F-SECURE ANTI-VIRUS FOR MICROSOFT EXCHANGE 8.00 - Administrator's Manual - page 237
CHAPTER 9
237
The Logging Directory
The logging directory is defined when installing the application. It can be
changed by clicking
Browse
.
9.5.3
The Action.log file
The action log is collecting data about the actions done by the firewall
continuously. It is a normal text file with the maximum size of 10 MB, and
can be viewed with any text editing application capable of reading large
files. The action log file can be cleared and removed anytime, so it is easy
to restart into a new file if the file size gets too big. You can view the action
log by clicking
Show Action Log
on the Logging page.
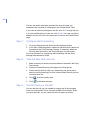
Practical examples of how to read the action log:
Change of firewall policy, for example a security level change:
07/16/03 15:48:01,success,general,daemon,Policy file has been
reloaded.
Opening a local connection, inbound or outbound:
The fields are:
Home users can use the packet logging to record evidence of
intrusion attempts.
The action log uses the standard unix syslog format
1
2
3
4
5
6
7
8
9
10
07/16/03
16:54:41
info
appl control
C:\WINNT\system32\services.exe
allow
send
17
10.128.128.14
137
1. Date
2. Time
3. Type
4. Internal Reason
5. Name of application
6. Application control action
7. Network action
8. Protocol
9. Remote ip
10. Remote port