Canon imagePRESS C1 Service Manual - page 682
Chapter 11
11-37
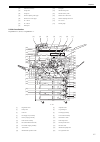
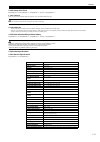
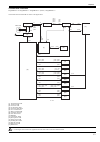
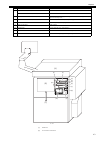
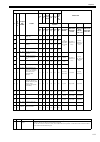
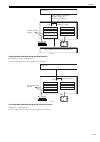
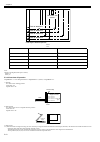
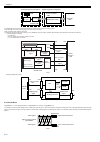
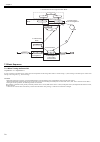
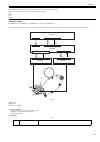
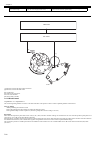
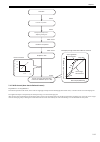
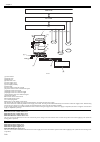
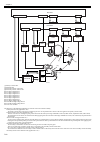
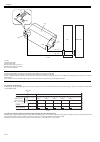
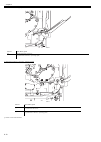
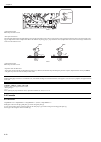
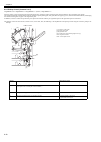
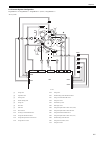
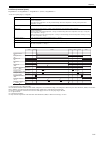
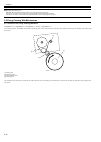
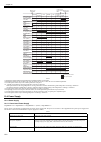
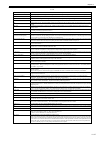
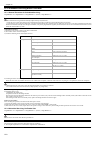
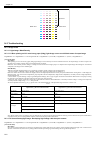
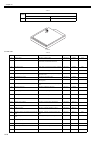
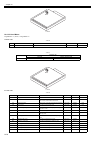
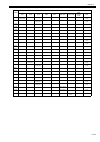
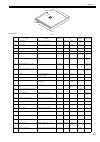
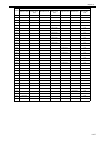
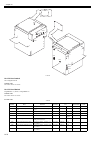
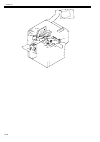
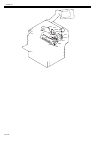
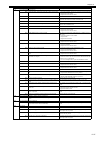
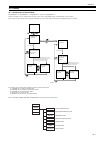
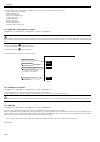
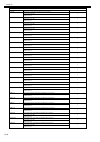
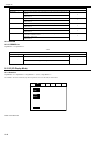
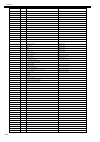
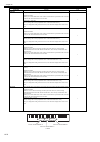
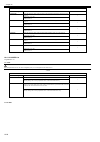
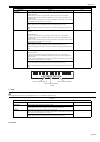
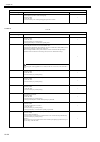
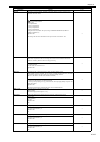
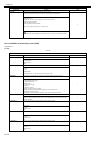
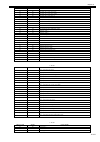
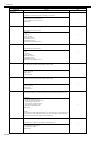
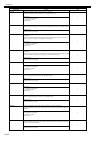
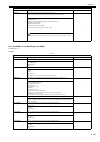
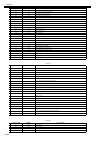
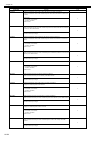
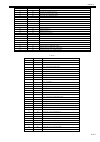
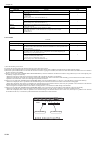
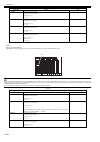
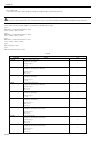
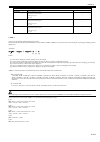
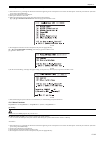
Site internal access mode process diagram
F-11-54
1) SSO-Tokyo acquires site lists from Active Directories.
Note, however, that the Active Directories accessed in order to acquire site lists are in the order in which they were returned by DNS, so there is no guarantee
that the same Active Directory will be accessed as in the initial settings (upon device settings or changes to NW settings, etc.).
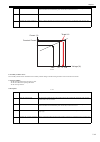
[Site subnet list]
Site: Tokyo: = 172.24.12.0/24, 172.24.35.0/24
Site: Osaka: = 192.168.1.0/24
Site: Hakata: = 211.111.1.0/24
As a result, since SSO-Tokyo is 172.24.12.80, the subnet is 172.24.12.0/24, and is judged as belonging to site Tokyo.
2) The DNS server obtains its Active Directory list from the primary or secondary DNS, as set in the device.
