IBM Proventia Network Enterprise User Manual - page 65
Enterprise Scanner User Groups
65
IBM Proventia Network Enterprise Scanner User Guide, Version 1.3
Enterprise Scanner User Groups
Introduction
This topic describes the predefined user groups in the SiteProtector system that apply to
Enterprise Scanner users. You add Enterprise Scanner users to the SiteProtector system
and define their Enterprise Scanner permissions just as you do for any type of the
SiteProtector system user.
All predefined user
groups
The SiteProtector system includes the following predefined User Groups:
●
Administrator
●
Analyst
●
Assessment Manager
●
Desktop Manager
●
Network Manager
●
Operator
●
Server Manager
User groups for
Enterprise Scanner
The SiteProtector User Group intended specifically for Enterprise Scanner users is
Assessment Manager; however, the Administrator and Analyst groups also provide full
access to Enterprise Scanner permissions. You can assign Enterprise Scanner permissions
to other users or other groups.
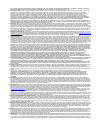
Scanning without
full permissions
To perform any Enterprise Scanner scan with SiteProtector 2.0, Service Pack 6.1
(SiteProtector DBSP 6.31 or later, a user must have permission to view the Network
Locations policy. This permission is granted for the predefined user groups that provide
full Enterprise Scanner permissions. If you define users or user groups with restricted
permissions, you must grant this permission explicitly. The way you grant permission is
based on the inheritance behavior of your policy:
Important:
Users who do not have permission to view the Network Locations policy—
either through group association or by a specific grant—cannot run Enterprise Scanner
scans. If those users try to run a scan, they receive an error message that the scan cannot be
run because a policy is not defined.
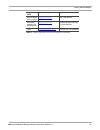
If you…
Then you…
do not change the inheritance
behavior of the policy
can define the permission once at the Site level.
change the inheritance
behavior of the policy
you must grant the permission for the group where you need the
permission and for all the groups above it in the hierarchy.
Table 19: Granting permission to the Network Locations policy