F-SECURE ANTI-VIRUS FOR MICROSOFT EXCHANGE 6.62 - Administrator's Manual - page 290
of
397
290
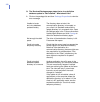
Figure 6-31 Proxy Configuration page
Proxy Configuration
Use proxy server
Specify whether F-Secure Content Scanner
Server uses a proxy server when it connects to
the threat detection center.
Proxy server address Specify the address of the proxy server.
Proxy server port
Specify the port number of the proxy server.
Authentication
method
Specify the authentication method to use to
authenticate to the proxy server.
NoAuth - The proxy server does not require
authentication.
Basic - The proxy uses the basic authentication
scheme.
NTLM - The proxy uses NTLM authentication
scheme.