D-Link DI-304 User Manual - page 71
DI-304/DI-304M ISDN Remote Router
63
♦
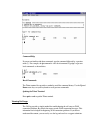
Protocol – Specify the protocol(s) this filter rule will apply to.
♦
IP Address – Specify a source and destination IP address for this filter rule to
apply to. Placing the symbol "!" before a particular IP Address will prevent this
rule from being applied to that IP address. It is equal to the logical NOT
operator.
♦
Subnet Mask – Specify the Subnet Mask for the IP Address column for this
filter rule to apply to.
♦
Operator – The operator column specifies the port number settings. If the
Start Port is empty, the Start Port and the End Port column will be ignored.
The filter rule will filter out any port number.
= : If the End Port is empty, the filter rule will set the port
number to be the value of the Start Port. Otherwise, the
port number ranges between the Start Port and the End
Port (including the Start Port and the End Port).
!= : If the End Port is empty, the port number is not equal
to the value of the Start Port. Otherwise, this port number
is not between the Start Port and the End Port (including
the Start Port and End Port).
> : Specify the port number is larger than the Start Port
(includes the Start Port).
< : Specify the port number is less than the Start Port
(includes the Start Port).
♦
Keep State – also may be quoted as SPI (stateful packets inspection),is a
mechanism used to drop the invalid incoming packets. When checked, protocol
information about the TCP/UDP/ICMP communication sessions will be kept
by the IP Filter/Firewall (the Firewall Protocol option requires that TCP or
UDP or TCP/UDP or ICMP be selected for this to operate correctly).
♦
Source Route – When checked, the IP options of source routing will be
applied for the rule. In general please do not enable this option for higher
security policy.
♦
Fragments – Specify a fragmented packets action.
? Don't Care - Specify no fragment options in the filter rule.
? Unfragmented - Apply the rule to unfragmented packets.
? Fragmented - Apply the rule to fragmented packets.
? Too Short - Apply the rule only to packets that are too short to contain
a complete header.
Some fragmented packets are malicious so it may be necessary to hinder
the fragmented packets for higher security policies.
Restricting Unauthorized Internet Services