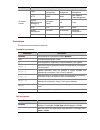
H3C LS-3100-52P-OVS-H3 Operation Manual - page 1277
4-2
packet forwarding authority must be taken out; otherwise, this means too many tokens have been used
— the traffic is in excess of the specification.
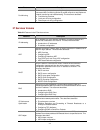
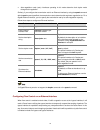
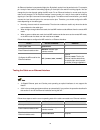
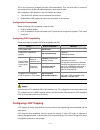
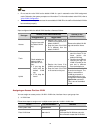
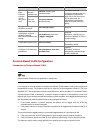
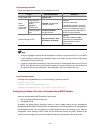
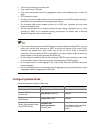
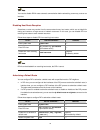
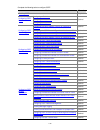
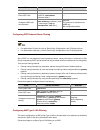
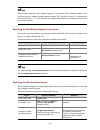
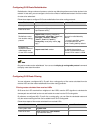
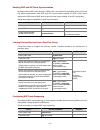
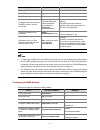
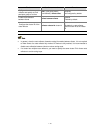
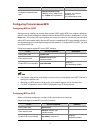
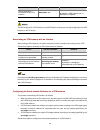
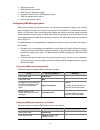
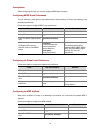
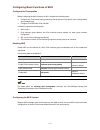
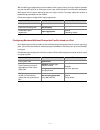
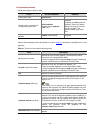
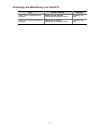
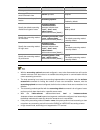
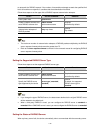
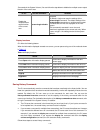
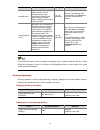
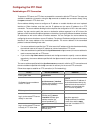
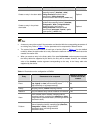
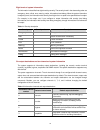
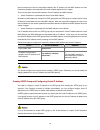
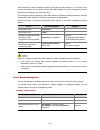
Complicated Evaluation
You can set two token buckets (referred to as the C bucket and E bucket respectively) in order to
evaluate more complicated conditions and implement more flexible regulation policies. For example,
traffic policing uses four parameters:
z
CIR: Rate at which tokens are put into the C bucket, that is, the average packet transmission or
forwarding rate allowed by the C bucket.
z
CBS: Size of the C bucket, that is, transient burst of traffic that the C bucket can forward.
z
Peak information rate (PIR): Rate at which tokens are put into the E bucket, that is, the average
packet transmission or forwarding rate allowed by the E bucket.
z
Excess burst size (EBS): Size of the E bucket, that is, transient burst of traffic that the E bucket can
forward.
In each evaluation, packets are measured against the buckets:
z
If the C bucket has enough tokens, packets are colored green.
z
If the C bucket does not have enough tokens but the E bucket has enough tokens, packets are
colored yellow.
z
If neither the C bucket nor the E bucket has sufficient tokens, packets are colored red.
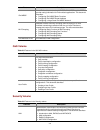
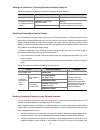
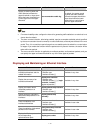
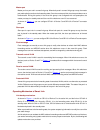
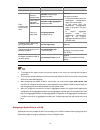
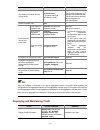
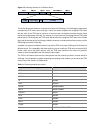
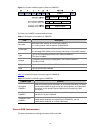
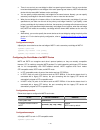
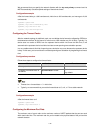
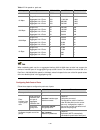
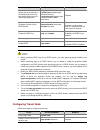
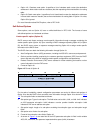
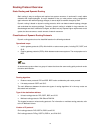
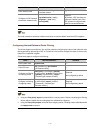
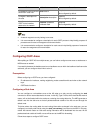
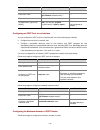
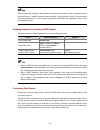
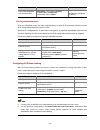
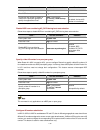
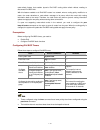
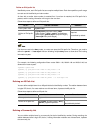
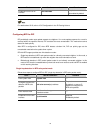
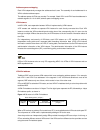
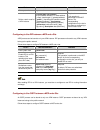
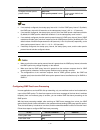
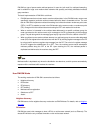
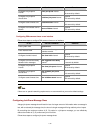
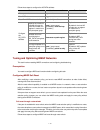
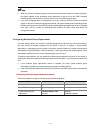
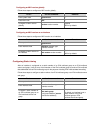
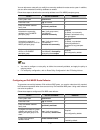
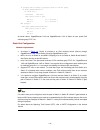
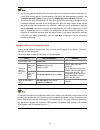
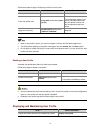
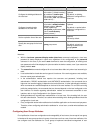
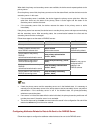
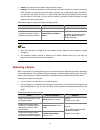
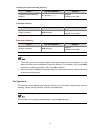
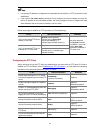
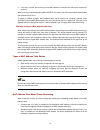
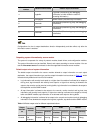
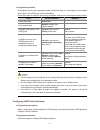
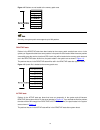
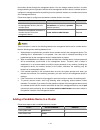
Traffic Policing
The typical application of traffic policing is to supervise the specification of certain traffic into the network
and limit it within a reasonable range, or to "discipline" the extra traffic. In this way, the network
resources and the interests of the operators are protected. For example, you can limit HTTP packets to
be within 50% of the network bandwidth. If the traffic of a certain connection is excess, traffic policing
can choose to drop the packets or to reset the priority of the packets.
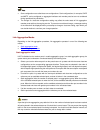
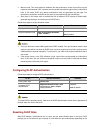
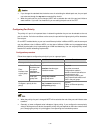
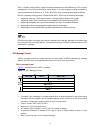
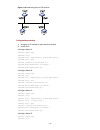
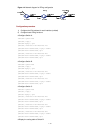
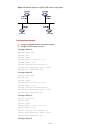
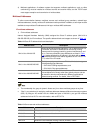
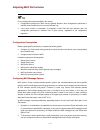
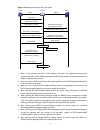
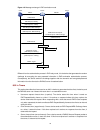
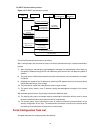
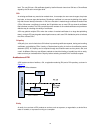
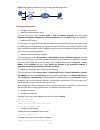
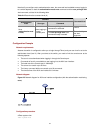
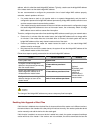
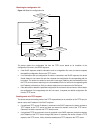
Figure 4-1 Diagram for TP
Token
bucket
Packets dropped
Packet
classification
Packets to be sent
through this interface
Packets sent
Tokens are put into the
bucket at the set rate
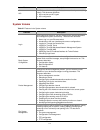
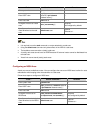
Traffic policing is widely used in policing the traffic into the network of internet service providers (ISPs).
Traffic policing can classify the policed traffic and perform pre-defined policing actions based on
different evaluation results. These actions include:
z
Forwarding conforming packets or non-conforming packets.