IBM Proventia Network Enterprise User Manual - page 178
Chapter 12: Interpreting Scan Results
178
IBM Internet Security Systems
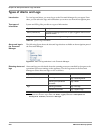
Viewing Vulnerabilities by Vuln Names
Introduction
Vulnerability names provides high-level information about the types of vulnerabilities
detected on your network.
Benefits
You can sort your view by most severe vulnerabilities to identify the most to least
important vulnerabilities on your network or by priority of fix.
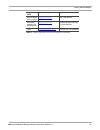
Field descriptions
The following table describes the fields and descriptions for this vulnerability view:
Field
Description
Tag Name
Use this filter to display or suppress events that match one or
more tag names. You can filter on tag names from the Site
database or on user-defined tag names.
Severity
Use this filter to display events according to their level of severity.
Status
You use the Status filter differently for events and vulnerabilities.
•
Events: The Status column indicates the impact of the event.
•
Vulnerabilities: The Status column indicates whether the
vulnerability was found.
Use this filter to show only the statuses that interest you.
Event Count
Use this filter to determine which events occur most frequently.
Target Count
Use to filter by the count of target hosts.
Object Count
Use to filter events according to the Object Count column in the
analysis views. SiteProtector calculates the Object Count
according to the number of objects that are associated with each
row of data in the analysis view. This filter filters data only in views
that contain the Object Count column. For example, if you apply
this filter to the Attacker view, SiteProtector would apply the
criteria you specified to each IP address (or row) that appears in
the view.
Latest Event
Use to filter events according to the Latest Event column in the
analysis views. SiteProtector calculates the time and date for the
latest event on each row of data in an analysis view. This filter
filters data only in views that contain the Latest Event column. For
example, if you apply this filter to the Event Name view,
SiteProtector would apply criteria you specified to each Tag name
(or row) that appears in the view.
Table 64: Vulnerability analysis–name fields