H3C LS-3100-52P-OVS-H3 Operation Manual - page 355
3-7
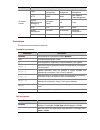
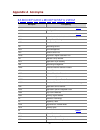
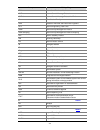
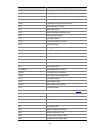
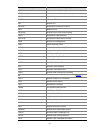
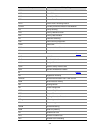
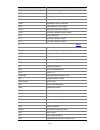
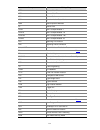
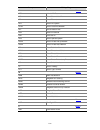
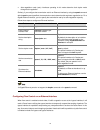
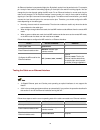
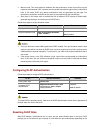
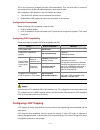
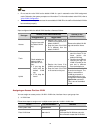
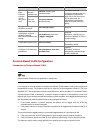
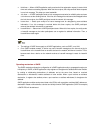
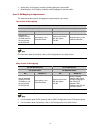
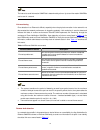
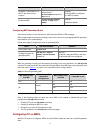
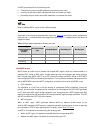
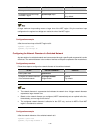
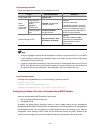
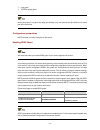
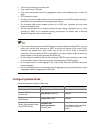
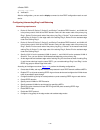
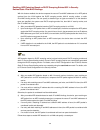
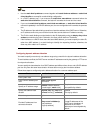
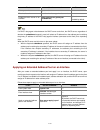
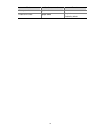
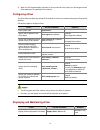
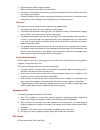
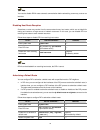
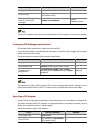
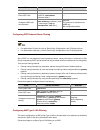
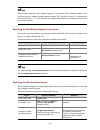
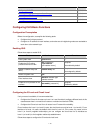
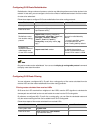
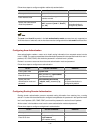
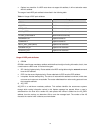
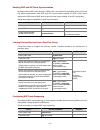
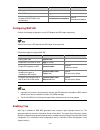
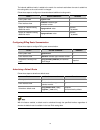
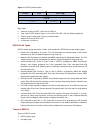
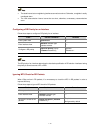
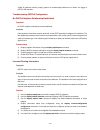
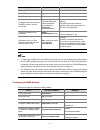
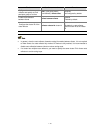
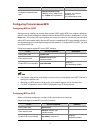
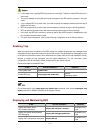
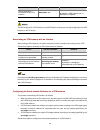
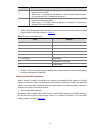
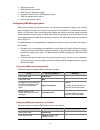
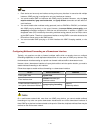
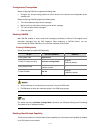
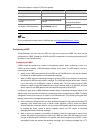
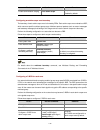
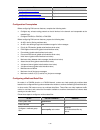
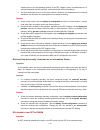
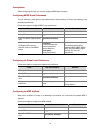
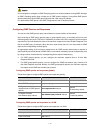
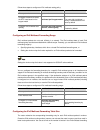
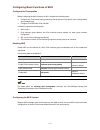
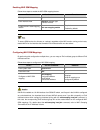
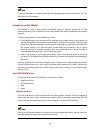
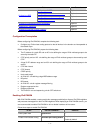
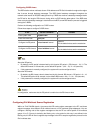
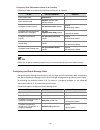
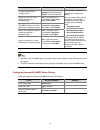
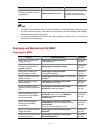
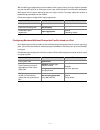
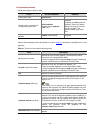
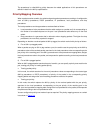
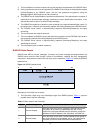
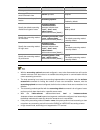
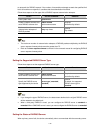
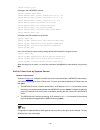
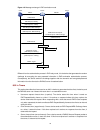
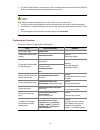
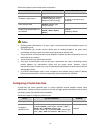
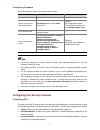
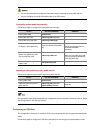
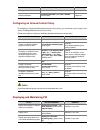
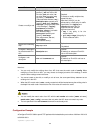
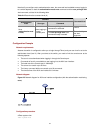
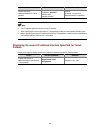
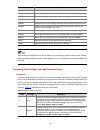
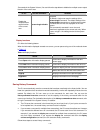
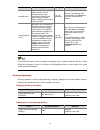
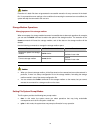
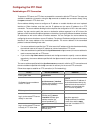
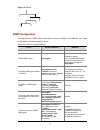
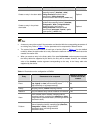
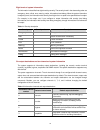
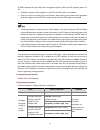
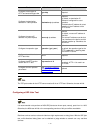
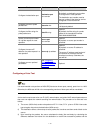
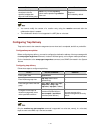
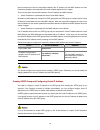
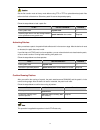
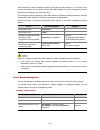
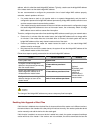
To do…
Use the command…
Remarks
Enter system view
system-view
—
Enter VLAN view
vlan vlan-id
—
Enable ARP detection for
the VLAN
arp detection enable
Required
Disabled by default. That is, the ARP
packets received on all the ports in the
VLAN will not be checked.