[Active Directory]
172.24.12.2, 172.24.35.2, 192.168.1.2, 211.111.1.30
3) Of the Active Directories in 2), above, the ones that belong to the same site (Tokyo) are 172.24.12.2 and 172.24.35.2.
Of these, the Active Directory that is the same subnet as SS-Tokyo is 172.24.12.2. Therefore, this one will be accessed.
4) If access fails at step 3), above, the other Active Directory of the same site, 172.24.35.2, will be accessed.
5) If access fails at step 4), above, also, SSO-Osaka and SSO-Hakata will be accessed (the order will depend on the order of the Active Directories in DNS). Note,
however, that this is an optional operation.
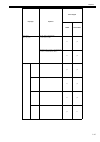
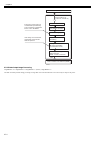
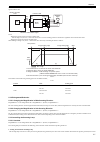
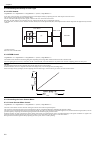
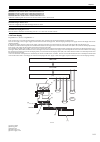
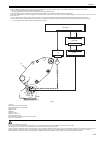
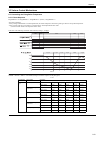
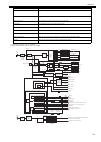
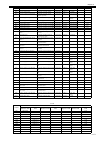
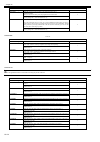
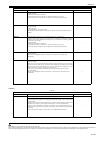
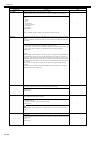
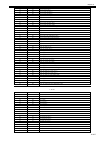
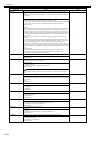
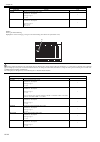
Logging into other domains at multi-domain
At multi-domain, if another domain is logged into, based on the site/ subnet information retrieved in the home domain, the Active Directories of the login destination
domain/ KDC address list are computed. In the event that the domain controller IP addresses of other domains are outside of the site access range, and only the
domain controller within the site is programmed for access, an error message will be displayed to the effect that the site information is incorrect.
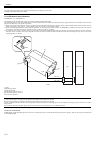
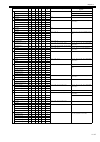
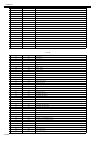
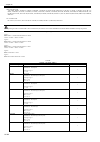
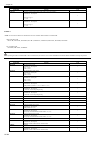
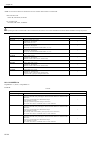
Environment confirmation
Refer to 'Environment confirmation' in this manual for details on the system requirements when using login services.
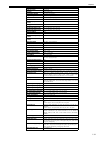
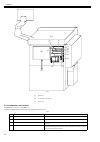
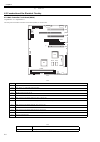
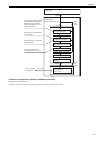
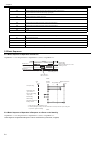
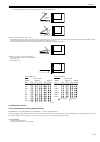
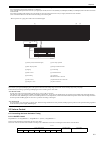
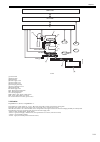
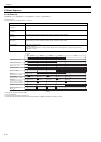
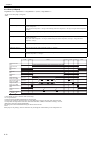
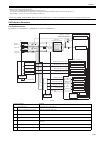
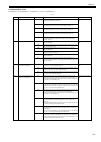
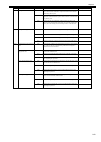
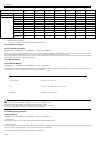
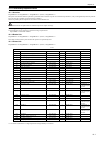
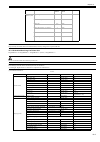
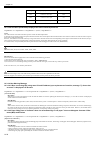
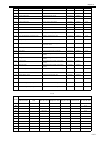
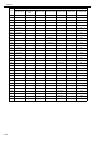
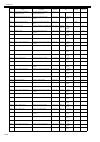
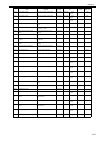
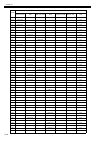
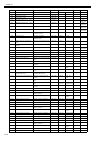
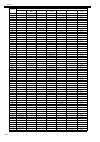
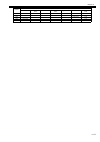
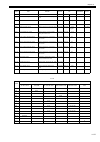
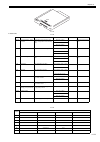
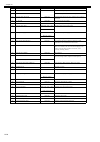
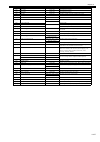
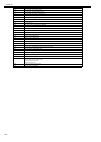
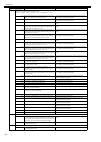
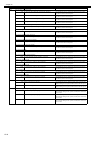
