IBM Proventia Network Enterprise User Manual - page 180
Chapter 12: Interpreting Scan Results
180
IBM Internet Security Systems
Assessment Report Descriptions
Introduction
This topic provides a brief description of each assessment report.
Available
assessment
reports
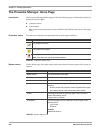
The Assessment reports that appear on the Report tab are as follows:
Report
Description
Asset Assessment Detail
A detailed list of vulnerabilities and services for each asset,
including vulnerability remedies and references.
Asset Assessment Summary
A list of discovered assets, and for each asset, its network
services and vulnerabilities.
Operating System Summary
Percentage and number of assets by operating system discovered
during an automated network scan.
Operating System Summary
by Asset
A list of assets scanned, and for each asset, its operating systems.
Service Summary
A list of services discovered.
Service Summary by Asset
A list of services discovered for each asset scanned.
Top Vulnerabilities
A list of the top vulnerabilities, by frequency, for a specified group
and time.
Vulnerability by Asset
A lists of the top assets by number of vulnerabilities for a specified
group and time.
Vulnerability by Group
A comparison of vulnerabilities across subgroups of a selected
group.
Vulnerability by OS
A comparison of vulnerability counts by Operating Systems.
Vulnerability Counts
A list detected of vulnerabilities by total number and by
percentage.
Vulnerability Counts by Asset
Number of vulnerabilities discovered for each asset by severity.
Vulnerability Detail by Asset
A detailed list of all vulnerability information available for each
asset.
Vulnerability Differential
A summary comparison of vulnerabilities and details for each
asset.
Vulnerability Names by Asset
A list of vulnerability names for each asset.
Vulnerability Remedies by
Asset
A list of vulnerabilities their remedies for each asset.
Vulnerability Summary by
Asset
A list of vulnerabilities and their descriptions for each asset.
Vulnerable Assets
A lists of assets by criticality for each vulnerability.
Table 65: Assessment report descriptions