Return to system view
quit
—
Enter Ethernet interface
view
interface interface-type
interface-number
—
Configure the port as a
trusted port
arp detection trust
Optional
The port is an untrusted port by
default.
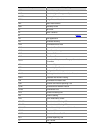
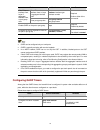
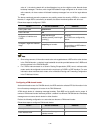
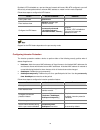
Return to system view
quit
—
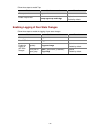
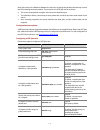
Specify an ARP attack
detection mode
arp detection mode
{ dhcp-snooping | dot1x |
static-bind } *
Required
No ARP attack detection mode is
specified by default; that is, ARP
detection based on DHCP snooping
entries/802.1x security entries/static
IP-to-MAC bindings is not enabled by
default.
Configure a static
IP-to-MAC binding for ARP
detection
arp detection static-bind
ip-address mac-address
Optional
Not configured by default.
If the ARP attack detection mode is
static-bind, you need to configure
static IP-to-MAC bindings for ARP
detection.
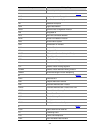
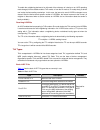
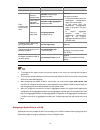
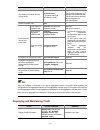
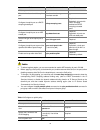
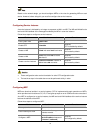
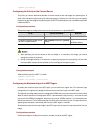
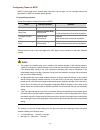
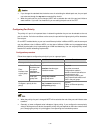
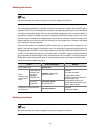
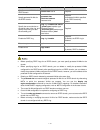
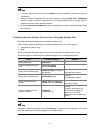
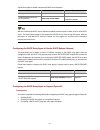
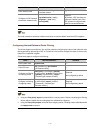
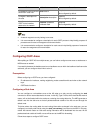
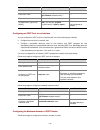
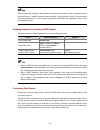
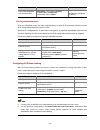
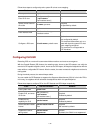
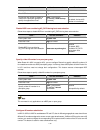
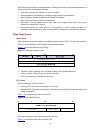
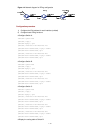
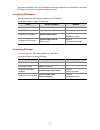
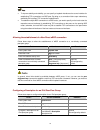
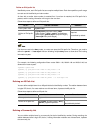
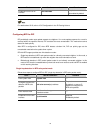
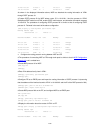
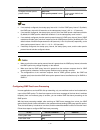
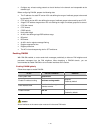
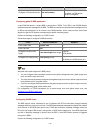
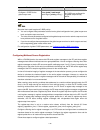
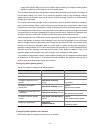
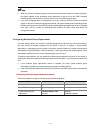
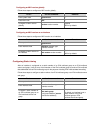
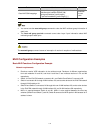
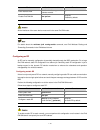
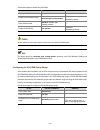
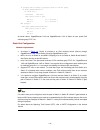
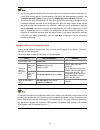
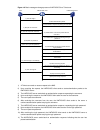
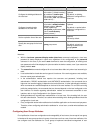
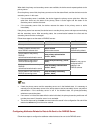
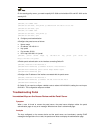
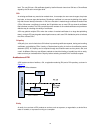
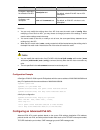
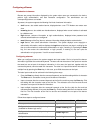
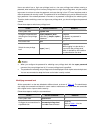
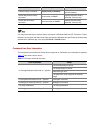
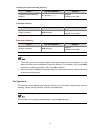
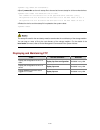
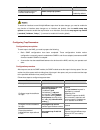
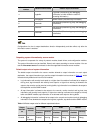
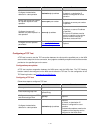
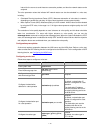
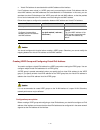
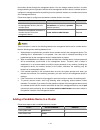
During the DHCP assignment process, when the client receives the DHCP-ACK message from the
DHCP server, it broadcasts a gratuitous ARP packet to detect address conflicts. If no response is
received in a pre-defined time period, the client uses the assigned IP address. If the client is enabled
with ARP detection based on 802.1X security entries, the IP address is not uploaded to the 802.1X
device before the client uses the IP address. As a result, the gratuitous ARP packet is considered to be
an attack packet and is discarded, and thus cannot detect conflicts. After the client uploads its IP
address to the 802.1X device, subsequent ARP packets sent by the client are considered to be valid
and are allowed to travel through.
