ..........................................................35, 76
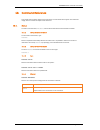
—E—
E.164..............................................21, 47, 49, 99, 107
ENUM ....................................................................47, 49
environmental issues............................................... 8, 9
ethernet ...................................................... 16, 76, 104
event levels................................................................. 61
event log ................................... 61, 62, 63, 65, 67, 97
event log verbosity ..................................................... 61
Expressway ...........................................................12, 31
external manager .............................................. 72, 107
—F—
fallback alias............................................................... 29
feedback ........................................................72, 90, 91
firewall...................................................29, 31, 36, 107
firewall traversal... 12, 29, 31, 36, 37, 51, 52, 84, 85
—G—
Gatekeeper ...........................................51, 76, 85, 107
Gatekeeper discovery ...................................16, 20, 76
Gatekeeper zone......................................................107
gateway .............................................................. 16, 107
—H—
H.235 - see also authentication ...................... 41, 106
H.323 ....................................................21, 76, 99, 106
H.323 Annex 0 ........................................................... 46
H.323 URI .............................................................47, 49
H.350 - see also LDAP ............................... 41, 42, 106
H.460 18/19.......................................... 20, 31, 61, 84
h323cs........................................................................ 46
h323ls......................................................................... 46
hop count.................................................................... 85
HP OpenView .............................................................. 82
HTTP(S) ..........................................................16, 68, 79
—I—
initial configuration .................................................... 16
insufficient bandwidth .........................................35, 76
IP
dialling............................................................52, 76
initial configuration .......................................16, 72
port....................................................................... 85
v4....................................................................20, 79
v6....................................................................20, 79
IP address ........................................ 17, 29, 76, 85, 92
IP address, default ........................................16, 85, 89
ITU standards ...........................................................104
—L—
LAN interface .............................................................. 12
LDAP......................................................................41, 72
LDAP over TLS ................................................... 43, 100