H3C LS-3100-52P-OVS-H3 Operation Manual - page 1546
ii
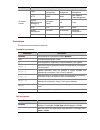
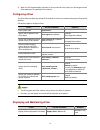
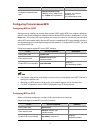
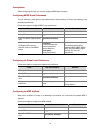
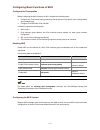
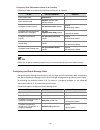
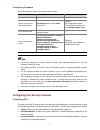
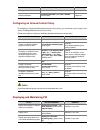
5 Logging In Through NMS··························································································································5-1
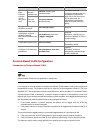
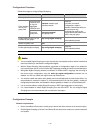
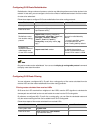
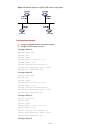
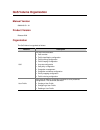
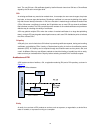
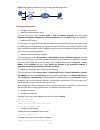
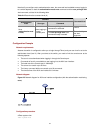
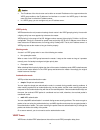
Introduction ·············································································································································5-1
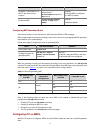
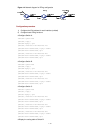
Connection Establishment Using NMS ···································································································5-1
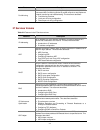
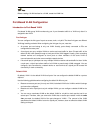
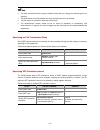
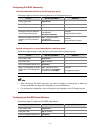
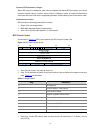
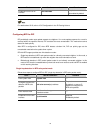
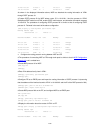
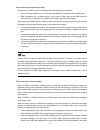
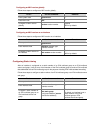
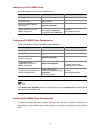
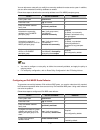
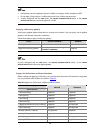
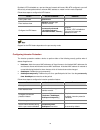
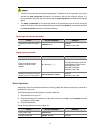
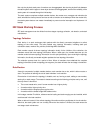
6 Specifying Source for Telnet Packets ·····································································································6-1
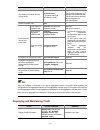
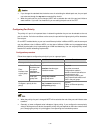
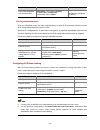
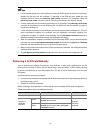
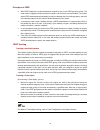
Introduction ·············································································································································6-1
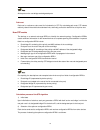
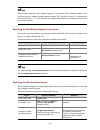
Specifying Source IP address/Interface for Telnet Packets····································································6-1
Displaying the source IP address/Interface Specified for Telnet Packets ··············································6-2
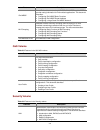
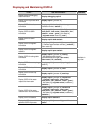
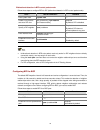
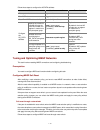
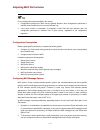
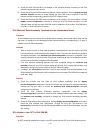
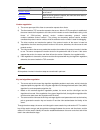
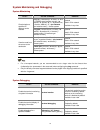
7 Controlling Login Users····························································································································7-1
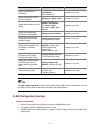
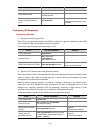
Introduction ·············································································································································7-1
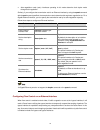
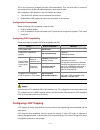
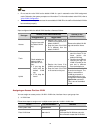
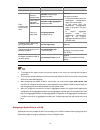
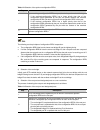
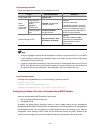
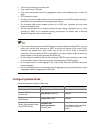
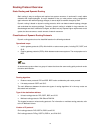
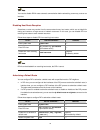
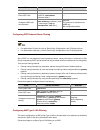
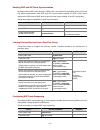
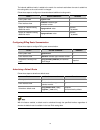
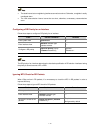
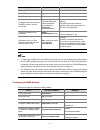
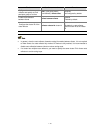
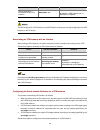
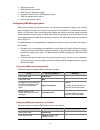
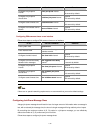
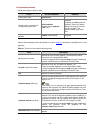
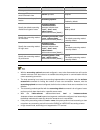
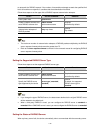
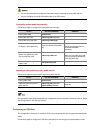
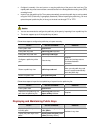
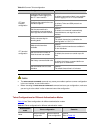
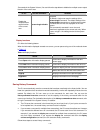
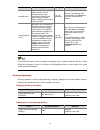
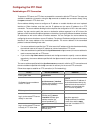
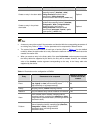
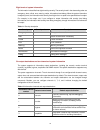
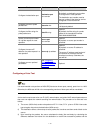
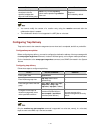
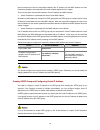
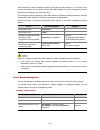
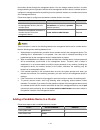
