IBM Proventia Network Enterprise User Manual - page 96
Chapter 6: Defining Background Scans
96
IBM Internet Security Systems
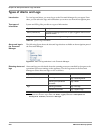
Key Parameters for Defining Scan Jobs
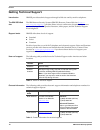
Introduction
If you understand how to define ad hoc and background scans with Enterprise Scanner,
you can use this topic to quickly reference key scanning parameters.
Key parameters
The following table describes how to find and configure key parameters to define scans:
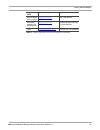
If you want to…
Then, open the…
And then…
define perspectives to use for
your Site
Network Locations policy for
the Site
add a new Network Location
Name.
define the perspective of an
agent
ESM policy for the agent
select the network location
from the Perspective
(Network location) list.
define the perspective from
which you want to scan a group
with a background scan
Scan Control policy for the
group to scan
select the perspective from the
Perform background scans
from this perspective
(Network location) list.
define the perspective from
which you want to scan a group
with an ad hoc scan
Remote Scan (ad hoc) policy
(right-click a group, and then
select Scan from the pop-up
menu)
select the perspective from the
Perform one-time scan from
this perspective (network
location) list.
define the number of assets in
a subgroup to scan in one
subtask
a
a. For guidance in determining the size of subtasks, see “Considerations for Subtask Sizes” on page 111.
ESM policy for the agent
change the Maximum IPs per
discovery subtask and/or the
Maximum assets per
assessment subtask boxes.
define the duration of the
scanning cycle—the amount of
time that passes before the
scans automatically run again
and refresh the data—for a
group of assets
Scan Control policy for the
group to scan
configure Cycle start date and
Cycle duration for discovery
and for assessment scans.
define the windows when
scanning is allowed
Scan Window policy for the
group to scan
configure the
Discovery
Windows and the
Assessment Windows.
Table 34: Key scanning parameters