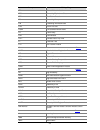
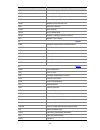
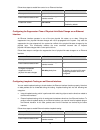
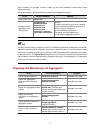
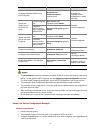
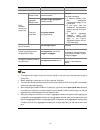
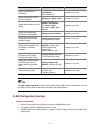
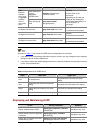
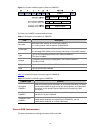
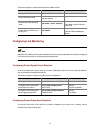
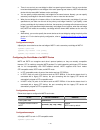
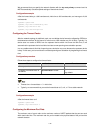
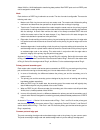
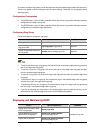
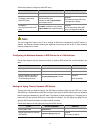
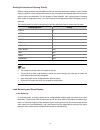
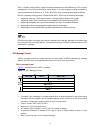
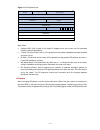
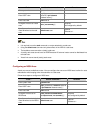
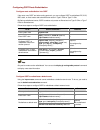
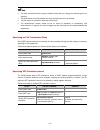
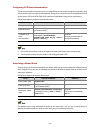
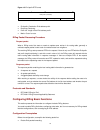
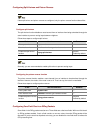
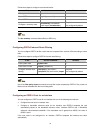
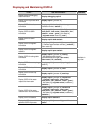
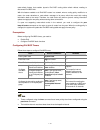
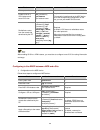
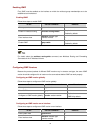
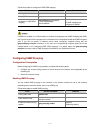
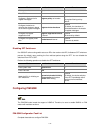
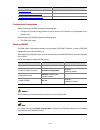
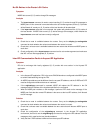
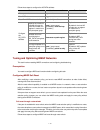
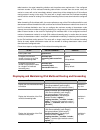
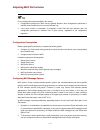
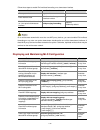
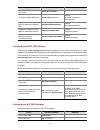
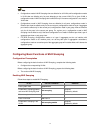
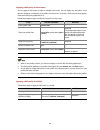
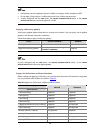
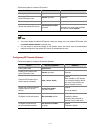
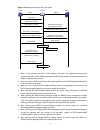
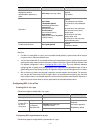
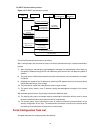
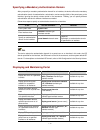
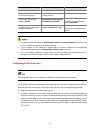
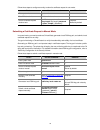
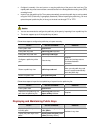
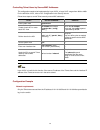
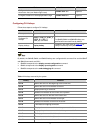
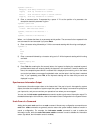
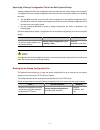
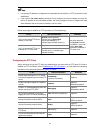
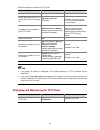
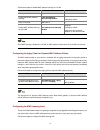
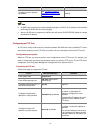
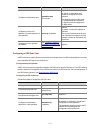
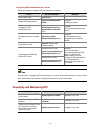
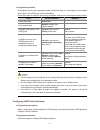
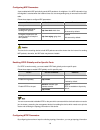
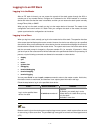
Configuring ARP Detection Based on Specified Objects
You can also specify objects in ARP packets to be detected. The objects involve:
z
src-mac: Checks whether the sender MAC address of an ARP packet is identical to the source
MAC address in the Ethernet header. If they are identical, the packet is forwarded; otherwise, the
packet is discarded.