Controlling Telnet Users ·························································································································7-1
Prerequisites····································································································································7-1
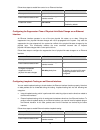
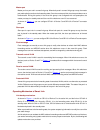
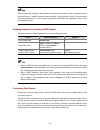
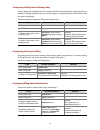
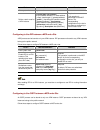
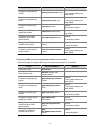
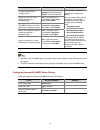
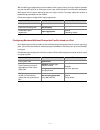
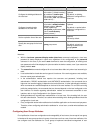
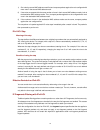
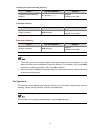
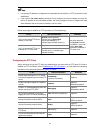
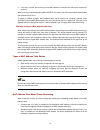
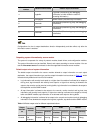
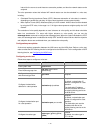
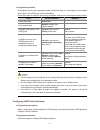
Controlling Telnet Users by Source IP Addresses ··········································································7-1
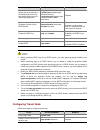
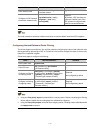
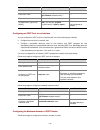
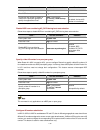
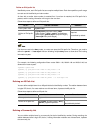
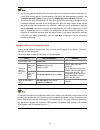
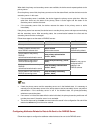
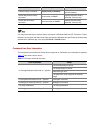
Controlling Telnet Users by Source and Destination IP Addresses················································7-2
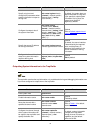
Controlling Telnet Users by Source MAC Addresses ·····································································7-3
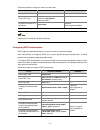
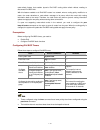
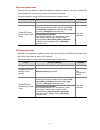
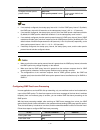
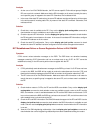
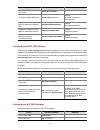
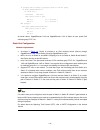
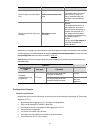
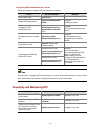
Configuration Example ····················································································································7-3
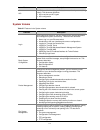
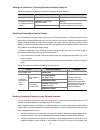
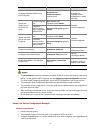
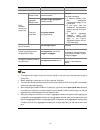
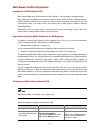
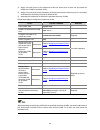
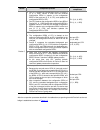
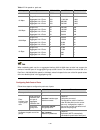
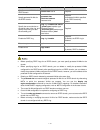
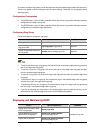
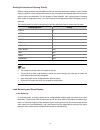
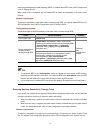
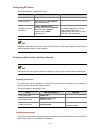
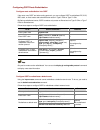
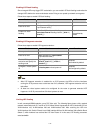
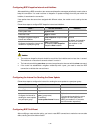
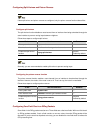
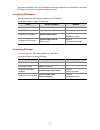
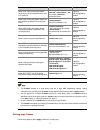
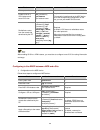
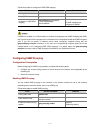
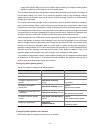
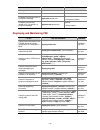
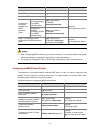
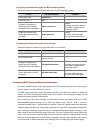
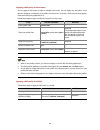
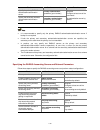
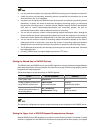
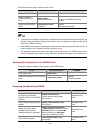
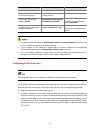
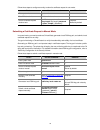
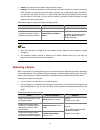
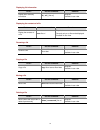
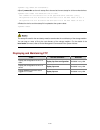
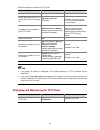
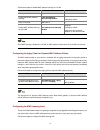
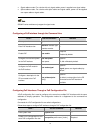
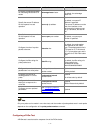
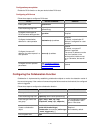
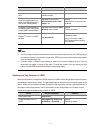
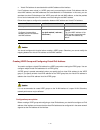
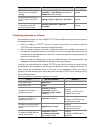
Controlling Network Management Users by Source IP Addresses ························································7-4
Prerequisites····································································································································7-4
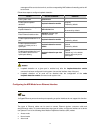
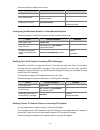
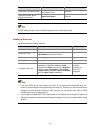
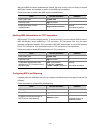
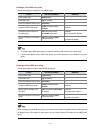
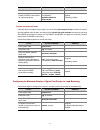
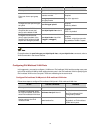
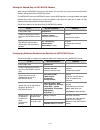
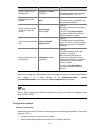
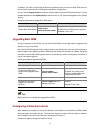
Controlling Network Management Users by Source IP Addresses·················································7-5
Configuration Example ····················································································································7-5