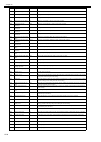
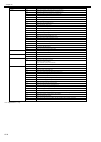
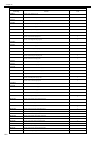
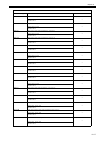
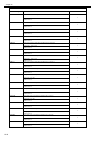
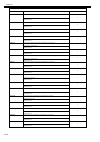
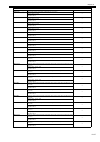
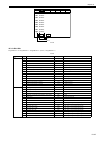
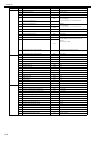
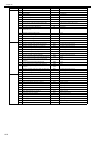
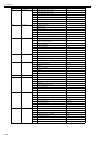
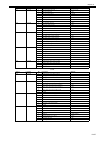
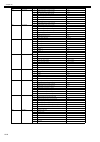
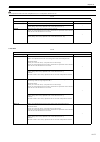
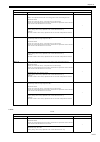
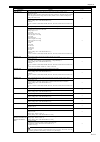
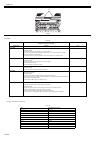
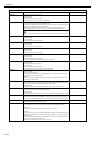
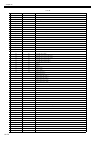
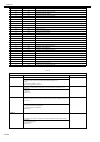
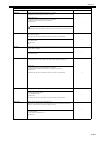
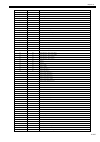
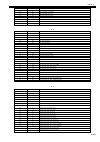
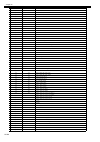
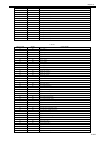
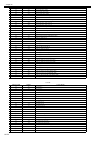
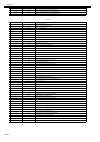
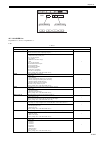
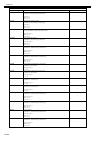
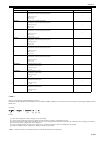
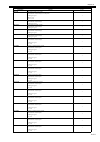
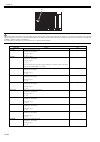
T-11-20
*1: Not supported, since merged with SSO-H in devices from iR3245 series onward.
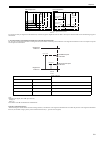
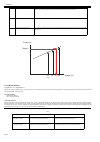
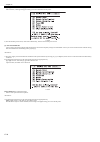
SSO/SDL handling
SSO Ver3.x
Excluded from pre-installation, but included in Administrator's CD (SA also included).
SSO included in the Administrator's CD from iR3245 onward has AMS functionality deleted and is provided as a non AMS enabled login application.
SDL
Login service
SSO-H
SSO-K*1
SSOV3
SDL*1
Local device users upper limit 5000
1000
1000
1000
No. of domains
200
10
200
-
Operating devices
Up till latest model
Till before iR 3245series
Up till latest model
Till before iR 3245series
IpV6
Available, but authentication
not performed in IPv6
N/A
Available
N/A
Memory (KB)/ threads
3584/33
2800/33
2800/33
2300/33
Supported AD
Windows 2000 Server/
Windows Server 2003
Windows 2000 Server/
Windows Server 2003
Windows 2000 Server/Windows
Server 2003
-
Authentication method
NTLM
Kerberos
Local Device Authentication
Kerberos
NTLM
Local
-
Server
AD/KDC
(included in AD)
SA/AD
-
Key
DES
-
-
Department ID management
linkage
Local authentication only available
However, domain requires NSA.
-
Site access
Available
Available
-
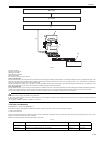
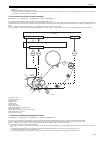
DomainX
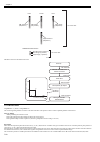
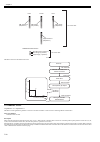
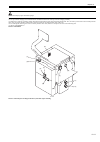
SSO- Toky o
DC-Tokyo/DNS
172. 24. 12. 2
172. 24. 12. 80
SSO-Osaka
DC-Osaka/DNS
192.168.1.2
192.168.1.90
SSO-Hakata
DC-Hakata/DNS
211. 111. 1. 30
211. 111. 1. 3
WAN
WAN
Repllication
Repllication
Site : Tokyo
172. 12. 12. 0/24
1. Initial settings,
site list acquisition,
compute sites attached
to device.
2.Acquire
AD list.
4.Access same
site AD.
3.Access same
subnet AD.
Site:Osaka
192.168.1.0/24
Sit e: Hakat a
211. 111. 1. 0/ 24
DNS server A
records:
AD 192.168.1.2
AD 172.24.12.2
AD 211.111.1.30
SSO-Tokyo 172.24.12.80
SSO-Osaka 192.168.1.90
SSO-Hakata 211.111.1.3
Site : Tokyo
172. 24. 12. 0/24
172. 24. 35. 0/24
Site : Osaka
192. 168. 1. 0/24
Site : Hakata
211. 111. 1. 0/24
172. 24. 35. 0/24